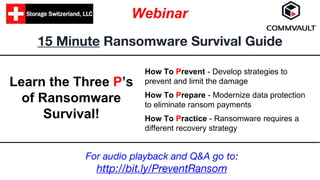
15 Minute Ransomware Survival Guide
- 1. 15 Minute Ransomware Survival Guide Webinar How To Prevent - Develop strategies to prevent and limit the damage How To Prepare - Modernize data protection to eliminate ransom payments How To Practice - Ransomware requires a different recovery strategy Learn the Three P’s of Ransomware Survival! For audio playback and Q&A go to: http://bit.ly/PreventRansom
- 2. Logistics ● All audio is through your speaker, no dial-in ● Ask questions using the Ask a Question box ○ On-Demand Viewers please tweet us questions @storageswiss #PreventRansom ● At the end of the presentation, please provide feedback and rate today’s webinar
- 3. Our Speakers George Crump is the founder of Storage Switzerland, the leading storage analyst focused on the subjects of big data, solid state storage, virtualization, cloud computing and data protection. He is widely recognized for his articles, white papers, and videos on such current approaches as all-flash arrays, deduplication, SSDs, software-defined storage, backup appliances, and storage networking. He has over 25 years of experience designing storage solutions for data centers across the US. Gregg Ogden is a Solutions Marketer at Commvault, which helps companies protect, access and use all of their data, anywhere and anytime - turning data into a powerful strategic asset. Gregg has demonstrated success in multiple business-to-business roles, leveraging experiences from a range of diverse technology companies in the US and the UK.
- 4. • What is Ransomware? • How does it work? • What is BitCoin? Ransomware 101
- 5. • Data is compromised at any time during the day • Hundreds of thousands of files are compromised Why Is Ransomware Different?
- 6. • Train users about Suspicious Links • Patch and Update Servers • Contain User Access • Limit Data Exposure • Archive old data • Maintain a disconnected copy Prevention
- 7. • Alert of unusual modification levels • List impacted files • Suspend offending account Implement A Detection System
- 8. • Ransomware can attach at any point during the day • CDP, Snapshots, CBT, Replication Increase Protection Frequency of Unstructured Data
- 9. • Impacted data is likely unstructured • Maybe hundreds of thousands of files to recover • Typically worst case scenario for backup software • Understand how your solution will respond Speed Up Recovery Capabilities
- 10. • Recovery from Ransomware is unlike any other • More widespread than a typical daily recovery • Not as widespread (in most cases) as a complete data center outage Practice
- 11. • Also you may be recovering into an infected storage • Practice recovering from disconnected copy Practice
- 12. Strategies to fend off Ransomware Cloud Application Backup Endpoint Data Protection Disaster Recovery
- 13. Strategies to fend off Ransomware Endpoint Data Protection • Collect and secure endpoint device data • Auto detection • Secure data transfers • Data loss prevention • Standardized platform
- 14. Cloud Application Backup Strategies to fend off Ransomware • Secure data in/to/from the cloud • Restricted access to Commvault databases • Data loss prevention technologies/procedures • Standardized platform
- 15. Disaster Recovery Strategies to fend off Ransomware • Isolate infection • Offline backups • Recover CommServer • Recover data • Standardized platform
- 16. Thank you! Storage Switzerland http://www.storageswiss.com georgeacrump@storageswiss.com StorageSwiss on Twitter: http://twitter.com/storageswiss StorageSwiss on YouTube: http://www.youtube.com/user/storageswiss Commvault https://www.commvault.com Commvault on Twitter: https://twitter.com/commvault Commvault on Facebook: https://www.facebook.com/CommVault/
- 17. 15 Minute Ransomware Survival Guide For complete Audio and Q&A please register for the On Demand Version at: http://bit.ly/PreventRansom
