ISS SA: Spector360 Funcionalidad para Mantener la privacidad
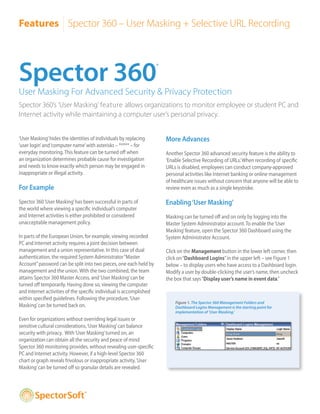
- 1. Features Spector 360 – User Masking + Selective URL Recording Spector 360 ® User Masking For Advanced Security & Privacy Protection Spector 360’s ‘User Masking’ feature allows organizations to monitor employee or student PC and Internet activity while maintaining a computer user’s personal privacy. ‘User Masking’ hides the identities of individuals by replacing More Advances ‘user login’ and ‘computer name’ with asterisks – ***** – for everyday monitoring. This feature can be turned off when Another Spector 360 advanced security feature is the ability to an organization determines probable cause for investigation ‘Enable Selective Recording of URLs.’ When recording of specific and needs to know exactly which person may be engaged in URLs is disabled, employees can conduct company-approved inappropriate or illegal activity. personal activities like Internet banking or online management of healthcare issues without concern that anyone will be able to For Example review even as much as a single keystroke. Spector 360 ‘User Masking’ has been successful in parts of Enabling ‘User Masking’ the world where viewing a specific individual’s computer and Internet activities is either prohibited or considered Masking can be turned off and on only by logging into the unacceptable management policy. Master System Administrator account. To enable the ‘User Masking’ feature, open the Spector 360 Dashboard using the In parts of the European Union, for example, viewing recorded System Administrator Account. PC and Internet activity requires a joint decision between management and a union representative. In this case of dual Click on the Management button in the lower left corner, then authentication, the required System Administrator “Master click on “Dashboard Logins” in the upper left – see Figure 1 Account” password can be split into two pieces, one each held by below – to display users who have access to a Dashboard login. management and the union. With the two combined, the team Modify a user by double-clicking the user’s name, then uncheck attains Spector 360 Master Access, and ‘User Masking’ can be the box that says “Display user’s name in event data.” turned off temporarily. Having done so, viewing the computer and Internet activities of the specific individual is accomplished within specified guidelines. Following the procedure, ‘User Figure 1. The Spector 360 Management Folders and Masking’ can be turned back on. Dashboard Logins Management is the starting point for implementation of ‘User Masking.’ Even for organizations without overriding legal issues or sensitive cultural considerations, ‘User Masking’ can balance security with privacy. With ‘User Masking’ turned on, an organization can obtain all the security and peace of mind Spector 360 monitoring provides, without revealing user-specific PC and Internet activity. However, if a high-level Spector 360 chart or graph reveals frivolous or inappropriate activity, ‘User Masking’ can be turned off so granular details are revealed. ®
- 2. Features Spector 360 – User Masking + Selective URL Recording Ensure Employee Privacy with Spector 360 ‘User Masking’ and ‘Selective Recording’ of URLs Figures 2 through 5a depict actual Spector 360 screen snapshots, showing what is seen – and unseen – when implementing ‘User Masking’ as well as ‘Selective Recording of URLs.’ Figure 2. With ‘User Masking’ on, the Spector 360 Dashboard Login displays asterisks where specific user names previously appeared. Masking OFF Checked by default, this option displays the user’s name in all Event Data. Masking ON With the option unchecked, all user names are masked by asterisks. Figure 3. Spector 360 charts and graphs provide valuable trend data with or without user specificity. Masking OFF Masking ON ®
- 3. Features Spector 360 – User Masking + Selective URL Recording Figure 4. Where law or culture dictates protection of computer user identities, Spector 360 ‘User Masking’ will still provide all the Events necessary to detect frivolous or inappropriate activity. Masking OFF Masking ON Figure 5. The ability to enable ‘Selective Recording’ of URLs is just one of many advanced security features in Spector 360. When recording of specific URLs is disabled, employees can conduct company-approved personal activities – such as Internet banking or online management of healthcare issues – confident in the knowledge that nobody will be able to review even as much as a single keystroke. Figure 5a. With ‘Selective Program Instance Active Time Focus Time Total Time Window Caption Recording’ of URLs enabled, Program Activity is noted but URL titles are not recorded, and neither is any activity occurring during the URL visit. Selective Recording ENABLED Program Activity ® 1.888.598.2788 toll-free www.spector360.com © 1998-2010 SpectorSoft® Corporation. All rights reserved. All other trademarks are the property of their respective owners. 072010
