FY19_RVAs_Mapped_to_the_MITRE_ATTCK_Framework_508.pdf
•
0 likes•1 view
Rty
Report
Share
Report
Share
Download to read offline
Recommended
Recommended
Cisco Connect 2018 Thailand Cisco Connect 2018 Thailand - Security automation and programmability mr. kho...

Cisco Connect 2018 Thailand - Security automation and programmability mr. kho...NetworkCollaborators
More Related Content
Similar to FY19_RVAs_Mapped_to_the_MITRE_ATTCK_Framework_508.pdf
Cisco Connect 2018 Thailand Cisco Connect 2018 Thailand - Security automation and programmability mr. kho...

Cisco Connect 2018 Thailand - Security automation and programmability mr. kho...NetworkCollaborators
Similar to FY19_RVAs_Mapped_to_the_MITRE_ATTCK_Framework_508.pdf (20)
Evolution of Offensive Testing - ATT&CK-based Adversary Emulation Plans

Evolution of Offensive Testing - ATT&CK-based Adversary Emulation Plans
3 steps to 4x the risk coverage of CA ControlMinder

3 steps to 4x the risk coverage of CA ControlMinder
Cisco Connect 2018 Thailand - Security automation and programmability mr. kho...

Cisco Connect 2018 Thailand - Security automation and programmability mr. kho...
Cisco Connect 2018 Thailand - Telco service provider network analytics 

Cisco Connect 2018 Thailand - Telco service provider network analytics
More from sikandar girgoukar
More from sikandar girgoukar (9)
Engineering process in detail with block diagram and explanation

Engineering process in detail with block diagram and explanation
2211-III-IV-Info-Security-061cab6ee6c0fb0-53969879.ppt

2211-III-IV-Info-Security-061cab6ee6c0fb0-53969879.ppt
ISO27k ISMS Mandatory documentation checklist release 1v1 (2).docx

ISO27k ISMS Mandatory documentation checklist release 1v1 (2).docx
Recently uploaded
Call girls in delhi ✔️✔️🔝 9953056974 🔝✔️✔️Welcome To Vip Escort Services In Delhi [ ]Noida Gurgaon 24/7 Open Sex Escort Services With Happy Ending ServiCe Done By Most Attractive Charming Soft Spoken Bold Beautiful Full Cooperative Independent Escort Girls ServiCe In All-Star Hotel And Home Service In All Over Delhi, Noida, Gurgaon, Faridabad, Ghaziabad, Greater Noida,
• IN CALL AND OUT CALL SERVICE IN DELHI NCR
• 3* 5* 7* HOTELS SERVICE IN DELHI NCR
• 24 HOURS AVAILABLE IN DELHI NCR
• INDIAN, RUSSIAN, PUNJABI, KASHMIRI ESCORTS
• REAL MODELS, COLLEGE GIRLS, HOUSE WIFE, ALSO AVAILABLE
• SHORT TIME AND FULL TIME SERVICE AVAILABLE
• HYGIENIC FULL AC NEAT AND CLEAN ROOMS AVAIL. IN HOTEL 24 HOURS
• DAILY NEW ESCORTS STAFF AVAILABLE
• MINIMUM TO MAXIMUM RANGE AVAILABLE.
Call Girls in Delhi & Independent Escort Service –
CALL GIRLS SERVICE DELHI NCR
Vip call girls in Delhi
Call Girls in Delhi, Call Girl Service 24×7 open
Call Girls in Delhi Best Delhi Escorts in Delhi
Low Rate Call Girls In Saket Delhi
X~CALL GIRLS IN Ramesh Nagar Metro
best Delhi call girls and Delhi escort service.
CALL GIRLS SERVICE IN ALL DELHI …
(Delhi) Call Girls in (Chanakyapuri)
Hot And Sexy Independent Model Escort Service In Delhi Unlimited Enjoy Genuine 100% Profiles And Trusted Door Step Call Girls Feel Free To Call Us Female Service Hot Busty & Sexy Party Girls Available For Complete Enjoyment. We Guarantee Full Satisfaction & In Case Of Any Unhappy Experience, We Would Refund Your Fees, Without Any Questions Asked. Feel Free To Call Us Female Service Provider Hours Opens Thanks.
Delhi Escorts Services 100% secure Services.Incall_OutCall Available and outcall Services provide.
We are available 24*7 for Full Night and short Time Escort Services all over Delhi NCR.
Delhi All Hotel Services available 3* 4* 5* Call Call
Delhi Escorts Services And Delhi Call Girl Agency 100% secure Services in my agency. Incall and outcall Services provide.
We are available 24*7 for Full Night and short Time Escort Services my agency in all over New Delhi
Delhi All Hotel Services available my agency
SERVICES [✓✓✓]
Housewife
College Girl
VIP Escort
Independent Girl
Aunty
Without a Condom sucking )?
Sexy Aunty.DSL (Dick Sucking Lips)?
DT (Dining at the Toes English Spanking)
Doggie (Sex style from no behind)??
OutCall- All Over Delhi Noida Gurgaon 24/7
FOR APPOINTMENT Call/Whatsop / 9953056974Call Girls in Patel Nagar, Delhi 💯 Call Us 🔝9953056974 🔝 Escort Service

Call Girls in Patel Nagar, Delhi 💯 Call Us 🔝9953056974 🔝 Escort Service9953056974 Low Rate Call Girls In Saket, Delhi NCR
Call Girls Service Jammu Ishita Call Now: 8617697112 Jammu Escorts Booking Contact Details WhatsApp Chat: +91-8617697112 Jammu Escort Service includes providing maximum physical satisfaction to their clients as well as engaging conversation that keeps your time enjoyable and entertaining. Plus they look fabulously elegant; making an impressionable. Independent Escorts Jammu understands the value of confidentiality and discretion - they will go the extra mile to meet your needs. Simply contact them via text messaging or through their online profiles; they'd be more than delighted to accommodate any request or arrange a romantic date or fun-filled night together. We provide –(ISHITA) Call Girls Service Jammu Call Now 8617697112 Jammu Escorts 24x7

(ISHITA) Call Girls Service Jammu Call Now 8617697112 Jammu Escorts 24x7Call Girls in Nagpur High Profile Call Girls
Recently uploaded (20)
ELECTRICITÉ TMT 55.pdf electrick diagram manitout

ELECTRICITÉ TMT 55.pdf electrick diagram manitout
Vip Hot Call Girls 🫤 Mahipalpur ➡️ 9711199171 ➡️ Delhi 🫦 Whatsapp Number

Vip Hot Call Girls 🫤 Mahipalpur ➡️ 9711199171 ➡️ Delhi 🫦 Whatsapp Number
Call Girls Kadugodi Just Call 👗 7737669865 👗 Top Class Call Girl Service Bang...

Call Girls Kadugodi Just Call 👗 7737669865 👗 Top Class Call Girl Service Bang...
Call Girls in Malviya Nagar Delhi 💯 Call Us 🔝9205541914 🔝( Delhi) Escorts Ser...

Call Girls in Malviya Nagar Delhi 💯 Call Us 🔝9205541914 🔝( Delhi) Escorts Ser...
Top Rated Call Girls South Mumbai : 9920725232 We offer Beautiful and sexy Ca...

Top Rated Call Girls South Mumbai : 9920725232 We offer Beautiful and sexy Ca...
Is Your BMW PDC Malfunctioning Discover How to Easily Reset It

Is Your BMW PDC Malfunctioning Discover How to Easily Reset It
John Deere 7430 7530 Tractors Diagnostic Service Manual W.pdf

John Deere 7430 7530 Tractors Diagnostic Service Manual W.pdf
Call Girls in Patel Nagar, Delhi 💯 Call Us 🔝9953056974 🔝 Escort Service

Call Girls in Patel Nagar, Delhi 💯 Call Us 🔝9953056974 🔝 Escort Service
Majestic Call Girls: 🍓 7737669865 🍓 High Profile Model Escorts | Bangalore Es...

Majestic Call Girls: 🍓 7737669865 🍓 High Profile Model Escorts | Bangalore Es...
Sales & Marketing Alignment_ How to Synergize for Success.pptx.pdf

Sales & Marketing Alignment_ How to Synergize for Success.pptx.pdf
Bangalore Call Girls: 🍓 7737669865 🍓 High Profile Model Escorts | Bangalore E...

Bangalore Call Girls: 🍓 7737669865 🍓 High Profile Model Escorts | Bangalore E...
➥🔝 7737669865 🔝▻ narsinghpur Call-girls in Women Seeking Men 🔝narsinghpur🔝 ...

➥🔝 7737669865 🔝▻ narsinghpur Call-girls in Women Seeking Men 🔝narsinghpur🔝 ...
Vip Mumbai Call Girls Navi Mumbai Call On 9920725232 With Body to body massag...

Vip Mumbai Call Girls Navi Mumbai Call On 9920725232 With Body to body massag...
+971565801893>>SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN ABUDHABI,DUBAI MA...

+971565801893>>SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN ABUDHABI,DUBAI MA...
Call Girls In Kotla Mubarakpur Delhi ❤️8448577510 ⊹Best Escorts Service In 24...

Call Girls In Kotla Mubarakpur Delhi ❤️8448577510 ⊹Best Escorts Service In 24...
Escorts Service Rajajinagar ☎ 7737669865☎ Book Your One night Stand (Bangalore)

Escorts Service Rajajinagar ☎ 7737669865☎ Book Your One night Stand (Bangalore)
(ISHITA) Call Girls Service Jammu Call Now 8617697112 Jammu Escorts 24x7

(ISHITA) Call Girls Service Jammu Call Now 8617697112 Jammu Escorts 24x7
FY19_RVAs_Mapped_to_the_MITRE_ATTCK_Framework_508.pdf
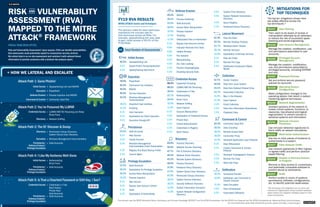
- 1. TLP:WHITE RIS AND K VULNERABILITY ASSESSMENT (RVA) MAPPED TO THE MITRE ATT&CK® FRAMEWORK FISCAL YEAR 2019 (FY19) TLP:WHITE Risk and Vulnerability Assessment: Upon request, CISA can identify vulnerabilities that adversaries could potentially exploit to compromise security controls. We collect data in an on-site assessment and combine it with national threat information to provide customers with a tailored risk analysis report. + HOW WE LATERAL AND ESCALATE Initial Access » Spearphishing Link and MSHTA Execution » PowerShell Defense Evasion » Process Injection and MSHTA Command & Control » Commonly Used Port Attack Path 1: Gone Phishin’ Attack Path 2: You’ve Poisoned My LLMNR Credential Access » LLMNR/NBT-NS Poisoning and Relay Brute Force Discovery » Network Sniffing Attack Path 3: The Ol’ Discover & Dump Discovery » Permissions Group Discovery System Owner/User Discovery Execution » Windows Management Instrumentation Persistence/ » Valid Accounts Defense Evasion/ Privilege Escalation Attack Path 4: I Like My Kerberos Well-Done Initial Access » Kerberoasting Brute Force Persistence/ » Valid Accounts Defense Evasion/ Privilege Escalation Attack Path 5: Is That a Cleartext Password or SSH Key, I See? Credential Access » Credentials in Files Bash History Private Keys Valid Accounts Persistence/ » Valid Accounts Defense Evasion/ Privilege Escalation FY19 RVA RESULTS MITRE ATT&CK Tactics and Techniques The percent noted for each technique represents the success rate for that technique across all RVAs. For example, spearphishing link was used to gain initial access in 45.5% of the FY19 RVAs. 44 Total Number of Assessments Initial Access 45.5% Spearphishing Link 4.5% Exploit Public-Facing Application 2.3% Spearphishing Attachment Execution 70.5% PowerShell 63.6% Command-Line Interface 45.5% MSHTA 45.5% Service Execution 43.2% Windows Management Instrumentation 18.2% Graphical User Interface 11.4% Scripting 9.1% User Execution 9.1% Exploitation for Client Execution 2.3% Execution through API Persistence 25.0% Valid Accounts 9.1% New Service 4.5% Create Account 2.3% Windows Management Instrumentation Event Subscription 2.3% Registry Run Keys/Startup Folder 2.3% Launch Agent Privilege Escalation 25.0% Valid Accounts 20.5% Exploitation for Privilege Escalation 20.5% Access Token Manipulation 15.9% Process Injection 9.1% New Service 9.1% Bypass User Account Control 2.3% Sudo 2.3% Exploitation of Vulnerability Defense Evasion 45.5% MSHTA 36.4% Process Hollowing 25.0% Valid Accounts 20.5% Access Token Manipulation 15.9% Process Injection 11.4% Scripting 11.4% Obfuscated Files or Information 9.1% Bypass User Account Control 6.8% Indicator Removal from Tools 6.8% Hidden Window 6.8% File Deletion 4.5% Masquerading 4.5% DLL Side-Loading 2.3% Process Dopplegänging 2.3% Disabling Security Tools Credential Access 88.6% Credential Dumping 68.2% LLMNR/NBT-NS Poisoning 38.6% Credentials in Files 22.7% Kerberoasting 20.5% Brute Force 15.9% Network Sniffing 11.4% Input Capture 9.1% Account Manipulation 4.5% Exploitation of Credential Access 2.3% Private Keys 2.3% Forced Authentication 2.3% Credentials in Registry 2.3% Bash History Discovery 63.6% Account Discovery 50.0% Network Service Scanning 47.7% File & Directory Discovery 45.5% Network Share Discovery 43.2% Remote System Discovery 40.9% Process Discovery 31.8% Password Policy Discovery 27.3% System Owner/User Discovery 27.3% Permission Groups Discovery 18.2% System Service Discovery 18.2% Security Software Discovery 13.6% System Information Discovery 11.4% System Network Configuration Discovery 4.5% System Time Discovery 4.5% System Network Connections Discovery 4.5% Query Registry 2.3% Peripheral Device Discovery Lateral Movement 61.4% Pass the Hash 52.3% Remote Desktop Protocol 22.7% Windows Admin Shares 22.7% Remote Services 13.6% Exploitation of Remote Services 9.1% Pass the Ticket 2.3% Remote File Copy 2.3% Distributed Component Object Model Collection 47.7% Screen Capture 45.5% Data from Local System 36.4% Data from Network Shared Drive 22.7% Automated Collection 11.4% Man in the Browser 11.4% Input Capture 2.3% Email Collection 2.3% Data from Information Repositories 2.3% Clipboard Data Command & Control 54.5% Commonly Used Port 20.5% Data Encoding 18.2% Remote Access Tools 18.2% Connection Proxy 11.4% Standard Application Layer Protocol 9.1% Data Obfuscation 9.1% Custom Command & Control Protocol 4.5% Standard Cryptographic Protocol 2.3% Remote File Copy 2.3% Multi-hop Proxy Exfiltration 18.2% Scheduled Transfer 13.6% Exfiltration over Command & Control Channel 11.4% Data Encrypted 4.5% Data Compressed 4.5% Automated Exfiltration MITIGATIONS FOR TOP TECHNIQUES The top ten mitigations shown here are widely effective across the top techniques.* *Top techniques and mitigations vary by sector and environment. Organizations should consider additional attack vectors and mitigation strategies based on their unique environment. User Training M1017 Train users to be aware of access or manipulation attempts by an adversary to reduce the risk of successful spear- phishing and social engineering. User Account Management M1018 Manage the creation, modification, use, and permissions associated to user accounts. Privileged Account Management M1026 Manage the creation, modification, use, and permissions associated to privileged accounts, including SYSTEM and root. Password Policies M1027 Set and enforce secure password policies for accounts. Operating System Configuration M1028 Make configuration changes to the operating system that result in system hardening against techniques. Network Segmentation M1030 Architect sections of the network to isolate critical systems, functions, or resources. Use physical and logical segmentation to prevent access to sensitive systems and information. Network Intrusion Prevention M1031 Use intrusion detection signatures to block traffic at network boundaries. Multi-factor Authentication M1032 Use two or more pieces of evidence to authenticate to a system. Filter Network Traffic M1037 Use network appliances to filter ingress or egress traffic and perform protocol- based filtering. Disable or Remove Feature or Program M1042 Remove or deny access to unnecessary and potentially vulnerable software to prevent abuse by adversaries. Audit M1047 Perform audits or scans of systems, permissions, software, configurations, etc. to identify potential weaknesses. This advisory uses the MITRE Adversarial Tactics, Techniques, and Common Knowledge (ATT&CK®) and Pre-ATT&CK frameworks. See the ATT&CK for Enterprise and Pre-ATT&CK frameworks for referenced threat actor techniques. For more information about CISA assessment services, please visit https://www.cisa.gov/
