Cryptography
Lesson 10
© Copyright 2012-2013 (ISC)², Inc. All Rights Reserved.
For Personal Use of (ISC)2 Seminar Attendee Only.
Contents May Not Be Copied or Otherwise Distributed Under Any Circumstances
© (ISC)2 ® 2010, All Rights Reserved
For Personal Use of (ISC)2 Seminar Attendee Only
Contents May Not Be Copied or Otherwise Distributed Under Any Circumstances
CISSP-ISSEP® Bootcamp Seminar v10
Technical Management
Public Key Infrastructure
Chapter 7
© Copyright 2012-2013 (ISC)², Inc. All Rights Reserved.
For Personal Use of (ISC)2 Seminar Attendee Only.
Contents May Not Be Copied or Otherwise Distributed Under Any Circumstances
2
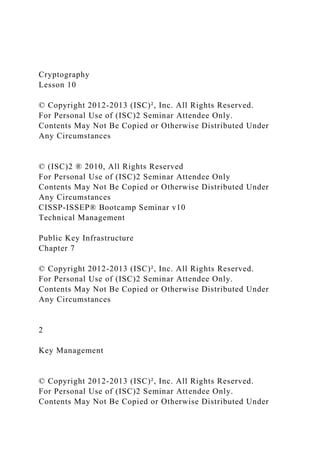
Key Management
© Copyright 2012-2013 (ISC)², Inc. All Rights Reserved.
For Personal Use of (ISC)2 Seminar Attendee Only.
Contents May Not Be Copied or Otherwise Distributed Under Any Circumstances
3
2
Usage Control
5
6
7
Storage
Recovery
Escrow
8
Zeroization
1
3
Creation
Change and Expiry
4
Distribution
Creation
Automated key generation
Truly random
Suitable length
Key encrypting keys
© Copyright 2012-2013 (ISC)², Inc. All Rights Reserved.
For Personal Use of (ISC)2 Seminar Attendee Only.
Contents May Not Be Copied or Otherwise Distributed Under Any Circumstances
4
Key Usage Control
Management has a vested interest in what activities or content may be hidden in cryptographically protected communications or files
They may create a policy that allows management to audit or decrypt encrypted data at their discretion
© Copyright 2012-2013 (ISC)², Inc. All Rights Reserved.
For Personal Use of (ISC)2 Seminar Attendee Only.
Contents May Not Be Copied or Otherwise Distributed Under Any Circumstances
5
Key Change and Expiry
In any environment, plans should be made to update keys periodically
Generating symmetric keys is easy, but delivering them is expensive since you will be delivering [N*(N-1)]/2 keys to N users
Expiry
Expiry ensures that a key is never overused
Expiry based upon:
Amount of traffic
Amount of traffic over time
Time-in-use
© Copyright 2012-2013 (ISC)², Inc. All Rights Reserved.
For Personal Use of (ISC)2 Seminar Attendee Only.
Contents May Not Be Copied or Otherwise Distributed Under Any Circumstances
6
Distribution
Out of band
Public key encryption
Secret key construction
Secret key delivery
Key Distribution Centers (KDC)
Certificates
© Copyright 2012-2013 (ISC)², Inc. All Rights Reserved.
For Personal Use of (ISC)2 Seminar Attendee Only.
Contents May Not Be Copied or Otherwise Distributed Under Any Circumstances
7
Storage
Trusted hardware
Smartcards
© Copyright 2012-2013 (ISC)², Inc. All Rights Reserved.
For Personal Use of (ISC)2 Seminar Attendee Only.
Contents May Not Be Copied or Otherwise Distributed Under Any Circumstances
8
Recovery
Split knowledge
Multi-party key recovery (MPR)
© Copyright 2012-2013 (ISC)², Inc. All Rights Reserved.
For Personal Use of (ISC)2 Seminar Attendee Only.
Contents May Not Be Copied or Otherwise.