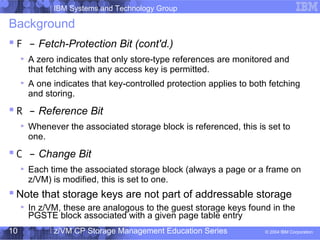
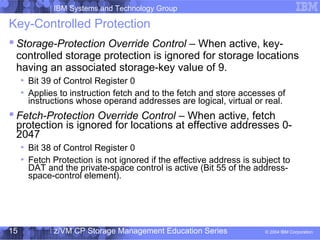
This document provides an overview of storage protection mechanisms on z/Architecture systems, including key-controlled protection, access-list-controlled protection, page protection, and low-address protection. It defines important concepts like virtual addresses, real addresses, and storage keys. It describes how access keys are determined and how violations of protection are handled for different types of storage access, including via the CPU, channels, and measurement blocks. Override controls for storage protection and fetch protection are also outlined.