COSO ERM Topology
•
0 likes•497 views
Created by Jason P. Rusch
Report
Share
Report
Share
Download to read offline
Recommended
Recent COSO Internal Control and Risk Management Developments

Recent COSO Internal Control and Risk Management DevelopmentsInternational Federation of Accountants
Recommended
Recent COSO Internal Control and Risk Management Developments

Recent COSO Internal Control and Risk Management DevelopmentsInternational Federation of Accountants
Upgrading Risk Management and Internal Control in Your Organization

Upgrading Risk Management and Internal Control in Your OrganizationInternational Federation of Accountants
Why Community-based Financial Institutions Should Practice Enterprise Risk Ma...

Why Community-based Financial Institutions Should Practice Enterprise Risk Ma...WolfPAC - Integrated Risk Management
More Related Content
What's hot
Upgrading Risk Management and Internal Control in Your Organization

Upgrading Risk Management and Internal Control in Your OrganizationInternational Federation of Accountants
Why Community-based Financial Institutions Should Practice Enterprise Risk Ma...

Why Community-based Financial Institutions Should Practice Enterprise Risk Ma...WolfPAC - Integrated Risk Management
What's hot (20)
Pp the three lines of defense in effective risk management and control

Pp the three lines of defense in effective risk management and control
Upgrading Risk Management and Internal Control in Your Organization

Upgrading Risk Management and Internal Control in Your Organization
Audit, control and enterprise wide risk management

Audit, control and enterprise wide risk management
Why Community-based Financial Institutions Should Practice Enterprise Risk Ma...

Why Community-based Financial Institutions Should Practice Enterprise Risk Ma...
Similar to COSO ERM Topology
Similar to COSO ERM Topology (20)
7 Key Elements Of An Enterprise Risk Management Program

7 Key Elements Of An Enterprise Risk Management Program
Mastering Risk Management: Strategies for Safeguarding Business Success

Mastering Risk Management: Strategies for Safeguarding Business Success
More from Jason Rusch - CISSP CGEIT CISM CISA GNSA
More from Jason Rusch - CISSP CGEIT CISM CISA GNSA (20)
Information_Governance_Risk_Compliance_Frameworks (v5)

Information_Governance_Risk_Compliance_Frameworks (v5)
Recently uploaded
Recently uploaded (20)
BAGALUR CALL GIRL IN 98274*61493 ❤CALL GIRLS IN ESCORT SERVICE❤CALL GIRL

BAGALUR CALL GIRL IN 98274*61493 ❤CALL GIRLS IN ESCORT SERVICE❤CALL GIRL
SEO Case Study: How I Increased SEO Traffic & Ranking by 50-60% in 6 Months

SEO Case Study: How I Increased SEO Traffic & Ranking by 50-60% in 6 Months
Call Girls In Majnu Ka Tilla 959961~3876 Shot 2000 Night 8000

Call Girls In Majnu Ka Tilla 959961~3876 Shot 2000 Night 8000
How to Get Started in Social Media for Art League City

How to Get Started in Social Media for Art League City
Marel Q1 2024 Investor Presentation from May 8, 2024

Marel Q1 2024 Investor Presentation from May 8, 2024
Call Girls Kengeri Satellite Town Just Call 👗 7737669865 👗 Top Class Call Gir...

Call Girls Kengeri Satellite Town Just Call 👗 7737669865 👗 Top Class Call Gir...
Quick Doctor In Kuwait +2773`7758`557 Kuwait Doha Qatar Dubai Abu Dhabi Sharj...

Quick Doctor In Kuwait +2773`7758`557 Kuwait Doha Qatar Dubai Abu Dhabi Sharj...
👉Chandigarh Call Girls 👉9878799926👉Just Call👉Chandigarh Call Girl In Chandiga...

👉Chandigarh Call Girls 👉9878799926👉Just Call👉Chandigarh Call Girl In Chandiga...
Call Girls Electronic City Just Call 👗 7737669865 👗 Top Class Call Girl Servi...

Call Girls Electronic City Just Call 👗 7737669865 👗 Top Class Call Girl Servi...
RSA Conference Exhibitor List 2024 - Exhibitors Data

RSA Conference Exhibitor List 2024 - Exhibitors Data
Nelamangala Call Girls: 🍓 7737669865 🍓 High Profile Model Escorts | Bangalore...

Nelamangala Call Girls: 🍓 7737669865 🍓 High Profile Model Escorts | Bangalore...
JAYNAGAR CALL GIRL IN 98274*61493 ❤CALL GIRLS IN ESCORT SERVICE❤CALL GIRL

JAYNAGAR CALL GIRL IN 98274*61493 ❤CALL GIRLS IN ESCORT SERVICE❤CALL GIRL
The Abortion pills for sale in Qatar@Doha [+27737758557] []Deira Dubai Kuwait![The Abortion pills for sale in Qatar@Doha [+27737758557] []Deira Dubai Kuwait](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![The Abortion pills for sale in Qatar@Doha [+27737758557] []Deira Dubai Kuwait](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
The Abortion pills for sale in Qatar@Doha [+27737758557] []Deira Dubai Kuwait
Russian Call Girls In Gurgaon ❤️8448577510 ⊹Best Escorts Service In 24/7 Delh...

Russian Call Girls In Gurgaon ❤️8448577510 ⊹Best Escorts Service In 24/7 Delh...
Call Girls Ludhiana Just Call 98765-12871 Top Class Call Girl Service Available

Call Girls Ludhiana Just Call 98765-12871 Top Class Call Girl Service Available
Value Proposition canvas- Customer needs and pains

Value Proposition canvas- Customer needs and pains
COSO ERM Topology
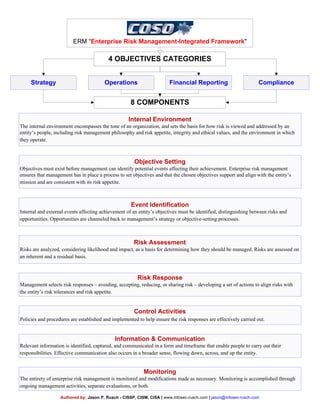
- 1. ERM “Enterprise Risk Management-Integrated Framework" 4 OBJECTIVES CATEGORIES Internal Environment The internal environment encompasses the tone of an organization, and sets the basis for how risk is viewed and addressed by an entity’s people, including risk management philosophy and risk appetite, integrity and ethical values, and the environment in which they operate. Strategy Objective Setting Objectives must exist before management can identify potential events affecting their achievement. Enterprise risk management ensures that management has in place a process to set objectives and that the chosen objectives support and align with the entity’s mission and are consistent with its risk appetite. Event Identification Internal and external events affecting achievement of an entity’s objectives must be identified, distinguishing between risks and opportunities. Opportunities are channeled back to management’s strategy or objective-setting processes. Risk Assessment Risks are analyzed, considering likelihood and impact, as a basis for determining how they should be managed. Risks are assessed on an inherent and a residual basis. Risk Response Management selects risk responses – avoiding, accepting, reducing, or sharing risk – developing a set of actions to align risks with the entity’s risk tolerances and risk appetite. Control Activities Policies and procedures are established and implemented to help ensure the risk responses are effectively carried out. Information & Communication Relevant information is identified, captured, and communicated in a form and timeframe that enable people to carry out their responsibilities. Effective communication also occurs in a broader sense, flowing down, across, and up the entity. Monitoring The entirety of enterprise risk management is monitored and modifications made as necessary. Monitoring is accomplished through ongoing management activities, separate evaluations, or both. ComplianceOperations Financial Reporting 8 COMPONENTS Authored by; Jason P. Rusch - CISSP, CISM, CISA | www.infosec-rusch.com | jason@infosec-rusch.com
