Mobility And Mobile I Pv4
•Download as PPT, PDF•
1 like•706 views
Unit 3 Of ACN
Report
Share
Report
Share
More Related Content
What's hot
What's hot (20)
Performance of Various Mobile IP Protocols and Security Considerations

Performance of Various Mobile IP Protocols and Security Considerations
Tracing An IP Address or Domain Name by Raghu Khimani

Tracing An IP Address or Domain Name by Raghu Khimani
Viewers also liked
Viewers also liked (20)
Computer Security Lecture 3: Classical Encryption Techniques 2

Computer Security Lecture 3: Classical Encryption Techniques 2
Computer Security Lecture 2: Classical Encryption Techniques 1

Computer Security Lecture 2: Classical Encryption Techniques 1
Classical Encryption Techniques in Network Security

Classical Encryption Techniques in Network Security
IS Unit 1_Conventional Encryption_Classical Encryption Techniques

IS Unit 1_Conventional Encryption_Classical Encryption Techniques
Revista qué pasa ranking UNIVERSIDADES 2010. (1de2)

Revista qué pasa ranking UNIVERSIDADES 2010. (1de2)
Similar to Mobility And Mobile I Pv4
Similar to Mobility And Mobile I Pv4 (20)
More from Ram Dutt Shukla
More from Ram Dutt Shukla (20)
Recently uploaded
Recently uploaded (20)
ProductAnonymous-April2024-WinProductDiscovery-MelissaKlemke

ProductAnonymous-April2024-WinProductDiscovery-MelissaKlemke
Finding Java's Hidden Performance Traps @ DevoxxUK 2024

Finding Java's Hidden Performance Traps @ DevoxxUK 2024
Strategize a Smooth Tenant-to-tenant Migration and Copilot Takeoff

Strategize a Smooth Tenant-to-tenant Migration and Copilot Takeoff
Mcleodganj Call Girls 🥰 8617370543 Service Offer VIP Hot Model

Mcleodganj Call Girls 🥰 8617370543 Service Offer VIP Hot Model
Elevate Developer Efficiency & build GenAI Application with Amazon Q

Elevate Developer Efficiency & build GenAI Application with Amazon Q
Navigating the Deluge_ Dubai Floods and the Resilience of Dubai International...

Navigating the Deluge_ Dubai Floods and the Resilience of Dubai International...
EMPOWERMENT TECHNOLOGY GRADE 11 QUARTER 2 REVIEWER

EMPOWERMENT TECHNOLOGY GRADE 11 QUARTER 2 REVIEWER
AWS Community Day CPH - Three problems of Terraform

AWS Community Day CPH - Three problems of Terraform
Web Form Automation for Bonterra Impact Management (fka Social Solutions Apri...

Web Form Automation for Bonterra Impact Management (fka Social Solutions Apri...
Why Teams call analytics are critical to your entire business

Why Teams call analytics are critical to your entire business
Apidays New York 2024 - Passkeys: Developing APIs to enable passwordless auth...

Apidays New York 2024 - Passkeys: Developing APIs to enable passwordless auth...
Apidays New York 2024 - Scaling API-first by Ian Reasor and Radu Cotescu, Adobe

Apidays New York 2024 - Scaling API-first by Ian Reasor and Radu Cotescu, Adobe
ICT role in 21st century education and its challenges

ICT role in 21st century education and its challenges
Cloud Frontiers: A Deep Dive into Serverless Spatial Data and FME

Cloud Frontiers: A Deep Dive into Serverless Spatial Data and FME
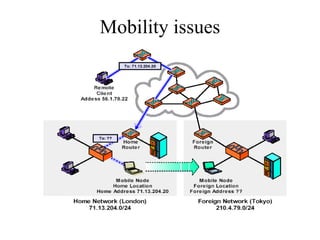
Mobility And Mobile I Pv4
- 12. Mobile IP Mobility Agent Advertisement Extension Format
- 18. Mobile tunneling Triangle path
