User can get help from assistant for any query.
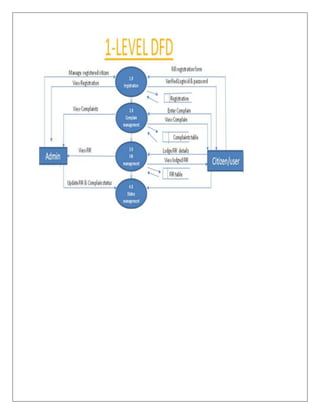
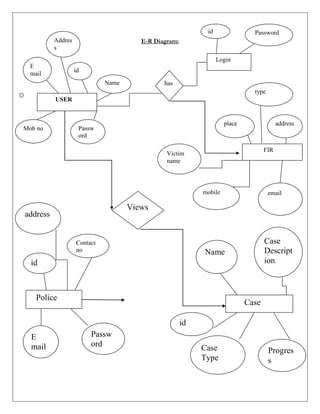
Login:
Registered user can login into the system by providing valid username and password.
Add Crime Details:
Member can add crime details like criminal name, crime type, location etc.
View Crime Details:
All user can view crime details added by member.
Update Crime Details:
Member can update existing crime details.
Delete Crime Details:
Member can delete existing crime details.
Add News:
Admin can add latest news related to crime.
View News:
All user can view latest news added by admin.