Embed presentation
Download as PDF, PPTX



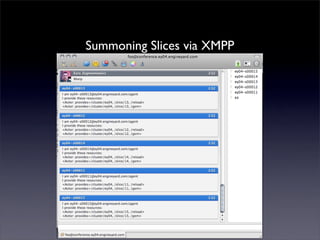
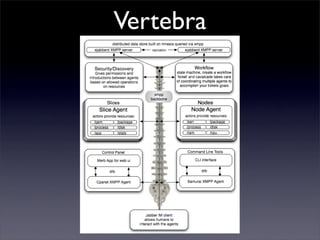
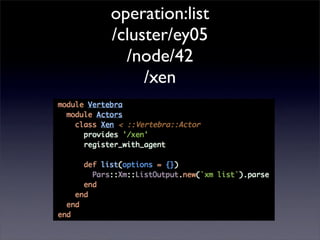
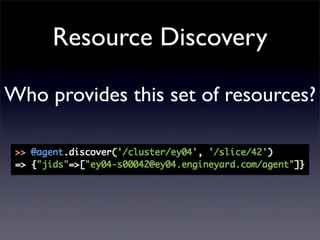
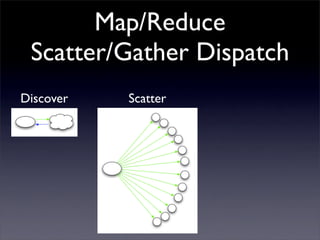
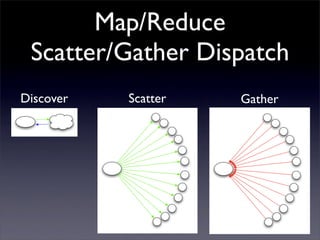
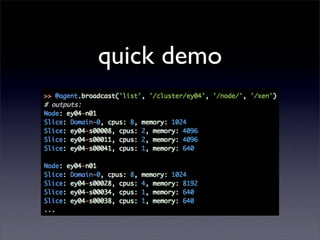

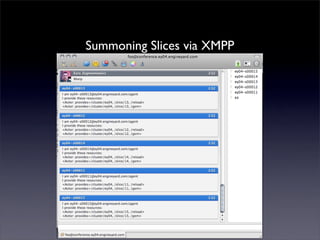
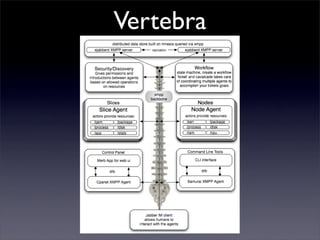
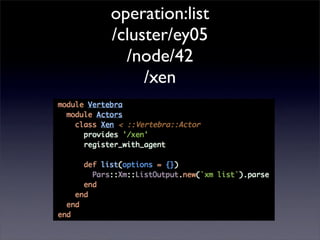
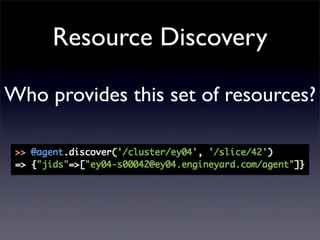
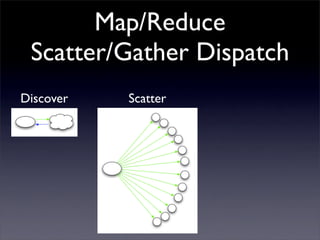
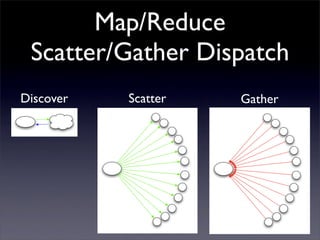
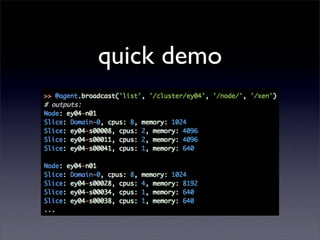
The document discusses the scalability of Ruby and Rails, emphasizing that they both can scale. It introduces cloud computing and the future of managing virtual machines, specifically mentioning the limitations of SSH and the need for a more robust solution like XMPP for communication. Additionally, it presents vertebra, a cloud computing and automation framework, as a means to handle distributed systems effectively.