Software version numbering - DSL of change
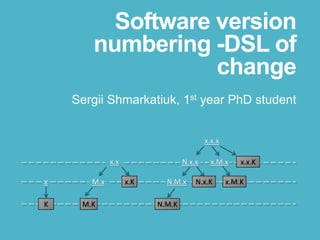
- 1. Software version numbering -DSL of change Sergii Shmarkatiuk, 1st year PhD student x.x x.KM.x M.K x K x.x.x x.x.KN.x.x N.M.K x.M.x x.M.KN.M.x N.x.K
- 2. Motivation
- 3. SCM practices Version control Build & deployment management Continuous integration Release management Dependencies management Merge management Version numbering
- 4. Software development activities Software testing Software implementation Project management Process management Software support & maintenance Version numbering
- 5. Version numbers are everywhere!
- 7. Why do we need version numbers? • Label unique states of software applications for future reference • Introduce continuity for history of software changes • Track progress of software development • Establish dependencies between modules, libraries, applications, APIs, etc
- 8. Problem: version numbering is broken • Ambiguous. Same version number often used to refer to different entities (e.g. builds and branches) • Unpredictable/inconsistent: 1.0 -> 1.1 - > 1.2 -> 2.0 -> 2.1 -> 3.1 • Not formalized • Cannot be used to serve its purpose (reliable reference, continuity, tracking progress, establishing dependencies)
- 9. Problem: version numbering is broken Inconsistent version numbering practices: • Undermine possibilities of development process automation • Increase need of communication • Become one of the causes of poor software quality • Cause many problems related to software maintenance and support
- 10. Problem: version numbering is broken
- 11. Root cause of the problem Version numbering is falsely associated with sections numbering and plain tree structure
- 12. Automatic document sections numbering 1. Consistent 2. Incremental 3. Formalized 4. Automated 5. Is not ambiguous. Two different sections cannot have the same section number 6. Section numbers can be ordered: 1.2.1 < 1.2.2 < 1.2.3 2.1 < 2.2 < 2.3 1.1 < 4.2 < 5 7. Section numbers unambiguously indicate parent and child sections (subsets): 1.1.1 ⊂ 1.1 ⊂ 1 1.1.1 ⊂ 1 1.2.1 ⊂ 1.2 ⊂ 1 1.2.1 ⊂ 1 1.2.2 ⊂ 1.2 ⊂ 1 1.2.2 ⊂ 1 1.2.3 ⊂ 1.2 ⊂ 1 1.2.3 ⊂ 1
- 13. Automatic document sections numbering Can be reused to number nodes of any tree
- 14. Automatic document sections numbering cannot be applied to software history 1.0.0 1.0.1 1.0.2 1.0 Δ1 Δ2 Δ3 1.0.0 ⊃ 1.0.1 ⊃ 1.0.2 ? Δ1 Δ1 + Δ2 Δ1 + Δ2 + Δ3
- 15. 1.0.0 1.0.1 1.0.2 1.0 Δ1 Δ2 Δ3 1.0.0 ⊅ 1.0.1 ⊅ 1.0.2 ! Δ1 Δ1 -Δ + Δ2 Δ1 -Δ + Δ2 -Δ + Δ3 -Δ -Δ 1.0.0 ⊅ 1.0! Automatic document sections numbering cannot be applied to software history
- 16. It is possible to come up with two different entities with the same number: Automatic document sections numbering cannot be applied to software history 1.1 1.1.1 1.2 1.2.1 1.2.2 1.2.3 ? 1.2.1.1 1.2.1.2
- 17. It is possible to come up with two different entities with the same number: Automatic document sections numbering cannot be applied to software history 1.1 1.1.1 1.2 1.2.1 1.2.2 1.2.3 1.2.2 1.2.1.1 1.2.1.2
- 18. It is possible to come up with two different entities with the same number: Automatic document sections numbering cannot be applied to software history 1.1 1.1.1 1.2 1.2.1 1.2.2 1.2.3 1.2.3 1.2.1.1 1.2.1.2
- 19. It is possible to come up with two different entities with the same number: Automatic document sections numbering cannot be applied to software history 1.1 1.1.1 1.2 1.2.1 1.2.2 1.2.3 1.2.1.1 1.2.1.1 1.2.1.2
- 20. It is possible to come up with two different entities with the same number: Automatic document sections numbering cannot be applied to software history 1.1 1.1.1 1.2 1.2.1 1.2.2 1.2.3 1.2.1.2 1.2.1.1 1.2.1.2
- 21. It is possible to come up with two different entities with the same number: Automatic document sections numbering cannot be applied to software history 1.1 1.1.1 1.2 1.2.1 1.2.2 1.2.3 1.2.4 1.2.1.1 1.2.1.2
- 22. It is possible to come up with two different entities with the same number: Automatic document sections numbering cannot be applied to software history 1.1 1.1.1 1.2 1.2.1 1.2.2 1.2.3 1.2.1.3 1.2.1.1 1.2.1.2
- 23. There are other problems … 1.0 1.1 1.2 1.0
- 24. There are other problems … variation variant #1 #2 #3 #N… version Maturity Platform OS Localizatio n Build type …
- 25. There are other problems … HTC_Touch_Diamond2_WM6.5_RUU_Topaz_S_HT C_RUS_2.16.411.2_Radio_Sign_Topaz_61.44 tc.25.32_4.49.25.17_Ship.exe Real world example:
- 26. There are other problems … HTC_Touch_Diamond2_WM6.5_RUU_Topaz_S_HT C_RUS_2.16.411.2_Radio_Sign_Topaz_61.44 tc.25.32_4.49.25.17_Ship.exe Real world example: Where is version?
- 27. There are other problems … HTC_Touch_Diamond2_WM6.5_RUU_Topaz_S_HT C_RUS_2.16.411.2_Radio_Sign_Topaz_61.44 tc.25.32_4.49.25.17_Ship.exe Real world example: Where is version?
- 28. There are other problems … HTC_Touch_Diamond2_WM6.5_RUU_Topaz_S_HT C_RUS_2.16.411.2_Radio_Sign_Topaz_61.44 tc.25.32_4.49.25.17_Ship.exe Real world example: Where is version?
- 29. There are other problems … HTC_Touch_Diamond2_WM6.5_RUU_Topaz_S_HT C_RUS_2.16.411.2_Radio_Sign_Topaz_61.44 tc.25.32_4.49.25.17_Ship.exe Real world example: Where is version?
- 30. There are other problems … HTC_Touch_Diamond2_WM6.5_RUU_Topaz_S_HT C_RUS_2.16.411.2_Radio_Sign_Topaz_61.44 tc.25.32_4.49.25.17_Ship.exe Real world example: Where is version?
- 34. Current version numbering practices Marketing names: Leopard, Vista, Kepler Dates: 98, 2000, 2013, 2015, 20140312 Revisions: 12345, 546894, 2131 Hashes: d5f954bef01d228b79ce35f2f1830aa7c7315d23 “Section numbering”: 1.0, 1.0.0, 5.1.6, 2.3.89.21 … [http://en.wikipedia.org/wiki/Software_versioning] OR something else…
- 35. Suggested solution 1. Take “section numbering” approach 2. Formalize it 3. Show that it is possible to perform basic operations using suggested formalization 4. Extend formalization to solve problems of software version numbering 5. Provide mapping from “old style” to “new style” approach
- 36. Elements of formal definition for sections numbering
- 37. Google docs demo
- 38. Formalization of “sections numbering” approach Nat o 0, 1, 2, … _._ ⊆ Nat × Nat × … × Nat o 0.1, 1.4, 45.23 o 1.0.0, 45.2.0, 34.89.9 o 3.5.20.11, 2.4.99.85.34.2 … Num = N1.N2. … .Nk _<_ ⊆ Num × Num o 0 < 1, 2 < 9, 3 < 90 o 1.1 < 1.2, 1.3 < 1.5, 4.1 < 6.8 o 2.1.1 < 4.69.78.2 , 2 < 3.8.2.3 … Section numbering
- 39. Formalization of “sections numbering” approach next : Num -> Nat-> Num o next 1 {1} -> 2 o next 1.0 1 -> 2.0 o next 1.0 2 -> 1.1 o next 3.4.5.6 3 -> 3.4.6.6 … NumTree : NumTree (Num NumTree) nTree = NumTree nTree => o 1 1.1 1.1.1 1.2 1.2.1 1.2.2 1.2.3 Section numbering
- 40. Formalization of “sections numbering” approach appendNext : NumTree -> Nat -> NumTree appendNext nTree 1 => o 1 1.1 1.1.1 1.2 1.2.1 1.2.2 1.2.3 o 2 appendNext nTree 2 => o 1 1.1 1.1.1 1.2 1.2.1 1.2.2 1.2.3 1.3 Section numbering
- 41. Formalization of “sections numbering” approach Section numbering appendNext nTree 3 => o 1 1.1 1.1.1 1.2 1.2.1 1.2.2 1.2.3 1.2.4
- 42. Elements of formal definition for version numbering
- 43. Extension of “sections numbering” approach Nat o 0, 1, 2, … _._ ⊆ Nat × Nat × … × Nat o 0.1, 1.4, 45.23 o 1.0.0, 45.2.0, 34.89.9 o 3.5.20.11, 2.4.99.85.34.2 … Num = N1.N2. … .Nk _<_ ⊆ Num × Num o 0 < 1, 2 < 9, 3 < 90 o 1.1 < 1.2, 1.3 < 1.5, 4.1 < 6.8 o 2.1.1 < 4.69.78.2 , 2 < 3.8.2.3 … Section numbering Nat o 0, 1, 2, … X : Set VC ::= Nat | X _._ ⊆ VC × VC × … × VC o 0.1, 1.4, 45.23 o 1.0.0, 45.2.0, 34.89.9 o 3.5.20.11, 2.4.99.85.34.2, o X , X.X , X.X.X , X.X.X.X , X. … .X o X.1, X.2, X.3, X.4, … X.n o X.X.2, X.5.X, 6.X.X, 6.5.X, X.23.10 Num = N1.N2. … .Nk _<_ ⊆ Num × Num o 0 < 1, 2 < 9, 3 < 90 o 1.1 < 1.2, 1.3 < 1.5, 4.1 < 6.8 o 2.1.1 < 4.69.78.2 , 2 < 3.8.2.3 o X.0 < X.1 o 1.X.14 < 1.X.25 o 2.3.X < 3.8.X o X < 0 o 1.X.X < 1.0.X Version numbering
- 44. Extension of “sections numbering” approach next : Num -> Num -> Num o next 1 {1} -> 2 o next 1.0 1 -> 2.0 o next 1.0 2 -> 1.1 o next 3.4.5.6 3 -> 3.4.6.6 … NumTree : NumTree (Num NumTree) nTree = NumTree nTree => o 1 1.1 1.1.1 1.2 1.2.1 1.2.2 1.2.3 next : Num -> Num o next 1 -> 2 o next 1.0 -> 1.1 o next 3.4.5.6 -> 3.4.5.7 o next 1.X -> 2.X o next 3.X.X -> 4.X.X o next X.6 -> X.7 o next 1.0.X -> 1.1.X o next 1.X.13 -> 1.X.14 … NumTree : NumTree (Num NumTree) nTree = NumTree nTree => o X.X.X 1.X.X 1.0.X 1.1.X o 1.1.0 o 1.1.1 1.2.X o 1.2.0 o 1.2.1 o 1.2.2 o 1.2.3 Section numbering Version numbering
- 45. Extension of “sections numbering” approach appendNext : NumTree -> Nat -> NumTree appendNext vTree 1 => o 1 1.1 1.1.1 1.2 1.2.1 1.2.2 1.2.3 o 2 appendNext vTree 2 => o 1 1.1 1.1.1 1.2 1.2.1 1.2.2 1.2.3 1.3 Section numbering appendNext : NumTree -> Nat -> NumTree appendNext nTree 1 => o X.X.X 1.X.X 1.0.X 1.1.X o 1.1.0 o 1.1.1 1.2.X o 1.2.0 o 1.2.1 o 1.2.2 o 1.2.3 2.X.X appendNext nTree 2 => o X.X.X 1.X.X 1.0.X 1.1.X o 1.1.0 o 1.1.1 1.2.X o 1.2.0 o 1.2.1 o 1.2.2 o 1.2.3 1.3.X Version numbering
- 46. Extension of “sections numbering” approach Section numbering appendNext nTree 3 => o 1 1.1 1.1.1 1.2 1.2.1 1.2.2 1.2.3 1.2.4 appendNext nTree 3 => o X.X.X 1.X.X 1.0.X 1.1.X o 1.1.0 o 1.1.1 1.2.X o 1.2.0 o 1.2.1 o 1.2.2 o 1.2.3 o 1.2.4 Version numbering
- 47. Extension of “sections numbering” approach Version numbering _↓_ o X ↓ 1, X ↓ 2, X ↓ 3, … X ↓ k o X.X ↓ X.1 , X.X ↓ X.2 , … , X.X ↓ X.k o X.X ↓ 0.X , X.X ↓ 1.X , X.X ↓ 2.X , … , X.X ↓ m.X o 1.X ↓ 1.0 , 1.X ↓ 1.1 , 1.X ↓ 1.2 , … , 1.X ↓ 1.k o X.X.X ↓ 1.X.X , X.X.X ↓ 2.X.X, … , X.X.X ↓ n.X.X o 1.X.X ↓ 1.0.X , 1.X.X ↓ 1.1.X, … , 1.X.X ↓ 1.m.X o 1.X.X ↓ 1.X.0 , 1.X.X ↓ 1.X.1, … , 1.X.X ↓ 1.X.k o 1.0.X ↓ 1.0.0 , 1.0.X ↓ 1.0.1, … , 1.0.X ↓ 1.0.k o X.X.X ↓ X.X.X , X.X ↓ X.X , X ↓ X … _==_ o X.6.8 == 6.8 o X.1 == 1 o X.X.1 == 1 o X.X.k == k o X.2.6 == 2.6 o X.1.X == 1.X o X.X.X = X o X. … .X = X … Copy Equivalence
- 49. Extension of “sections numbering” approach: visual representation Version numbering _↓_ o X ↓ 1, X ↓ 2, X ↓ 3, … X ↓ k o X.X ↓ X.1 , X.X ↓ X.2 , … , X.X ↓ X.k o X.X ↓ 0.X , X.X ↓ 1.X , X.X ↓ 2.X , … , X.X ↓ m.X o 1.X ↓ 1.0 , 1.X ↓ 1.1 , 1.X ↓ 1.2 , … , 1.X ↓ 1.k o X.X.X ↓ 1.X.X , X.X.X ↓ 2.X.X, … , X.X.X ↓ n.X.X o 1.X.X ↓ 1.0.X , 1.X.X ↓ 1.1.X, … , 1.X.X ↓ 1.m.X o 1.X.X ↓ 1.X.0 , 1.X.X ↓ 1.X.1, … , 1.X.X ↓ 1.X.k o 1.0.X ↓ 1.0.0 , 1.0.X ↓ 1.0.1, … , 1.0.X ↓ 1.0.k o X.X.X ↓ X.X.X , X.X ↓ X.X , X ↓ X … _==_ o X.6.8 == 6.8 o X.1 == 1 o X.X.1 == 1 o X.X.k == k o X.2.6 == 2.6 o X.1.X == 1.X o X.X.X = X o X. … .X = X … 1 2 3 k… X
- 50. Extension of “sections numbering” approach: visual representation Version numbering _↓_ o X ↓ 1, X ↓ 2, X ↓ 3, … X ↓ k o X.X ↓ X.1 , X.X ↓ X.2 , … , X.X ↓ X.k o X.X ↓ 1.X , X.X ↓ 2.X , … , X.X ↓ m.X o 1.X ↓ 1.0 , 1.X ↓ 1.1 , 1.X ↓ 1.2 , … , 1.X ↓ 1.k o X.X.X ↓ 1.X.X , X.X.X ↓ 2.X.X, … , X.X.X ↓ n.X.X o 1.X.X ↓ 1.0.X , 1.X.X ↓ 1.1.X, … , 1.X.X ↓ 1.m.X o 1.X.X ↓ 1.X.0 , 1.X.X ↓ 1.X.1, … , 1.X.X ↓ 1.X.k o 1.0.X ↓ 1.0.0 , 1.0.X ↓ 1.0.1, … , 1.0.X ↓ 1.0.k o X.X.X ↓ X.X.X , X.X ↓ X.X , X ↓ X … _==_ o X.6.8 == 6.8 o X.1 == 1 o X.X.1 == 1 o X.X.k == k o X.2.6 == 2.6 o X.1.X == 1.X o X.X.X = X o X. … .X = X … 1 2 3 k… X X.X /1.X 1.0 1.1 1.2 X.1 X.2 X.3 X.k… 1.k… … /2.X /m.X
- 51. Extension of “sections numbering” approach: visual representation Version numbering _↓_ o X ↓ 1, X ↓ 2, X ↓ 3, … X ↓ k o X.X ↓ X.1 , X.X ↓ X.2 , … , X.X ↓ X.k o X.X ↓ 1.X , X.X ↓ 2.X , … , X.X ↓ m.X o 1.X ↓ 1.0 , 1.X ↓ 1.1 , 1.X ↓ 1.2 , … , 1.X ↓ 1.k o X.X.X ↓ 1.X.X , X.X.X ↓ 2.X.X, … , X.X.X ↓ n.X.X o 1.X.X ↓ 1.0.X , 1.X.X ↓ 1.1.X, … , 1.X.X ↓ 1.m.X o 1.X.X ↓ 1.X.0 , 1.X.X ↓ 1.X.1, … , 1.X.X ↓ 1.X.k o 1.0.X ↓ 1.0.0 , 1.0.X ↓ 1.0.1, … , 1.0.X ↓ 1.0.k o X.X.X ↓ X.X.X , X.X ↓ X.X , X ↓ X … _==_ o X.6.8 == 6.8 o X.1 == 1 o X.X.1 == 1 o X.X.k == k o X.2.6 == 2.6 o X.1.X == 1.X o X.X.X = X o X. … .X = X … 1 2 3 k… X X.X /1.X 1.0 1.1 1.2 X.1 X.2 X.3 X.k… 1.k… … /2.X /m.X
- 52. Extension of “sections numbering” approach: visual representation Version numbering _↓_ o X ↓ 1, X ↓ 2, X ↓ 3, … X ↓ k o X.X ↓ X.1 , X.X ↓ X.2 , … , X.X ↓ X.k o X.X ↓ 1.X , X.X ↓ 2.X , … , X.X ↓ m.X o 1.X ↓ 1.0 , 1.X ↓ 1.1 , 1.X ↓ 1.2 , … , 1.X ↓ 1.k o X.X.X ↓ 1.X.X , X.X.X ↓ 2.X.X, … , X.X.X ↓ n.X.X o 1.X.X ↓ 1.0.X , 1.X.X ↓ 1.1.X, … , 1.X.X ↓ 1.m.X o 1.X.X ↓ 1.X.0 , 1.X.X ↓ 1.X.1, … , 1.X.X ↓ 1.X.k o 1.0.X ↓ 1.0.0 , 1.0.X ↓ 1.0.1, … , 1.0.X ↓ 1.0.k o X.X.X ↓ X.X.X , X.X ↓ X.X , X ↓ X … _==_ o X.6.8 == 6.8 o X.1 == 1 o X.X.1 == 1 o X.X.k == k o X.2.6 == 2.6 o X.1.X == 1.X o X.X.X = X o X. … .X = X … 1 2 3 k… X X.X /1.X 1.0 1.1 1.2 X.1 X.2 X.3 X.k… 1.k… … /2.X /m.X
- 53. Extension of “sections numbering” approach: visual representation Version numbering _↓_ o X ↓ 1, X ↓ 2, X ↓ 3, … X ↓ k o X.X ↓ X.1 , X.X ↓ X.2 , … , X.X ↓ X.k o X.X ↓ 1.X , X.X ↓ 2.X , … , X.X ↓ m.X o 1.X ↓ 1.0 , 1.X ↓ 1.1 , 1.X ↓ 1.2 , … , 1.X ↓ 1.k o X.X.X ↓ 1.X.X , X.X.X ↓ 2.X.X, … , X.X.X ↓ n.X.X o 1.X.X ↓ 1.0.X , 1.X.X ↓ 1.1.X, … , 1.X.X ↓ 1.m.X o 1.X.X ↓ 1.X.0 , 1.X.X ↓ 1.X.1, … , 1.X.X ↓ 1.X.k o 1.0.X ↓ 1.0.0 , 1.0.X ↓ 1.0.1, … , 1.0.X ↓ 1.0.k o X.X.X ↓ X.X.X , X.X ↓ X.X , X ↓ X … _==_ o X.6.8 == 6.8 o X.1 == 1 o X.X.1 == 1 o X.X.k == k o X.2.6 == 2.6 o X.1.X == 1.X o X.X.X = X o X. … .X = X … 1 2 3 k… X X.X /1.X 1.0 1.1 1.2 X.1 X.2 X.3 X.k… 1.k… … /2.X /m.X
- 54. Extension of “sections numbering” approach: visual representation 1.x.x 1.0.x x.x.x x.x.1 x.x.2 x.x.3 1.x.0 1.x.1 1.x.k 1.0.0 1.0.1 1.0.k… … n.x.x 1.1.x 1.m.x n.x.0 n.x.1 n.x.k… … … 2.x.x x.x.4 x.x.5 x.x.6 x.x.k… _↓_ o X ↓ 0, X ↓ 1, X ↓ 2, … X ↓ k o X.X ↓ X.1 , X.X ↓ X.2 , … , X.X ↓ X.k o X.X ↓ 1.X , X.X ↓ 2.X , … , X.X ↓ m.X o 1.X ↓ 1.0 , 1.X ↓ 1.1 , 1.X ↓ 1.2 , … , 1.X ↓ 1.k o X.X.X ↓ 1.X.X , X.X.X ↓ 2.X.X, … , X.X.X ↓ n.X.X o 1.X.X ↓ 1.0.X , 1.X.X ↓ 1.1.X, … , 1.X.X ↓ 1.m.X o 1.X.X ↓ 1.X.0 , 1.X.X ↓ 1.X.1, … , 1.X.X ↓ 1.X.k o 1.0.X ↓ 1.0.0 , 1.0.X ↓ 1.0.1, … , 1.0.X ↓ 1.0.k o X.X.X ↓ X.X.X , X.X ↓ X.X , X ↓ X …
- 55. Extension of “sections numbering” approach: visual representation 1.x.x 1.0.x x.x.x x.x.1 x.x.2 x.x.3 1.x.0 1.x.1 1.x.k 1.0.0 1.0.1 1.0.k… … n.x.x 1.1.x 1.m.x n.x.0 n.x.1 n.x.k… … … 2.x.x x.x.4 x.x.5 x.x.6 x.x.k… _↓_ o X ↓ 0, X ↓ 1, X ↓ 2, … X ↓ k o X.X ↓ X.1 , X.X ↓ X.2 , … , X.X ↓ X.k o X.X ↓ 1.X , X.X ↓ 2.X , … , X.X ↓ m.X o 1.X ↓ 1.0 , 1.X ↓ 1.1 , 1.X ↓ 1.2 , … , 1.X ↓ 1.k o X.X.X ↓ 1.X.X , X.X.X ↓ 2.X.X, … , X.X.X ↓ n.X.X o 1.X.X ↓ 1.0.X , 1.X.X ↓ 1.1.X, … , 1.X.X ↓ 1.m.X o 1.X.X ↓ 1.X.0 , 1.X.X ↓ 1.X.1, … , 1.X.X ↓ 1.X.k o 1.0.X ↓ 1.0.0 , 1.0.X ↓ 1.0.1, … , 1.0.X ↓ 1.0.k o X.X.X ↓ X.X.X , X.X ↓ X.X , X ↓ X …
- 56. Extension of “sections numbering” approach: visual representation 1.x.x 1.0.x x.x.x x.x.1 x.x.2 x.x.3 1.x.0 1.x.1 1.x.k 1.0.0 1.0.1 1.0.k… … n.x.x 1.1.x 1.m.x n.x.0 n.x.1 n.x.k… … … 2.x.x x.x.4 x.x.5 x.x.6 x.x.k… _↓_ o X ↓ 0, X ↓ 1, X ↓ 2, … X ↓ k o X.X ↓ X.1 , X.X ↓ X.2 , … , X.X ↓ X.k o X.X ↓ 1.X , X.X ↓ 2.X , … , X.X ↓ m.X o 1.X ↓ 1.0 , 1.X ↓ 1.1 , 1.X ↓ 1.2 , … , 1.X ↓ 1.k o X.X.X ↓ 1.X.X , X.X.X ↓ 2.X.X, … , X.X.X ↓ n.X.X o 1.X.X ↓ 1.0.X , 1.X.X ↓ 1.1.X, … , 1.X.X ↓ 1.m.X o 1.X.X ↓ 1.X.0 , 1.X.X ↓ 1.X.1, … , 1.X.X ↓ 1.X.k o 1.0.X ↓ 1.0.0 , 1.0.X ↓ 1.0.1, … , 1.0.X ↓ 1.0.k o X.X.X ↓ X.X.X , X.X ↓ X.X , X ↓ X …
- 57. Extension of “sections numbering” approach: visual representation 1.x.x 1.0.x x.x.x x.x.1 x.x.2 x.x.3 1.x.0 1.x.1 1.x.k 1.0.0 1.0.1 1.0.k… … n.x.x 1.1.x 1.m.x n.x.0 n.x.1 n.x.k… … … 2.x.x x.x.4 x.x.5 x.x.6 x.x.k… _↓_ o X ↓ 0, X ↓ 1, X ↓ 2, … X ↓ k o X.X ↓ X.1 , X.X ↓ X.2 , … , X.X ↓ X.k o X.X ↓ 1.X , X.X ↓ 2.X , … , X.X ↓ m.X o 1.X ↓ 1.0 , 1.X ↓ 1.1 , 1.X ↓ 1.2 , … , 1.X ↓ 1.k o X.X.X ↓ 1.X.X , X.X.X ↓ 2.X.X, … , X.X.X ↓ n.X.X o 1.X.X ↓ 1.0.X , 1.X.X ↓ 1.1.X, … , 1.X.X ↓ 1.m.X o 1.X.X ↓ 1.X.0 , 1.X.X ↓ 1.X.1, … , 1.X.X ↓ 1.X.k o 1.0.X ↓ 1.0.0 , 1.0.X ↓ 1.0.1, … , 1.0.X ↓ 1.0.k o X.X.X ↓ X.X.X , X.X ↓ X.X , X ↓ X …
- 58. Extension of “sections numbering” approach: visual representation 1.x.x 1.0.x x.x.x x.x.1 x.x.2 x.x.3 1.x.0 1.x.1 1.x.k 1.0.0 1.0.1 1.0.k… … n.x.x 1.1.x 1.m.x n.x.0 n.x.1 n.x.k… … … 2.x.x x.x.4 x.x.5 x.x.6 x.x.k… _↓_ o X ↓ 0, X ↓ 1, X ↓ 2, … X ↓ k o X.X ↓ X.1 , X.X ↓ X.2 , … , X.X ↓ X.k o X.X ↓ 1.X , X.X ↓ 2.X , … , X.X ↓ m.X o 1.X ↓ 1.0 , 1.X ↓ 1.1 , 1.X ↓ 1.2 , … , 1.X ↓ 1.k o X.X.X ↓ 1.X.X , X.X.X ↓ 2.X.X, … , X.X.X ↓ n.X.X o 1.X.X ↓ 1.0.X , 1.X.X ↓ 1.1.X, … , 1.X.X ↓ 1.m.X o 1.X.X ↓ 1.X.0 , 1.X.X ↓ 1.X.1, … , 1.X.X ↓ 1.X.k o 1.0.X ↓ 1.0.0 , 1.0.X ↓ 1.0.1, … , 1.0.X ↓ 1.0.k o X.X.X ↓ X.X.X , X.X ↓ X.X , X ↓ X …
- 59. Extension of “sections numbering” approach: visual representation 1.x.x 1.0.x x.x.x x.x.1 x.x.2 x.x.3 1.x.0 1.x.1 1.x.k 1.0.0 1.0.1 1.0.k… … n.x.x 1.1.x 1.m.x n.x.0 n.x.1 n.x.k… … … 2.x.x x.x.4 x.x.5 x.x.6 x.x.k… 1 2 k… x 3 4 5 6 == == == == == == == _==_ o X.6.8 == 6.8 o X.1 == 1 o X.X.1 == 1 o X.X.k == k o X.2.6 == 2.6 o X.1.X == 1.X o X.X.X = X o X. … .X = X
- 60. Extension of “sections numbering” approach: visual representation x.x.x x.x.x x.x.x x.x.x x.x.x x.x.x … x.x.x _↓_ o X ↓ 0, X ↓ 1, X ↓ 2, … X ↓ k o X.X ↓ X.1 , X.X ↓ X.2 , … , X.X ↓ X.k o X.X ↓ 1.X , X.X ↓ 2.X , … , X.X ↓ m.X o 1.X ↓ 1.0 , 1.X ↓ 1.1 , 1.X ↓ 1.2 , … , 1.X ↓ 1.k o X.X.X ↓ 1.X.X , X.X.X ↓ 2.X.X, … , X.X.X ↓ n.X.X o 1.X.X ↓ 1.0.X , 1.X.X ↓ 1.1.X, … , 1.X.X ↓ 1.m.X o 1.X.X ↓ 1.X.0 , 1.X.X ↓ 1.X.1, … , 1.X.X ↓ 1.X.k o 1.0.X ↓ 1.0.0 , 1.0.X ↓ 1.0.1, … , 1.0.X ↓ 1.0.k o X.X.X ↓ X.X.X , X.X ↓ X.X , X ↓ X … x.x.x x.x.x x.x.x … _==_ o X.6.8 == 6.8 o X.1 == 1 o X.X.1 == 1 o X.X.k == k o X.2.6 == 2.6 o X.1.X == 1.X o X.X.X = X o X. … .X = X
- 61. Extension of “sections numbering” approach: visual representation x.x x.x x.x x.x x.x x.x … x.x _↓_ o X ↓ 0, X ↓ 1, X ↓ 2, … X ↓ k o X.X ↓ X.1 , X.X ↓ X.2 , … , X.X ↓ X.k o X.X ↓ 1.X , X.X ↓ 2.X , … , X.X ↓ m.X o 1.X ↓ 1.0 , 1.X ↓ 1.1 , 1.X ↓ 1.2 , … , 1.X ↓ 1.k o X.X.X ↓ 1.X.X , X.X.X ↓ 2.X.X, … , X.X.X ↓ n.X.X o 1.X.X ↓ 1.0.X , 1.X.X ↓ 1.1.X, … , 1.X.X ↓ 1.m.X o 1.X.X ↓ 1.X.0 , 1.X.X ↓ 1.X.1, … , 1.X.X ↓ 1.X.k o 1.0.X ↓ 1.0.0 , 1.0.X ↓ 1.0.1, … , 1.0.X ↓ 1.0.k o X.X.X ↓ X.X.X , X.X ↓ X.X , X ↓ X … x.x x.x x.x … _==_ o X.6.8 == 6.8 o X.1 == 1 o X.X.1 == 1 o X.X.k == k o X.2.6 == 2.6 o X.1.X == 1.X o X.X.X = X o X. … .X = X
- 62. Extension of “sections numbering” approach: visual representation x x x x x x … x _↓_ o X ↓ 0, X ↓ 1, X ↓ 2, … X ↓ k o X.X ↓ X.1 , X.X ↓ X.2 , … , X.X ↓ X.k o X.X ↓ 1.X , X.X ↓ 2.X , … , X.X ↓ m.X o 1.X ↓ 1.0 , 1.X ↓ 1.1 , 1.X ↓ 1.2 , … , 1.X ↓ 1.k o X.X.X ↓ 1.X.X , X.X.X ↓ 2.X.X, … , X.X.X ↓ n.X.X o 1.X.X ↓ 1.0.X , 1.X.X ↓ 1.1.X, … , 1.X.X ↓ 1.m.X o 1.X.X ↓ 1.X.0 , 1.X.X ↓ 1.X.1, … , 1.X.X ↓ 1.X.k o 1.0.X ↓ 1.0.0 , 1.0.X ↓ 1.0.1, … , 1.0.X ↓ 1.0.k o X.X.X ↓ X.X.X , X.X ↓ X.X , X ↓ X … x x x … _==_ o X.6.8 == 6.8 o X.1 == 1 o X.X.1 == 1 o X.X.k == k o X.2.6 == 2.6 o X.1.X == 1.X o X.X.X = X o X. … .X = X
- 64. Mapping from “old style” to “new style” Approach: decomposition into branches and tags
- 65. Mapping from “old style” to “new style” x.x.x 1.x.x 1.0.x x.x.1 x.x.2 x.x.3 1.x.0 1.x.1 1.0.0 1.0.1 x.x.4 x.x.5 x.x.6 1.1 1.2 1.3 1.4 2.1 2.2 1.3.1.1 1.3.1.2 1.3.2.1 1.3.2.2 1.0.x 1.x.x x.x.x 1.0.x 1.x.x x.x.x
- 66. 1.0.x 1.x.x x.1.x x.2.x x.x.x Mapping from “old style” to “new style” 1.0.x 1.x.x x.1.x x.2.x x.x.x x.x.x 1.x.x 1.0.x x.2.1 x.2.2x.1.1 1.0.0 1.0.1 x.1.2 x.1.3 x.1.4 2.1 2.21.1 1.2 1.3 1.4 1.3.2.1 1.3.2.2 x.1.x x.2.x 1.x.0 1.x.1 1.3.1.1 1.3.1.2
- 67. 1.0.x 1.x.x x.1.x x.2.x x.x.x Mapping from “old style” to “new style” 1.0.x 1.x.x x.1.x x.2.x x.x.x 1.x.x 1.0.x x.x.x x.2.1 x.2.2x.1.1 1.x.0 1.x.1 1.0.0 x.1.2 x.1.3 x.1.4 2.1 2.21.1 1.2 1.3 1.4 1.3.1.1 1.3.2.1 1.3.1.2 x.1.x x.2.x 1.x.2 1.3.2.2
- 68. 1.0.x 1.1.x 2.x.x x.x.x 1.x.x Mapping from “old style” to “new style” 1.0.x 1.1.x x.x.x 2.x.1 2.x.21.x.1 1.0.0 1.x.2 1.x.3 1.x.4 2.1 2.21.1 1.2 1.3 1.4 1.3.1.1 1.x.x 2.x.x 1.0.1 1.3.1.2 1.1.0 1.3.2.1 1.1.1 1.3.2.2 1.0.x 1.1.x 2.x.x x.x.x 1.x.x
- 69. 2.x.x x.x.x 1.x.x 1.1.x 1.0.x Mapping from “old style” to “new style” 1.0.x 1.1.x 2.x.x x.x.x 1.x.x 1.0.x 1.1.x x.x.x 2.x.1 2.x.21.x.1 1.0.0 1.x.2 1.x.3 1.x.4 2.1 2.21.1 1.2 1.3 1.4 1.3.2.1 1.x.x 2.x.x 1.0.1 1.3.2.2 1.1.0 1.3.1.1 1.1.1 1.3.1.2
- 70. Mapping from “old style” to “new style” 1.x.x x.x.x 1.1.x 1.0.x 1.0.x 1.1.x 1.x.x x.x.x 1.0.x 1.1.x x.x.x 2.x.1 2.x.21.x.1 1.0.0 1.x.2 1.x.3 1.x.4 2.1 2.21.1 1.2 1.3 1.4 1.3.2.1 2.x.x 1.x.x 1.0.1 1.3.2.2 1.1.0 1.3.1.1 1.1.1 1.3.1.2 1.x.x
- 71. x.x.x x.x.x x.x.x x.x.x Mapping from “old style” to “new style” x.x.x x.x.x x.x.x x.x.x x.x.x x.x.x x.x.x x.x.8 x.x.10 x.x.1 x.x.7 x.x.2 x.x.3 x.x.5 2.1 2.2 1.1 1.2 1.3 1.4 1.3.2.1 x.x.x x.x.9 1.3.2.2 x.x.4 1.3.1.1 x.x.6 1.3.1.2
- 72. x.x x.x x.x x.x Mapping from “old style” to “new style” x.x x.x x.x x.x x.x x.x x.x x.8 x.10 x.1 x.7 x.2 x.3 x.5 2.1 2.2 1.1 1.2 1.3 1.4 1.3.2.1 x.x x.9 1.3.2.2 x.4 1.3.1.1 x.6 1.3.1.2
- 73. x x x x Revisions: 1, 2, 3, … , 2131, … Mapping from “old style” to “new style” x x x x x x x 8 10 1 7 2 3 5 2.1 2.2 1.1 1.2 1.3 1.4 1.3.2.1 x 9 1.3.2.2 4 1.3.1.1 6 1.3.1.2
- 74. Semantics of version numbering 1.0.x 1.x.x x.1.x x.2.x x.x.x 1.0.x 1.x.x x.x.x 1.0.x 1.1.x 2.x.x x.x.x 1.x.x 1.0.x 1.1.x 1.x.x x.x.x x x x x There are many different ways to decompose the same history of versions. Which one should we choose? We need to learn about semantics of
- 76. Semantics of “old” version numbering [major].[minor].[build] 1.2.3 ITERATIONS ARCHITECTURE CONCEPTS PORTING MARKETING BUILD PATCH http://semver.org/
- 77. Semantics of “new” version numbering x.x.x N.M.K mutable immutable Creation of immutable artifact compatible incompatible Definition of compatibility scope all changes Fixed set of features Feature freeze
- 78. Semantics of version numbers x.x.x x.x.K N.x.x N.M.K x.M.K N.M.x N.x.K x.M.x x.x.x x.x.K N.x.x N.M.K x.M.K x.M.x N.M.x N.x.K x.x.x x.x.KN.x.x N.M.K x.M.x x.M.KN.M.x N.x.K ≃ ≃isomorphic
- 79. x.x.x x.x.K N.x.x N.M.K x.M.K N.M.x N.x.K x.M.x x.x.x x.x.K N.x.x N.M.K x.M.K x.M.x N.M.x N.x.K Any changes Features subset M Universall y compatible Subset N of compatible features Semantics of version numbers Mutable (branch) Immutable (tag) Universall y compatible Subset N of compatible features
- 80. x.x.x x.x.K N.x.x N.M.K x.M.K N.M.x N.x.K x.M.x x.x.x x.x.K N.x.x N.M.K x.M.K x.M.x N.M.x N.x.K Any changes Features subset M Universall y compatible Subset N of compatible features Semantics of version numbers Mutable (branch) Immutable (tag) Universall y compatible Subset N of compatible features
- 81. Mapping from “old style” to “new style” 1.0.x 1.x.x x.1.x x.2.x x.x.x 1.0.x 1.x.x x.x.x 1.0.x 1.1.x 2.x.x x.x.x 1.x.x 1.0.x 1.1.x 1.x.x x.x.x x x x x ? ? ? ? ?
- 82. Mapping from “old style” to “new style” • Way of versions history decomposition depends on WHY certain versions were created: • Purpose of tagging, branching, etc • Actual content of tag, branch, etc • It is difficult to refactor existing history of versions because of insufficient information about purpose and content of certain artifacts. • It is easier to follow rules of version numbering semantics at early stages of software projects. • It is even more easy to follow rules if there is a special tool that helps with version numbering.
- 84. Why new approach is better
- 85. How does “new approach” solve problems? 1.2.1 < 1.2.2 < 1.2.3 2.1 < 2.2 < 2.3 1.1 < 4.2 < 5 x.x.1 < x.x.2 < x.x.3 < x.x.4 < x.x.5 < x.x.6 x.1.1 < x.1.2 < x.1.3 < x.1.4 < x.2.1 < x.2.2 1.x.1 < 1.x.2 < 1.x.3 < 1.x.4 < 2.x.1 < 2.x.2 1.x.0 < 1.x.1 < 1.x.2 1.0.0 < 1.0.1 < 1.1.0 < 1.1.1 It is possible to order version numbers (partially)
- 86. 1.1.1 ⊂ 1.1 ⊂ 1 1.2.1 ⊂ 1.2 ⊂ 1 1.2.2 ⊂ 1.2 ⊂ 1 1.2.3 ⊂ 1.2 ⊂ 1 ⊂ ↓-> 1.1.1 ⊂ 1 1.2.1 ⊂ 1 1.2.2 ⊂ 1 1.2.3 ⊂ 1 How does “new approach” solve problems? Concept of subset ⊂ is not applicable to version numbers. “Copy” operation ↓ is used instead.
- 87. X.X.X ↓ 1.X X.X.X ↓ 2.X … X.X.X ↓ M.X X.X.X ↓ X.X.1 X.X.X ↓ X.X.2 … X.X.X ↓ X.X.K X.X.X ↓ X.1 X.X.X ↓ X.2 … X.X.X ↓ X.K X.X.X ↓ 1 X.X.X ↓ 2 … X.X.X ↓ 4 X.X.X ↓ 1.X.X X.X.X ↓ 2.X.X … X.X.X ↓ N.X.X X.X.X ↓ X.1.X X.X.X ↓ X.2.X … X.X.X ↓ X.M.X N.X.X ↓ N.1.X N.X.X ↓ N.2.X … N.X.X ↓ N.M.X N.X.X ↓ N.X.1 N.X.X ↓ N.X.2 … N.X.X ↓ N.X.K How does “new approach” solve problems? ⊂ ↓->
- 88. Hierarchy of version numbers x.x x.KM.x M.K x K x.x.x x.x.KN.x.x N.M.K x.M.x x.M.KN.M.x N.x.K X.X.X ↓ X.M.X X.X.X ↓ N.X.X X.X.X ↓ X.X.K N.X.X ↓ N.M.X N.X.X ↓ N.X.K X.M.X ↓ X.M.K N.M.X ↓ N.M.K X.X ↓ M.X X.X ↓ X.K M.X ↓ M.K M.X ↓ M.K X ↓ K It is possible to establish hierarchy of version numbers using copy operation:
- 90. Does version == variation NO
- 91. Versions vs variations Versions Variations Provides Context (branches) and snapshots (tags) Choice Keeps track of Content Alternative implementations Takes into account Selected choices Potential choices Version + choice configuration = variant
- 92. Version numbering for variations 1.x.x x64 en debu g TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE app variations
- 93. 1.x.1 Version numbering for variations 1.x.x 1.x.0 x64 en debu g TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE 1.x.0 app 1.x.0 1.x.2 1.x.2 1.x.2 1.x.2 1.x.3 1.x.3 1.x.4 1.x.4 1.x.5 1.x.5 1.x.6 1.x.6 1.x.6 1.x.6 1.x.6 variations versions
- 94. 1.x.1 Version numbering for variations 1.x.x 1.x.0 x64 en debu g TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE 1.x.0 app app_1.x.6 app_1.x.6_debug app_1.x.3_en app_1.x.6_en_debug app_1.x.0_x64 app_1.x.6_x64_debug app_1.x.5_en_debug app_1.x.6_x64_en_debug1.x.0 1.x.2 1.x.2 1.x.2 1.x.2 1.x.3 1.x.3 1.x.4 1.x.4 1.x.5 1.x.5 1.x.6 1.x.6 1.x.6 1.x.6 1.x.6 variations versions variants
- 95. 1.x.1 Version numbering for variations 1.x.x 1.x.0 x64 en debu g TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE 1.x.0 app app_1.x.6 app_1.x.6_debug app_1.x.3_en app_1.x.6_en_debug app_1.x.0_x64 app_1.x.6_x64_debug app_1.x.5_en_debug app_1.x.6_x64_en_debug1.x.0 1.x.2 1.x.2 1.x.2 1.x.2 1.x.3 1.x.3 1.x.4 1.x.4 1.x.5 1.x.5 1.x.6 1.x.6 1.x.6 1.x.6 1.x.6
- 96. 1.x.1 Version numbering for variations 1.x.x 1.x.0 x64 en debu g TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE 1.x.0 app app_1.x.6 app_1.x.6_debug app_1.x.3_en app_1.x.6_en_debug app_1.x.0_x64 app_1.x.6_x64_debug app_1.x.5_en_debug app_1.x.6_x64_en_debug1.x.0 1.x.2 1.x.2 1.x.2 1.x.2 1.x.3 1.x.3 1.x.4 1.x.4 1.x.5 1.x.5 1.x.6 1.x.6 1.x.6 1.x.6 1.x.6
- 97. 1.x.1 Version numbering for variations 1.x.x 1.x.0 x64 en debu g TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE 1.x.0 app app_1.x.6 app_1.x.6_debug app_1.x.3_en app_1.x.6_en_debug app_1.x.0_x64 app_1.x.6_x64_debug app_1.x.5_en_debug app_1.x.6_x64_en_debug1.x.0 1.x.2 1.x.2 1.x.2 1.x.2 1.x.3 1.x.3 1.x.4 1.x.4 1.x.5 1.x.5 1.x.6 1.x.6 1.x.6 1.x.6 1.x.6
- 98. 1.x.1 Version numbering for variations 1.x.0 x64 en debu g TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE 1.x.0 app app app_debug app_en app_en_debug app_x64 app_x64_debug app_en_debug app_x64_en_debug1.x.0 1.x.2 1.x.2 1.x.2 1.x.2 1.x.3 1.x.3 1.x.4 1.x.4 1.x.5 1.x.5 1.x.6 1.x.6 1.x.6 1.x.6 1.x.6 Keeping track only of latest version
- 99. 1.x.1 Version numbering for variations 1.x.0 x64 en debu g TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE 1.x.0 app app app_debug app_en app_en_debug app_x64 app_x64_debug app_en_debug app_x64_en_debug1.x.0 1.x.2 1.x.2 1.x.2 1.x.2 1.x.3 1.x.3 1.x.4 1.x.4 1.x.5 1.x.5 1.x.6 1.x.6 1.x.6 1.x.6 1.x.6 1.x.3 1.x.5 Keeping track only of latest version
- 100. 1.x.1 Version numbering for variations 1.x.0 x64 en debu g TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE 1.x.0 app app app_debug app_en app_en_debug app_x64 app_x64_debug app_en_debug app_x64_en_debug1.x.0 1.x.2 1.x.2 1.x.2 1.x.2 1.x.3 1.x.3 1.x.4 1.x.4 1.x.5 1.x.5 1.x.6 1.x.6 1.x.6 1.x.6 1.x.6 1.x.0 1.x.3 1.x.5 Keeping track only of latest version
- 101. Conclusion
- 102. Conclusion • Version != variation • Versions and variations are complementary and always go side by side in software development • Necessity of software configuration management practices arises because of high variability of software • Both formalized version numbering and variations can help to understand nature of changes better • If formalized, versions can provide context for variations and choices of alternative implementations • Proper version numbering must be introduced into software projects as early as possible to avoid problems with version numbering. • Formalized version numbering and variations are stepping stone for better software tools.
