Dinis Cruz (CV) - CISO and Transformation Agent v1.2
•
2 likes•1,767 views
Here is my CV (this format is much easier to consume than documents) You can reach me on LinkedIn (https://www.linkedin.com/in/diniscruz/) , twitter (https://twitter.com/diniscruz) or email (dinis.cruz@owasp.org) Created on 30 Oct 2019
Report
Share
Report
Share
Download to read offline
Recommended
Recommended
More Related Content
What's hot
What's hot (20)
Managing & Showing Value during Red Team Engagements & Purple Team Exercises ...

Managing & Showing Value during Red Team Engagements & Purple Team Exercises ...
Understanding The Security Vendor Landscape Using the Cyber Defense Matrix (R...

Understanding The Security Vendor Landscape Using the Cyber Defense Matrix (R...
Managing and Securing Remote Access To Critical Infrastructure, Yariv Lenchne...

Managing and Securing Remote Access To Critical Infrastructure, Yariv Lenchne...
Cybersecurity Frameworks | NIST Cybersecurity Framework | Cybersecurity Certi...

Cybersecurity Frameworks | NIST Cybersecurity Framework | Cybersecurity Certi...
Putting MITRE ATT&CK into Action with What You Have, Where You Are

Putting MITRE ATT&CK into Action with What You Have, Where You Are
Proactive Threat Hunting: Game-Changing Endpoint Protection Beyond Alerting

Proactive Threat Hunting: Game-Changing Endpoint Protection Beyond Alerting
Putting Firepower Into The Next Generation Firewall

Putting Firepower Into The Next Generation Firewall
Boardroom to War Room: Practical Application of the NIST Cybersecurity Frame...

Boardroom to War Room: Practical Application of the NIST Cybersecurity Frame...
Similar to Dinis Cruz (CV) - CISO and Transformation Agent v1.2
Similar to Dinis Cruz (CV) - CISO and Transformation Agent v1.2 (20)
(OLD VERSION) Dinis Cruz (CV) - CISO and Transformation Agent v0.6 

(OLD VERSION) Dinis Cruz (CV) - CISO and Transformation Agent v0.6
Choreo - Build unique digital experiences on WSO2's platform, secured by Etho...

Choreo - Build unique digital experiences on WSO2's platform, secured by Etho...
Upskilling: Adapting Humans At The Speed of DevOps

Upskilling: Adapting Humans At The Speed of DevOps
Developers Driving DevOps at Scale: 5 Keys to Success

Developers Driving DevOps at Scale: 5 Keys to Success
CloudNativeLondon 2018: "In Search of the Perfect Cloud Native Developer Expe...

CloudNativeLondon 2018: "In Search of the Perfect Cloud Native Developer Expe...
More from Dinis Cruz
More from Dinis Cruz (20)
Map camp - Why context is your crown jewels (Wardley Maps and Threat Modeling)

Map camp - Why context is your crown jewels (Wardley Maps and Threat Modeling)
Glasswall - Safety and Integrity Through Trusted Files

Glasswall - Safety and Integrity Through Trusted Files
Glasswall - How to Prevent, Detect and React to Ransomware incidents

Glasswall - How to Prevent, Detect and React to Ransomware incidents
The benefits of police and industry investigation - NPCC Conference

The benefits of police and industry investigation - NPCC Conference
Serverless Security Workflows - cyber talks - 19th nov 2019

Serverless Security Workflows - cyber talks - 19th nov 2019
Making fact based decisions and 4 board decisions (Oct 2019)

Making fact based decisions and 4 board decisions (Oct 2019)
Using OWASP Security Bot (OSBot) to make Fact Based Security Decisions

Using OWASP Security Bot (OSBot) to make Fact Based Security Decisions
GSBot Commands (Slack Bot used to access Jira data)

GSBot Commands (Slack Bot used to access Jira data)
OSBot - Data transformation workflow (from GSheet to Jupyter)

OSBot - Data transformation workflow (from GSheet to Jupyter)
Jira schemas - Open Security Summit (Working Session 21th May 2019)

Jira schemas - Open Security Summit (Working Session 21th May 2019)
Template for "Sharing anonymised risk theme dashboards v0.8"

Template for "Sharing anonymised risk theme dashboards v0.8"
Evolving challenges for modern enterprise architectures in the age of APIs

Evolving challenges for modern enterprise architectures in the age of APIs
How to not fail at security data analytics (by CxOSidekick)

How to not fail at security data analytics (by CxOSidekick)
Using security to drive chaos engineering - April 2018

Using security to drive chaos engineering - April 2018
Recently uploaded
💉💊+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHABI}}+971581248768
+971581248768 Mtp-Kit (500MG) Prices » Dubai [(+971581248768**)] Abortion Pills For Sale In Dubai, UAE, Mifepristone and Misoprostol Tablets Available In Dubai, UAE CONTACT DR.Maya Whatsapp +971581248768 We Have Abortion Pills / Cytotec Tablets /Mifegest Kit Available in Dubai, Sharjah, Abudhabi, Ajman, Alain, Fujairah, Ras Al Khaimah, Umm Al Quwain, UAE, Buy cytotec in Dubai +971581248768''''Abortion Pills near me DUBAI | ABU DHABI|UAE. Price of Misoprostol, Cytotec” +971581248768' Dr.DEEM ''BUY ABORTION PILLS MIFEGEST KIT, MISOPROTONE, CYTOTEC PILLS IN DUBAI, ABU DHABI,UAE'' Contact me now via What's App…… abortion Pills Cytotec also available Oman Qatar Doha Saudi Arabia Bahrain Above all, Cytotec Abortion Pills are Available In Dubai / UAE, you will be very happy to do abortion in Dubai we are providing cytotec 200mg abortion pill in Dubai, UAE. Medication abortion offers an alternative to Surgical Abortion for women in the early weeks of pregnancy. We only offer abortion pills from 1 week-6 Months. We then advise you to use surgery if its beyond 6 months. Our Abu Dhabi, Ajman, Al Ain, Dubai, Fujairah, Ras Al Khaimah (RAK), Sharjah, Umm Al Quwain (UAQ) United Arab Emirates Abortion Clinic provides the safest and most advanced techniques for providing non-surgical, medical and surgical abortion methods for early through late second trimester, including the Abortion By Pill Procedure (RU 486, Mifeprex, Mifepristone, early options French Abortion Pill), Tamoxifen, Methotrexate and Cytotec (Misoprostol). The Abu Dhabi, United Arab Emirates Abortion Clinic performs Same Day Abortion Procedure using medications that are taken on the first day of the office visit and will cause the abortion to occur generally within 4 to 6 hours (as early as 30 minutes) for patients who are 3 to 12 weeks pregnant. When Mifepristone and Misoprostol are used, 50% of patients complete in 4 to 6 hours; 75% to 80% in 12 hours; and 90% in 24 hours. We use a regimen that allows for completion without the need for surgery 99% of the time. All advanced second trimester and late term pregnancies at our Tampa clinic (17 to 24 weeks or greater) can be completed within 24 hours or less 99% of the time without the need surgery. The procedure is completed with minimal to no complications. Our Women's Health Center located in Abu Dhabi, United Arab Emirates, uses the latest medications for medical abortions (RU-486, Mifeprex, Mifegyne, Mifepristone, early options French abortion pill), Methotrexate and Cytotec (Misoprostol). The safety standards of our Abu Dhabi, United Arab Emirates Abortion Doctors remain unparalleled. They consistently maintain the lowest complication rates throughout the nation. Our Physicians and staff are always available to answer questions and care for women in one of the most difficult times in their lives. The decision to have an abortion at the Abortion Cl+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...

+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...?#DUbAI#??##{{(☎️+971_581248768%)**%*]'#abortion pills for sale in dubai@
Recently uploaded (20)
Connector Corner: Accelerate revenue generation using UiPath API-centric busi...

Connector Corner: Accelerate revenue generation using UiPath API-centric busi...
Polkadot JAM Slides - Token2049 - By Dr. Gavin Wood

Polkadot JAM Slides - Token2049 - By Dr. Gavin Wood
TrustArc Webinar - Stay Ahead of US State Data Privacy Law Developments

TrustArc Webinar - Stay Ahead of US State Data Privacy Law Developments
+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...

+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...
Boost Fertility New Invention Ups Success Rates.pdf

Boost Fertility New Invention Ups Success Rates.pdf
Navi Mumbai Call Girls 🥰 8617370543 Service Offer VIP Hot Model

Navi Mumbai Call Girls 🥰 8617370543 Service Offer VIP Hot Model
Strategies for Landing an Oracle DBA Job as a Fresher

Strategies for Landing an Oracle DBA Job as a Fresher
Apidays New York 2024 - Scaling API-first by Ian Reasor and Radu Cotescu, Adobe

Apidays New York 2024 - Scaling API-first by Ian Reasor and Radu Cotescu, Adobe
Apidays Singapore 2024 - Scalable LLM APIs for AI and Generative AI Applicati...

Apidays Singapore 2024 - Scalable LLM APIs for AI and Generative AI Applicati...
AWS Community Day CPH - Three problems of Terraform

AWS Community Day CPH - Three problems of Terraform
Repurposing LNG terminals for Hydrogen Ammonia: Feasibility and Cost Saving

Repurposing LNG terminals for Hydrogen Ammonia: Feasibility and Cost Saving
ICT role in 21st century education and its challenges

ICT role in 21st century education and its challenges
Axa Assurance Maroc - Insurer Innovation Award 2024

Axa Assurance Maroc - Insurer Innovation Award 2024
Strategize a Smooth Tenant-to-tenant Migration and Copilot Takeoff

Strategize a Smooth Tenant-to-tenant Migration and Copilot Takeoff
Dinis Cruz (CV) - CISO and Transformation Agent v1.2
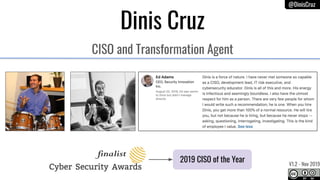
- 1. @DinisCruz Dinis Cruz CISO and Transformation Agent 2019 CISO of the Year V1.2 - Nov 2019
- 2. @DinisCruz Rare combination of management experience with deep technical skills CISO Board Member Dir. Advanced Tech Project leader and main developer CTO Can code in: Python, C#, Coffeescript, Javascript, Bash, Java, Groovy, Go, C++, PHP, Ruby, Swift, SQL, Perl, Clipper, Assembly (m68k and x86), Delphi, Pascal and Basic
- 3. @DinisCruz Respected by peers and team members
- 5. @DinisCruz Mentor talent and Created diverse teams
- 6. @DinisCruz Strategy Risk Dashboards Create strong team Graph everything Modern CISO Services Driven
- 7. @DinisCruz Created OWASP Summit* event. Motivated 100+ Security professionals to collaborate together, and release knowledge/code under Open Source (or Creative Commons) * now called Open Security Summit
- 10. @DinisCruz Thinks in Graphs and Maps
- 12. @DinisCruz LinkedIn, GitHub, Twitter, Blog, Email http://www.linkedin.com/in/diniscruz https://twitter.com/DinisCruz http://github.com/diniscruz http://blog.diniscruz.com/ dinis.cruz@owasp.org
