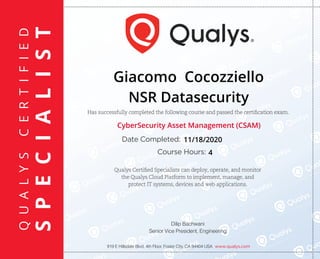
CyberSecurity Asset Management (CSAM).pdf
- 1. P E C I A L I S T C E R T I F I E D S P E C I A L I S T P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T S P E C I A L I S T E C I A L I S T E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T I E D S P E C I A L I S T C E R T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T T I F I E D S P E C C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C E C E R T I F I E D S P E C I C E R T I F I E D S P E C I A L I S T C E R T I F I E D S P E C C E R T I F I E D S P E C I C E R T Q U A L Y S C E R T I F I E D S P E C I A L I S T Has successfully completed the following course and passed the certification exam. 919 E Hillsdale Blvd, 4th Floor, Foster City, CA 94404 USA www.qualys.com Date Completed: Course Hours: Qualys Certified Specialists can deploy, operate, and monitor the Qualys Cloud Platform to implement, manage, and protect IT systems, devices and web applications. Dilip Bachwani Senior Vice President, Engineering Giacomo Cocozziello NSR Datasecurity CyberSecurity Asset Management (CSAM) 11/18/2020 4