Embed presentation
Download to read offline

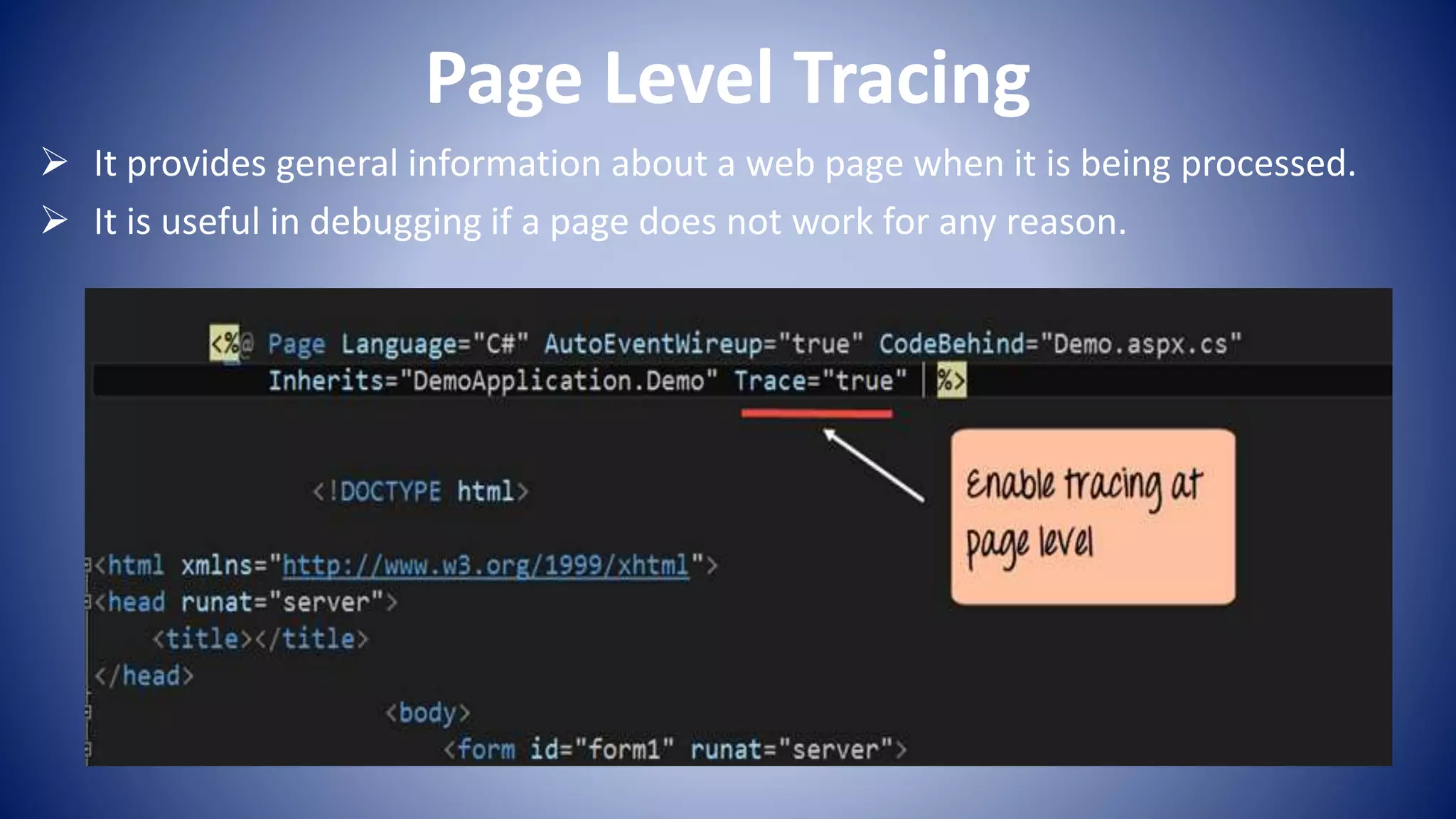

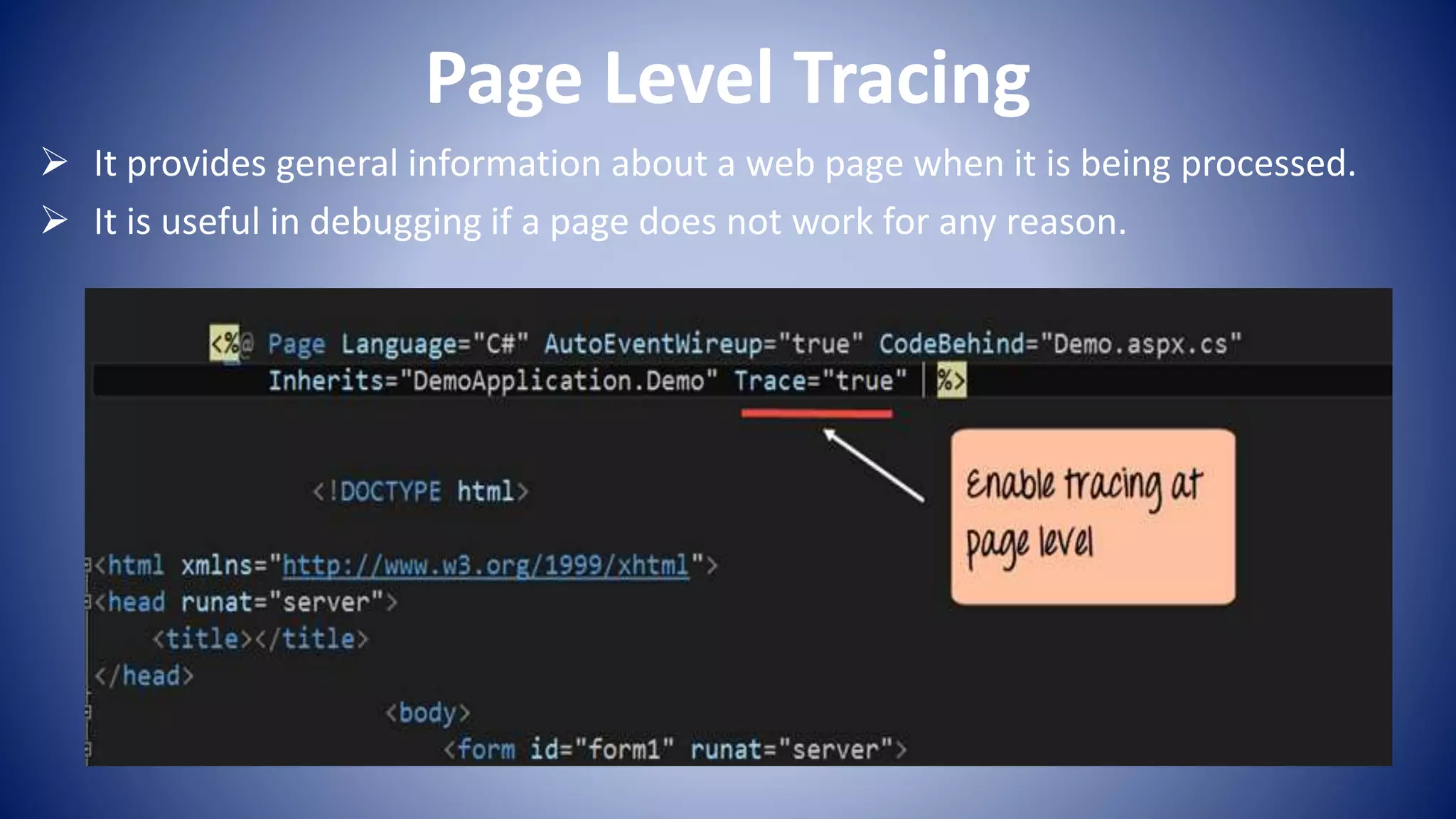
Tracing in ASP.NET allows developers to monitor page requests and debug errors by enabling a "trace.axd" page that provides details about the processing of web pages. Tracing can be done at the page level to troubleshoot specific pages or at the application level to monitor overall performance. Application level tracing provides information about the time of page requests, name of pages requested, status codes, and other processing details to help identify issues.