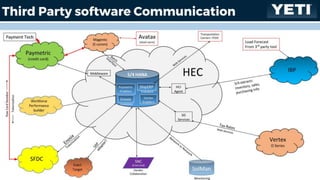
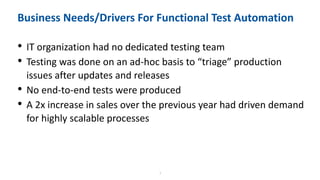
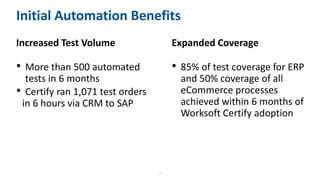
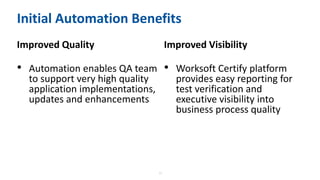
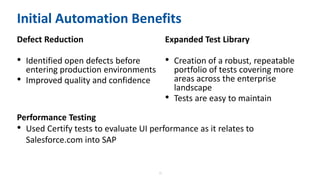
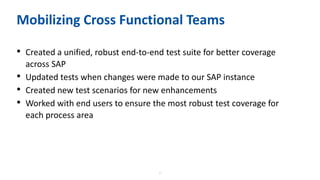
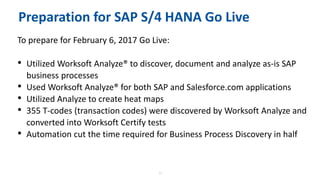
Yeti Coolers implemented a comprehensive plan for their SAP S/4HANA deployment using intelligent automation for documenting and validating business processes. The approach resulted in over 500 automated tests in six months, improved testing coverage, and reduced defects before production environments. Future plans include expanding the test suite and enhancing testing performance with additional applications.