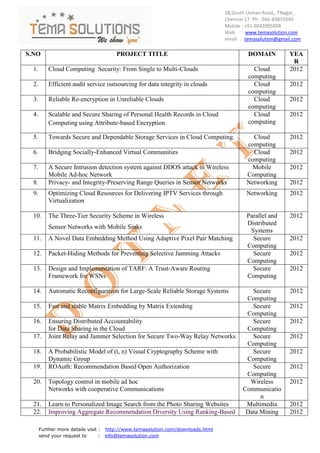
Dotnet tiltle for 2012 c
- 1. 28,South Usman Road,, TNagar, Chennai-17. Ph : 044-43855940 Mobile : +91-9042085008 Web : www.temasolution.com email : temasolution@gmail.com S.NO PROJECT TITLE DOMAIN YEA R 1. Cloud Computing Security: From Single to Multi-Clouds Cloud 2012 computing 2. Efficient audit service outsourcing for data integrity in clouds Cloud 2012 computing 3. Reliable Re-encryption in Unreliable Clouds Cloud 2012 computing 4. Scalable and Secure Sharing of Personal Health Records in Cloud Cloud 2012 Computing using Attribute-based Encryption. computing 5. Towards Secure and Dependable Storage Services in Cloud Computing. Cloud 2012 computing 6. Bridging Socially-Enhanced Virtual Communities Cloud 2012 computing 7. A Secure Intrusion detection system against DDOS attack in Wireless Mobile 2012 Mobile Ad-hoc Network Computing 8. Privacy- and Integrity-Preserving Range Queries in Sensor Networks Networking 2012 9. Optimizing Cloud Resources for Delivering IPTV Services through Networking 2012 Virtualization 10. The Three-Tier Security Scheme in Wireless Parallel and 2012 Distributed Sensor Networks with Mobile Sinks Systems 11. A Novel Data Embedding Method Using Adaptive Pixel Pair Matching Secure 2012 Computing 12. Packet-Hiding Methods for Preventing Selective Jamming Attacks Secure 2012 Computing 13. Design and Implementation of TARF: A Trust-Aware Routing Secure 2012 Framework for WSNs Computing 14. Automatic Reconfiguration for Large-Scale Reliable Storage Systems Secure 2012 Computing 15. Fast and stable Matrix Embedding by Matrix Extending Secure 2012 Computing 16. Ensuring Distributed Accountability Secure 2012 for Data Sharing in the Cloud Computing 17. Joint Relay and Jammer Selection for Secure Two-Way Relay Networks Secure 2012 Computing 18. A Probabilistic Model of (t, n) Visual Cryptography Scheme with Secure 2012 Dynamic Group Computing 19. ROAuth: Recommendation Based Open Authorization Secure 2012 Computing 20. Topology control in mobile ad hoc Wireless 2012 Networks with cooperative Communications Communicatio n 21. Learn to Personalized Image Search from the Photo Sharing Websites Multimedia 2012 22. Improving Aggregate Recommendation Diversity Using Ranking-Based Data Mining 2012 Further more details visit : http://www.temasolution.com/downloads.html send your request to : info@temasolution.com
- 2. 28,South Usman Road,, TNagar, Chennai-17. Ph : 044-43855940 Mobile : +91-9042085008 Web : www.temasolution.com email : temasolution@gmail.com Techniques 23. Organizing User Search Histories. Data Mining 2012 24. Enabling Secure and Efficient Ranked Keyword Search over Data Mining 2012 Outsourced Cloud Data. 25. Ranking Model Adaptation for Domain-Specific Search Rank Matrices Data Mining 2012 26. Slicing: A New Approach to Privacy Preserving Data Publishing Data Mining 2012 27. Online Modeling of Proactive Moderation System for Auction Fraud Image 2012 Processing Detection 28. OAuth Web Authorization Protocol Internet 2012 Computing Further more details visit : http://www.temasolution.com/downloads.html send your request to : info@temasolution.com