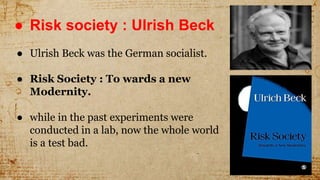
The document discusses technophobia, defined as the fear or aversion to technology, particularly complex devices like computers. It explores the cultural implications of this fear in the context of a risk society, as highlighted by Ulrich Beck, and addresses concerns about technological unemployment and its socio-political repercussions. Additionally, it touches on issues of privacy and cybersecurity in the modern age of e-banking.