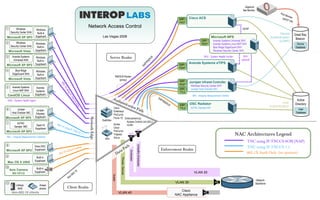
2008 lv nac-big-pic
- 1. Gigamon Net Monitor Port M onito Cisco ACS DHC r EAP- P info FAST 1 Windows Network Access Control HCAP Windows Security Center SHA Built-in Device Great Bay Microsoft XP SP3 Supplicant Las Vegas 2008 Microsoft NPS Authentication Beacon EAP- Avenda Systems Universal SHV (LDAP) 2 Windows Windows PEAP Avenda Systems Linux NAP SHV Device Security Center SHA Built-in Blue Ridge EdgeGuard SHV Database Microsoft Vista Supplicant Windows Security Center SHV 3 Avenda Systems Windows Server Realm SHV - System Health Verifier SHV US Universal SHA optional DI Built-in RA Supplicant Avenda Systems eTIPS P/ Microsoft XP SP3 EAP- EA PEAP 4 Blue Ridge Windows EdgeGuard SHA Built-in RADIUS Router Microsoft Vista Supplicant (proxy) EAP- Juniper Infranet Controller 80 PEAP Windows Security Center SHV 2.1 5 Avenda Systems Avenda Xu EAP- Juniper Host Checker IMV Linux NAP SHA Systems sin TTLS gI CentOS Linux Supplicant IMV - Integrity Measurement Verifier F-T Au t EA NC P/R Active SHA - System Health Agent hen AD CS t icat IUS OSC Radiator User Directory -SO ion EAP- Authentication Pat libTNC Sample IMV H Cisco TTLS User 6 Juniper Host Checker IMC Juniper Enterasys h Database Odyssey ProCurve Microsoft XP SP2 Supplicant Force 10 Enforcement by: Network Edge Switches 7 Access Control List (ACL) libTNC 802. Aruba Open1X 1 X us VLAN Sample IMC ing I Cisco Supplicant F -TNC ProCurve Microsoft XP SP2 CS 1 IMC - Integrity Measurement Collector . 1 Trapeze ACL ACL NAC Architectures Legend APs Xirrus TNC using IF-TNCCS-SOH (NAP) 8 th TNC using IF-TNCCS 1.1 Unhealthy Employees Cisco SSC sture a Microsoft XP SP2 Supplicant witho ut Po ataP Enforcement Realm 802.1X Auth Only (no posture) Employees X 802.1 D 9 Built-in Phones / Devices Supplicant Mac OS X UNIX 10 Axis Camera Built-in 802.1X/TLS Supplicant 2 .1X VLAN 20 - 80 Guests n No Network 11 VLAN 30 ACL Backbone Linksys Avaya NAS phone Client Realm Cisco Non-802.1X clients VLAN 40 ACL NAC Appliance
