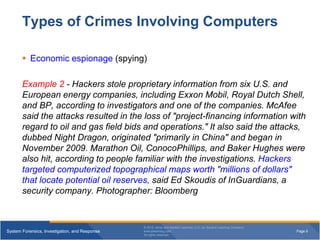
The document discusses various types of crimes involving computers. It describes white-collar crimes like the Enron case, where executives hid losses and fabricated profits. It also discusses counterintelligence gathering to protect against espionage. Economic espionage and theft of intellectual property from companies are provided as examples. Common computer crimes also described include financial fraud, hacking, denial of service attacks, computer viruses, and theft of data.
![Page 2System Forensics, Investigation, and Response
© 2015 Jones and Bartlett Learning, LLC, an Ascend Learning Company
www.jblearning.com
All rights reserved.
Types of Crimes Involving Computers
White-collar crimes - refers to financially motivated nonviolent crime
committed by business and government professionals [higher level
employee]
Enron case (energy, commodities, and services company) - In this
famous white collar crime case, a company that was once successful
resorted to schemes to hide losses and fabricate profits.
Though Enron shares were worth $90.75 at its peak, they fell to just
$0.67 after the company filed for bankruptcy in 2002. Some of the
criminal practices involved in the Enron case included using off-
balance-sheet special purpose vehicles (SPVs) in order to hide
mounting debt and “toxic assets” from both investors and creditors.
Chief Financial Officer (CFO) Andrew Fastow was held largely
responsible for orchestrating these false business tactics.](https://image.slidesharecdn.com/223-200511043920/85/223-Computer-ethics-2-320.jpg)