Software for Finding vulnerabilities in programs.pdf
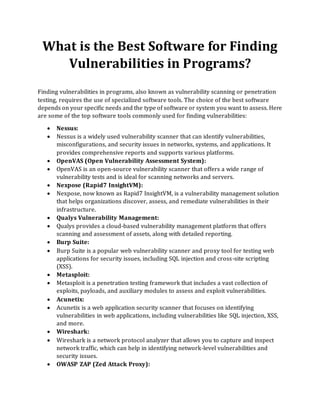
- 1. What is the Best Software for Finding Vulnerabilities in Programs? Finding vulnerabilities in programs, also known as vulnerability scanning or penetration testing, requires the use of specialized software tools. The choice of the best software depends on your specific needs and the type of software or system you want to assess. Here are some of the top software tools commonly used for finding vulnerabilities: • Nessus: • Nessus is a widely used vulnerability scanner that can identify vulnerabilities, misconfigurations, and security issues in networks, systems, and applications. It provides comprehensive reports and supports various platforms. • OpenVAS (Open Vulnerability Assessment System): • OpenVAS is an open-source vulnerability scanner that offers a wide range of vulnerability tests and is ideal for scanning networks and servers. • Nexpose (Rapid7 InsightVM): • Nexpose, now known as Rapid7 InsightVM, is a vulnerability management solution that helps organizations discover, assess, and remediate vulnerabilities in their infrastructure. • Qualys Vulnerability Management: • Qualys provides a cloud-based vulnerability management platform that offers scanning and assessment of assets, along with detailed reporting. • Burp Suite: • Burp Suite is a popular web vulnerability scanner and proxy tool for testing web applications for security issues, including SQL injection and cross-site scripting (XSS). • Metasploit: • Metasploit is a penetration testing framework that includes a vast collection of exploits, payloads, and auxiliary modules to assess and exploit vulnerabilities. • Acunetix: • Acunetix is a web application security scanner that focuses on identifying vulnerabilities in web applications, including vulnerabilities like SQL injection, XSS, and more. • Wireshark: • Wireshark is a network protocol analyzer that allows you to capture and inspect network traffic, which can help in identifying network-level vulnerabilities and security issues. • OWASP ZAP (Zed Attack Proxy):
- 2. • OWASP ZAP is an open-source web application security scanner that helps you find vulnerabilities in web applications by performing automated and manual testing. • Snort: • Snort is an open-source intrusion detection and prevention system (IDPS) that can be used to monitor network traffic for suspicious activity and potential vulnerabilities. • Qualys Web Application Scanning: • This tool specializes in scanning and assessing web applications for security vulnerabilities and weaknesses. • Retina CS: • Retina CS by BeyondTrust is a vulnerability management solution that provides comprehensive scanning, assessment, and reporting capabilities. • Aircrack-ng: • Aircrack-ng is a set of tools for assessing Wi-Fi network security, including cracking WEP and WPA/WPA2 keys and performing various network attacks. When choosing a vulnerability scanning tool, consider factors such as your budget, the types of systems and applications you need to assess, the level of automation required, and the depth of reporting. Many organizations use a combination of these tools to conduct thorough vulnerability assessments and penetration tests. Additionally, it's crucial to follow ethical hacking and responsible disclosure practices when performing security assessments on systems that you do not own or have explicit permission to test. Bytecode security provides 1 year diploma course in cybersecurity field. If you are looking for best career opportunity , you can enroll now 9513805401
