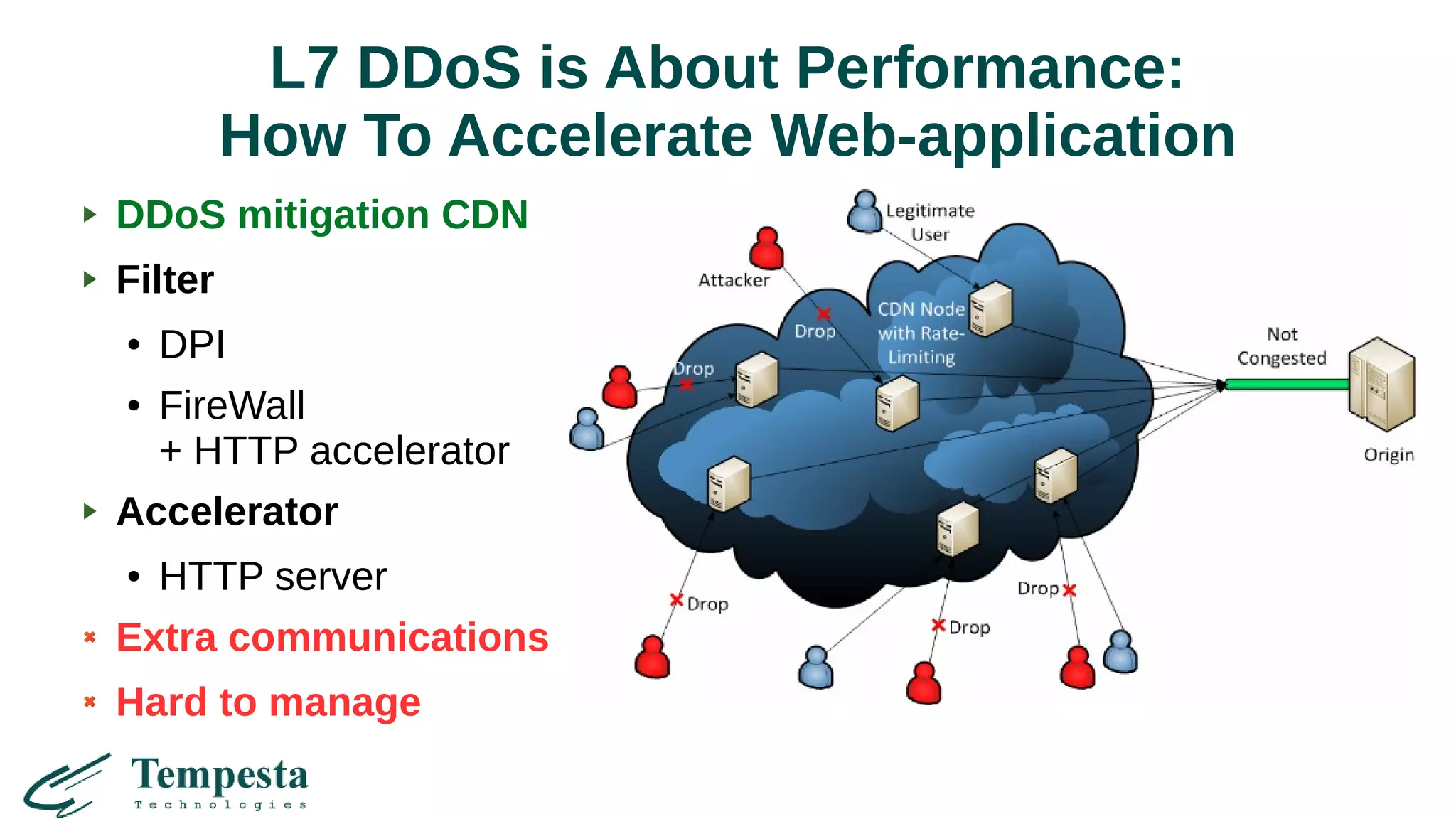
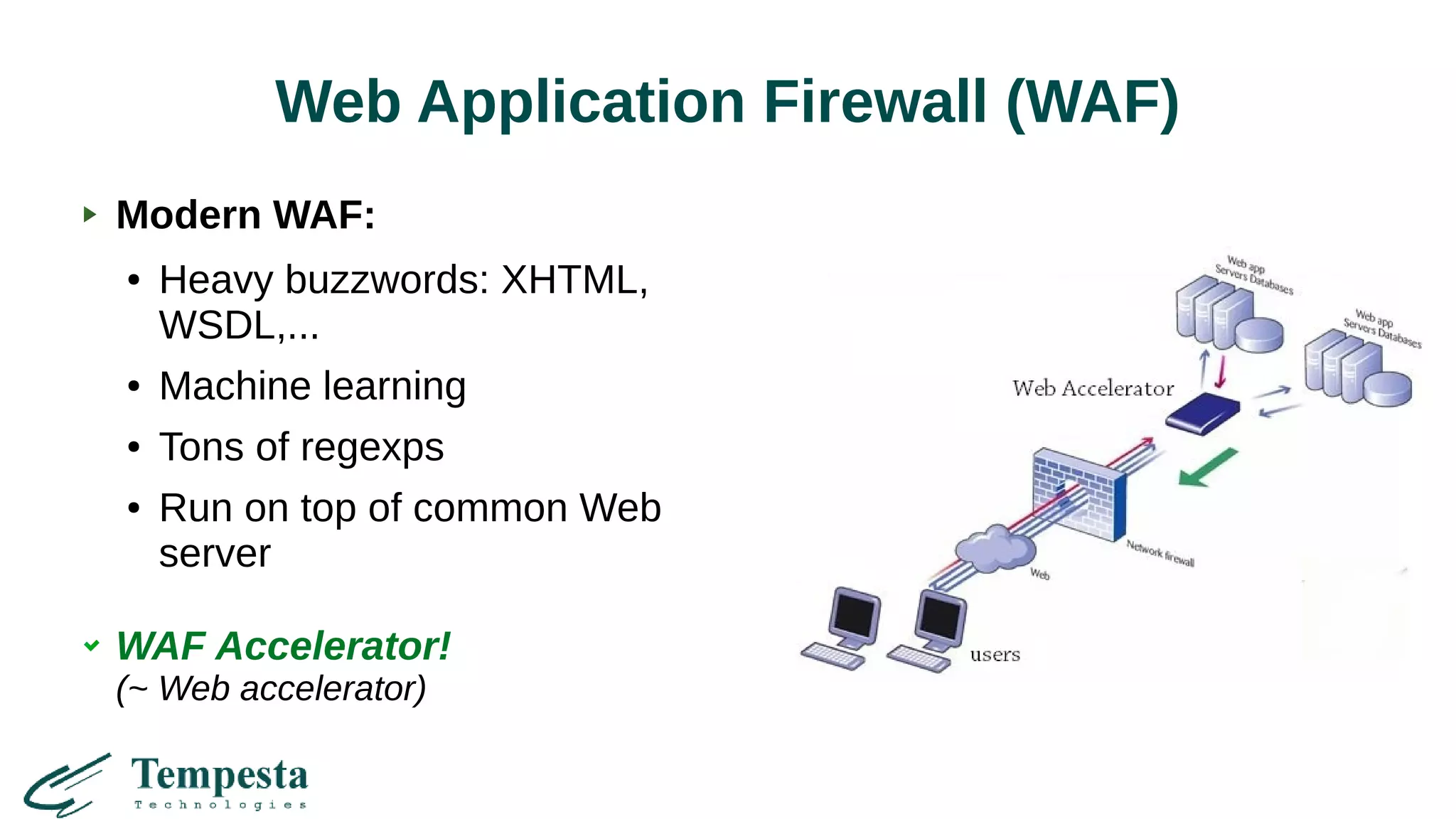
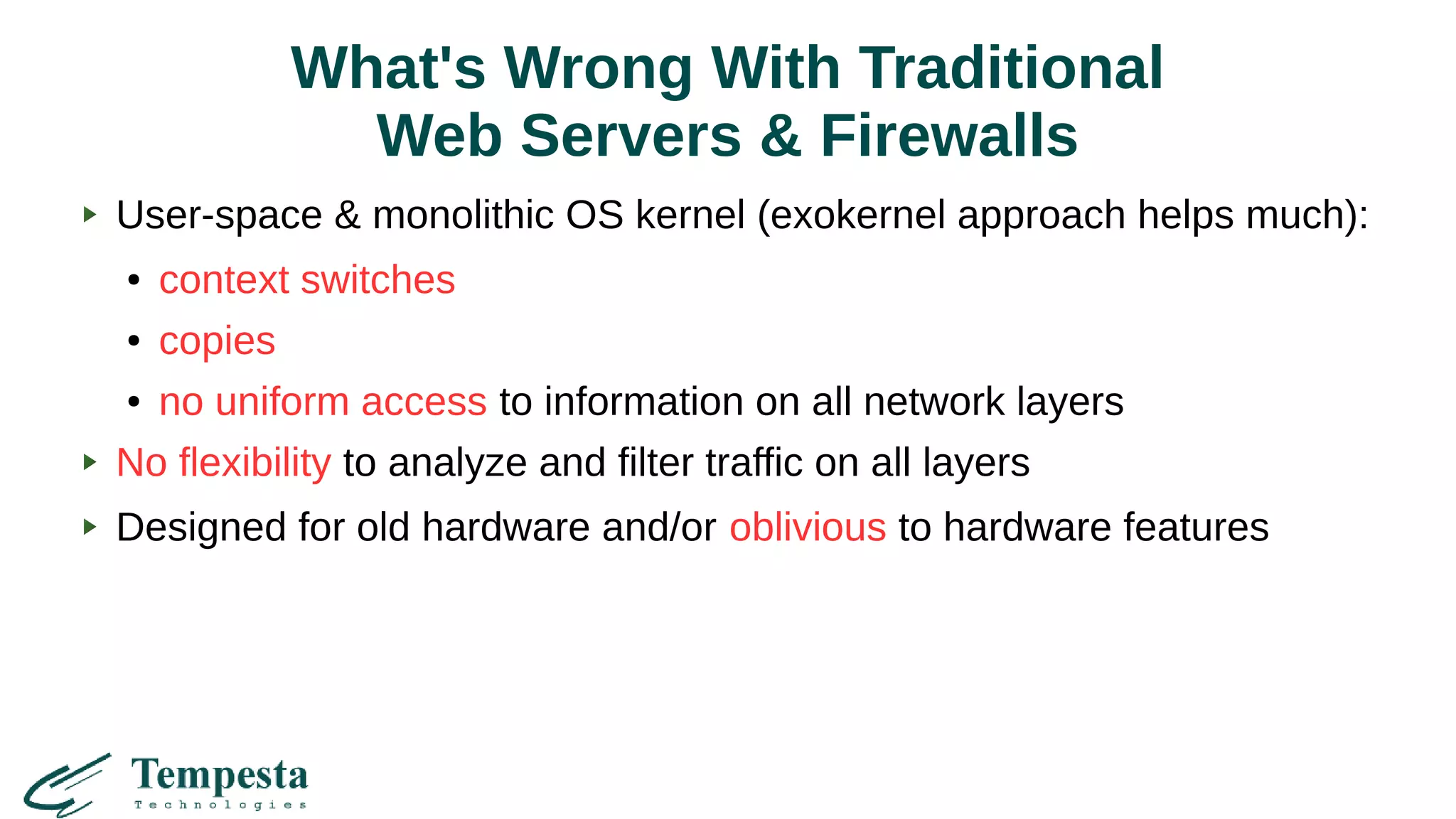
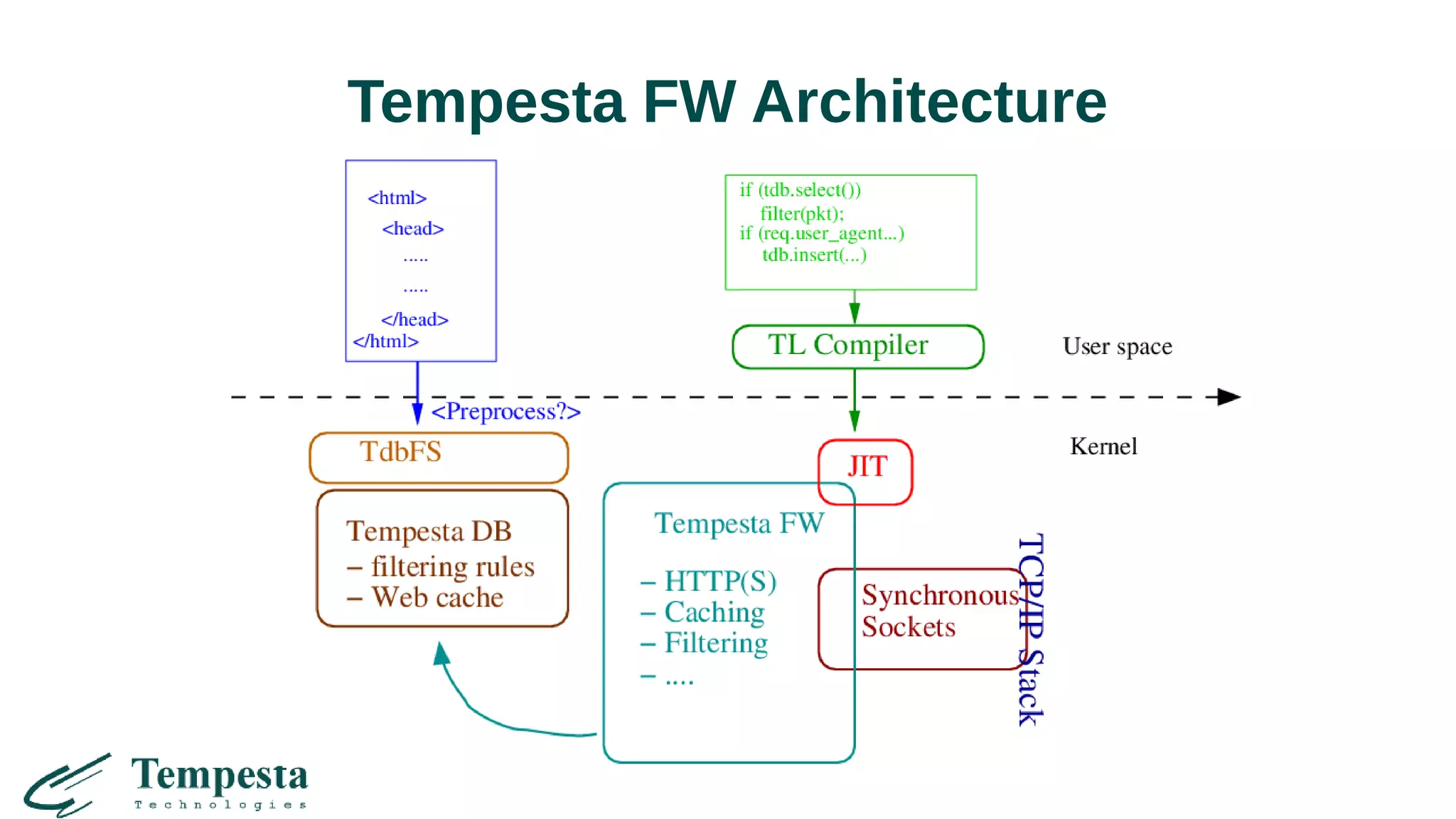
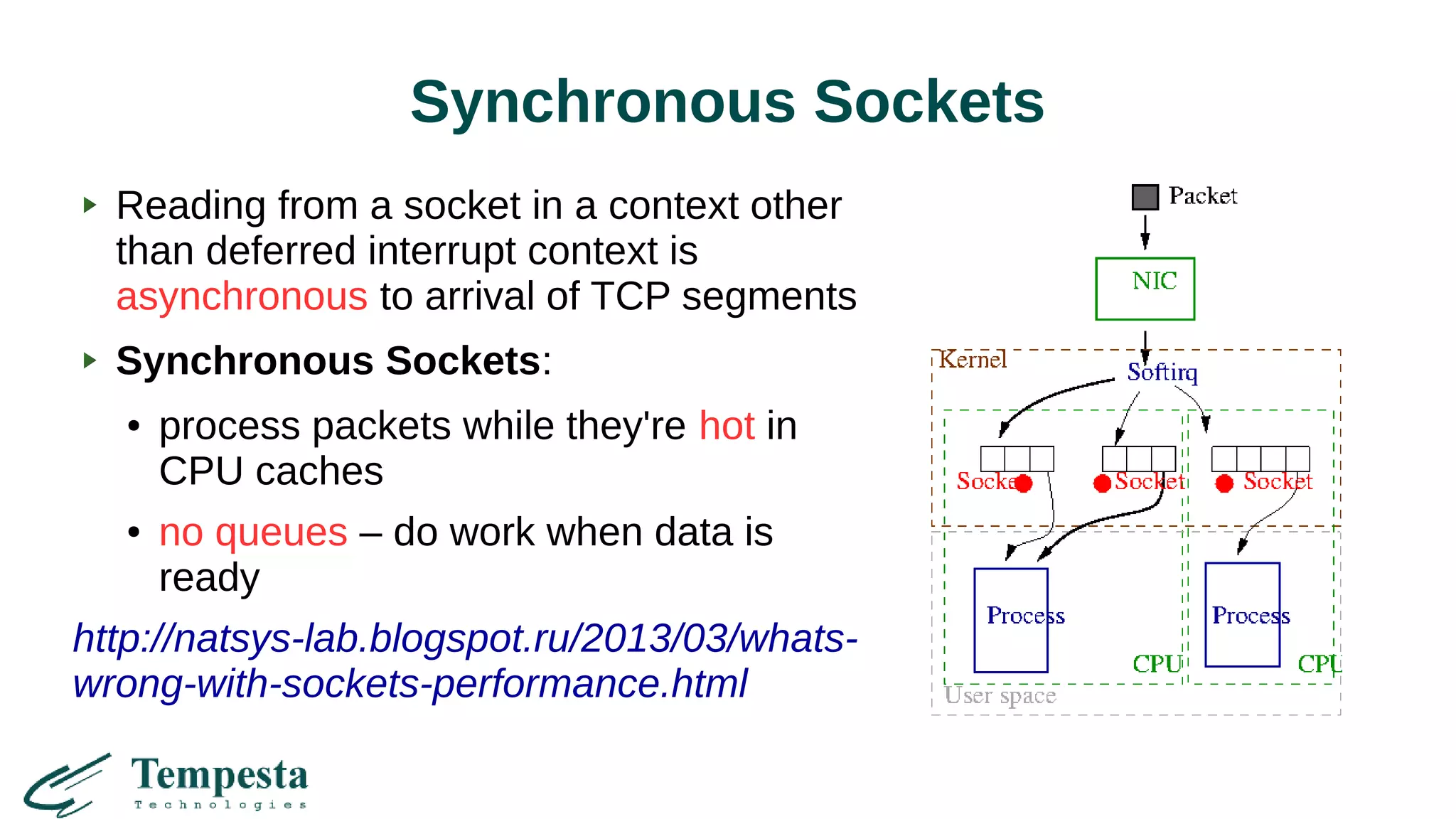
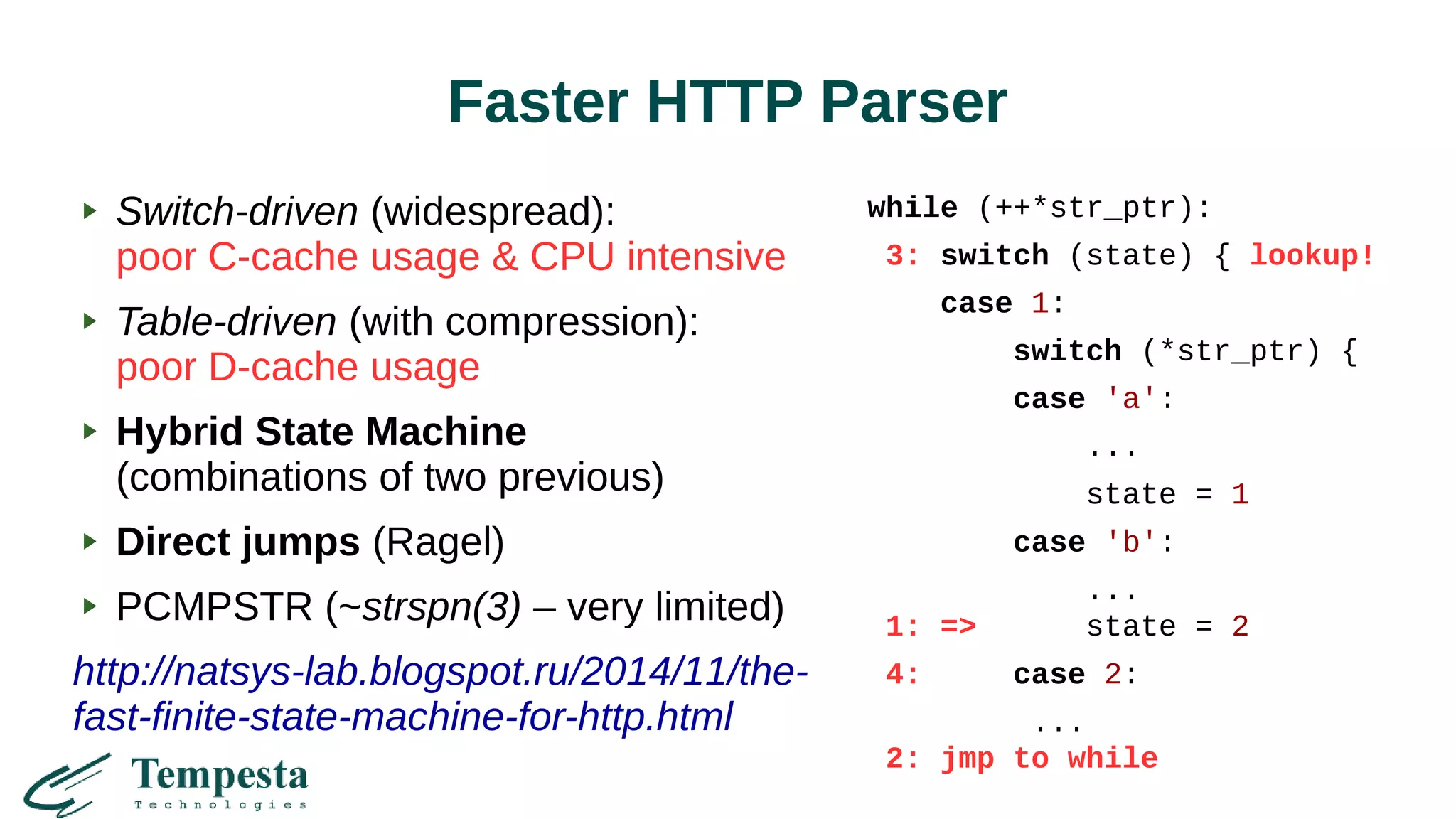
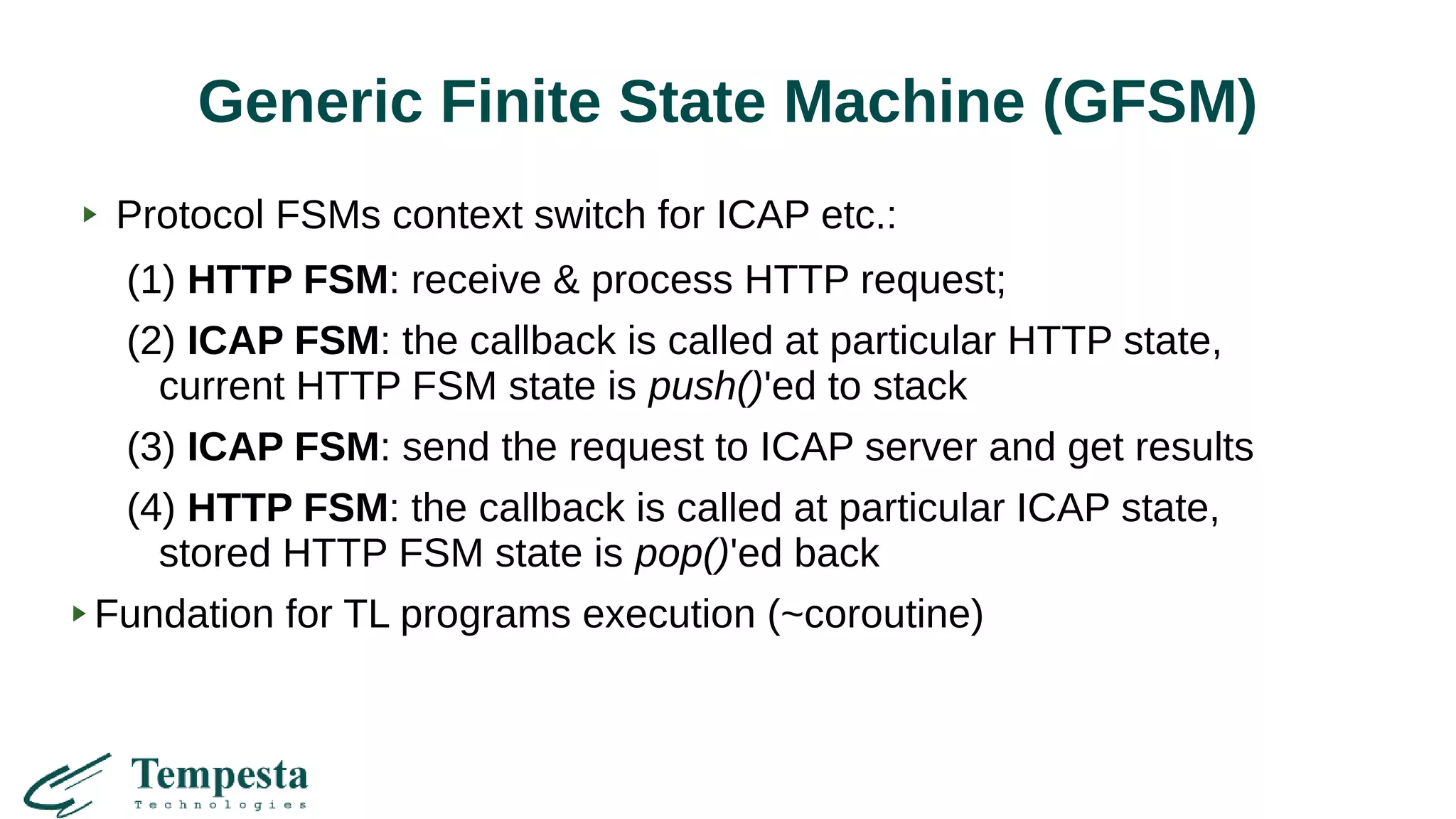
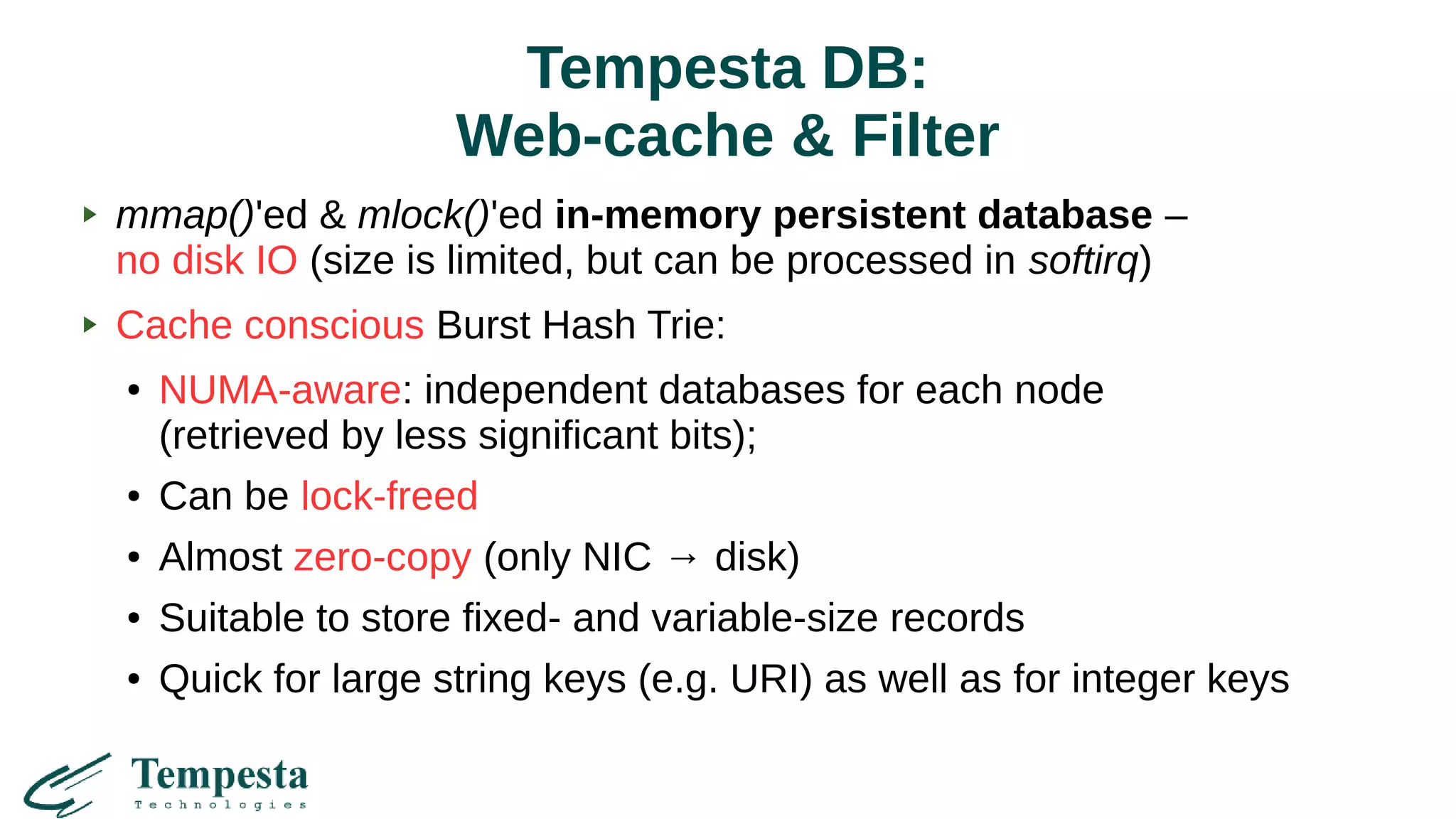
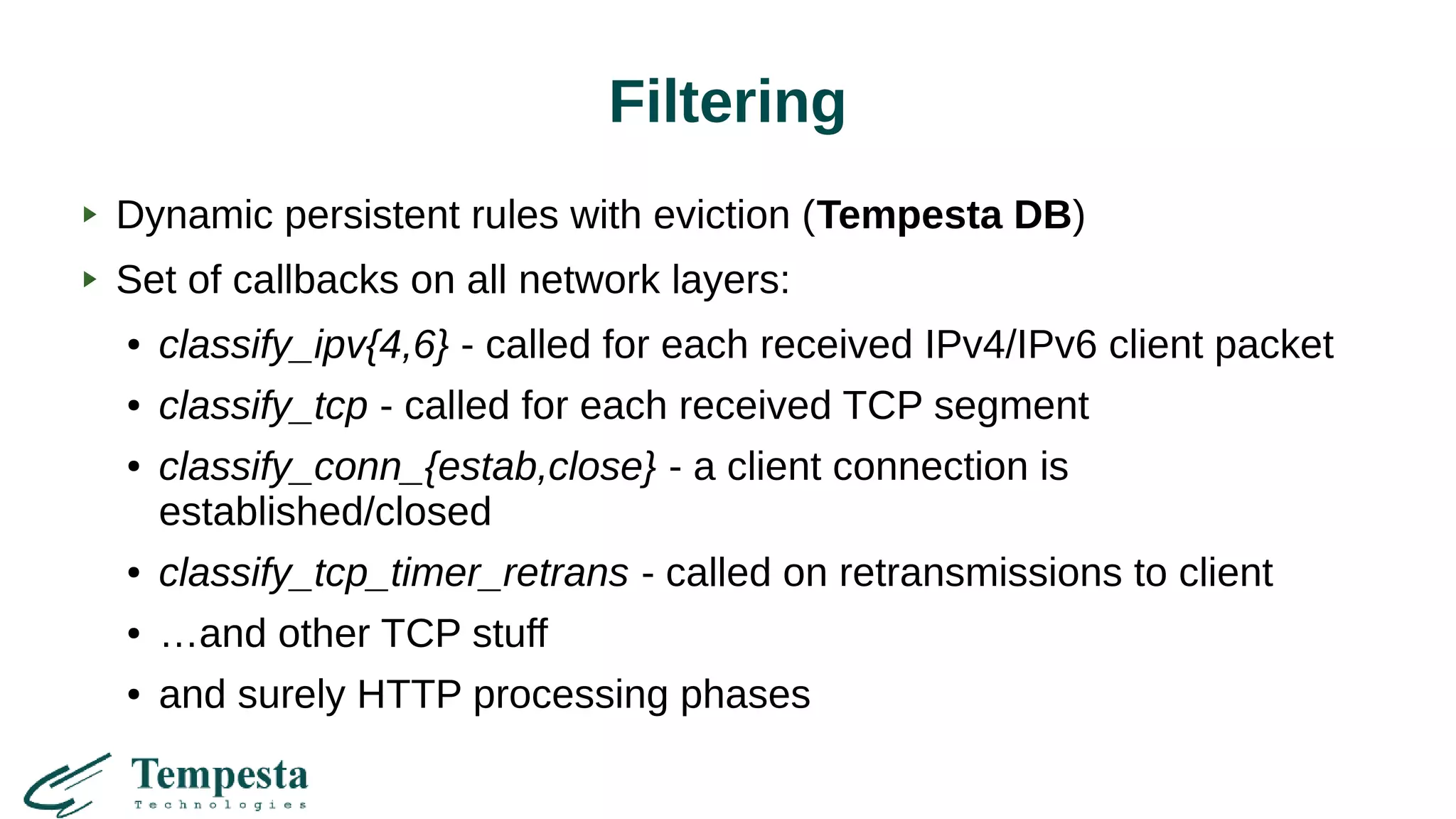
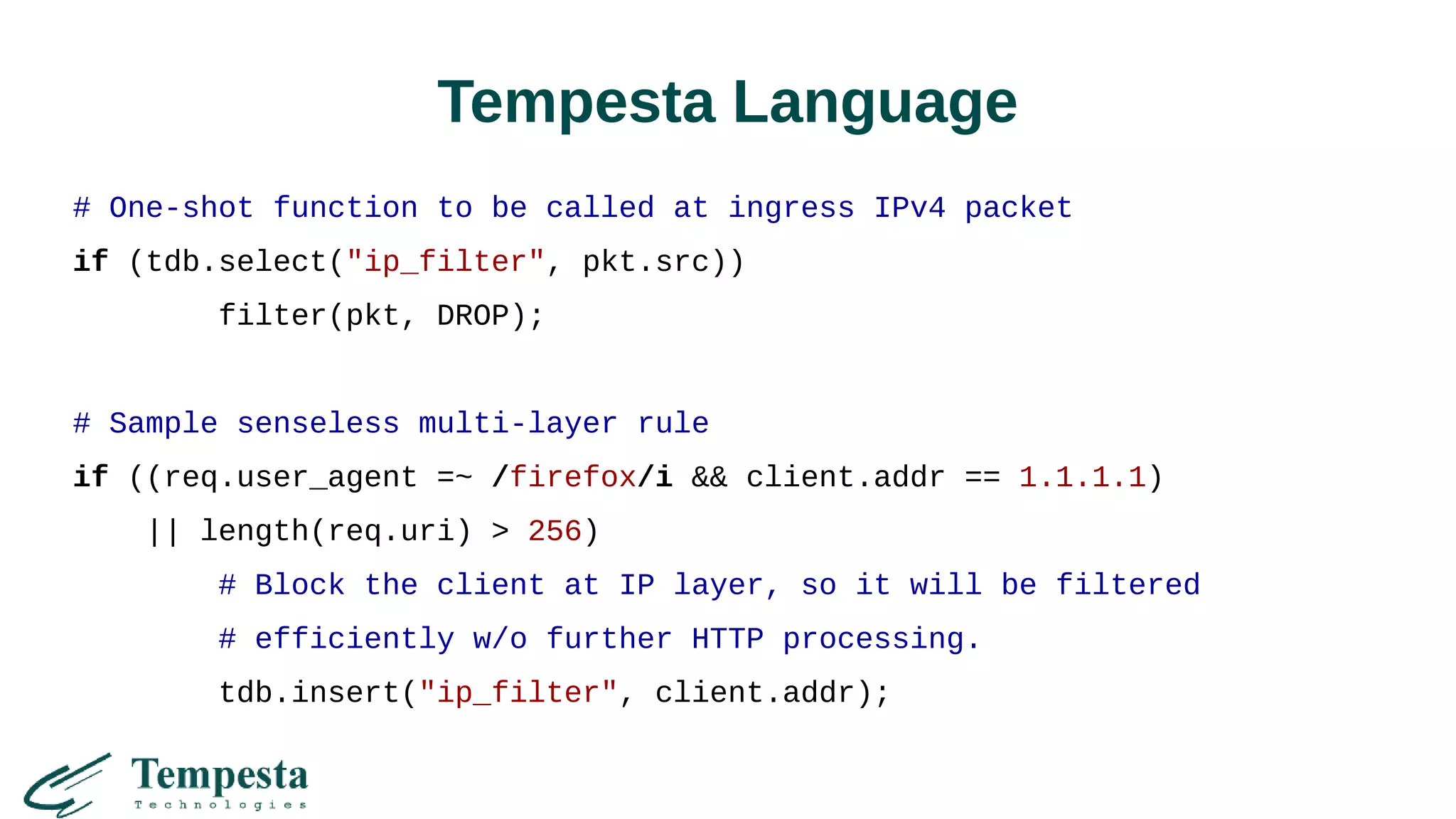
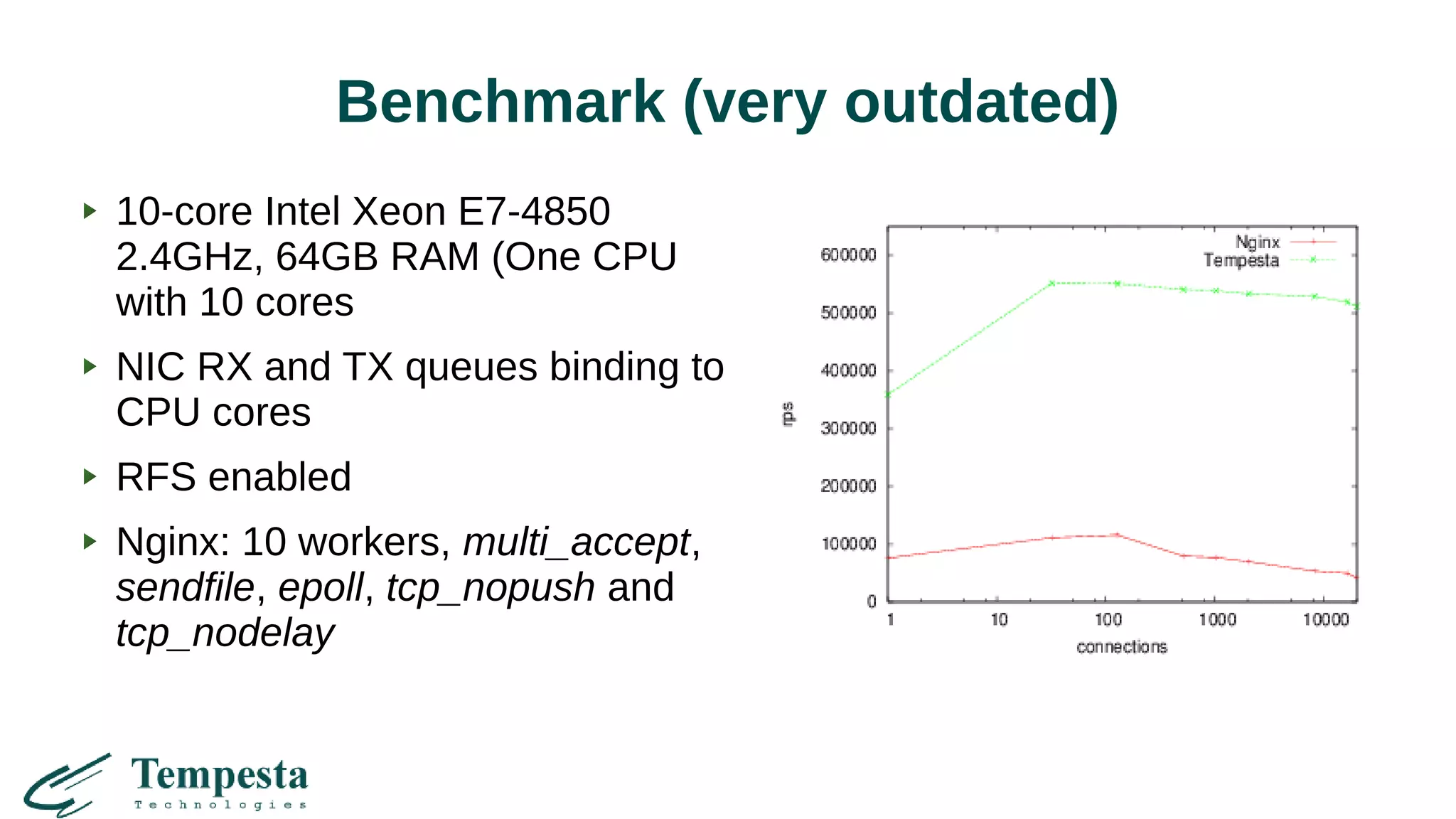
Tempesta FW is an open source framework for building high performance intelligent DDoS mitigation systems and web application firewalls. It directly embeds into the Linux TCP/IP stack and uses a just-in-time domain specific language to efficiently process and filter traffic at layers 3 through 7. This allows for fine-grained rule filtering, acceleration of web applications to mitigate DDoS attacks, and caching of content for improved performance. Tempesta aims to overcome limitations of traditional web servers and firewalls through its synchronous socket processing, fast HTTP parsing, generic finite state machine, and in-memory persistent database.