Report
Share
Recommended
Instalacion antivirus

Para instalar nuestro antivirus Kaspersky, debemos descargar el software instalador, abrir la carpeta de instalación, hacer doble clic en el instalador y seguir los pasos para extraer los archivos e iniciar el programa, activándolo con el código de la carpeta. Una vez completada la instalación, el antivirus estará en modo de prueba hasta renovar la licencia descargando e instalando el archivo de reinicio de prueba.
Conocimiento estudiante y didactica

Este documento presenta una serie de preguntas de opción múltiple relacionadas con conceptos del desarrollo psicológico infantil y adolescente, así como estrategias pedagógicas. Las preguntas abarcan temas como las etapas del desarrollo cognitivo según Piaget, el desarrollo moral según Kohlberg, características del desarrollo psicosocial y cognitivo en la infancia y adolescencia, estrategias para generar aprendizajes significativos, y el uso de instrumentos para evaluar la expresión oral.
Precentacion

Este documento presenta un caso sobre cómo conectar un computador de escritorio a un televisor de casa. Explica que se puede usar un cable HDMI y da los pasos a seguir: 1) Revisar los puertos HDMI en el computador y televisor, 2) Conectar el cable HDMI a ambos dispositivos, y 3) Realizar ajustes en el computador y televisor como cambiar la entrada y visualización del video.
Zeff - Kecewa 

Zeff is a band that can be contacted via their email or social media accounts. They will be performing their single "Kecewa" and wish to thank unspecified parties for their support.
Assistive technologies for efficient mid range wireless transmission of elect...

This document summarizes recent developments in mid-range wireless power transmission technologies. It discusses techniques like magnetic resonant coupling that can achieve higher transmission efficiencies over longer distances compared to basic inductive coupling. Developments discussed include using metamaterials and resonator arrays to further increase efficiency and range. Other topics covered are using coil shapes and additional relays to optimize efficiency, as well as powering moving vehicles through arrays of resonators. The document provides an overview of the key concepts and innovations in mid-range wireless power transmission.
Evaluación de-proceso-com-1 (1)

EVALUACION DE PROCESO 2016 EN EL AREA DE COMUNICACION APLICADO A ESTUDIANTES DEL PRIMER GRADO DE SECUNDARIA
Componentes de un computador de escritorio

Este documento resume los principales componentes de un computador de escritorio, incluyendo la memoria RAM, el microprocesador, la pila BIOS, el disco duro, la fuente de poder, la unidad de disco, la placa madre, el chasis, la unidad de disquete, el cable de poder, el monitor, el teclado y el mouse.
Recommended
Instalacion antivirus

Para instalar nuestro antivirus Kaspersky, debemos descargar el software instalador, abrir la carpeta de instalación, hacer doble clic en el instalador y seguir los pasos para extraer los archivos e iniciar el programa, activándolo con el código de la carpeta. Una vez completada la instalación, el antivirus estará en modo de prueba hasta renovar la licencia descargando e instalando el archivo de reinicio de prueba.
Conocimiento estudiante y didactica

Este documento presenta una serie de preguntas de opción múltiple relacionadas con conceptos del desarrollo psicológico infantil y adolescente, así como estrategias pedagógicas. Las preguntas abarcan temas como las etapas del desarrollo cognitivo según Piaget, el desarrollo moral según Kohlberg, características del desarrollo psicosocial y cognitivo en la infancia y adolescencia, estrategias para generar aprendizajes significativos, y el uso de instrumentos para evaluar la expresión oral.
Precentacion

Este documento presenta un caso sobre cómo conectar un computador de escritorio a un televisor de casa. Explica que se puede usar un cable HDMI y da los pasos a seguir: 1) Revisar los puertos HDMI en el computador y televisor, 2) Conectar el cable HDMI a ambos dispositivos, y 3) Realizar ajustes en el computador y televisor como cambiar la entrada y visualización del video.
Zeff - Kecewa 

Zeff is a band that can be contacted via their email or social media accounts. They will be performing their single "Kecewa" and wish to thank unspecified parties for their support.
Assistive technologies for efficient mid range wireless transmission of elect...

This document summarizes recent developments in mid-range wireless power transmission technologies. It discusses techniques like magnetic resonant coupling that can achieve higher transmission efficiencies over longer distances compared to basic inductive coupling. Developments discussed include using metamaterials and resonator arrays to further increase efficiency and range. Other topics covered are using coil shapes and additional relays to optimize efficiency, as well as powering moving vehicles through arrays of resonators. The document provides an overview of the key concepts and innovations in mid-range wireless power transmission.
Evaluación de-proceso-com-1 (1)

EVALUACION DE PROCESO 2016 EN EL AREA DE COMUNICACION APLICADO A ESTUDIANTES DEL PRIMER GRADO DE SECUNDARIA
Componentes de un computador de escritorio

Este documento resume los principales componentes de un computador de escritorio, incluyendo la memoria RAM, el microprocesador, la pila BIOS, el disco duro, la fuente de poder, la unidad de disco, la placa madre, el chasis, la unidad de disquete, el cable de poder, el monitor, el teclado y el mouse.
Imageeeeeeeeeeees

The document discusses strategies for promoting an acoustic-folk singer similar to Regina Spektor. It analyzes logos, album poster designs, target audiences, and record labels. While Warner Music Group could help with distribution due to its size, the document deems the label too mainstream for the artist, who is aiming for a niche audience of "Savants and Enthusiasts."
Technol2

The document discusses the various technologies used to create a music video project, including a Canon digital video camera, Panasonic Lumix digital stills camera, Apple Mac computer, Final Cut Express video editing software, and Photoshop image editing software. The key features and advantages of each technology are described, such as the video camera's zoom and image stabilization capabilities, the computer's processing power and graphics, and the software's professional editing tools. Some minor disadvantages are also noted, such as limited camera access time and a learning curve for the complex software.
Attracting audience

The document discusses strategies for attracting an audience to a music video through lighting, costumes, locations, camera angles, framing, and song choice. Natural lighting and vibrant colors were used to make the products and artist stand out. The model's unique boho-inspired costumes would attract an indie audience. Unusual locations like a supermarket aisle and green screen shots would grab attention. Varying camera angles and avoiding overcrowded frames maintains audience interest. While the folk song initially aimed to attract listeners, a different choice may have connected better.
Lily Allen

Lily Allen changed her brand image from retro to move forward and separate herself from others who had adopted a retro style. She altered her image to ensure her new brand image stood out and was noticed. Her original retro brand image risked becoming too common and could have harmed her career if she did not change and adapt her image.
Technol

The document discusses the various technologies used to produce a music video and ancillary tasks, including:
- A Canon video camera with advanced zoom and features to reduce shake was used to shoot all video footage.
- A Panasonic stills camera with high megapixels and optical zoom was used to take pictures of locations and the artist.
- An Apple Mac computer with large memory and advanced graphics was used for planning, designing, editing, and distributing the project due to its fast speed and ability to view high quality images.
- Final Cut Express video editing software, compatible with common formats, was used to edit the music video due to its ability to create professional looking videos with titles, graphics, filters and effects
Secondary Audience

This document discusses secondary target audiences, which are groups within the population that a company can identify and target but are not as important as the primary demographic. It lists some potential secondary target audiences such as males, friends, older or younger people, higher earners, casuals, and indifferents.
Audience Types

The target audience for the music video is defined as female, aged 16-24, from socio-economic classes C2, D, and E. Graham Burton identified three ways audiences can be defined: by particular products, types of media, and pre-existing groups like age, gender, and class. The document discusses attracting "enthusiasts" and "savants" who represent 25% of the 15-39 age group and have music as a key part or everything tied to their lives.
Innovations

The document discusses the success of various artists in the 1980s, 1990s, and 2000s that were similar in style or genre to the author's own innovations. It notes that Kate Bush, Alanis Morissette, Cyndi Lauper, Shania Twain, Eva Cassidy, Gwen Stefani, Lady Gaga, Regina Spektor, and Taylor Swift all found success with unique styles, pop-folk genres, or experimental sounds. This success of comparable artists in the same time periods led the author to believe their own innovations would also prove commercially successful.
Columbus Data & Analytics Wednesdays - June 2024

Columbus Data & Analytics Wednesdays, June 2024 with Maria Copot 20
GraphRAG for LifeSciences Hands-On with the Clinical Knowledge Graph

Tomaz Bratanic
Graph ML and GenAI Expert - Neo4j
GNSS spoofing via SDR (Criptored Talks 2024)

In the realm of cybersecurity, offensive security practices act as a critical shield. By simulating real-world attacks in a controlled environment, these techniques expose vulnerabilities before malicious actors can exploit them. This proactive approach allows manufacturers to identify and fix weaknesses, significantly enhancing system security.
This presentation delves into the development of a system designed to mimic Galileo's Open Service signal using software-defined radio (SDR) technology. We'll begin with a foundational overview of both Global Navigation Satellite Systems (GNSS) and the intricacies of digital signal processing.
The presentation culminates in a live demonstration. We'll showcase the manipulation of Galileo's Open Service pilot signal, simulating an attack on various software and hardware systems. This practical demonstration serves to highlight the potential consequences of unaddressed vulnerabilities, emphasizing the importance of offensive security practices in safeguarding critical infrastructure.
Leveraging the Graph for Clinical Trials and Standards

Katja Glaß
OpenStudyBuilder Community Manager - Katja Glaß Consulting
Marius Conjeaud
Principal Consultant - Neo4j
Freshworks Rethinks NoSQL for Rapid Scaling & Cost-Efficiency

Freshworks creates AI-boosted business software that helps employees work more efficiently and effectively. Managing data across multiple RDBMS and NoSQL databases was already a challenge at their current scale. To prepare for 10X growth, they knew it was time to rethink their database strategy. Learn how they architected a solution that would simplify scaling while keeping costs under control.
Must Know Postgres Extension for DBA and Developer during Migration

Mydbops Opensource Database Meetup 16
Topic: Must-Know PostgreSQL Extensions for Developers and DBAs During Migration
Speaker: Deepak Mahto, Founder of DataCloudGaze Consulting
Date & Time: 8th June | 10 AM - 1 PM IST
Venue: Bangalore International Centre, Bangalore
Abstract: Discover how PostgreSQL extensions can be your secret weapon! This talk explores how key extensions enhance database capabilities and streamline the migration process for users moving from other relational databases like Oracle.
Key Takeaways:
* Learn about crucial extensions like oracle_fdw, pgtt, and pg_audit that ease migration complexities.
* Gain valuable strategies for implementing these extensions in PostgreSQL to achieve license freedom.
* Discover how these key extensions can empower both developers and DBAs during the migration process.
* Don't miss this chance to gain practical knowledge from an industry expert and stay updated on the latest open-source database trends.
Mydbops Managed Services specializes in taking the pain out of database management while optimizing performance. Since 2015, we have been providing top-notch support and assistance for the top three open-source databases: MySQL, MongoDB, and PostgreSQL.
Our team offers a wide range of services, including assistance, support, consulting, 24/7 operations, and expertise in all relevant technologies. We help organizations improve their database's performance, scalability, efficiency, and availability.
Contact us: info@mydbops.com
Visit: https://www.mydbops.com/
Follow us on LinkedIn: https://in.linkedin.com/company/mydbops
For more details and updates, please follow up the below links.
Meetup Page : https://www.meetup.com/mydbops-databa...
Twitter: https://twitter.com/mydbopsofficial
Blogs: https://www.mydbops.com/blog/
Facebook(Meta): https://www.facebook.com/mydbops/
"$10 thousand per minute of downtime: architecture, queues, streaming and fin...

Direct losses from downtime in 1 minute = $5-$10 thousand dollars. Reputation is priceless.
As part of the talk, we will consider the architectural strategies necessary for the development of highly loaded fintech solutions. We will focus on using queues and streaming to efficiently work and manage large amounts of data in real-time and to minimize latency.
We will focus special attention on the architectural patterns used in the design of the fintech system, microservices and event-driven architecture, which ensure scalability, fault tolerance, and consistency of the entire system.
"Choosing proper type of scaling", Olena Syrota

Imagine an IoT processing system that is already quite mature and production-ready and for which client coverage is growing and scaling and performance aspects are life and death questions. The system has Redis, MongoDB, and stream processing based on ksqldb. In this talk, firstly, we will analyze scaling approaches and then select the proper ones for our system.
zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...

Folding is a recent technique for building efficient recursive SNARKs. Several elegant folding protocols have been proposed, such as Nova, Supernova, Hypernova, Protostar, and others. However, all of them rely on an additively homomorphic commitment scheme based on discrete log, and are therefore not post-quantum secure. In this work we present LatticeFold, the first lattice-based folding protocol based on the Module SIS problem. This folding protocol naturally leads to an efficient recursive lattice-based SNARK and an efficient PCD scheme. LatticeFold supports folding low-degree relations, such as R1CS, as well as high-degree relations, such as CCS. The key challenge is to construct a secure folding protocol that works with the Ajtai commitment scheme. The difficulty, is ensuring that extracted witnesses are low norm through many rounds of folding. We present a novel technique using the sumcheck protocol to ensure that extracted witnesses are always low norm no matter how many rounds of folding are used. Our evaluation of the final proof system suggests that it is as performant as Hypernova, while providing post-quantum security.
Paper Link: https://eprint.iacr.org/2024/257
"Scaling RAG Applications to serve millions of users", Kevin Goedecke

How we managed to grow and scale a RAG application from zero to thousands of users in 7 months. Lessons from technical challenges around managing high load for LLMs, RAGs and Vector databases.
“Temporal Event Neural Networks: A More Efficient Alternative to the Transfor...

“Temporal Event Neural Networks: A More Efficient Alternative to the Transfor...Edge AI and Vision Alliance
For the full video of this presentation, please visit: https://www.edge-ai-vision.com/2024/06/temporal-event-neural-networks-a-more-efficient-alternative-to-the-transformer-a-presentation-from-brainchip/
Chris Jones, Director of Product Management at BrainChip , presents the “Temporal Event Neural Networks: A More Efficient Alternative to the Transformer” tutorial at the May 2024 Embedded Vision Summit.
The expansion of AI services necessitates enhanced computational capabilities on edge devices. Temporal Event Neural Networks (TENNs), developed by BrainChip, represent a novel and highly efficient state-space network. TENNs demonstrate exceptional proficiency in handling multi-dimensional streaming data, facilitating advancements in object detection, action recognition, speech enhancement and language model/sequence generation. Through the utilization of polynomial-based continuous convolutions, TENNs streamline models, expedite training processes and significantly diminish memory requirements, achieving notable reductions of up to 50x in parameters and 5,000x in energy consumption compared to prevailing methodologies like transformers.
Integration with BrainChip’s Akida neuromorphic hardware IP further enhances TENNs’ capabilities, enabling the realization of highly capable, portable and passively cooled edge devices. This presentation delves into the technical innovations underlying TENNs, presents real-world benchmarks, and elucidates how this cutting-edge approach is positioned to revolutionize edge AI across diverse applications.More Related Content
More from Lauren
Imageeeeeeeeeeees

The document discusses strategies for promoting an acoustic-folk singer similar to Regina Spektor. It analyzes logos, album poster designs, target audiences, and record labels. While Warner Music Group could help with distribution due to its size, the document deems the label too mainstream for the artist, who is aiming for a niche audience of "Savants and Enthusiasts."
Technol2

The document discusses the various technologies used to create a music video project, including a Canon digital video camera, Panasonic Lumix digital stills camera, Apple Mac computer, Final Cut Express video editing software, and Photoshop image editing software. The key features and advantages of each technology are described, such as the video camera's zoom and image stabilization capabilities, the computer's processing power and graphics, and the software's professional editing tools. Some minor disadvantages are also noted, such as limited camera access time and a learning curve for the complex software.
Attracting audience

The document discusses strategies for attracting an audience to a music video through lighting, costumes, locations, camera angles, framing, and song choice. Natural lighting and vibrant colors were used to make the products and artist stand out. The model's unique boho-inspired costumes would attract an indie audience. Unusual locations like a supermarket aisle and green screen shots would grab attention. Varying camera angles and avoiding overcrowded frames maintains audience interest. While the folk song initially aimed to attract listeners, a different choice may have connected better.
Lily Allen

Lily Allen changed her brand image from retro to move forward and separate herself from others who had adopted a retro style. She altered her image to ensure her new brand image stood out and was noticed. Her original retro brand image risked becoming too common and could have harmed her career if she did not change and adapt her image.
Technol

The document discusses the various technologies used to produce a music video and ancillary tasks, including:
- A Canon video camera with advanced zoom and features to reduce shake was used to shoot all video footage.
- A Panasonic stills camera with high megapixels and optical zoom was used to take pictures of locations and the artist.
- An Apple Mac computer with large memory and advanced graphics was used for planning, designing, editing, and distributing the project due to its fast speed and ability to view high quality images.
- Final Cut Express video editing software, compatible with common formats, was used to edit the music video due to its ability to create professional looking videos with titles, graphics, filters and effects
Secondary Audience

This document discusses secondary target audiences, which are groups within the population that a company can identify and target but are not as important as the primary demographic. It lists some potential secondary target audiences such as males, friends, older or younger people, higher earners, casuals, and indifferents.
Audience Types

The target audience for the music video is defined as female, aged 16-24, from socio-economic classes C2, D, and E. Graham Burton identified three ways audiences can be defined: by particular products, types of media, and pre-existing groups like age, gender, and class. The document discusses attracting "enthusiasts" and "savants" who represent 25% of the 15-39 age group and have music as a key part or everything tied to their lives.
Innovations

The document discusses the success of various artists in the 1980s, 1990s, and 2000s that were similar in style or genre to the author's own innovations. It notes that Kate Bush, Alanis Morissette, Cyndi Lauper, Shania Twain, Eva Cassidy, Gwen Stefani, Lady Gaga, Regina Spektor, and Taylor Swift all found success with unique styles, pop-folk genres, or experimental sounds. This success of comparable artists in the same time periods led the author to believe their own innovations would also prove commercially successful.
More from Lauren (10)
Recently uploaded
Columbus Data & Analytics Wednesdays - June 2024

Columbus Data & Analytics Wednesdays, June 2024 with Maria Copot 20
GraphRAG for LifeSciences Hands-On with the Clinical Knowledge Graph

Tomaz Bratanic
Graph ML and GenAI Expert - Neo4j
GNSS spoofing via SDR (Criptored Talks 2024)

In the realm of cybersecurity, offensive security practices act as a critical shield. By simulating real-world attacks in a controlled environment, these techniques expose vulnerabilities before malicious actors can exploit them. This proactive approach allows manufacturers to identify and fix weaknesses, significantly enhancing system security.
This presentation delves into the development of a system designed to mimic Galileo's Open Service signal using software-defined radio (SDR) technology. We'll begin with a foundational overview of both Global Navigation Satellite Systems (GNSS) and the intricacies of digital signal processing.
The presentation culminates in a live demonstration. We'll showcase the manipulation of Galileo's Open Service pilot signal, simulating an attack on various software and hardware systems. This practical demonstration serves to highlight the potential consequences of unaddressed vulnerabilities, emphasizing the importance of offensive security practices in safeguarding critical infrastructure.
Leveraging the Graph for Clinical Trials and Standards

Katja Glaß
OpenStudyBuilder Community Manager - Katja Glaß Consulting
Marius Conjeaud
Principal Consultant - Neo4j
Freshworks Rethinks NoSQL for Rapid Scaling & Cost-Efficiency

Freshworks creates AI-boosted business software that helps employees work more efficiently and effectively. Managing data across multiple RDBMS and NoSQL databases was already a challenge at their current scale. To prepare for 10X growth, they knew it was time to rethink their database strategy. Learn how they architected a solution that would simplify scaling while keeping costs under control.
Must Know Postgres Extension for DBA and Developer during Migration

Mydbops Opensource Database Meetup 16
Topic: Must-Know PostgreSQL Extensions for Developers and DBAs During Migration
Speaker: Deepak Mahto, Founder of DataCloudGaze Consulting
Date & Time: 8th June | 10 AM - 1 PM IST
Venue: Bangalore International Centre, Bangalore
Abstract: Discover how PostgreSQL extensions can be your secret weapon! This talk explores how key extensions enhance database capabilities and streamline the migration process for users moving from other relational databases like Oracle.
Key Takeaways:
* Learn about crucial extensions like oracle_fdw, pgtt, and pg_audit that ease migration complexities.
* Gain valuable strategies for implementing these extensions in PostgreSQL to achieve license freedom.
* Discover how these key extensions can empower both developers and DBAs during the migration process.
* Don't miss this chance to gain practical knowledge from an industry expert and stay updated on the latest open-source database trends.
Mydbops Managed Services specializes in taking the pain out of database management while optimizing performance. Since 2015, we have been providing top-notch support and assistance for the top three open-source databases: MySQL, MongoDB, and PostgreSQL.
Our team offers a wide range of services, including assistance, support, consulting, 24/7 operations, and expertise in all relevant technologies. We help organizations improve their database's performance, scalability, efficiency, and availability.
Contact us: info@mydbops.com
Visit: https://www.mydbops.com/
Follow us on LinkedIn: https://in.linkedin.com/company/mydbops
For more details and updates, please follow up the below links.
Meetup Page : https://www.meetup.com/mydbops-databa...
Twitter: https://twitter.com/mydbopsofficial
Blogs: https://www.mydbops.com/blog/
Facebook(Meta): https://www.facebook.com/mydbops/
"$10 thousand per minute of downtime: architecture, queues, streaming and fin...

Direct losses from downtime in 1 minute = $5-$10 thousand dollars. Reputation is priceless.
As part of the talk, we will consider the architectural strategies necessary for the development of highly loaded fintech solutions. We will focus on using queues and streaming to efficiently work and manage large amounts of data in real-time and to minimize latency.
We will focus special attention on the architectural patterns used in the design of the fintech system, microservices and event-driven architecture, which ensure scalability, fault tolerance, and consistency of the entire system.
"Choosing proper type of scaling", Olena Syrota

Imagine an IoT processing system that is already quite mature and production-ready and for which client coverage is growing and scaling and performance aspects are life and death questions. The system has Redis, MongoDB, and stream processing based on ksqldb. In this talk, firstly, we will analyze scaling approaches and then select the proper ones for our system.
zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...

Folding is a recent technique for building efficient recursive SNARKs. Several elegant folding protocols have been proposed, such as Nova, Supernova, Hypernova, Protostar, and others. However, all of them rely on an additively homomorphic commitment scheme based on discrete log, and are therefore not post-quantum secure. In this work we present LatticeFold, the first lattice-based folding protocol based on the Module SIS problem. This folding protocol naturally leads to an efficient recursive lattice-based SNARK and an efficient PCD scheme. LatticeFold supports folding low-degree relations, such as R1CS, as well as high-degree relations, such as CCS. The key challenge is to construct a secure folding protocol that works with the Ajtai commitment scheme. The difficulty, is ensuring that extracted witnesses are low norm through many rounds of folding. We present a novel technique using the sumcheck protocol to ensure that extracted witnesses are always low norm no matter how many rounds of folding are used. Our evaluation of the final proof system suggests that it is as performant as Hypernova, while providing post-quantum security.
Paper Link: https://eprint.iacr.org/2024/257
"Scaling RAG Applications to serve millions of users", Kevin Goedecke

How we managed to grow and scale a RAG application from zero to thousands of users in 7 months. Lessons from technical challenges around managing high load for LLMs, RAGs and Vector databases.
“Temporal Event Neural Networks: A More Efficient Alternative to the Transfor...

“Temporal Event Neural Networks: A More Efficient Alternative to the Transfor...Edge AI and Vision Alliance
For the full video of this presentation, please visit: https://www.edge-ai-vision.com/2024/06/temporal-event-neural-networks-a-more-efficient-alternative-to-the-transformer-a-presentation-from-brainchip/
Chris Jones, Director of Product Management at BrainChip , presents the “Temporal Event Neural Networks: A More Efficient Alternative to the Transformer” tutorial at the May 2024 Embedded Vision Summit.
The expansion of AI services necessitates enhanced computational capabilities on edge devices. Temporal Event Neural Networks (TENNs), developed by BrainChip, represent a novel and highly efficient state-space network. TENNs demonstrate exceptional proficiency in handling multi-dimensional streaming data, facilitating advancements in object detection, action recognition, speech enhancement and language model/sequence generation. Through the utilization of polynomial-based continuous convolutions, TENNs streamline models, expedite training processes and significantly diminish memory requirements, achieving notable reductions of up to 50x in parameters and 5,000x in energy consumption compared to prevailing methodologies like transformers.
Integration with BrainChip’s Akida neuromorphic hardware IP further enhances TENNs’ capabilities, enabling the realization of highly capable, portable and passively cooled edge devices. This presentation delves into the technical innovations underlying TENNs, presents real-world benchmarks, and elucidates how this cutting-edge approach is positioned to revolutionize edge AI across diverse applications.Skybuffer SAM4U tool for SAP license adoption

Manage and optimize your license adoption and consumption with SAM4U, an SAP free customer software asset management tool.
SAM4U, an SAP complimentary software asset management tool for customers, delivers a detailed and well-structured overview of license inventory and usage with a user-friendly interface. We offer a hosted, cost-effective, and performance-optimized SAM4U setup in the Skybuffer Cloud environment. You retain ownership of the system and data, while we manage the ABAP 7.58 infrastructure, ensuring fixed Total Cost of Ownership (TCO) and exceptional services through the SAP Fiori interface.
inQuba Webinar Mastering Customer Journey Management with Dr Graham Hill

HERE IS YOUR WEBINAR CONTENT! 'Mastering Customer Journey Management with Dr. Graham Hill'. We hope you find the webinar recording both insightful and enjoyable.
In this webinar, we explored essential aspects of Customer Journey Management and personalization. Here’s a summary of the key insights and topics discussed:
Key Takeaways:
Understanding the Customer Journey: Dr. Hill emphasized the importance of mapping and understanding the complete customer journey to identify touchpoints and opportunities for improvement.
Personalization Strategies: We discussed how to leverage data and insights to create personalized experiences that resonate with customers.
Technology Integration: Insights were shared on how inQuba’s advanced technology can streamline customer interactions and drive operational efficiency.
Monitoring and Managing Anomaly Detection on OpenShift.pdf

Monitoring and Managing Anomaly Detection on OpenShift
Overview
Dive into the world of anomaly detection on edge devices with our comprehensive hands-on tutorial. This SlideShare presentation will guide you through the entire process, from data collection and model training to edge deployment and real-time monitoring. Perfect for those looking to implement robust anomaly detection systems on resource-constrained IoT/edge devices.
Key Topics Covered
1. Introduction to Anomaly Detection
- Understand the fundamentals of anomaly detection and its importance in identifying unusual behavior or failures in systems.
2. Understanding Edge (IoT)
- Learn about edge computing and IoT, and how they enable real-time data processing and decision-making at the source.
3. What is ArgoCD?
- Discover ArgoCD, a declarative, GitOps continuous delivery tool for Kubernetes, and its role in deploying applications on edge devices.
4. Deployment Using ArgoCD for Edge Devices
- Step-by-step guide on deploying anomaly detection models on edge devices using ArgoCD.
5. Introduction to Apache Kafka and S3
- Explore Apache Kafka for real-time data streaming and Amazon S3 for scalable storage solutions.
6. Viewing Kafka Messages in the Data Lake
- Learn how to view and analyze Kafka messages stored in a data lake for better insights.
7. What is Prometheus?
- Get to know Prometheus, an open-source monitoring and alerting toolkit, and its application in monitoring edge devices.
8. Monitoring Application Metrics with Prometheus
- Detailed instructions on setting up Prometheus to monitor the performance and health of your anomaly detection system.
9. What is Camel K?
- Introduction to Camel K, a lightweight integration framework built on Apache Camel, designed for Kubernetes.
10. Configuring Camel K Integrations for Data Pipelines
- Learn how to configure Camel K for seamless data pipeline integrations in your anomaly detection workflow.
11. What is a Jupyter Notebook?
- Overview of Jupyter Notebooks, an open-source web application for creating and sharing documents with live code, equations, visualizations, and narrative text.
12. Jupyter Notebooks with Code Examples
- Hands-on examples and code snippets in Jupyter Notebooks to help you implement and test anomaly detection models.
5th LF Energy Power Grid Model Meet-up Slides

5th Power Grid Model Meet-up
It is with great pleasure that we extend to you an invitation to the 5th Power Grid Model Meet-up, scheduled for 6th June 2024. This event will adopt a hybrid format, allowing participants to join us either through an online Mircosoft Teams session or in person at TU/e located at Den Dolech 2, Eindhoven, Netherlands. The meet-up will be hosted by Eindhoven University of Technology (TU/e), a research university specializing in engineering science & technology.
Power Grid Model
The global energy transition is placing new and unprecedented demands on Distribution System Operators (DSOs). Alongside upgrades to grid capacity, processes such as digitization, capacity optimization, and congestion management are becoming vital for delivering reliable services.
Power Grid Model is an open source project from Linux Foundation Energy and provides a calculation engine that is increasingly essential for DSOs. It offers a standards-based foundation enabling real-time power systems analysis, simulations of electrical power grids, and sophisticated what-if analysis. In addition, it enables in-depth studies and analysis of the electrical power grid’s behavior and performance. This comprehensive model incorporates essential factors such as power generation capacity, electrical losses, voltage levels, power flows, and system stability.
Power Grid Model is currently being applied in a wide variety of use cases, including grid planning, expansion, reliability, and congestion studies. It can also help in analyzing the impact of renewable energy integration, assessing the effects of disturbances or faults, and developing strategies for grid control and optimization.
What to expect
For the upcoming meetup we are organizing, we have an exciting lineup of activities planned:
-Insightful presentations covering two practical applications of the Power Grid Model.
-An update on the latest advancements in Power Grid -Model technology during the first and second quarters of 2024.
-An interactive brainstorming session to discuss and propose new feature requests.
-An opportunity to connect with fellow Power Grid Model enthusiasts and users.
AppSec PNW: Android and iOS Application Security with MobSF

Mobile Security Framework - MobSF is a free and open source automated mobile application security testing environment designed to help security engineers, researchers, developers, and penetration testers to identify security vulnerabilities, malicious behaviours and privacy concerns in mobile applications using static and dynamic analysis. It supports all the popular mobile application binaries and source code formats built for Android and iOS devices. In addition to automated security assessment, it also offers an interactive testing environment to build and execute scenario based test/fuzz cases against the application.
This talk covers:
Using MobSF for static analysis of mobile applications.
Interactive dynamic security assessment of Android and iOS applications.
Solving Mobile app CTF challenges.
Reverse engineering and runtime analysis of Mobile malware.
How to shift left and integrate MobSF/mobsfscan SAST and DAST in your build pipeline.
Fueling AI with Great Data with Airbyte Webinar

This talk will focus on how to collect data from a variety of sources, leveraging this data for RAG and other GenAI use cases, and finally charting your course to productionalization.
Essentials of Automations: Exploring Attributes & Automation Parameters

Building automations in FME Flow can save time, money, and help businesses scale by eliminating data silos and providing data to stakeholders in real-time. One essential component to orchestrating complex automations is the use of attributes & automation parameters (both formerly known as “keys”). In fact, it’s unlikely you’ll ever build an Automation without using these components, but what exactly are they?
Attributes & automation parameters enable the automation author to pass data values from one automation component to the next. During this webinar, our FME Flow Specialists will cover leveraging the three types of these output attributes & parameters in FME Flow: Event, Custom, and Automation. As a bonus, they’ll also be making use of the Split-Merge Block functionality.
You’ll leave this webinar with a better understanding of how to maximize the potential of automations by making use of attributes & automation parameters, with the ultimate goal of setting your enterprise integration workflows up on autopilot.
Apps Break Data

How information systems are built or acquired puts information, which is what they should be about, in a secondary place. Our language adapted accordingly, and we no longer talk about information systems but applications. Applications evolved in a way to break data into diverse fragments, tightly coupled with applications and expensive to integrate. The result is technical debt, which is re-paid by taking even bigger "loans", resulting in an ever-increasing technical debt. Software engineering and procurement practices work in sync with market forces to maintain this trend. This talk demonstrates how natural this situation is. The question is: can something be done to reverse the trend?
Recently uploaded (20)
GraphRAG for LifeSciences Hands-On with the Clinical Knowledge Graph

GraphRAG for LifeSciences Hands-On with the Clinical Knowledge Graph
Leveraging the Graph for Clinical Trials and Standards

Leveraging the Graph for Clinical Trials and Standards
Freshworks Rethinks NoSQL for Rapid Scaling & Cost-Efficiency

Freshworks Rethinks NoSQL for Rapid Scaling & Cost-Efficiency
Must Know Postgres Extension for DBA and Developer during Migration

Must Know Postgres Extension for DBA and Developer during Migration
"$10 thousand per minute of downtime: architecture, queues, streaming and fin...

"$10 thousand per minute of downtime: architecture, queues, streaming and fin...
zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...

zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...
"Scaling RAG Applications to serve millions of users", Kevin Goedecke

"Scaling RAG Applications to serve millions of users", Kevin Goedecke
Nordic Marketo Engage User Group_June 13_ 2024.pptx

Nordic Marketo Engage User Group_June 13_ 2024.pptx
“Temporal Event Neural Networks: A More Efficient Alternative to the Transfor...

“Temporal Event Neural Networks: A More Efficient Alternative to the Transfor...
inQuba Webinar Mastering Customer Journey Management with Dr Graham Hill

inQuba Webinar Mastering Customer Journey Management with Dr Graham Hill
Monitoring and Managing Anomaly Detection on OpenShift.pdf

Monitoring and Managing Anomaly Detection on OpenShift.pdf
AppSec PNW: Android and iOS Application Security with MobSF

AppSec PNW: Android and iOS Application Security with MobSF
Essentials of Automations: Exploring Attributes & Automation Parameters

Essentials of Automations: Exploring Attributes & Automation Parameters
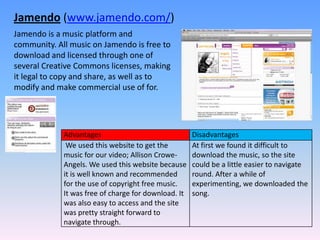
Technol software#
- 1. Jamendo (www.jamendo.com/) Jamendo is a music platform and community. All music on Jamendo is free to download and licensed through one of several Creative Commons licenses, making it legal to copy and share, as well as to modify and make commercial use of for.
- 2. Wikipedia(http://en.wikipedia.org/) Wikipedia is a free, web-based, collaborative encyclopedia project supported by the non-profit Wikimedia Foundation. It was launched in 2001 and is currently the largest and most popular general reference work on the Internet.
- 3. AOL (http://webmail.aol.com/) AOL Mail is a web-based email service provided by AOL. Its main competitors are Gmail, Windows Live Hotmail and Yahoo! Mail. AOL Mail is free and also features an option for creating an email address for a custom domain.
- 4. YouTube(http://www.youtube.com/) YouTube is a video sharing website on which users can upload and share videos. It uses Adobe Flash Video technology to display a wide variety of user-generated video content, including movie clips, TV clips, and music videos, as well as amateur content such as video blogging and short original videos. Most of the content on YouTube has been uploaded by individuals, although media corporations including CBS, the BBC, UMG and other organizations offer some of their material via the site, as part of the YouTube partnership program.
- 5. Blogger(www.blogger.com/) Blogger is a blog storage service that allows private or multi-user blogs with time-stamped entries. It is funded by on-screen ads. Generally, the blogs are hosted by Google at subdomains of blogspot.com. this was a website that we have used frequently throughout the creation of our coursework.
- 6. Dafont(http://www.dafont.com/) An online website that provides internet users with lots of interesting fonts to download free of charge. You can preview the fonts to check their suitability before you download.
- 7. Microsoft PowerPoint Microsoft PowerPoint is a presentation program by Microsoft. It is part of the Microsoft Office suite, and runs on Microsoft Windows and Apple Mac OS X operating system. I personally used this to create a presentation for artist branding, to put it into an easy to understand format for the research on our blog.