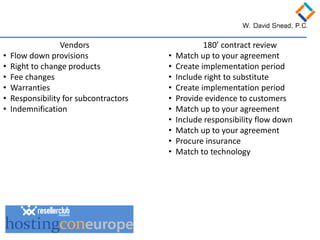
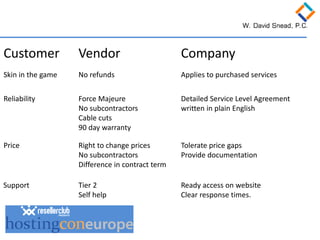
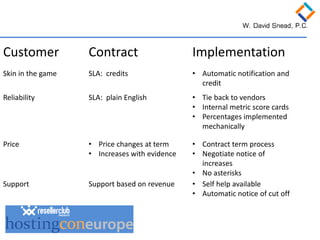
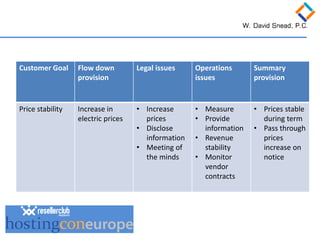
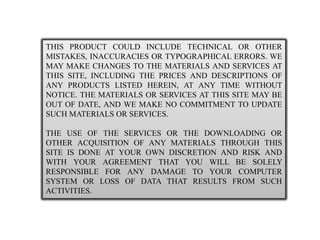
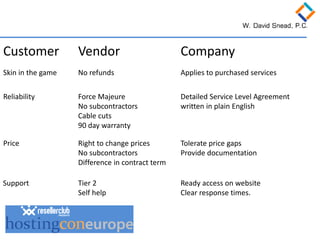
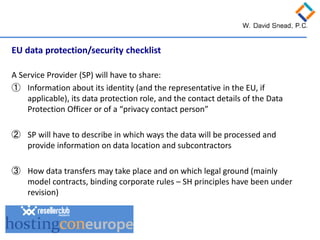
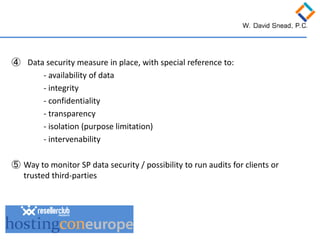
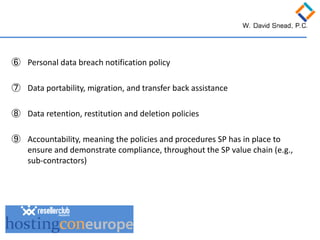
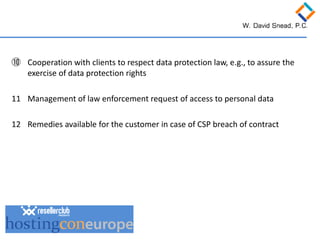
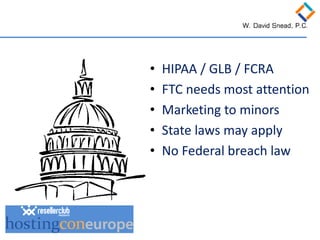
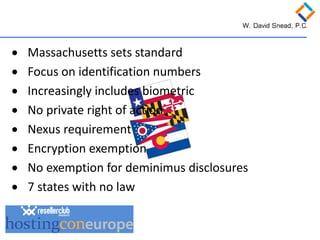
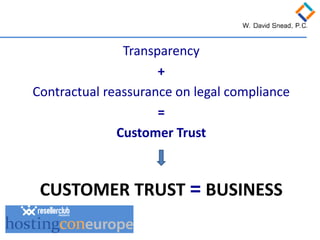
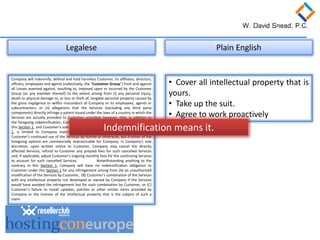
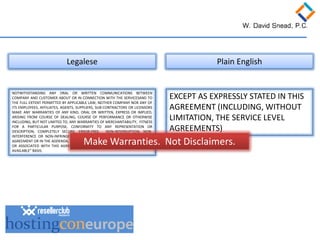
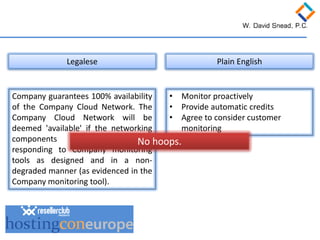
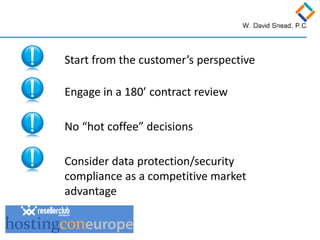
The document discusses creating effective global contracts for internet businesses. It provides tips for drafting clear and compliant contract language while protecting the business. Key points include conducting a thorough review of contracts, ensuring data protection and security compliance as a competitive advantage, starting from the customer's perspective, and addressing issues like indemnification, warranties and service level agreements in plain language terms. The presenters provide expertise in international legal advice and European data protection law.