Perimeter Protected Access Design Pattern
•
4 likes•1,016 views
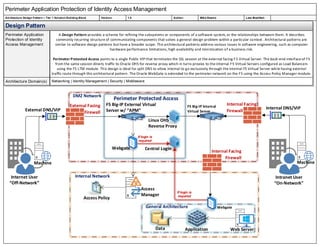
Design pattern called "Perimeter Application Protection of Identity Access Management" describes the general pattern for following securing applications with external access
Report
Share
Report
Share
Recommended
More Related Content
What's hot
What's hot (13)
Architectural Styles and Case Studies, Software architecture ,unit–2

Architectural Styles and Case Studies, Software architecture ,unit–2
Viewers also liked
Viewers also liked (7)
Re-engineering Your Intranet With User Friendly Architecture

Re-engineering Your Intranet With User Friendly Architecture
Similar to Perimeter Protected Access Design Pattern
Similar to Perimeter Protected Access Design Pattern (20)
Embedded system design: a modern approach to the electronic design.

Embedded system design: a modern approach to the electronic design.
"A Highly Decoupled Front-end Framework for High Trafficked Web Applications"...

"A Highly Decoupled Front-end Framework for High Trafficked Web Applications"...
10 - Architetture Software - More architectural styles

10 - Architetture Software - More architectural styles
Popeye - Using Fine-grained Network Access Control to Support Mobile Users an...

Popeye - Using Fine-grained Network Access Control to Support Mobile Users an...
National%20 online%20examination%20system%20an%20architectural%20perspective

National%20 online%20examination%20system%20an%20architectural%20perspective
National%20 online%20examination%20system%20an%20architectural%20perspective

National%20 online%20examination%20system%20an%20architectural%20perspective
IBM DataPower Gateways - What's new in 2016 v7.5.2

IBM DataPower Gateways - What's new in 2016 v7.5.2
Software architectural patterns - A Quick Understanding Guide

Software architectural patterns - A Quick Understanding Guide
Design Decisions For Understanding Software Architecture

Design Decisions For Understanding Software Architecture
Architecture Proposition For Multimedia repository

Architecture Proposition For Multimedia repository
Top 5 Software Architecture Pattern Event Driven SOA Microservice Serverless ...

Top 5 Software Architecture Pattern Event Driven SOA Microservice Serverless ...
More from Mike Reams
More from Mike Reams (17)
Knowledge Transfer Training Presentation for Identity Lifecycle Manager

Knowledge Transfer Training Presentation for Identity Lifecycle Manager
Design Pattern for Federated Single Sign-On Access

Design Pattern for Federated Single Sign-On Access
High-level Architecture viewpoint of a Troux Infrastructure

High-level Architecture viewpoint of a Troux Infrastructure
Visio Diagram Scripting and Server Management flow

Visio Diagram Scripting and Server Management flow
Visual representation as an architectural artifact

Visual representation as an architectural artifact
Recently uploaded
Abortion Pills in Oman (+918133066128) Cytotec clinic buy Oman Muscat

Abortion Pills in Oman (+918133066128) Cytotec clinic buy Oman MuscatAbortion pills in Kuwait Cytotec pills in Kuwait
call girls in Dakshinpuri (DELHI) 🔝 >༒9953056974 🔝 genuine Escort Service 🔝✔️✔️

call girls in Dakshinpuri (DELHI) 🔝 >༒9953056974 🔝 genuine Escort Service 🔝✔️✔️9953056974 Low Rate Call Girls In Saket, Delhi NCR
Recently uploaded (20)
Nisha Yadav Escorts Service Ernakulam ❣️ 7014168258 ❣️ High Cost Unlimited Ha...

Nisha Yadav Escorts Service Ernakulam ❣️ 7014168258 ❣️ High Cost Unlimited Ha...
Abortion Pills in Oman (+918133066128) Cytotec clinic buy Oman Muscat

Abortion Pills in Oman (+918133066128) Cytotec clinic buy Oman Muscat
Escorts Service Nagavara ☎ 7737669865☎ Book Your One night Stand (Bangalore)

Escorts Service Nagavara ☎ 7737669865☎ Book Your One night Stand (Bangalore)
Just Call Vip call girls Nagpur Escorts ☎️8617370543 Starting From 5K to 25K ...

Just Call Vip call girls Nagpur Escorts ☎️8617370543 Starting From 5K to 25K ...
8377087607, Door Step Call Girls In Majnu Ka Tilla (Delhi) 24/7 Available

8377087607, Door Step Call Girls In Majnu Ka Tilla (Delhi) 24/7 Available
WhatsApp Chat: 📞 8617697112 Call Girl Baran is experienced

WhatsApp Chat: 📞 8617697112 Call Girl Baran is experienced
UI:UX Design and Empowerment Strategies for Underprivileged Transgender Indiv...

UI:UX Design and Empowerment Strategies for Underprivileged Transgender Indiv...
Hire 💕 8617697112 Meerut Call Girls Service Call Girls Agency

Hire 💕 8617697112 Meerut Call Girls Service Call Girls Agency
call girls in Dakshinpuri (DELHI) 🔝 >༒9953056974 🔝 genuine Escort Service 🔝✔️✔️

call girls in Dakshinpuri (DELHI) 🔝 >༒9953056974 🔝 genuine Escort Service 🔝✔️✔️
Escorts Service Basapura ☎ 7737669865☎ Book Your One night Stand (Bangalore)

Escorts Service Basapura ☎ 7737669865☎ Book Your One night Stand (Bangalore)
❤Personal Whatsapp Number 8617697112 Samba Call Girls 💦✅.

❤Personal Whatsapp Number 8617697112 Samba Call Girls 💦✅.
VIP Model Call Girls Kalyani Nagar ( Pune ) Call ON 8005736733 Starting From ...

VIP Model Call Girls Kalyani Nagar ( Pune ) Call ON 8005736733 Starting From ...
8377087607, Door Step Call Girls In Kalkaji (Locanto) 24/7 Available

8377087607, Door Step Call Girls In Kalkaji (Locanto) 24/7 Available
Perimeter Protected Access Design Pattern
- 1. Intranet User “On-Network” Perimeter Protected Access Perimeter Application Protection of Identity Access Management Architecture Design Pattern – Tier 1 Solution Building Block Version: 1.0 Author: Mike Reams Last Modified: DMZ Network Design Pattern Perimeter Application Protection of Identity Access Management A Design Pattern provides a scheme for refining the subsystems or components of a software system, or the relationships between them. It describes commonly recurring structure of communicating components that solves a general design problem within a particular context . Architectural patterns are similar to software design patterns but have a broader scope. The architectural patterns address various issues in software engineering, such as computer hardware performance limitations, high availability and minimization of a business risk. Perimeter Protected Access points to a single Public VIP that terminates the SSL session at the external facing F5 Virtual Server. The back-end interface of F5 from the same session directs traffic to Oracle OHS for reverse proxy which in turns proxies to the internal F5 Virtual Servers configured as Load Balancers using the F5 LTM module. This design is ideal for split DNS to allow internal to go exclusively through the internal F5 Virtual Server while having external traffic route through this architectural pattern. The Oracle WebGate is extended to the perimeter network on the F5 using the Access Policy Manager module. Architecture Domain(s) Networking | Identity Management | Security | Middleware External DNS/VIP External Facing Firewall F5 Big-IP Internal Virtual Server Application Internet User “Off-Network” Linux OHS Reverse Proxy Internal Network Data Web Server Access Manager Access Policy Central Login F5 Big-IP External Virtual Server w/ “APM” If login is required Internal DNS/VIP Internal Facing Firewall Webgate Machine Machine General Architecture If login is required Webgate Internal Facing Firewall
