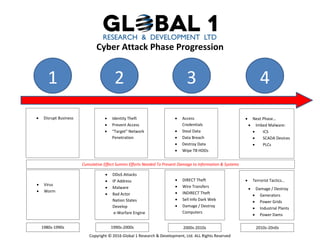
Cyber Attack Phase Progression
•
0 likes•117 views
The document outlines the typical 4 phase progression of a cyber attack: 1) disrupt business and prevent access, 2) access credentials and steal data, 3) embed malware on industrial control systems and devices, and 4) directly damage or destroy infrastructure through computer networks or sell stolen information. It notes how cyber attacks have evolved over the decades to cause greater damage and disruption.
Report
Share
Report
Share
Download to read offline
Recommended
Cyber Security in the Manufacturing Industry: New challenges in the informati...

Cyber Security in the Manufacturing Industry: New challenges in the informati...Ekonomikas ministrija
More Related Content
What's hot
Cyber Security in the Manufacturing Industry: New challenges in the informati...

Cyber Security in the Manufacturing Industry: New challenges in the informati...Ekonomikas ministrija
What's hot (20)
Cybersecurity threats you should know about in 2018

Cybersecurity threats you should know about in 2018
Cyber Security in the Manufacturing Industry: New challenges in the informati...

Cyber Security in the Manufacturing Industry: New challenges in the informati...
More from William Kiss
More from William Kiss (8)
Cyber Attack Phase Progression
- 1. Copyright © 2016 Global 1 Research & Development, Ltd. ALL Rights Reserved Cyber Attack Phase Progression 1 2 3 4 Disrupt Business Identity Theft Prevent Access “Target” Network Penetration Access Credentials Steal Data Data Breach Destroy Data Wipe TB HDDs Next Phase… Imbed Malware: ICS SCADA Devices PLCs Virus Worm DDoS Attacks IP Address Malware Bad Actor Nation States Develop e-Warfare Engine DIRECT Theft Wire Transfers INDIRECT Theft Sell Info Dark Web Damage / Destroy Computers Terrorist Tactics… Damage / Destroy Generators Power Grids Industrial Plants Power Dams 1980s-1990s 1990s-2000s 2000s-2010s 2010s-20n0s Cumulative Effect Summs Efforts Needed To Prevent Damage to Information & Systems
