A trip to ict and society
•Download as PPTX, PDF•
0 likes•252 views
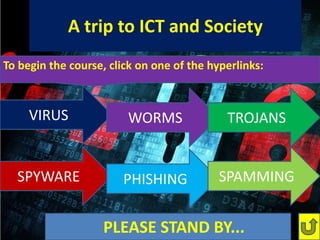
This document provides an overview of different types of malware and security threats including viruses, worms, Trojans, spyware, phishing, spamming and spoofing. Viruses replicate by inserting copies of themselves into other programs. Worms replicate automatically to spread to other computers. Trojans contain malicious code that is concealed. Spyware collects users' data without their knowledge or consent. Phishing involves collecting data from legitimate-looking websites while spoofing involves falsifying documents. Spamming sends unwanted messages that may contain infected attachments. The document concludes by advising readers to use anti-virus software and respect copyrights.
Report
Share
Report
Share
Recommended
More Related Content
What's hot
What's hot (20)
A Trip to ICT and Society Series 1 : INFECTED! PART 2

A Trip to ICT and Society Series 1 : INFECTED! PART 2
Similar to A trip to ict and society
Similar to A trip to ict and society (20)
Online Safety, Security, Ethics and Etiquette Standards.pptx

Online Safety, Security, Ethics and Etiquette Standards.pptx
Recently uploaded
Recently uploaded (20)
Swan(sea) Song – personal research during my six years at Swansea ... and bey...

Swan(sea) Song – personal research during my six years at Swansea ... and bey...
WhatsApp 9892124323 ✓Call Girls In Kalyan ( Mumbai ) secure service

WhatsApp 9892124323 ✓Call Girls In Kalyan ( Mumbai ) secure service
08448380779 Call Girls In Civil Lines Women Seeking Men

08448380779 Call Girls In Civil Lines Women Seeking Men
Transforming Data Streams with Kafka Connect: An Introduction to Single Messa...

Transforming Data Streams with Kafka Connect: An Introduction to Single Messa...
Injustice - Developers Among Us (SciFiDevCon 2024)

Injustice - Developers Among Us (SciFiDevCon 2024)
Next-generation AAM aircraft unveiled by Supernal, S-A2

Next-generation AAM aircraft unveiled by Supernal, S-A2
#StandardsGoals for 2024: What’s new for BISAC - Tech Forum 2024

#StandardsGoals for 2024: What’s new for BISAC - Tech Forum 2024
Tech-Forward - Achieving Business Readiness For Copilot in Microsoft 365

Tech-Forward - Achieving Business Readiness For Copilot in Microsoft 365
IAC 2024 - IA Fast Track to Search Focused AI Solutions

IAC 2024 - IA Fast Track to Search Focused AI Solutions
Presentation on how to chat with PDF using ChatGPT code interpreter

Presentation on how to chat with PDF using ChatGPT code interpreter
08448380779 Call Girls In Diplomatic Enclave Women Seeking Men

08448380779 Call Girls In Diplomatic Enclave Women Seeking Men
A trip to ict and society
- 1. SPYWARE A trip to ICT and Society INFECTED!!!PLEASE STAND BY... To begin the course, click on one of the hyperlinks: VIRUS WORMS TROJANS PHISHING SPAMMING
- 2. VIRUSES: INFECTION SPREADS A computer virus is a type of malware that, when executed, replicates by inserting copies of itself into the computer or network directly.
- 3. WORMS: INFECTION MULTIPLIES A computer worm is a standalone malware c omputer program that replicates itself in order to spread to other computers.
- 4. TROJANS: INFECTION IS STEALTHED A Trojan horse or Trojan is a non- self-replicating type of malware program containing malicious code.
- 5. SPYWARE: THE FBI IS WATCHING Spyware is a software aiding a person or organization to collect data from a person, unsuspecting the application installed.
- 6. PHISHING AND SPOOFING: LEGITIMATE THREATS Phishing is the collection of data from users accessing a “legitimate” website. Spoofing is falsifying documents.
- 7. SPAMMING: FLOODED INBOX Spamming is the process of delivering non-sensical messages to people, and can also carry an infected attachment.
- 8. Are you protected? • The mentioned security risks often come from the internet database. • Keep yourself protected using an anti-virus program • Copyright Infringement is a crime. This Presentation is “All Rights Rserved 2014”
