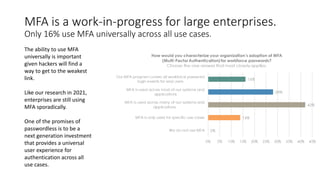
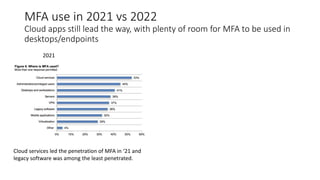
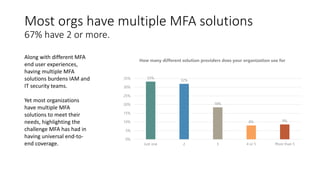
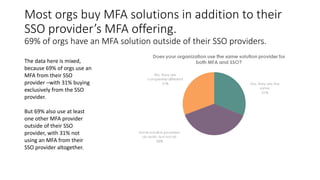
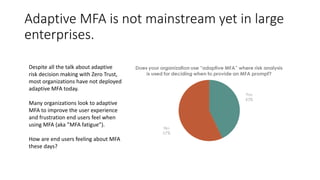
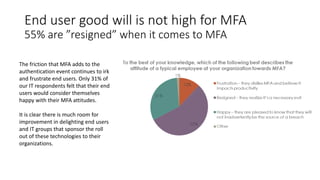
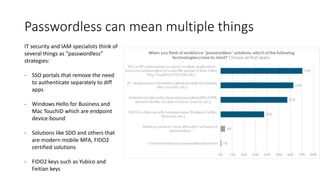
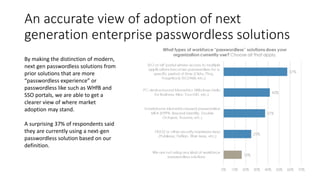
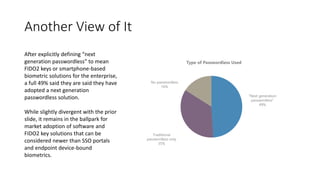
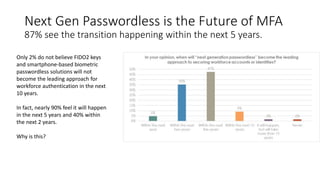
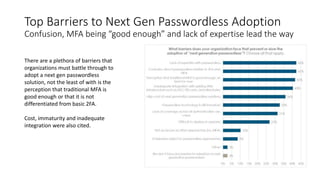
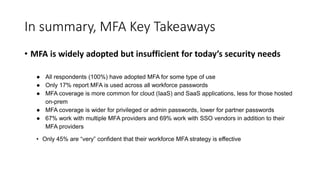
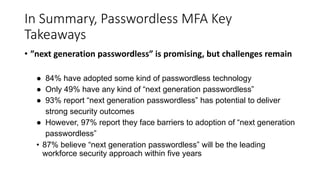
The 2022 workforce strong authentication demographics report highlights the slow adoption of multi-factor authentication (MFA) across large enterprises, with only 16% using it universally. While interest in next-generation passwordless solutions is growing, confusion and perceived sufficiency of traditional MFA pose significant barriers to adoption. Despite these challenges, 87% of respondents believe that next-generation passwordless solutions will become the leading approach for workforce security within the next five years.