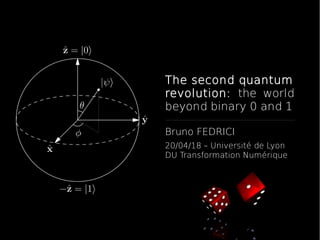
The second quantum revolution: the world beyond binary 0 and 1
- 1. The second quantum revolution: the world beyond binary 0 and 1 Bruno FEDRICI 20/04/18 – Université de Lyon DU Transformation Numérique
- 3. First half of the 20th century, discovery of fundamental laws of the microscopic realm Formulation of quantum physics
- 4. Ground-breaking technologies such as transistor (1947) and laser (1960)
- 5. Based on bulk effects where many quantum degrees of freedom are manipulated at once
- 6. “The mathematical theory of communication” C. Shannon, 1947 → source coding, channel coding, algorithmic complexity theory, algorithmic information theory, information- theoretic security, ... The age of information
- 7. Gave birth to the semiconductors and to the telecommunications industries
- 9. Technologies based on the manipulation of individual quantum systems
- 10. Technologies based on the manipulation of individual quantum systems Make use of quantum properties such as superposition and entanglement
- 11. Technologies based on the manipulation of individual quantum systems Make use of quantum properties such as superposition and entanglement Theoretically secure communications, ultimate computing power, ultraprecise sensors
- 13. Superposition – A quantum object can be in two or more states at the same time; only when a measurement is made does it fall back into a single state. If the coherence of the system is carefully maintained, superimposed states can interfere with each other with measurable consequences. This key feature enables quantum computers to go beyond the power of digital 1 and 0. It is also the source of the remarkable sensitivity of quantum sensors. 1
- 14. Superposition – A quantum object can be in two or more states at the same time; only when a measurement is made does it fall back into a single state. If the coherence of the system is carefully maintained, superimposed states can interfere with each other with measurable consequences. This key feature enables quantum computers to go beyond the power of digital 1 and 0. It is also the source of the remarkable sensitivity of quantum sensors. 1 Classical bit 0 1
- 15. Superposition – A quantum object can be in two or more states at the same time; only when a measurement is made does it fall back into a single state. If the coherence of the system is carefully maintained, superimposed states can interfere with each other with measurable consequences. This key feature enables quantum computers to go beyond the power of digital 1 and 0. It is also the source of the remarkable sensitivity of quantum sensors. 1 Classical bit 0 1 Quantum bit (Qubit) |α |2 + |β |2 = 1
- 16. Superposition – A quantum object can be in two or more states at the same time; only when a measurement is made does it fall back into a single state. If the coherence of the system is carefully maintained, superimposed states can interfere with each other with measurable consequences. This key feature enables quantum computers to go beyond the power of digital 1 and 0. It is also the source of the remarkable sensitivity of quantum sensors. 1 Classical bit 0 1 Quantum bit (Qubit) P(0) = |α |2 P(1) = |β |2 |α |2 + |β |2 = 1
- 17. Superposition – A quantum object can be in two or more states at the same time; only when a measurement is made does it fall back into a single state. If the coherence of the system is carefully maintained, superimposed states can interfere with each other with measurable consequences. This key feature enables quantum computers to go beyond the power of digital 1 and 0. It is also the source of the remarkable sensitivity of quantum sensors. 1 Blackboard ….
- 18. Indeterminacy – Quantum physics is an intrinsically probabilistic theory. The uncertainty principle tells us that it is not possible to precisely measure all properties of a quantum system at the same time; this leads to the No- Cloning Theorem: it is not possible to create an identical copy of a quantum state. This is central to quantum cryptography. 2
- 19. Indeterminacy – Quantum physics is an intrinsically probabilistic theory. The uncertainty principle tells us that it is not possible to precisely measure all properties of a quantum system at the same time; this leads to the No- Cloning Theorem: it is not possible to create an identical copy of a quantum state. This is central to quantum cryptography. 2
- 20. Indeterminacy – Quantum physics is an intrinsically probabilistic theory. The uncertainty principle tells us that it is not possible to precisely measure all properties of a quantum system at the same time; this leads to the No- Cloning Theorem: it is not possible to create an identical copy of a quantum state. This is central to quantum cryptography. 2 Blackboard ….
- 21. Entanglement – When two quantum objects are entangled they behave as one system. A measurement on one also affects the other, even if it is physically separated. This is intrinsic to the operation of quantum computers, and also to advanced forms of quantum cryptography. 3
- 22. Entanglement – When two quantum objects are entangled they behave as one system. A measurement on one also affects the other, even if it is physically separated. This is intrinsic to the operation of quantum computers, and also to advanced forms of quantum cryptography. 3 Single Q-system
- 23. Entanglement – When two quantum objects are entangled they behave as one system. A measurement on one also affects the other, even if it is physically separated. This is intrinsic to the operation of quantum computers, and also to advanced forms of quantum cryptography. 3 Single Q-system 2 Q-systems Separable state
- 24. Entanglement – When two quantum objects are entangled they behave as one system. A measurement on one also affects the other, even if it is physically separated. This is intrinsic to the operation of quantum computers, and also to advanced forms of quantum cryptography. 3 Single Q-system 2 Q-systems Separable state 2 Q-systems Entangled state
- 25. Entanglement – When two quantum objects are entangled they behave as one system. A measurement on one also affects the other, even if it is physically separated. This is intrinsic to the operation of quantum computers, and also to advanced forms of quantum cryptography. 3 Blackboard ….
- 26. Let's play with that !
- 28. Applications → Cryptography → Numerical simulations → Statistical sampling Random Numbers
- 29. Applications → Cryptography → Numerical simulations → Statistical sampling Critical that these values be → Uniform distribution → Independent Random Numbers
- 30. Applications → Cryptography → Numerical simulations → Statistical sampling Critical that these values be → Uniform distribution → Independent True random number generators provide this Random Numbers
- 31. Pseudo Random Numbers Cryptographic applications typically use algorithms for random number generation → Algorithms are deterministic and therefore produce sequences of numbers that are not trully random
- 32. Pseudo Random Numbers Cryptographic applications typically use algorithms for random number generation → Algorithms are deterministic and therefore produce sequences of numbers that are not trully random Pseudo random numbers are → Sequences produced that satisfy statistical randomness tests → Likely to be predictible
- 33. True vs Pseudo randomness Conversion to binary Deterministic algorithm Source of true randomness Seed Random bit stream Pseudo random bit stream TRNG PRNG
- 34. E.g. true random numbers from single photons and a 50:50 beam splitter: TRNG by quantum means
- 35. Single Photon Source E.g. true random numbers from single photons and a 50:50 beam splitter: TRNG by quantum means
- 36. Single Photon Source “1” E.g. true random numbers from single photons and a 50:50 beam splitter: TRNG by quantum means
- 37. Single Photon Source “0” “1” 1 0 0 1 1 0 1 0 1 0 0 E.g. true random numbers from single photons and a 50:50 beam splitter: TRNG by quantum means
- 38. Single Photon Source “0” “1” 1 0 0 1 1 0 1 0 1 0 0 E.g. true random numbers from single photons and a 50:50 beam splitter: QRNG are already commercially available → See for instance ID Quantique, Quintessence Labs, ... State of the art QRNG ~ 100 Gb/s TRNG by quantum means
- 39. https://qrng.anu.edu.au/RainBin.php To download true random numbers from quantum fluctuations of the vacuum field: TRNG by quantum means
- 41. Moore's law
- 42. R. Feynman, “Simulating physics with computers”, International Journal of Theoretical Physics, vol. 21, no. 6, pp. 467–488, 1982. D. Deutsch, “Quantum theory, the Church-Turing principle and the universal quantum computer”, Proc. R. Soc. A, vol. 400, no. 1818, pp. 97–117, 1985. Quantum Speedup
- 43. R. Feynman, “Simulating physics with computers”, International Journal of Theoretical Physics, vol. 21, no. 6, pp. 467–488, 1982. D. Deutsch, “Quantum theory, the Church-Turing principle and the universal quantum computer”, Proc. R. Soc. A, vol. 400, no. 1818, pp. 97–117, 1985. Quantum Speedup Conventional computing One out of 2N permutations → Sequential computation
- 44. R. Feynman, “Simulating physics with computers”, International Journal of Theoretical Physics, vol. 21, no. 6, pp. 467–488, 1982. D. Deutsch, “Quantum theory, the Church-Turing principle and the universal quantum computer”, Proc. R. Soc. A, vol. 400, no. 1818, pp. 97–117, 1985. Quantum Speedup Conventional computing One out of 2N permutations → Sequential computation Quantum computing All of 2N possible permutations → Parallel computation
- 45. R. Feynman, “Simulating physics with computers”, International Journal of Theoretical Physics, vol. 21, no. 6, pp. 467–488, 1982. D. Deutsch, “Quantum theory, the Church-Turing principle and the universal quantum computer”, Proc. R. Soc. A, vol. 400, no. 1818, pp. 97–117, 1985. Quantum Speedup Conventional computing: → Classical bits + Logic gates (AND, OR, XOR, ...)
- 46. R. Feynman, “Simulating physics with computers”, International Journal of Theoretical Physics, vol. 21, no. 6, pp. 467–488, 1982. D. Deutsch, “Quantum theory, the Church-Turing principle and the universal quantum computer”, Proc. R. Soc. A, vol. 400, no. 1818, pp. 97–117, 1985. Quantum Speedup Conventional computing: → Classical bits + Logic gates (AND, OR, XOR, ...) Quantum computing: → Quantum bits + Quantum logic gates
- 47. R. Feynman, “Simulating physics with computers”, International Journal of Theoretical Physics, vol. 21, no. 6, pp. 467–488, 1982. D. Deutsch, “Quantum theory, the Church-Turing principle and the universal quantum computer”, Proc. R. Soc. A, vol. 400, no. 1818, pp. 97–117, 1985. Quantum Speedup Blackboard ….
- 48. R. Feynman, “Simulating physics with computers”, International Journal of Theoretical Physics, vol. 21, no. 6, pp. 467–488, 1982. D. Deutsch, “Quantum theory, the Church-Turing principle and the universal quantum computer”, Proc. R. Soc. A, vol. 400, no. 1818, pp. 97–117, 1985. Quantum Speedup
- 49. Quantum Speedup R. Feynman, “Simulating physics with computers”, International Journal of Theoretical Physics, vol. 21, no. 6, pp. 467–488, 1982. D. Deutsch, “Quantum theory, the Church-Turing principle and the universal quantum computer”, Proc. R. Soc. A, vol. 400, no. 1818, pp. 97–117, 1985.
- 50. Quantum Speedup → 50-60 qubits for quantum advantage R. Feynman, “Simulating physics with computers”, International Journal of Theoretical Physics, vol. 21, no. 6, pp. 467–488, 1982. D. Deutsch, “Quantum theory, the Church-Turing principle and the universal quantum computer”, Proc. R. Soc. A, vol. 400, no. 1818, pp. 97–117, 1985.
- 51. Quantum Speedup → 50-60 qubits for quantum advantage → 100-150 qubits to tackle calculations in quantum chemistry R. Feynman, “Simulating physics with computers”, International Journal of Theoretical Physics, vol. 21, no. 6, pp. 467–488, 1982. D. Deutsch, “Quantum theory, the Church-Turing principle and the universal quantum computer”, Proc. R. Soc. A, vol. 400, no. 1818, pp. 97–117, 1985.
- 52. Quantum Speedup → 50-60 qubits for quantum advantage → 100-150 qubits to tackle calculations in quantum chemistry → 4000 qubits and more to break existing public key encryption standard (2048-bit RSA keys) R. Feynman, “Simulating physics with computers”, International Journal of Theoretical Physics, vol. 21, no. 6, pp. 467–488, 1982. D. Deutsch, “Quantum theory, the Church-Turing principle and the universal quantum computer”, Proc. R. Soc. A, vol. 400, no. 1818, pp. 97–117, 1985.
- 53. Quantum Speedup → 50-60 qubits for quantum advantage → 100-150 qubits to tackle calculations in quantum chemistry → 4000 qubits and more to break existing public key encryption standard (2048-bit RSA keys) Are these qubits the same as the ones often mentioned in press releases? R. Feynman, “Simulating physics with computers”, International Journal of Theoretical Physics, vol. 21, no. 6, pp. 467–488, 1982. D. Deutsch, “Quantum theory, the Church-Turing principle and the universal quantum computer”, Proc. R. Soc. A, vol. 400, no. 1818, pp. 97–117, 1985.
- 54. Fault Tolerance Exposure to heat and radiation makes qubits prone to errors (decoherence): → Bit flip errors → Phase flip errors
- 55. Fault Tolerance Exposure to heat and radiation makes qubits prone to errors (decoherence): → Bit flip errors → Phase flip errors Press releases often refer to “physical” qubits
- 56. Fault Tolerance Exposure to heat and radiation makes qubits prone to errors (decoherence): → Bit flip errors → Phase flip errors Press releases often refer to “physical” qubits We need auxiliary qubits to implement error correcting codes (e.g. surface codes): → Physical-to-Logical qubit ratio → Physical qubit fidelity threeshold
- 57. Fault Tolerance
- 58. The DiVicenzo Criteria 1. A scalable physical system with well characterized qubits. 2. The ability to initialize the state of the qubits to a simple fiducial state, such as . 3. Long relevant decoherence times, much longer than the gate operation time. 4. A “universal” set of quantum gates. 5. A qubit-specific measurement capability. DiVincenzo's Criteria David P. DiVincenzo, "The Physical Implementation of Quantum Computation", Fortschritte der Physik. 48: 771–783, 2000.
- 59. The DiVicenzo CriteriaPhysical implementation Behold the mighty qubit: https://www.youtube.com/wa tch?v=_P7K8jUbLU0 A Tour of an IBM Q Lab: https://www.youtube.com/wa tch?v=KZf4BSmgdO4 Running an experiment in the IBM Quantum Experience: https://www.youtube.com/wa tch?v=pYD6bvKLI_c
- 60. The DiVicenzo CriteriaPhysical implementation → Superconducting qubits (IBM ~50 qubits, Intel ~50 qubits, Google ~70 qubits ?, …) + Fast gate times, Fabrication - Coherence, Cryogenic T°
- 61. The DiVicenzo CriteriaPhysical implementation → Superconducting qubits (IBM ~50 qubits, Intel ~50 qubits, Google ~70 qubits ?, …) + Fast gate times, Fabrication - Coherence, Cryogenic T° But also: → Trapped ions → Spin qubits in silicon → All optical → NV center in diamond → ...
- 63. Private key Ciphered message transmission 2 Private key Ciphering with private key Unciphering with private key 3 1 Symmetric-key algorithms
- 64. Public key transmission Public key transmission Ciphering with public key Unciphering with private key 4 1 3 2 Ciphered message transmission Asymmetric-key algorithms
- 66. Types of cryptography Q-computing provides an exponential speedup
- 67. Types of cryptography Q-computing provides an exponential speedup Q-computing (only) provides a quadratic speedup
- 68. Quantum attacks on Bitcoin
- 70. Cybersecurity Requirements meet Quantum Cryptography Practical (no physical meeting) Information-theoretic security based on no-cloning theorem and Heisenberg's uncertainty relations Basic principle
- 77. BB84 QKD protocol 0 1
- 78. “No-cloning theorem: No quantum operation exists that can duplicate perfectly an arbitrary quantum state.” Valerio Scarani, Sofyan Iblisdir, Nicolas Gisin, and Antonio Acín Rev. Mod. Phys. 77, 1225 – Published 8 November 2005 Achievable distance
- 79. “No-cloning theorem: No quantum operation exists that can duplicate perfectly an arbitrary quantum state.” Valerio Scarani, Sofyan Iblisdir, Nicolas Gisin, and Antonio Acín Rev. Mod. Phys. 77, 1225 – Published 8 November 2005 “No-cloning theorem: No quantum operation exists that can duplicate perfectly an arbitrary quantum state.” W.K. Wootters and W.H. Zurek, “A Single Quantum Cannot be Cloned”, Nature 299 (1982), pp. 802-803
- 80. “No-cloning theorem: No quantum operation exists that can duplicate perfectly an arbitrary quantum state.” Valerio Scarani, Sofyan Iblisdir, Nicolas Gisin, and Antonio Acín Rev. Mod. Phys. 77, 1225 – Published 8 November 2005 SPS: Single Photon Source EPPS: Entangled Photon Pair Source BSM: Bell State Measurement “No-cloning theorem: No quantum operation exists that can duplicate perfectly an arbitrary quantum state.” W.K. Wootters and W.H. Zurek, “A Single Quantum Cannot be Cloned”, Nature 299 (1982), pp. 802-803
- 81. “No-cloning theorem: No quantum operation exists that can duplicate perfectly an arbitrary quantum state.” Valerio Scarani, Sofyan Iblisdir, Nicolas Gisin, and Antonio Acín Rev. Mod. Phys. 77, 1225 – Published 8 November 2005 SPS: Single Photon Source EPPS: Entangled Photon Pair Source BSM: Bell State Measurement “No-cloning theorem: No quantum operation exists that can duplicate perfectly an arbitrary quantum state.” W.K. Wootters and W.H. Zurek, “A Single Quantum Cannot be Cloned”, Nature 299 (1982), pp. 802-803
- 82. SPS: Single Photon Source EPPS: Entangled Photon Pair Source BSM: Bell State Measurement “No-cloning theorem: No quantum operation exists that can duplicate perfectly an arbitrary quantum state.” W.K. Wootters and W.H. Zurek, “A Single Quantum Cannot be Cloned”, Nature 299 (1982), pp. 802-803
- 83. DelayCoincidences SPS: Single Photon Source EPPS: Entangled Photon Pair Source BSM: Bell State Measurement D1 D2
- 84. DelayCoincidences SPS: Single Photon Source EPPS: Entangled Photon Pair Source BSM: Bell State Measurement SYNCHRONIZATION REQUIRED D1 D2
- 85. Satellite QKD https://www.youtube.com/watch?v=4QlcKuxDGrs Quantum satellite achieves 'spooky action' at record distance (China QKD network):
- 86. Quantum Internet
- 87. European flagship on quantum technologies
- 88. Quantum Manifesto was handed over to the European Commission in May 2016 → More than 3600 supporters from academia and industry 1b€ investment by the EU over 10 years