7 Undeniable Truths to Making Software Security Better
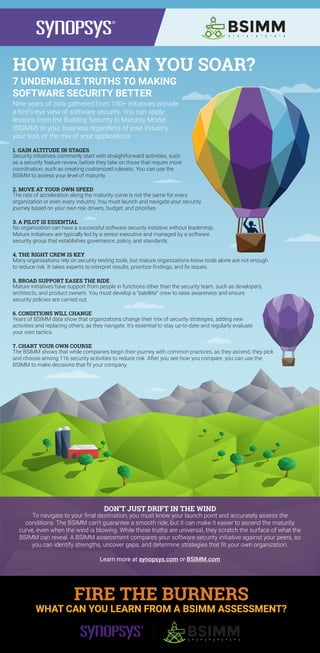
The document discusses 7 truths for improving software security based on data from the Building Security In Maturity Model (BSIMM). It summarizes that security initiatives commonly start with straightforward activities and gain altitude in stages; organizations move at their own speed along the maturity curve; leadership from a senior executive and a software security group is essential; using security testing tools alone is not enough and experts are needed; broad support from other teams helps reduce risk; strategies need to change as conditions change; and each organization can choose tactics that fit its needs after assessing its maturity. A BSIMM assessment compares an organization's initiative to peers to identify strengths, gaps, and strategies tailored to it.
Recommended
More Related Content
What's hot
What's hot (9)
Similar to 7 Undeniable Truths to Making Software Security Better
Similar to 7 Undeniable Truths to Making Software Security Better (20)
More from Synopsys Software Integrity Group
More from Synopsys Software Integrity Group (20)
Recently uploaded
Recently uploaded (20)
7 Undeniable Truths to Making Software Security Better
- 1. HOW HIGH CAN YOU SOAR? 7 UNDENIABLE TRUTHS TO MAKING SOFTWARE SECURITY BETTER Nine years of data gathered from 100+ initiatives provide a bird’s-eye view of software security. You can apply lessons from the Building Security In Maturity Model (BSIMM) to your business regardless of your industry, your size, or the mix of your applications. 1. GAIN ALTITUDE IN STAGES Security initiatives commonly start with straightforward activities, such as a security feature review, before they take on those that require more coordination, such as creating customized rulesets. You can use the BSIMM to assess your level of maturity. 2. MOVE AT YOUR OWN SPEED The rate of acceleration along the maturity curve is not the same for every organization or even every industry. You must launch and navigate your security journey based on your own risk drivers, budget, and priorities. 3. A PILOT IS ESSENTIAL No organization can have a successful software security initiative without leadership. Mature initiatives are typically led by a senior executive and managed by a software security group that establishes governance, policy, and standards. 4. THE RIGHT CREW IS KEY Many organizations rely on security testing tools, but mature organizations know tools alone are not enough to reduce risk. It takes experts to interpret results, prioritize findings, and fix issues. 5. BROAD SUPPORT EASES THE RIDE Mature initiatives have support from people in functions other than the security team, such as developers, architects, and product owners. You must develop a “satellite” crew to raise awareness and ensure security policies are carried out. 6. CONDITIONS WILL CHANGE Years of BSIMM data show that organizations change their mix of security strategies, adding new activities and replacing others, as they navigate. It’s essential to stay up-to-date and regularly evaluate your own tactics. 7. CHART YOUR OWN COURSE The BSIMM shows that while companies begin their journey with common practices, as they ascend, they pick and choose among 116 security activities to reduce risk. After you see how you compare, you can use the BSIMM to make decisions that fit your company. DON’T JUST DRIFT IN THE WIND To navigate to your final destination, you must know your launch point and accurately assess the conditions. The BSIMM can’t guarantee a smooth ride, but it can make it easier to ascend the maturity curve, even when the wind is blowing. While these truths are universal, they scratch the surface of what the BSIMM can reveal. A BSIMM assessment compares your software security initiative against your peers, so you can identify strengths, uncover gaps, and determine strategies that fit your own organization. Learn more at synopsys.com or BSIMM.com FIRE THE BURNERS WHAT CAN YOU LEARN FROM A BSIMM ASSESSMENT?
