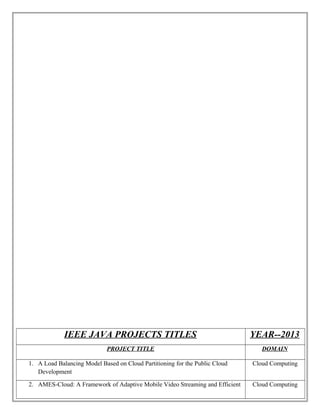
Java IEEE 2013 Projects list
- 1. IEEE JAVA PROJECTS TITLES YEAR--2013 PROJECT TITLE DOMAIN 1. A Load Balancing Model Based on Cloud Partitioning for the Public Cloud Development Cloud Computing 2. AMES-Cloud: A Framework of Adaptive Mobile Video Streaming and Efficient Cloud Computing
- 2. Social Video Sharing in the Clouds 3. Collaboration in Multi Cloud Computing Environments Framework & Security Issues Cloud Computing 4. Mining Contracts for Business Events and Temporal Constraints in Service Engagements Cloud Computing
- 3. 5. Privacy Preserving Delegated Access Control in Public Cloud Cloud Computing 6. Privacy Preserving Public Auditing for Secure Cloud Storage Cloud Computing 7. Winds of Change from Vendor Lock-In to the Meta Cloud Cloud Computing 8. Framework of Data Integrity for Cross Cloud Environment Using CPDP Scheme Cloud Computing 9. Load Rebalancing for Distributed File Systems in Clouds Cloud Computing
- 4. 10. Intelligent Lung Cancer Prediction System Data Mining 11. Fast nearest neighbor search with key words Data Mining 12. A Fast Clustering-Based Feature Subset Selection Algorithm for High Dimensional Data Data Mining 13. A System to Filter Unwanted Messages from OSN User Walls Data Mining 14. Cloud MoV Cloud-based Mobile Social TV Data Mining
- 5. 15. Comparable Entity Mining from Comparative Questions Data Mining 16. Crowd Sourcing Predictors of Behavioral Outcomes Data Mining 17. Facilitating effective user navigation through website structure improvement Data Mining 18. Focus Learning to Crawl Web Forums Data Mining 19. Incentive Compatible Privacy-Preserving Data Analysis Data Mining 20. PMSE : A Personalized Mobile Search Engine Data Mining
- 6. 21. Robust Module Based Data Management Data Mining 22. Sensitive Label Privacy Protection on Social Network Data Data Mining 23. Spatial Approximate String Search Data Mining 24. Multiparty Access Control for Online Social Networks: Model and Mechanisms Data Mining
- 7. 25. Annotating Search Results from Databases Data Mining 26. A Method for Mining Infrequent Causal Associations and Its Application in Finding Adverse Drug Reaction Signal Pairs Data Mining 27. m-Privacy for Collaborative Data Publishing Data Mining 28. Improving Various Reversible Data Hiding Schemes Image Processing 29. A Scalable Server Architecture for Mobile Presence Services in Social Network Mobile Computing
- 8. Applications 30. Distributed Cooperative Caching in Social Wireless Networks Mobile Computing 31. Mobile relay configuration in data-intensive wireless sensor networks Mobile Computing 32. Privacy Preserving Distributed Profile Matching in Proximity-based Mobile Social Networks Mobile Computing 33. Towards a statistical framework for source anonymity in sensor networks Mobile Computing
- 9. 34. Vampire attacks: Draining life from wireless ad-hoc sensor networks Mobile Computing 35. Self Adaptive Contention Aware Routing Protocol for Intermittently Connected Mobile Networks Mobile Computing 36. Combining Cryptographic Primitives to Prevent Jamming Attacks in Wireless Networks Mobile Computing 37. Discovery and verification of neighbor positions in mobile adhoc networks Mobile Computing
- 10. 38. Access Policy Consolidation for Event Processing Systems Networking 39. Fully Anonymous Profile Matching in Mobile Social Networks Networking 40. Optimizing Cloud Resources for Delivering IPTV Services through Virtualization Networking 41. Price Differentiation for Communication Networks Networking
- 11. 42. Pack: Prediction based cloud bandwidth and cost reduction system Networking 43. Dynamic resource allocation using virtual machines for cloud computing environment Parallel and Distribution 44. Scalable and Secure Sharing of Personal Health Records in Cloud Computing using Attribute-based Encryption Parallel and distribution 45. CAM Cloud-Assisted Privacy Preserving Mobile Health Monitoring Secure Computing
- 12. 46. Extracting Spread-Spectrum Hidden Data from Digital Media Secure Computing 47. Two Tales of Privacy in Online Social Networks Secure Computing 48. Utility-Privacy Tradeoff in Databases An Information-theoretic Approach Secure Computing 49. A secure protocol for spontaneous wireless ad-hoc network creation Wireless Sensor Networks
- 13. 50. A highly scalable key pre distribution scheme for wireless sensor networks Wireless Sensor Networks 51. Attribute-Based Encryption With Verifiable Outsourced Decryption Secure Computing 52. Protecting Sensitive Labels in Social Network Data Anonymization Data Mining