Security and Your Business
•
1 like•239 views
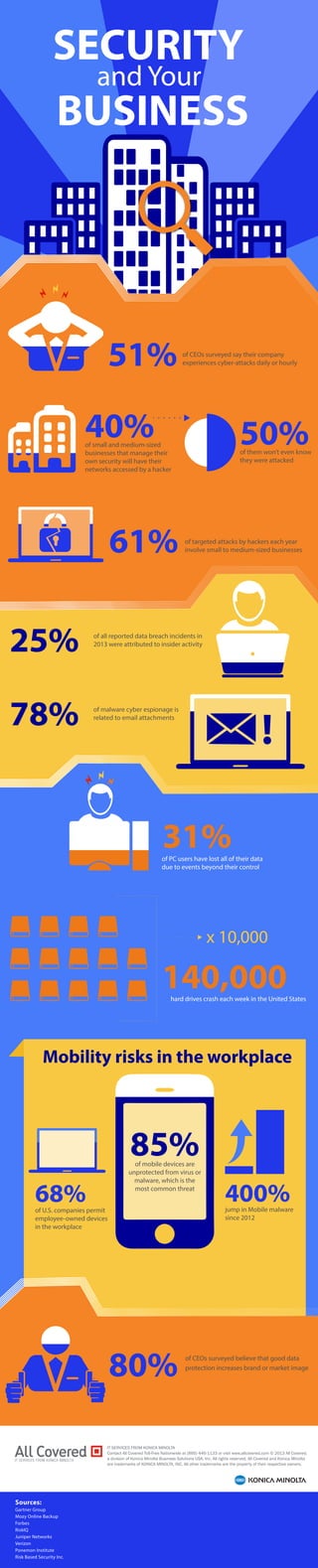
Don’t be next! More and more security breaches are happening every day. Regardless if you are a small, medium, or large company, the risk is always there. Don’t believe us? Take a look at our infographic and check out some of the eye-opening stats!
Report
Share
Report
Share
Download to read offline
Recommended
More Related Content
What's hot
What's hot (20)
Why Your Mobile Device Isn’t As Secure As You Think

Why Your Mobile Device Isn’t As Secure As You Think
Top Seven Risks of Enterprise Mobility - How to protect your business

Top Seven Risks of Enterprise Mobility - How to protect your business
Cybersecurity threats you should know about in 2018

Cybersecurity threats you should know about in 2018
Deutsche Telekom Partnering Operating Alliance Summit - Zimperium

Deutsche Telekom Partnering Operating Alliance Summit - Zimperium
Ms810 assignment viruses and malware affecting moblie devices

Ms810 assignment viruses and malware affecting moblie devices
Symantec Internet Security Threat Report 2014 - Volume 19

Symantec Internet Security Threat Report 2014 - Volume 19
Lookout Mobile Endpoint Security Datasheet (US - v2.5)

Lookout Mobile Endpoint Security Datasheet (US - v2.5)
Cyber Security Analytics – The Weapon to Fight Cyber Crime 

Cyber Security Analytics – The Weapon to Fight Cyber Crime
Viewers also liked
Viewers also liked (13)
Protecting Your Business - All Covered Security Services

Protecting Your Business - All Covered Security Services
Similar to Security and Your Business
Similar to Security and Your Business (20)
Top 10 Cybersecurity Trends to Watch Out For in 2022

Top 10 Cybersecurity Trends to Watch Out For in 2022
IS Decisions Company Overview. Solutions to secure your Windows Network.

IS Decisions Company Overview. Solutions to secure your Windows Network.
AI IN CYBERSECURITY: THE NEW FRONTIER OF DIGITAL PROTECTION

AI IN CYBERSECURITY: THE NEW FRONTIER OF DIGITAL PROTECTION
Securing mobile devices in the business environment

Securing mobile devices in the business environment
What Are Cyber Attacks All About? | Cyberroot Risk Advisory

What Are Cyber Attacks All About? | Cyberroot Risk Advisory
Recently uploaded
Best Practices for Implementing an External Recruiting Partnership

Best Practices for Implementing an External Recruiting PartnershipRecruitment Process Outsourcing Association
Enjoy ➥8448380779▻ Call Girls In Sector 18 Noida Escorts Delhi NCR

Enjoy ➥8448380779▻ Call Girls In Sector 18 Noida Escorts Delhi NCRStunning ➥8448380779▻ Call Girls In Hauz Khas Delhi NCR
Recently uploaded (20)
Best Practices for Implementing an External Recruiting Partnership

Best Practices for Implementing an External Recruiting Partnership
Lowrate Call Girls In Sector 18 Noida ❤️8860477959 Escorts 100% Genuine Servi...

Lowrate Call Girls In Sector 18 Noida ❤️8860477959 Escorts 100% Genuine Servi...
Enjoy ➥8448380779▻ Call Girls In Sector 18 Noida Escorts Delhi NCR

Enjoy ➥8448380779▻ Call Girls In Sector 18 Noida Escorts Delhi NCR
Call Girls In Sikandarpur Gurgaon ❤️8860477959_Russian 100% Genuine Escorts I...

Call Girls In Sikandarpur Gurgaon ❤️8860477959_Russian 100% Genuine Escorts I...
The CMO Survey - Highlights and Insights Report - Spring 2024

The CMO Survey - Highlights and Insights Report - Spring 2024
Call Girls in DELHI Cantt, ( Call Me )-8377877756-Female Escort- In Delhi / Ncr

Call Girls in DELHI Cantt, ( Call Me )-8377877756-Female Escort- In Delhi / Ncr
Tech Startup Growth Hacking 101 - Basics on Growth Marketing

Tech Startup Growth Hacking 101 - Basics on Growth Marketing
Call Girls Miyapur 7001305949 all area service COD available Any Time

Call Girls Miyapur 7001305949 all area service COD available Any Time
VIP Call Girl Jamshedpur Aashi 8250192130 Independent Escort Service Jamshedpur

VIP Call Girl Jamshedpur Aashi 8250192130 Independent Escort Service Jamshedpur
RE Capital's Visionary Leadership under Newman Leech

RE Capital's Visionary Leadership under Newman Leech
VIP Kolkata Call Girl Howrah 👉 8250192130 Available With Room

VIP Kolkata Call Girl Howrah 👉 8250192130 Available With Room
BEST Call Girls In Greater Noida ✨ 9773824855 ✨ Escorts Service In Delhi Ncr,

BEST Call Girls In Greater Noida ✨ 9773824855 ✨ Escorts Service In Delhi Ncr,
Lean: From Theory to Practice — One City’s (and Library’s) Lean Story… Abridged

Lean: From Theory to Practice — One City’s (and Library’s) Lean Story… Abridged
Sales & Marketing Alignment: How to Synergize for Success

Sales & Marketing Alignment: How to Synergize for Success
NewBase 22 April 2024 Energy News issue - 1718 by Khaled Al Awadi (AutoRe...

NewBase 22 April 2024 Energy News issue - 1718 by Khaled Al Awadi (AutoRe...
(8264348440) 🔝 Call Girls In Mahipalpur 🔝 Delhi NCR

(8264348440) 🔝 Call Girls In Mahipalpur 🔝 Delhi NCR
Security and Your Business
- 1. SECURITY and Your BUSINESS of all reported data breach incidents in 2013 were attributed to insider activity of malware cyber espionage is related to email attachments 31% 50% of them won’t even know they were attacked of PC users have lost all of their data due to events beyond their control x 10,000 40% of small and medium-sized businesses that manage their own security will have their networks accessed by a hacker 140,000 Mobility risks in the workplace IT SERVICES FROM KONICA MINOLTA Contact All Covered Toll-Free Nationwide at (866) 446-1133 or visit www.allcovered.com © 2013 All Covered, a division of Konica Minolta Business Solutions USA, Inc. All rights reserved. All Covered and Konica Minolta are trademarks of KONICA MINOLTA, INC. All other trademarks are the property of their respective owners. Sources: Gartner Group Mozy Online Backup Forbes RiskIQ Juniper Networks Verizon Ponemon Institute Risk Based Security Inc. of targeted attacks by hackers each year involve small to medium-sized businesses 85% of mobile devices are unprotected from virus or malware, which is the 68% most common threat of U.S. companies permit employee-owned devices in the workplace 400% jump in Mobile malware since 2012 51% 61% of CEOs surveyed say their company experiences cyber-attacks daily or hourly hard drives crash each week in the United States 25% 78% 80% of CEOs surveyed believe that good data protection increases brand or market image
