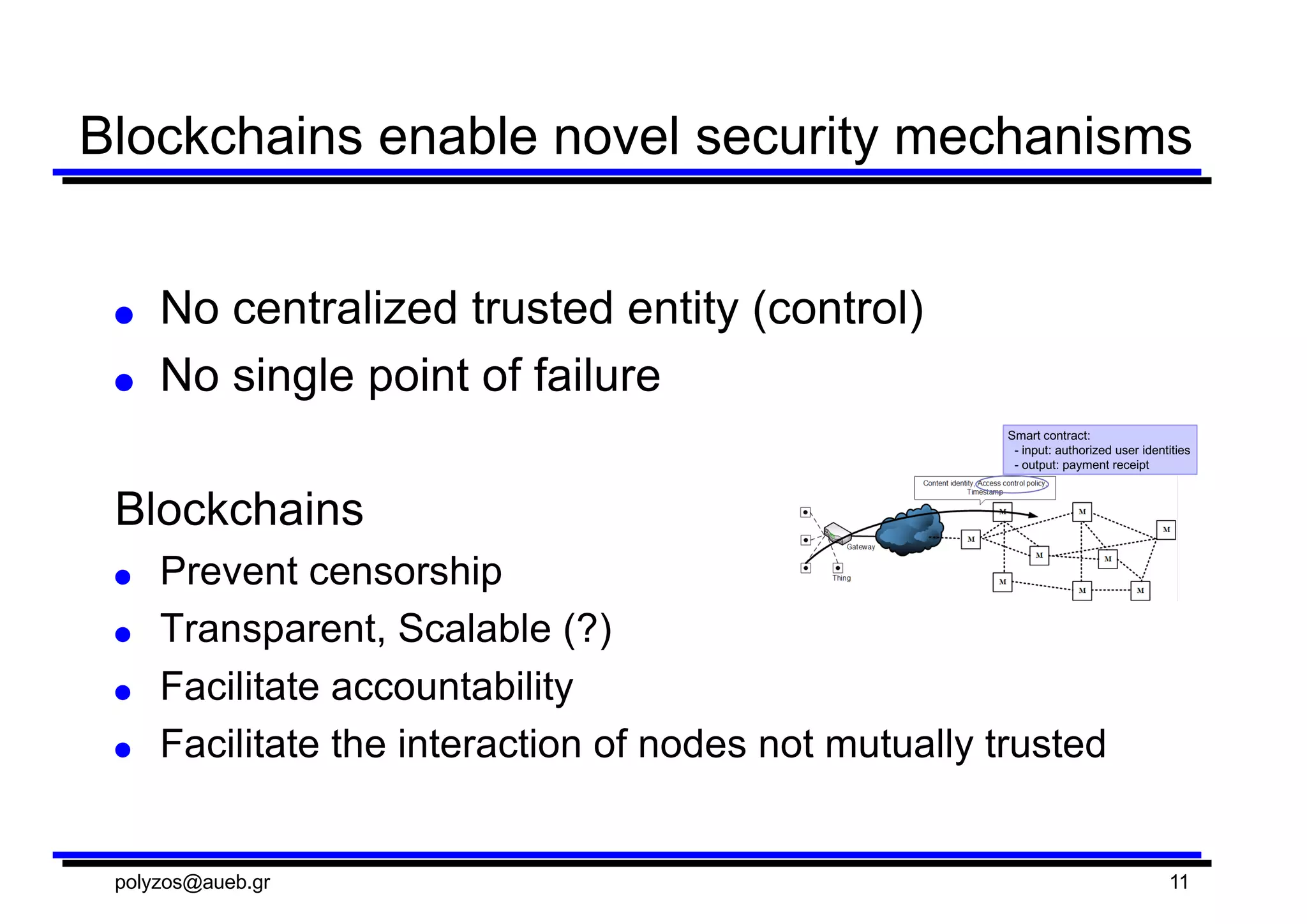
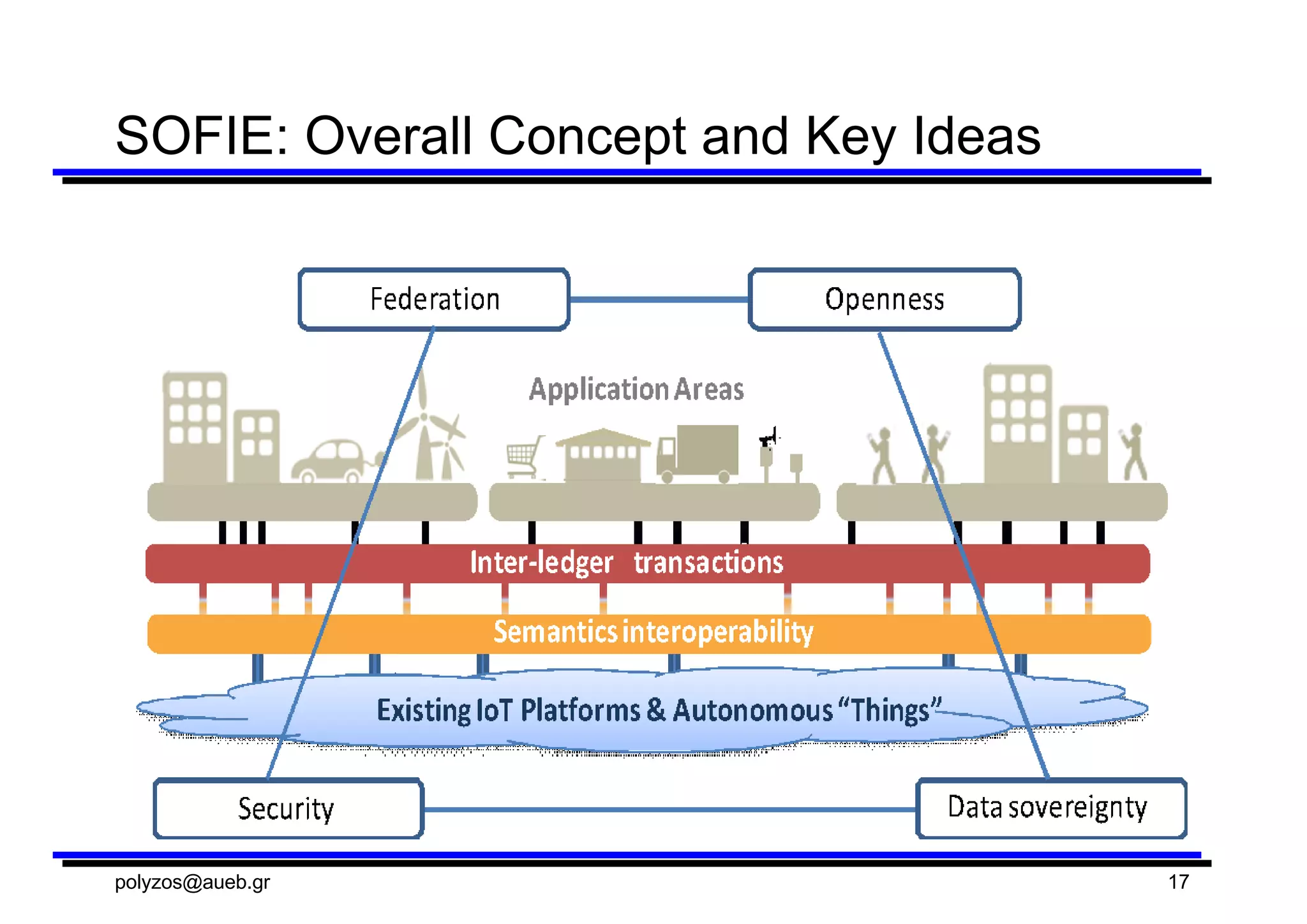
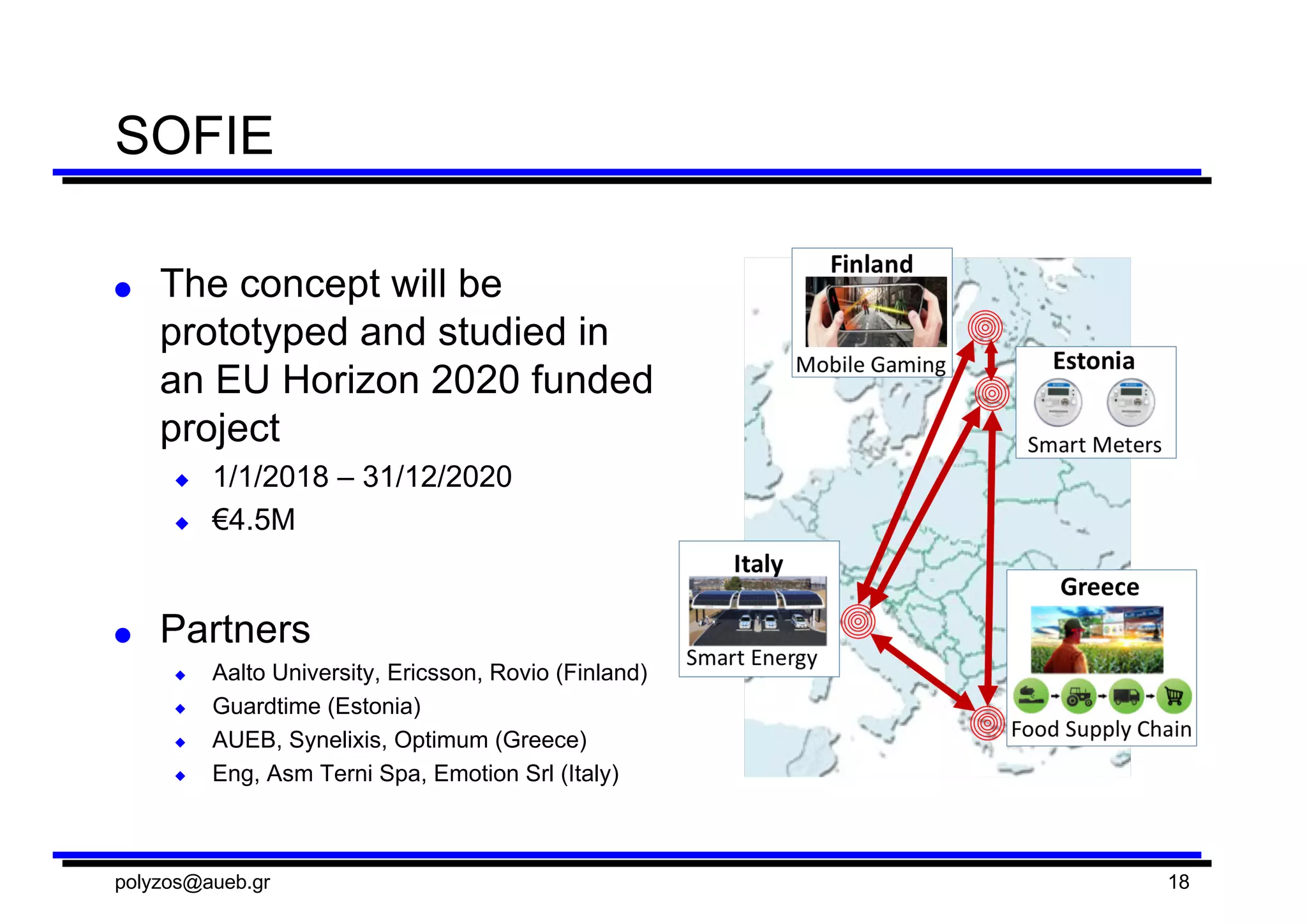
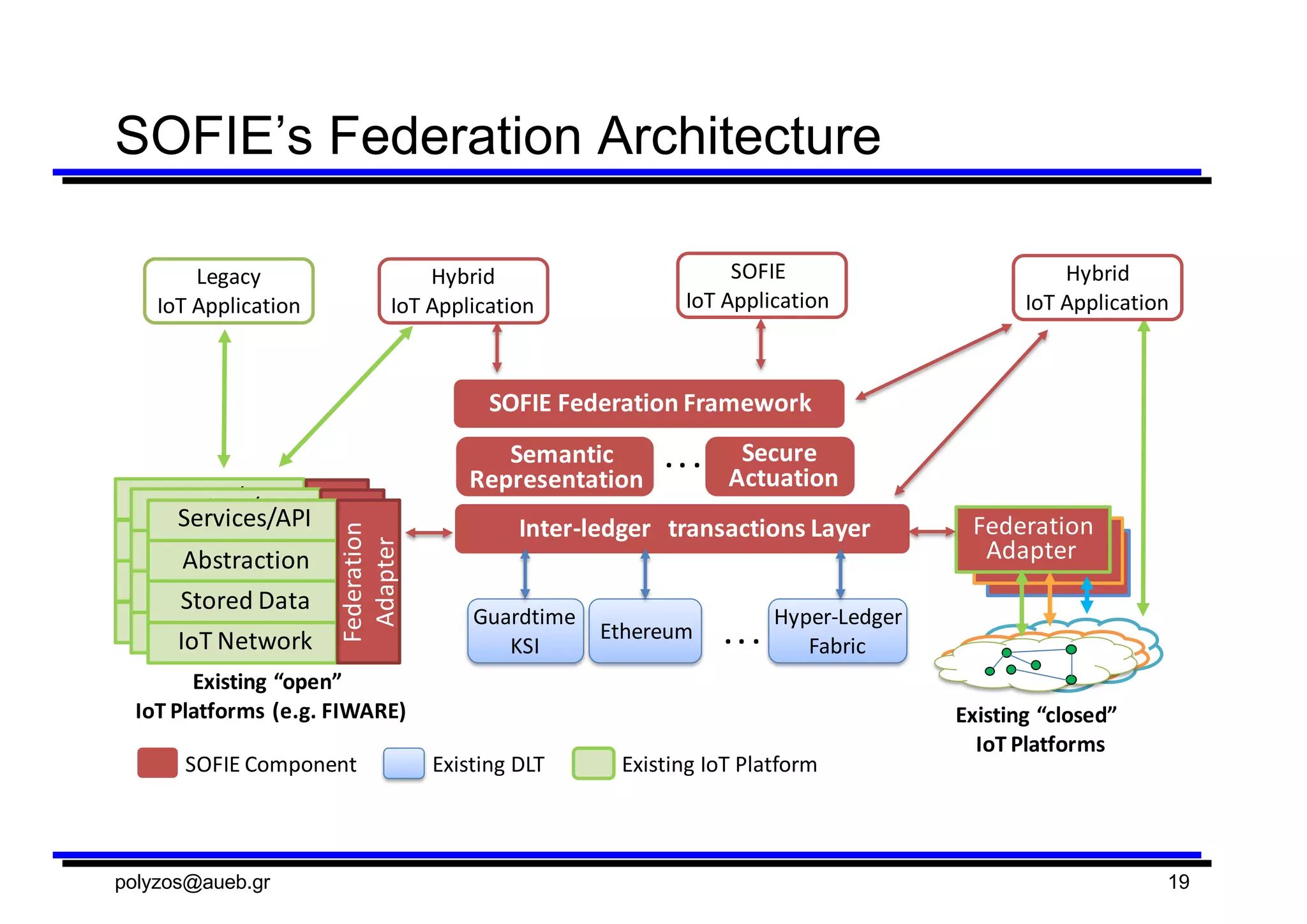
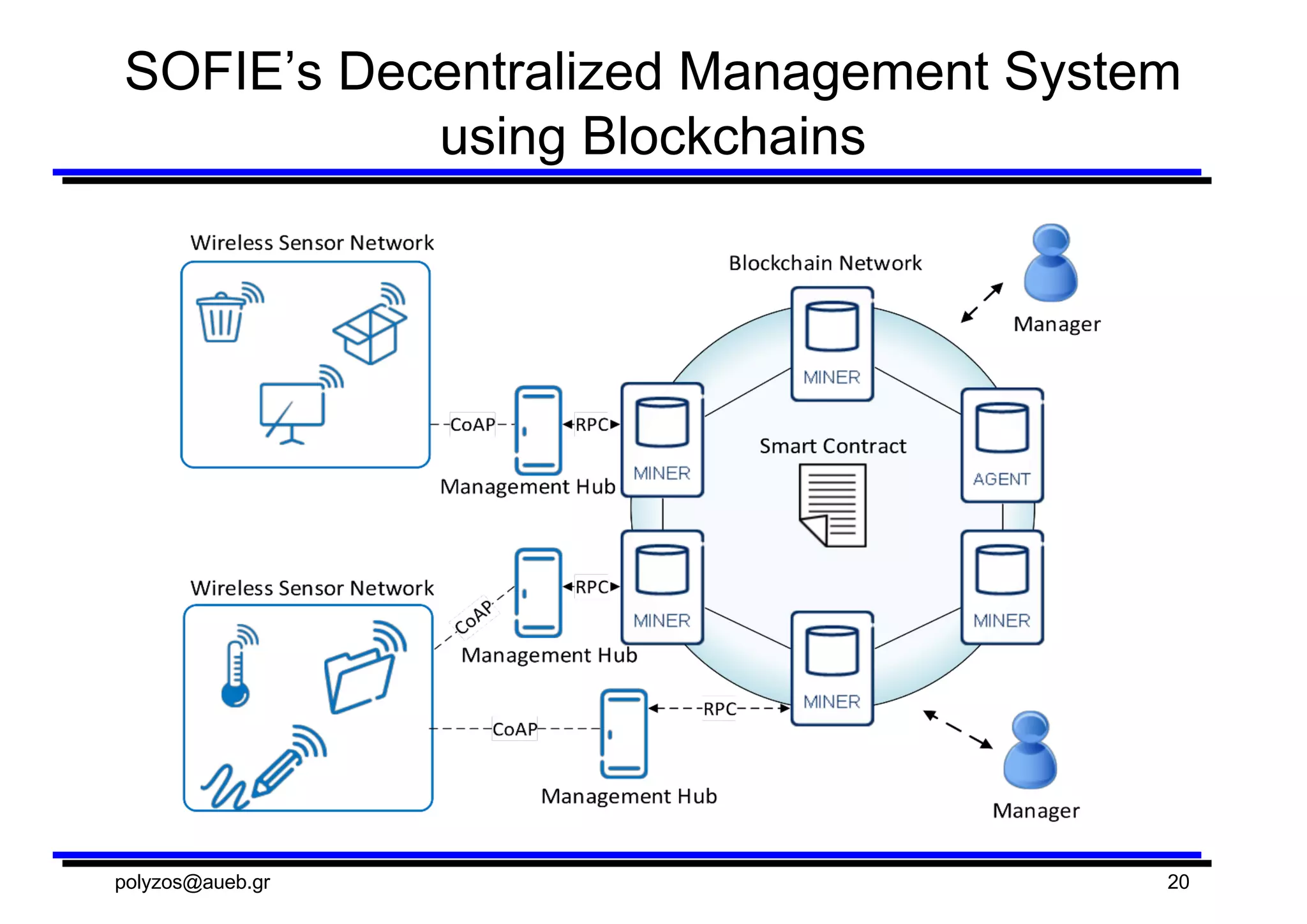
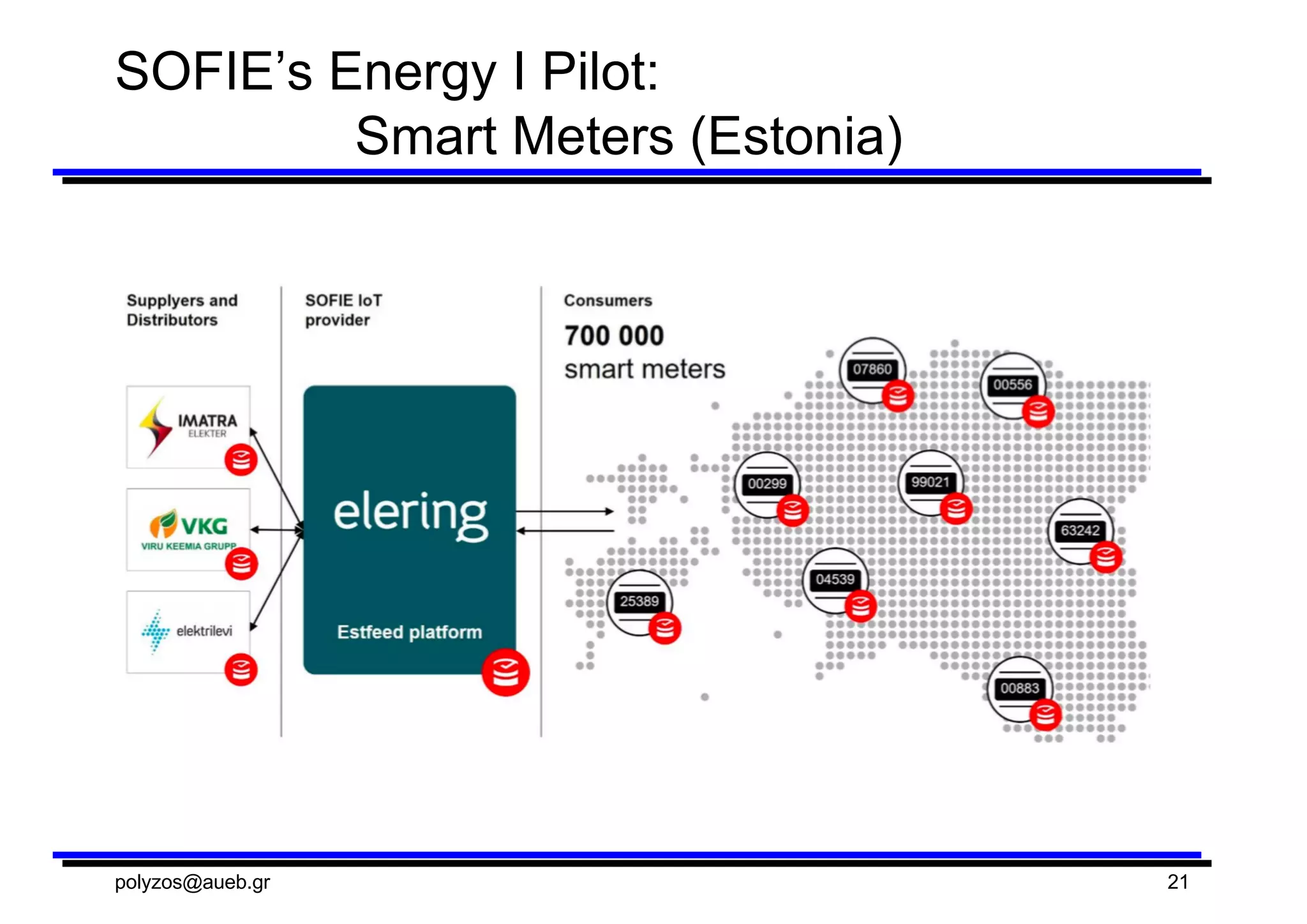
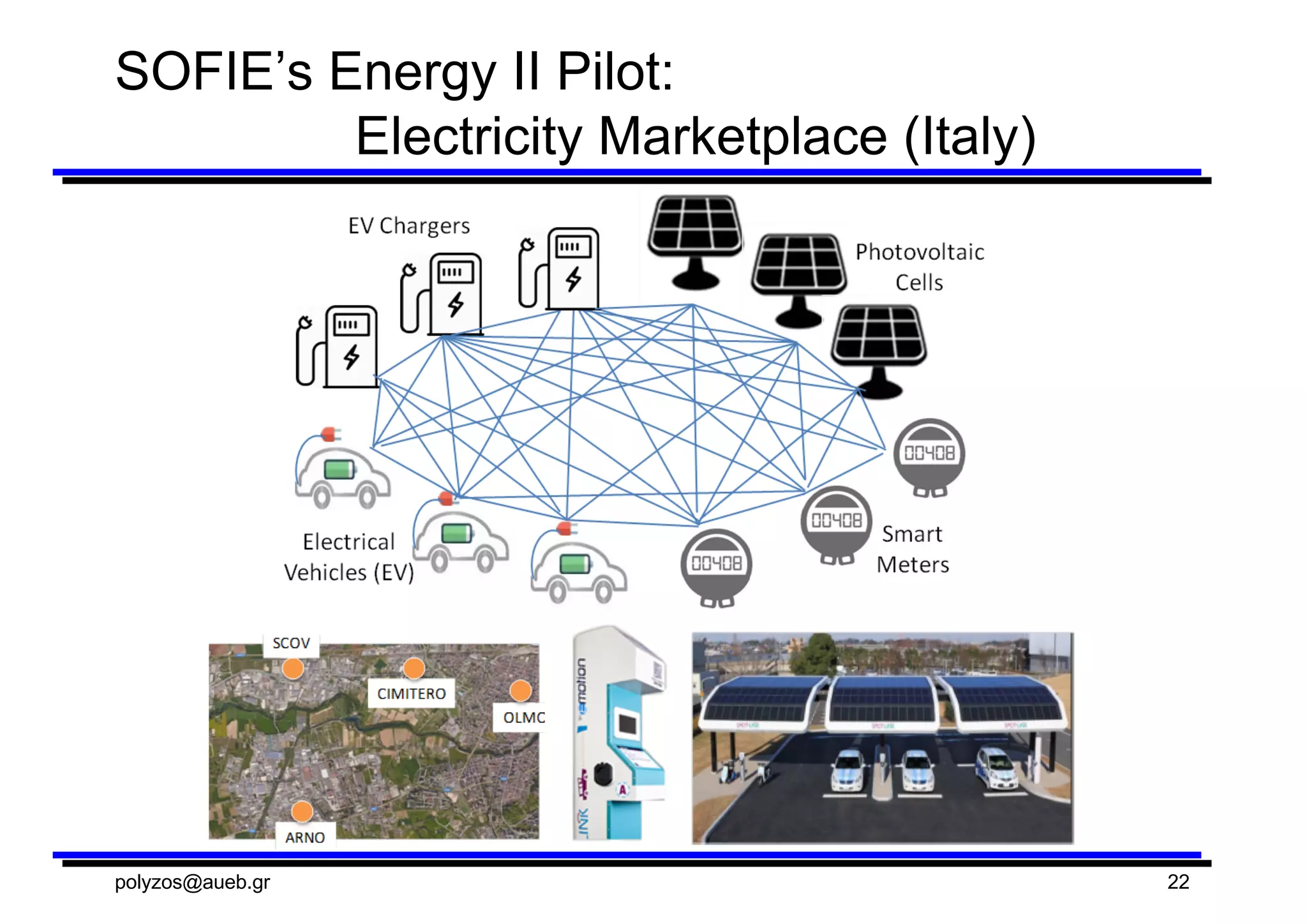
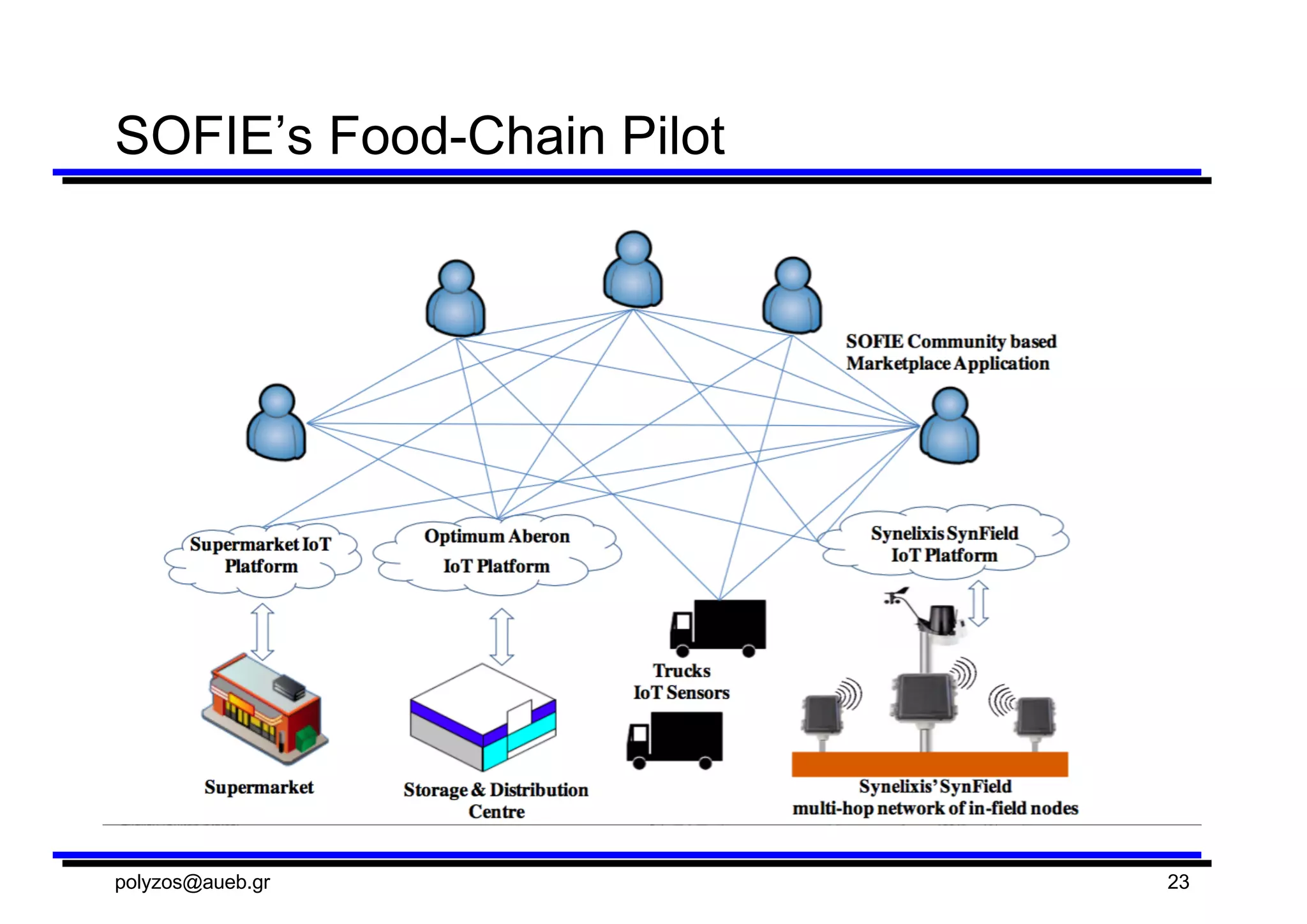
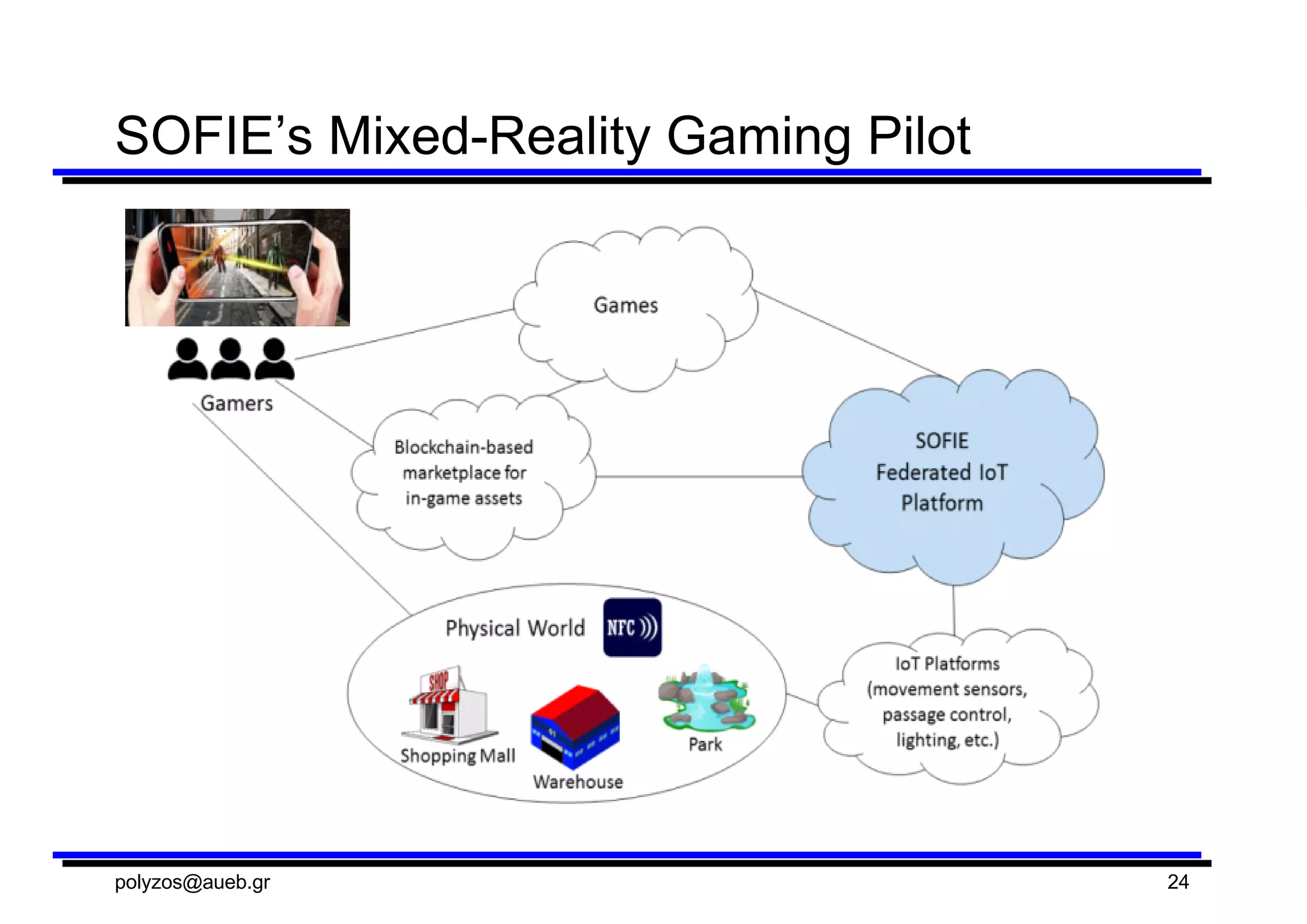
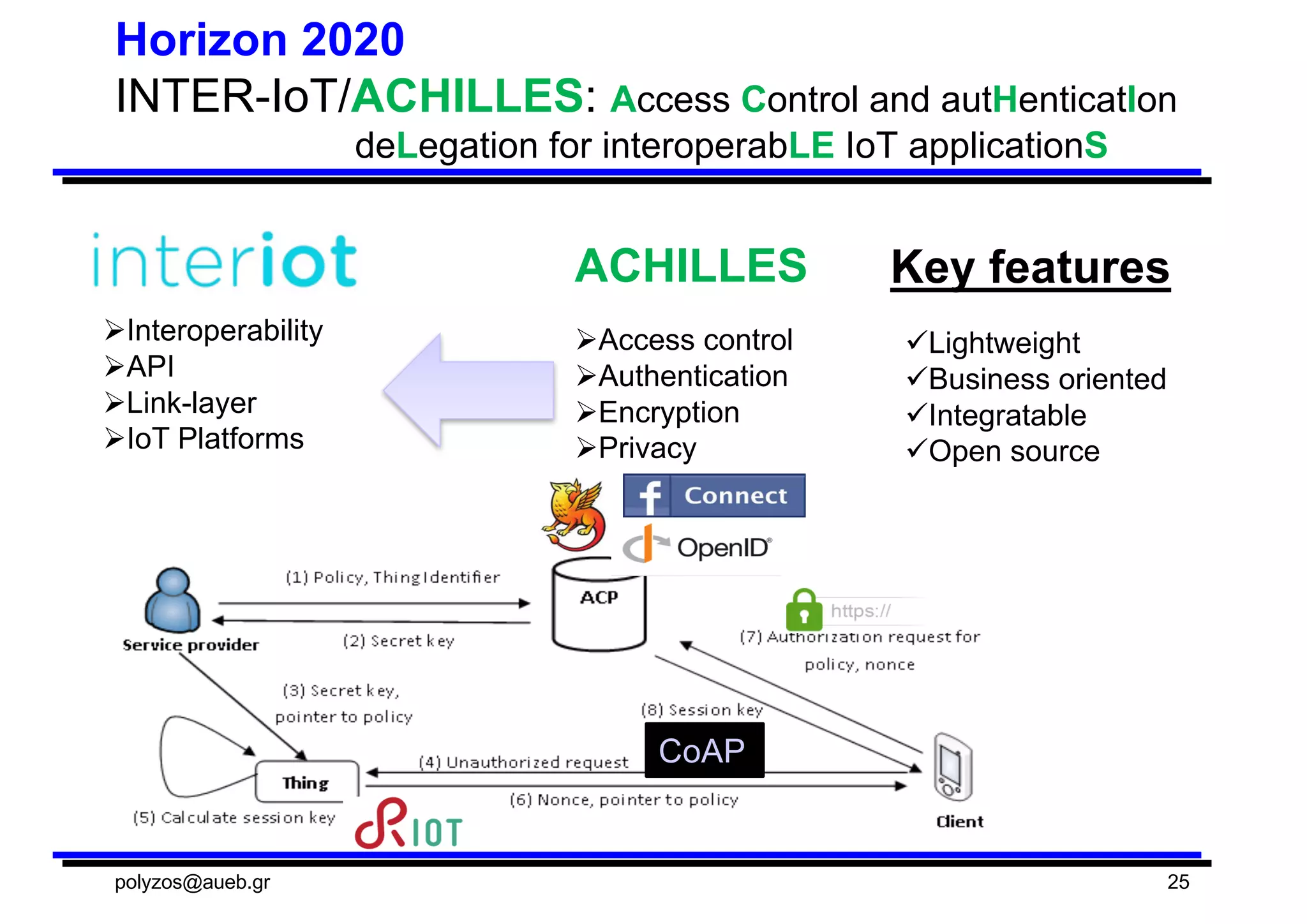
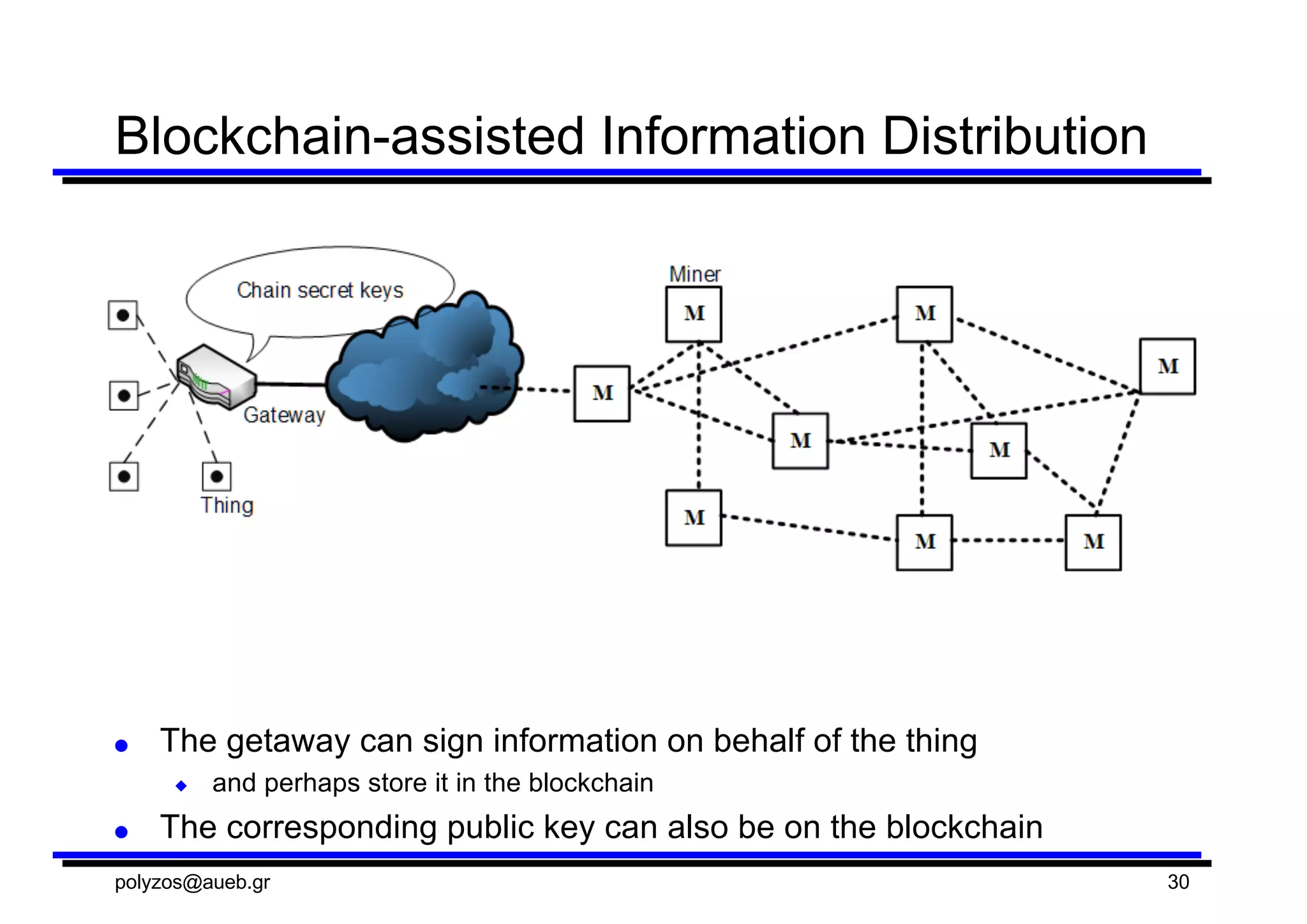
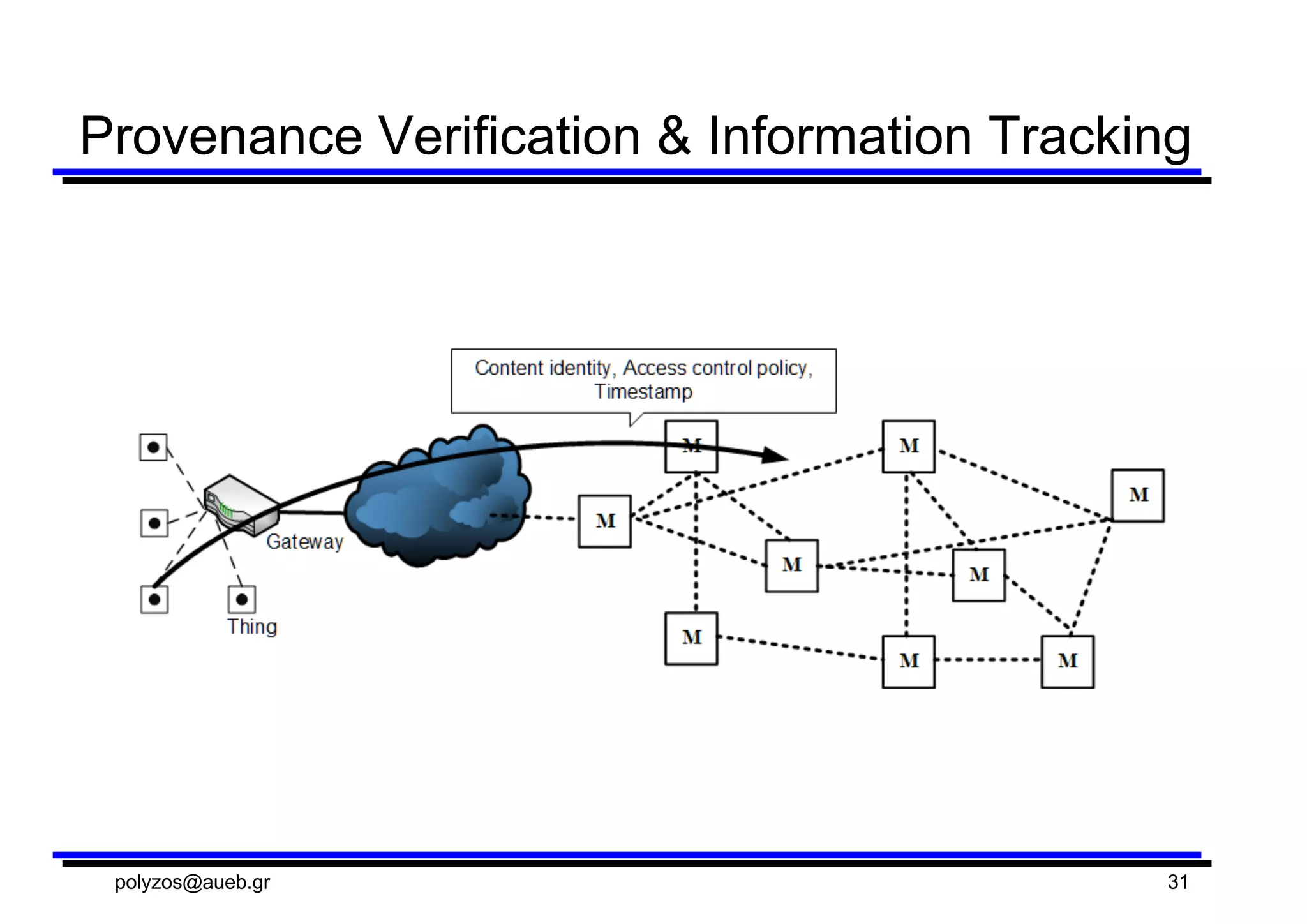
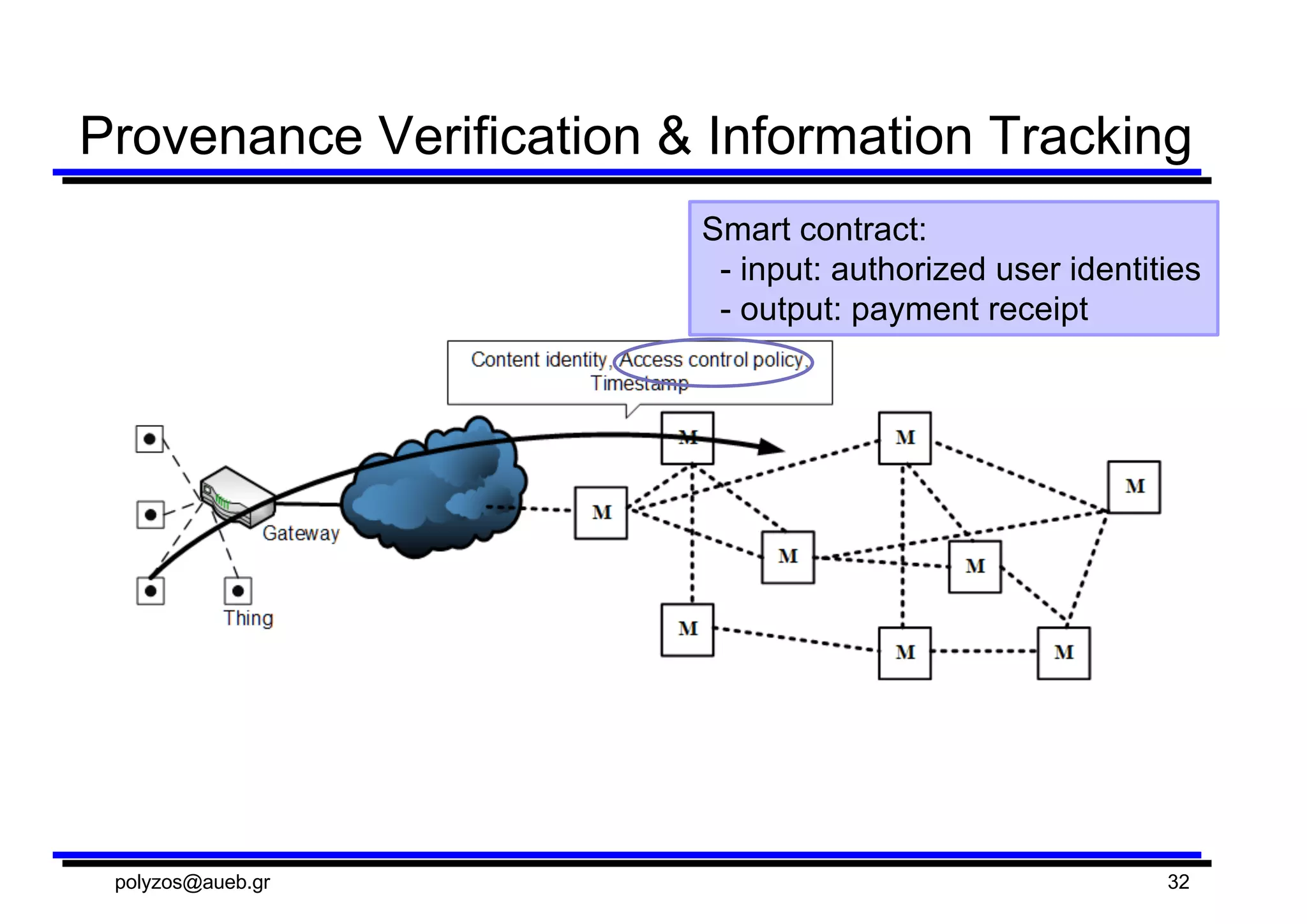
The document discusses the SOFIE project, which aims to securely federate different IoT platforms using distributed ledger technology. SOFIE will prototype applying blockchains to interconnect diverse IoT systems, provide metadata about platforms, and securely record transactions. It will include pilots involving smart meters, electricity marketplaces, food supply chains, and mixed reality gaming.