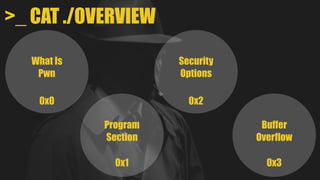
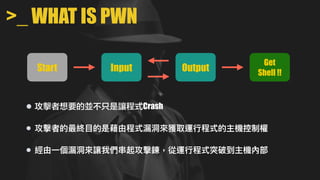
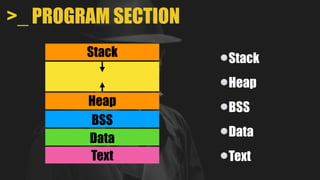
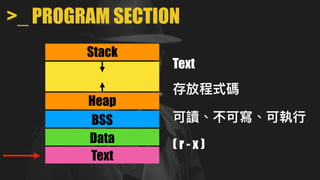
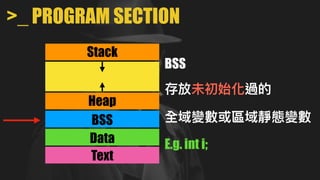
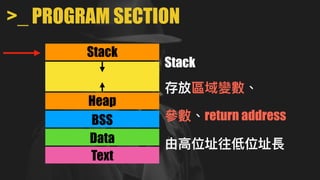
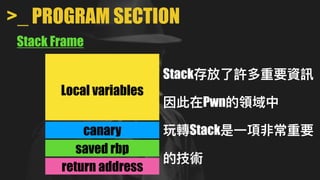
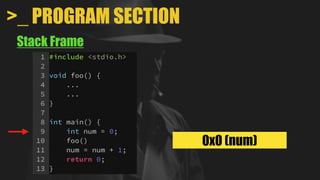
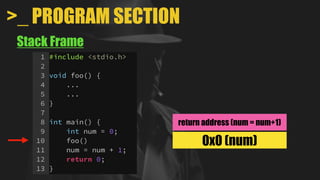
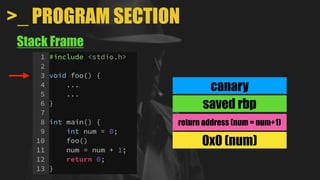
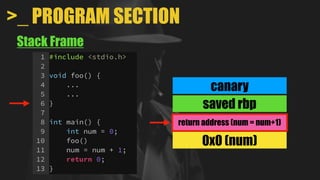
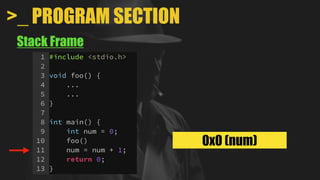
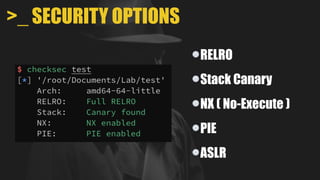
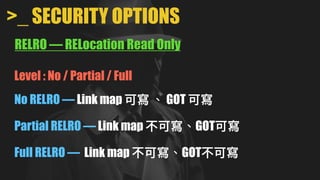
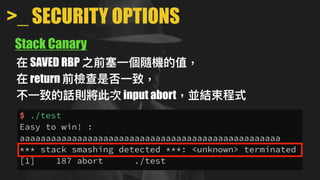
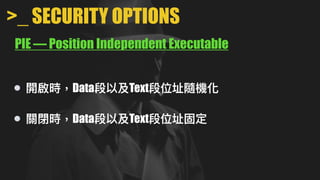
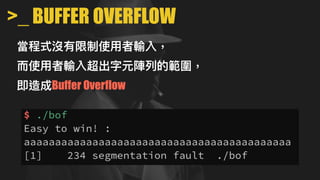
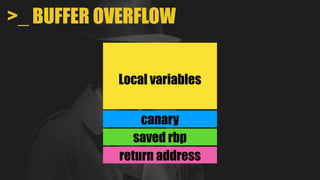
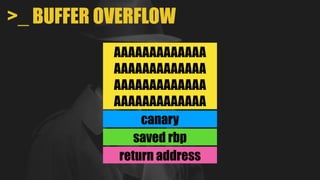
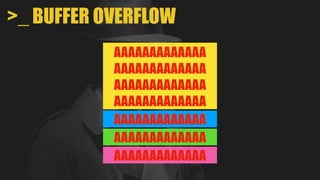
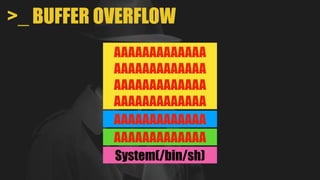
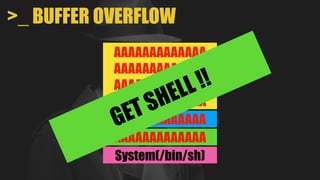
This document discusses binary exploitation techniques, specifically buffer overflows. It begins with an overview of program memory sections like the stack, heap, data, and text. It then covers security options like RELRO, stack canaries, and ASLR that aim to prevent exploits. Finally, it dives into buffer overflows, explaining how overflowing a buffer can overwrite the return address on the stack to redirect program flow and potentially execute shellcode to get remote code execution. The goal of "pwn" techniques is to leverage program vulnerabilities to gain control of the target system.