Embed presentation
Downloaded 146 times





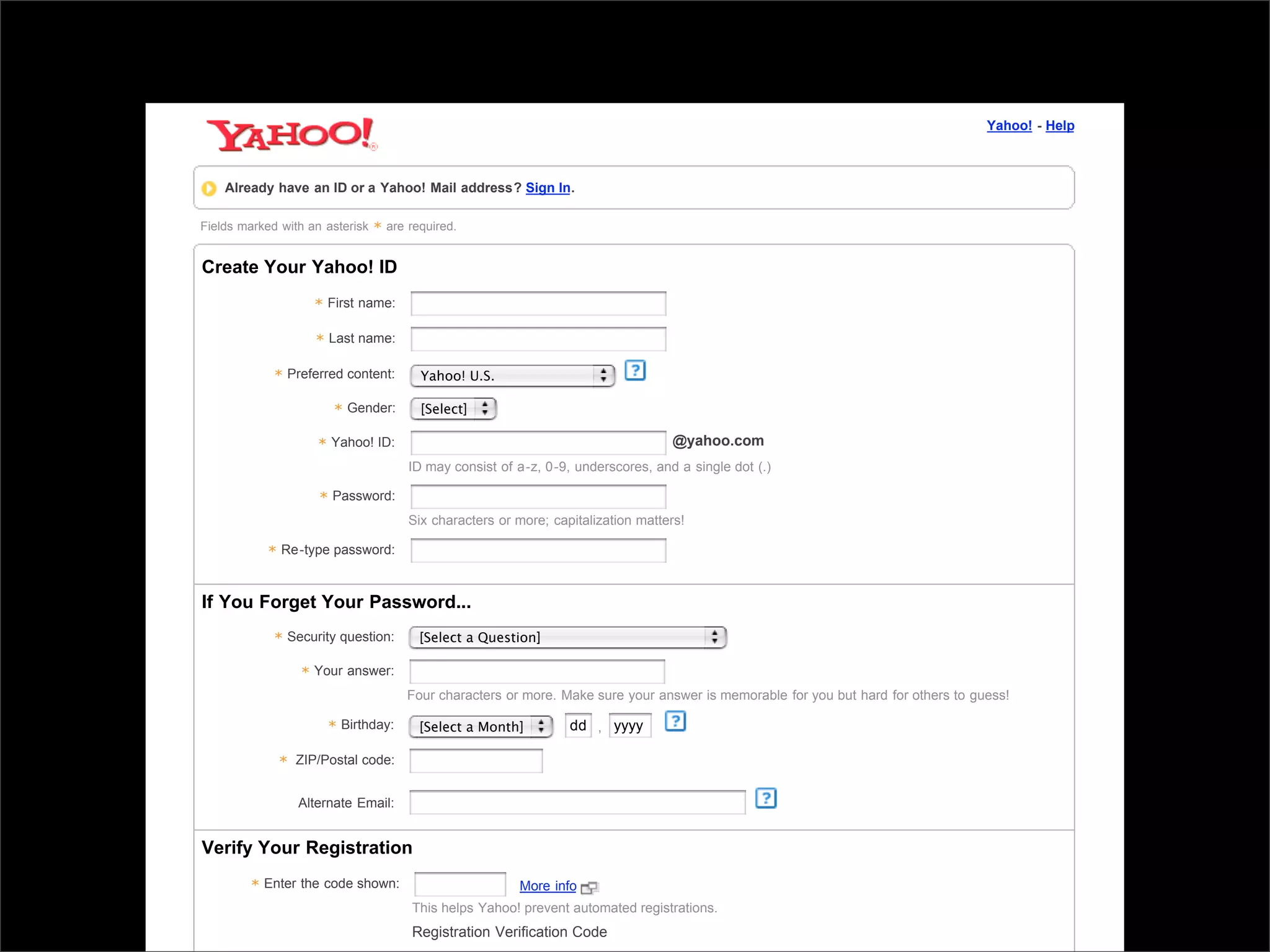











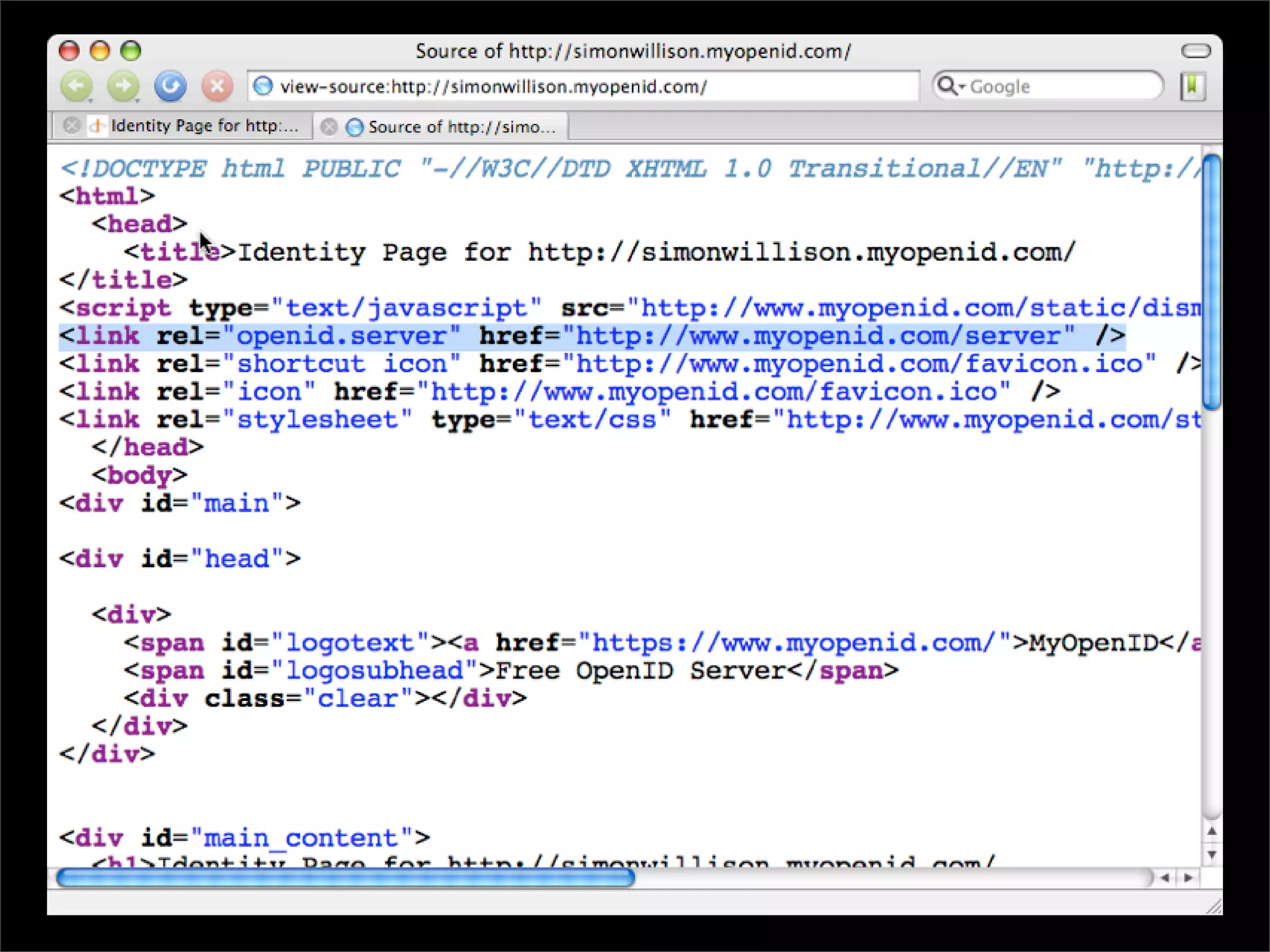
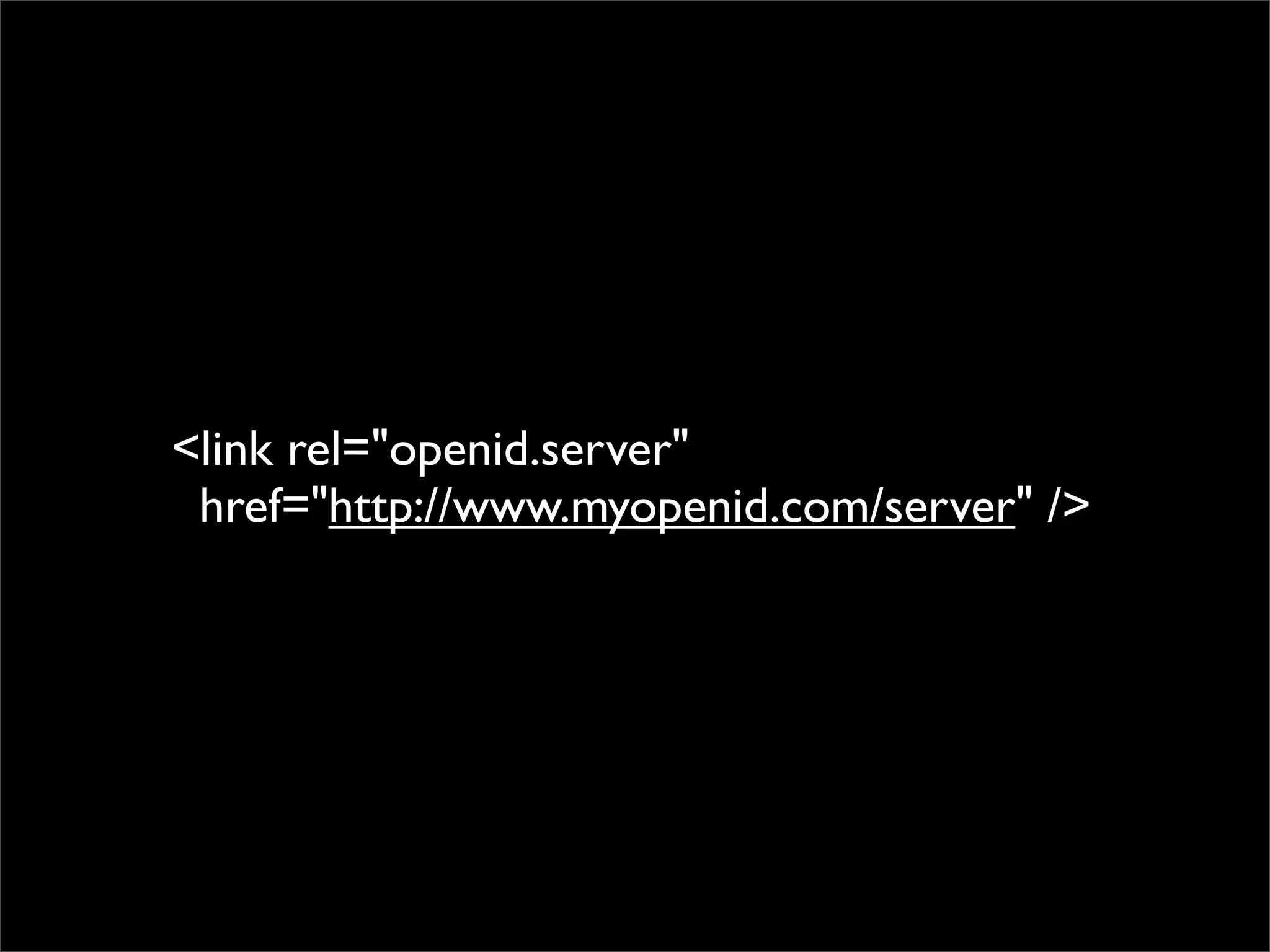


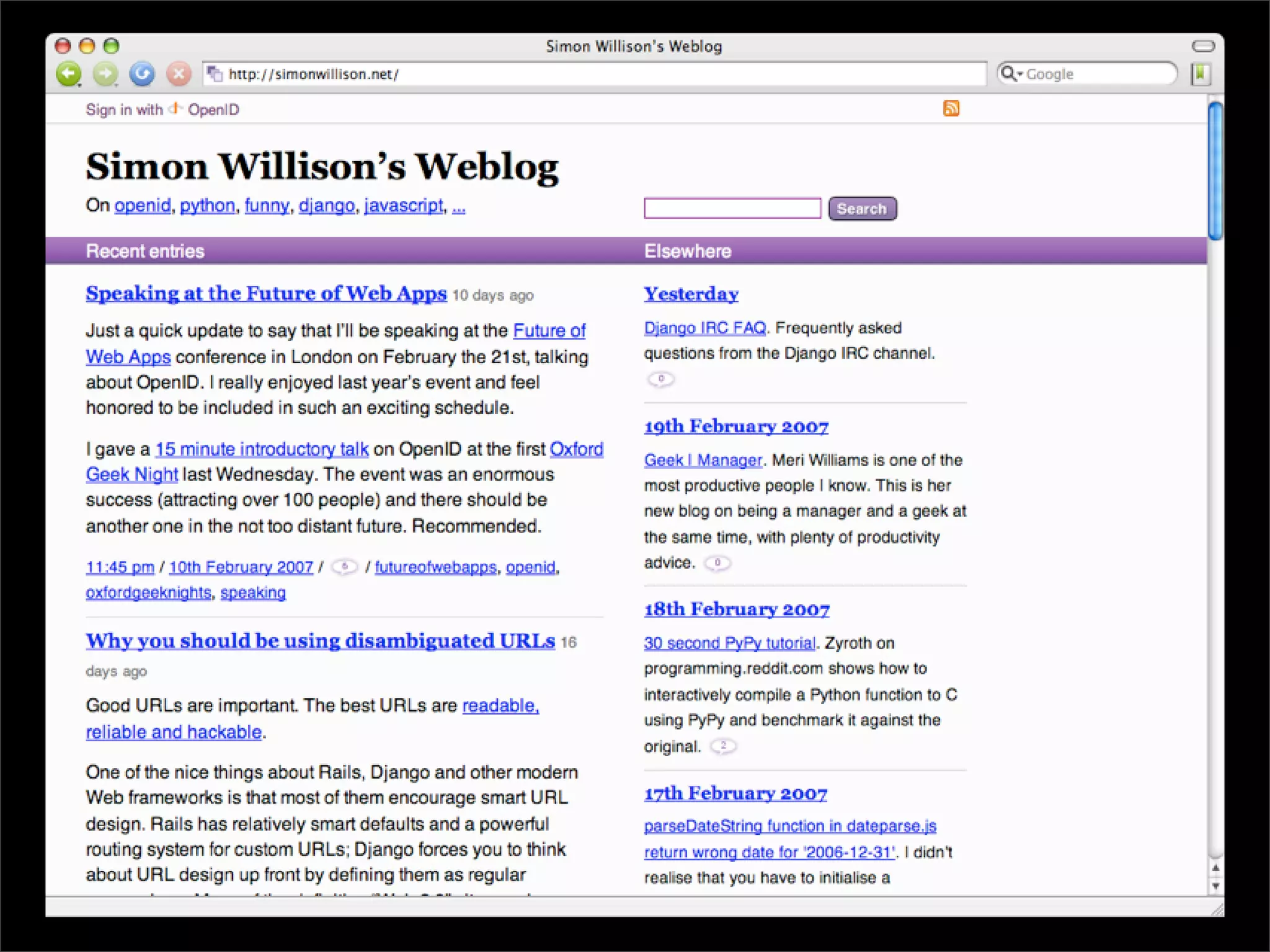

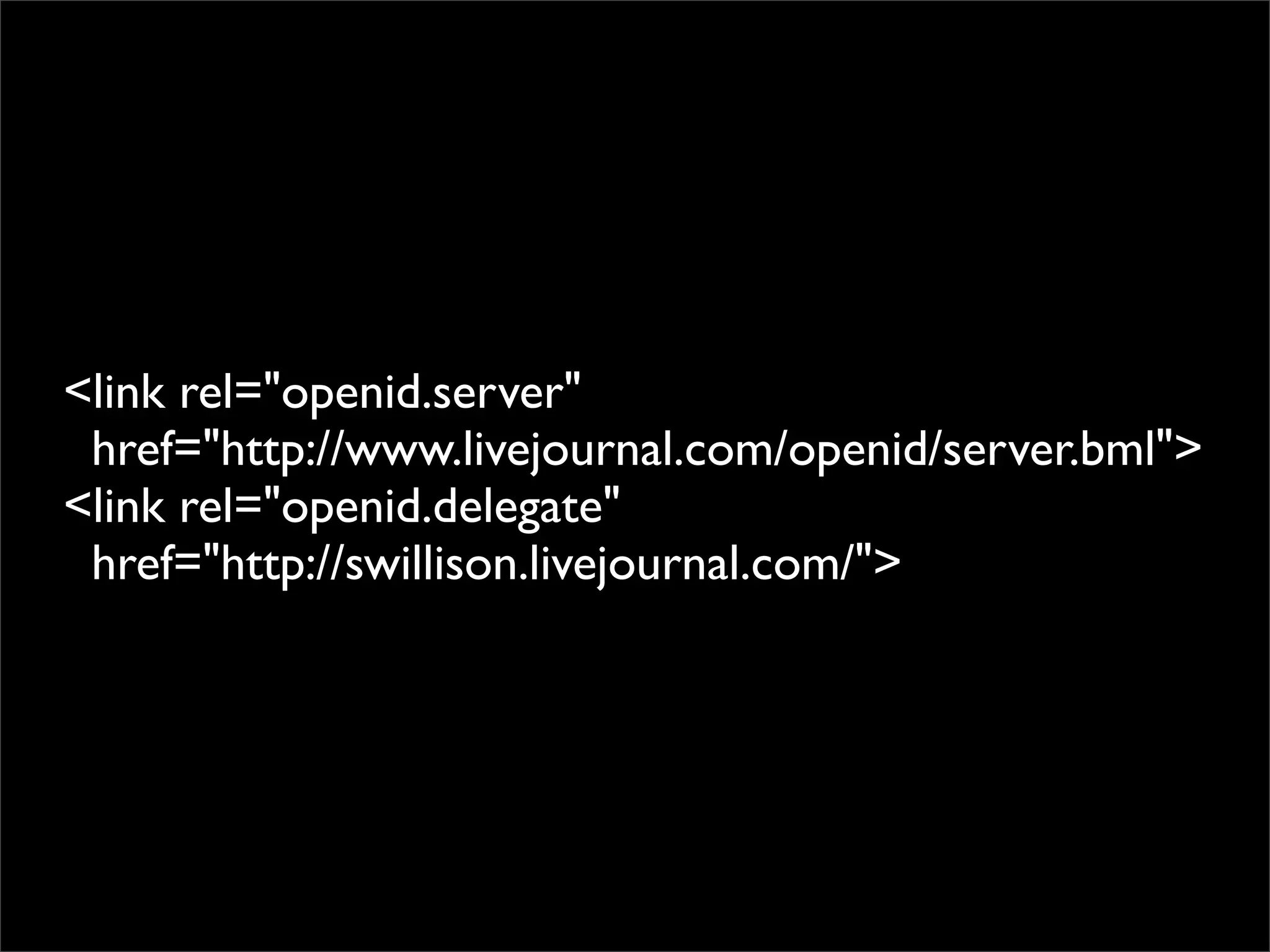











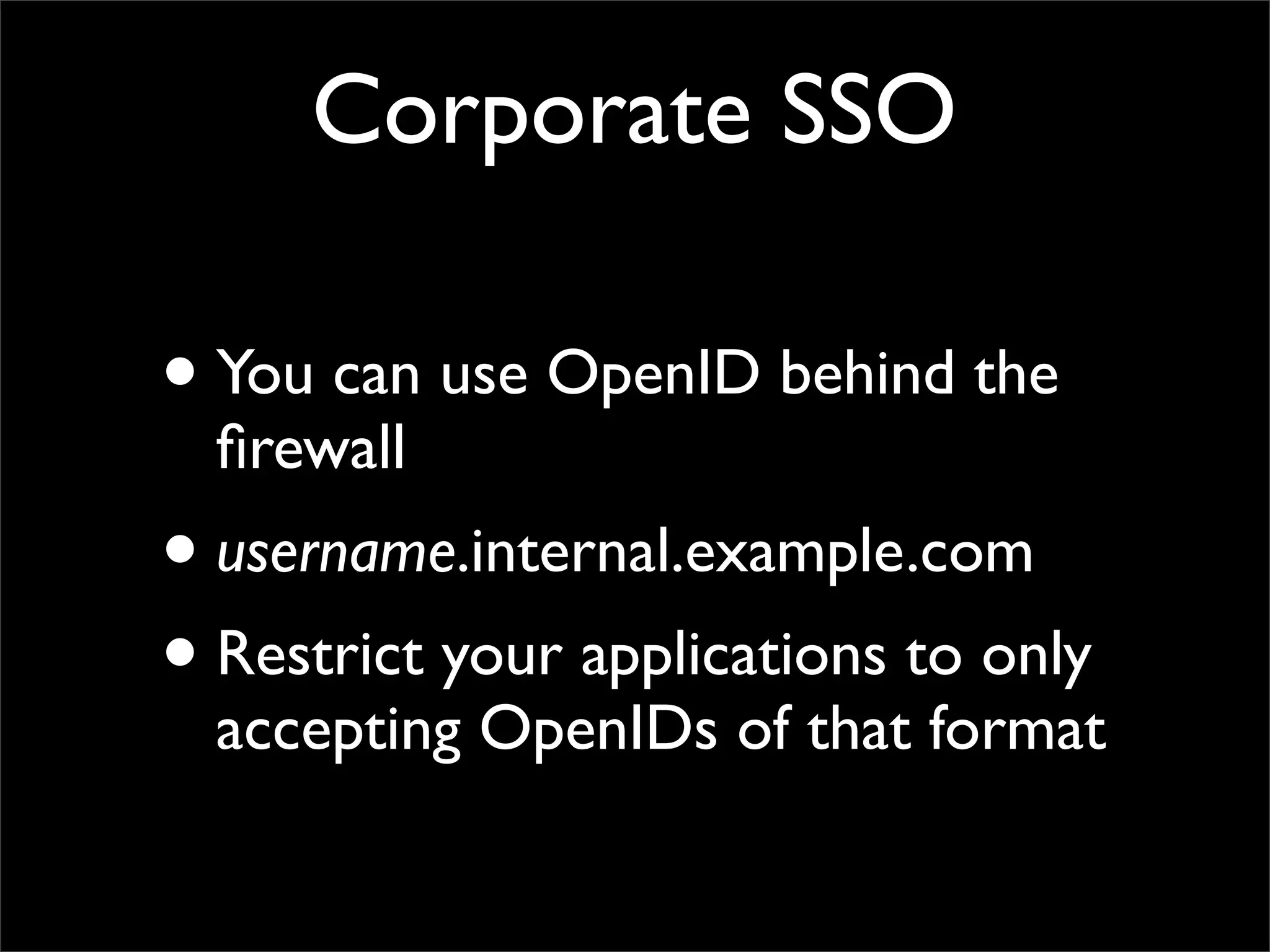

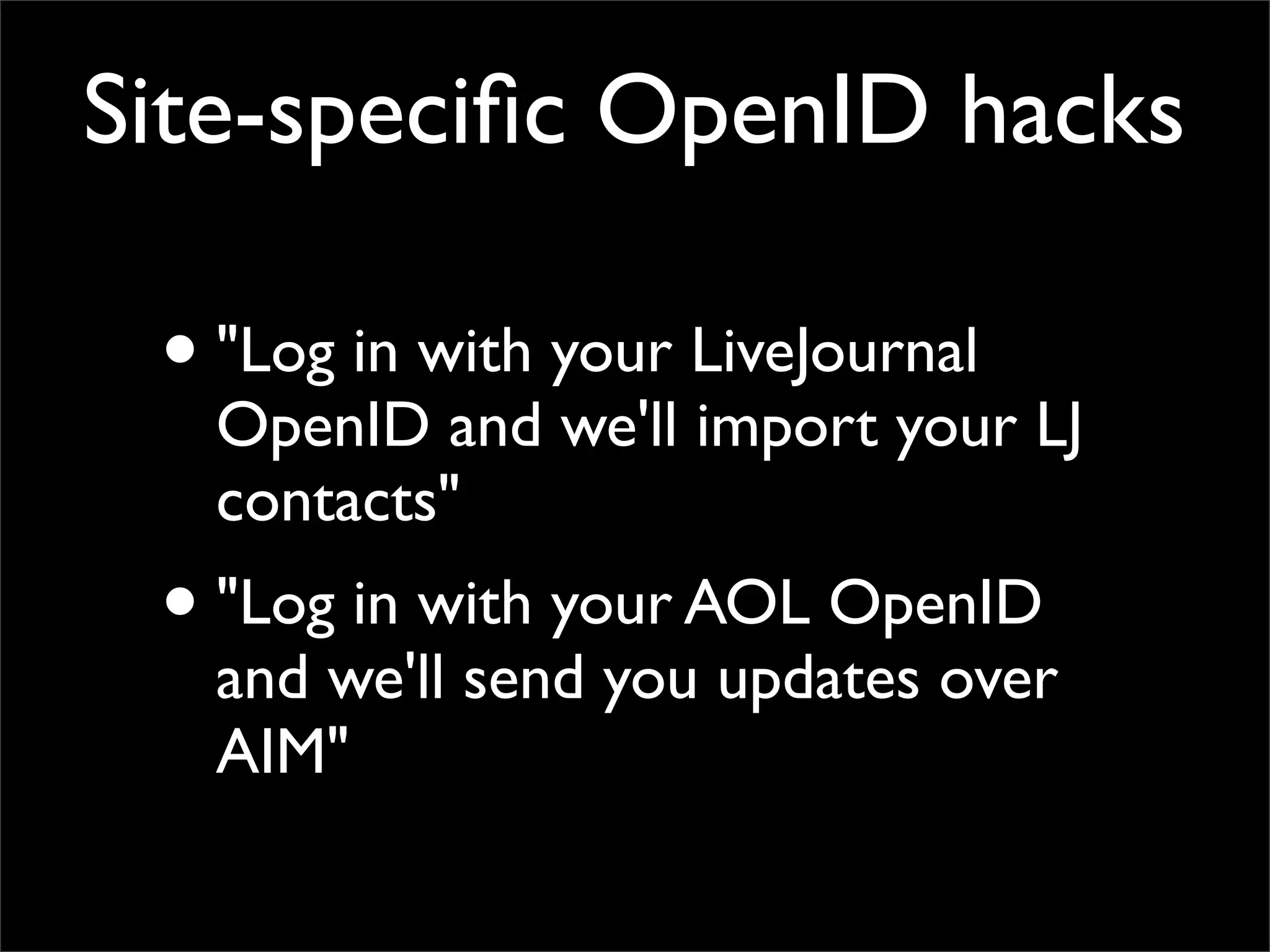
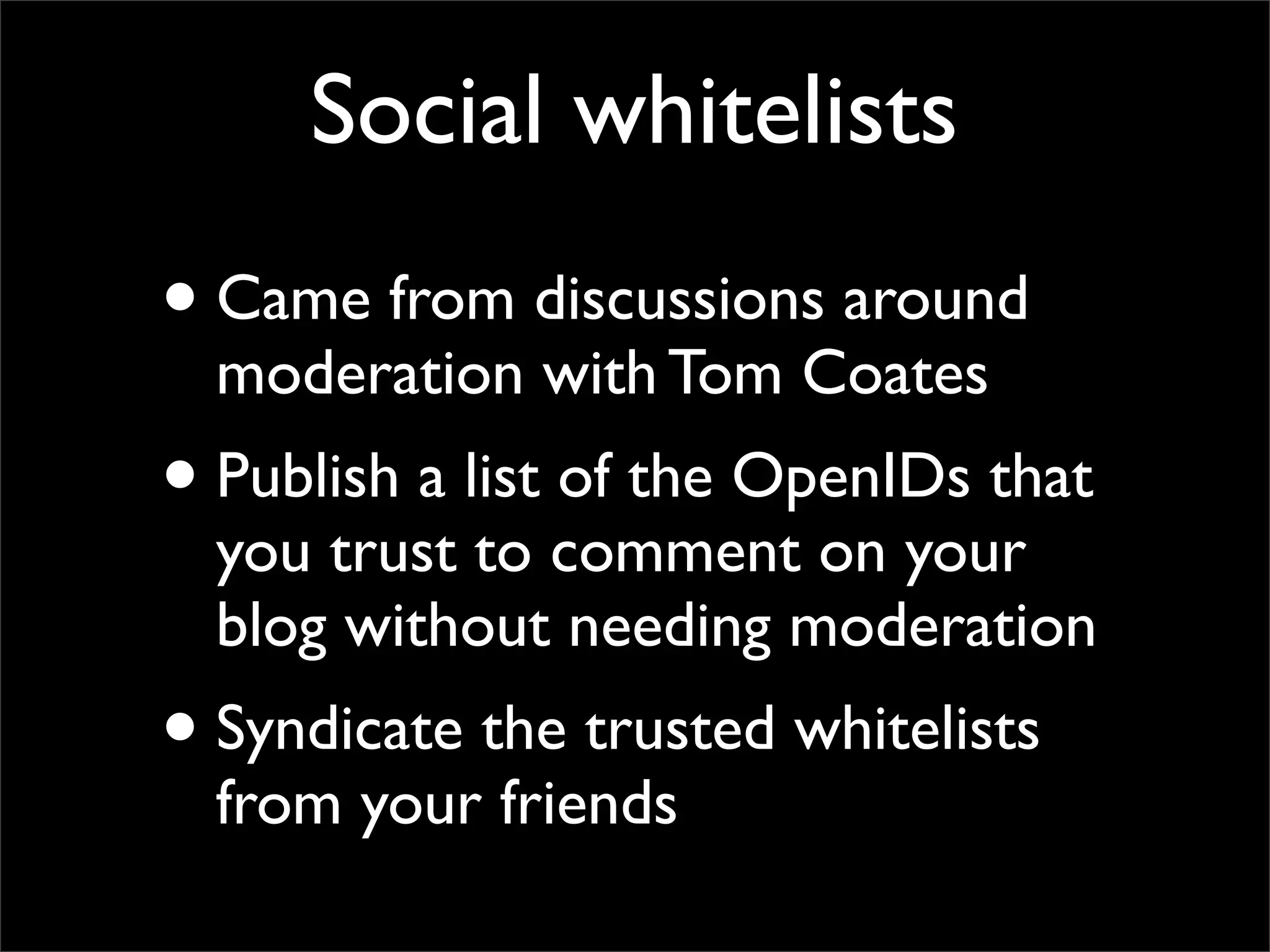
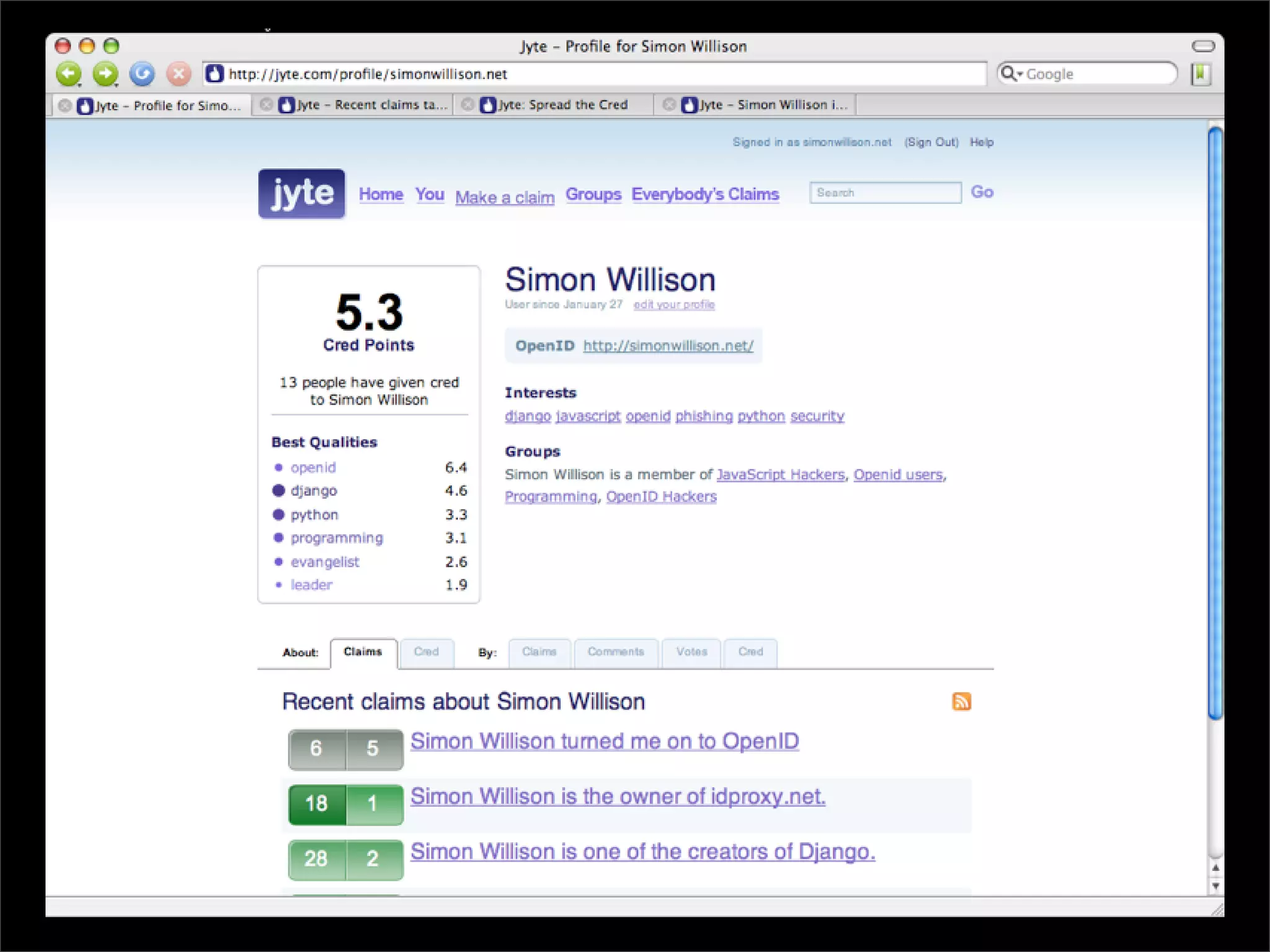
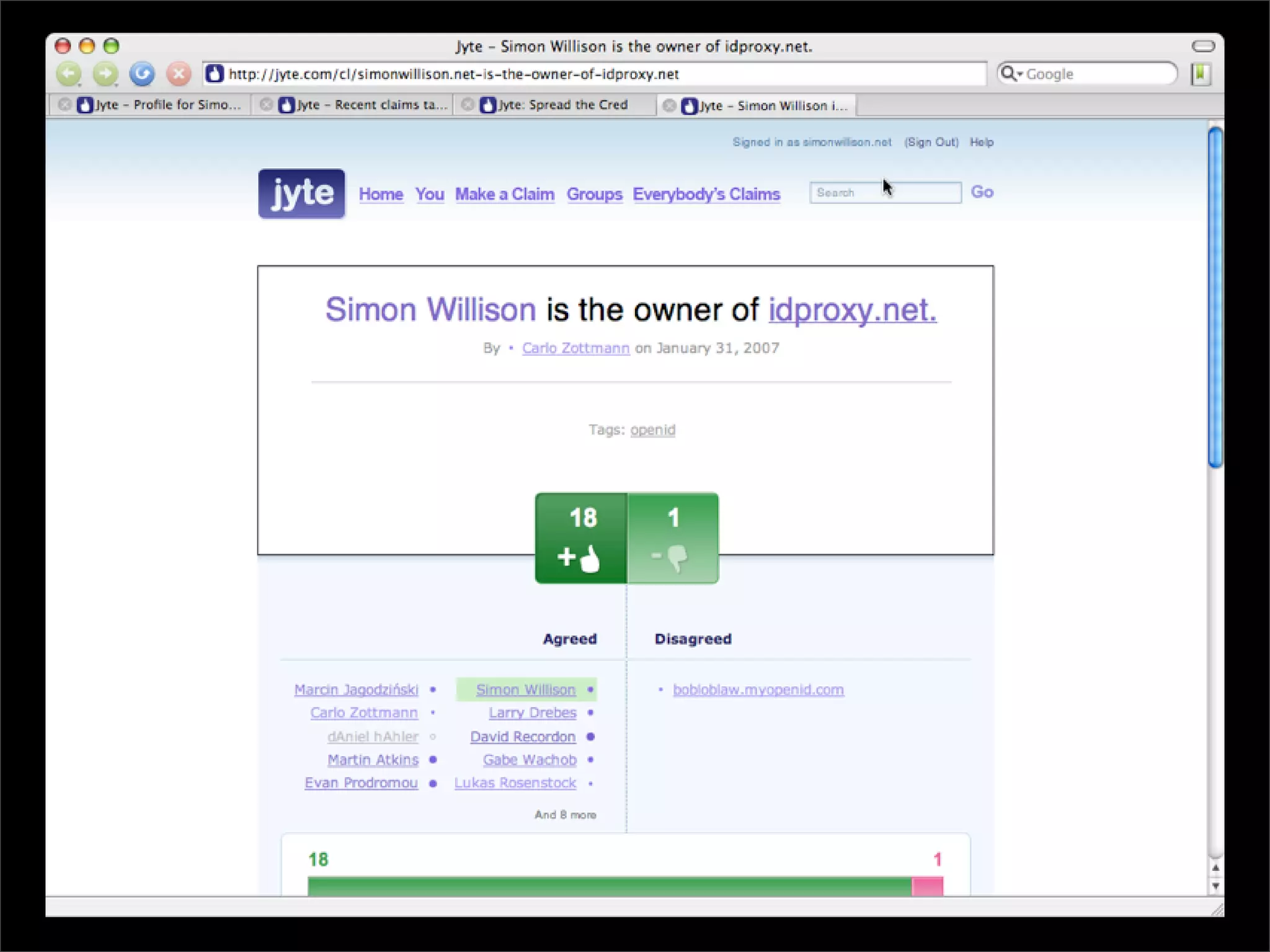




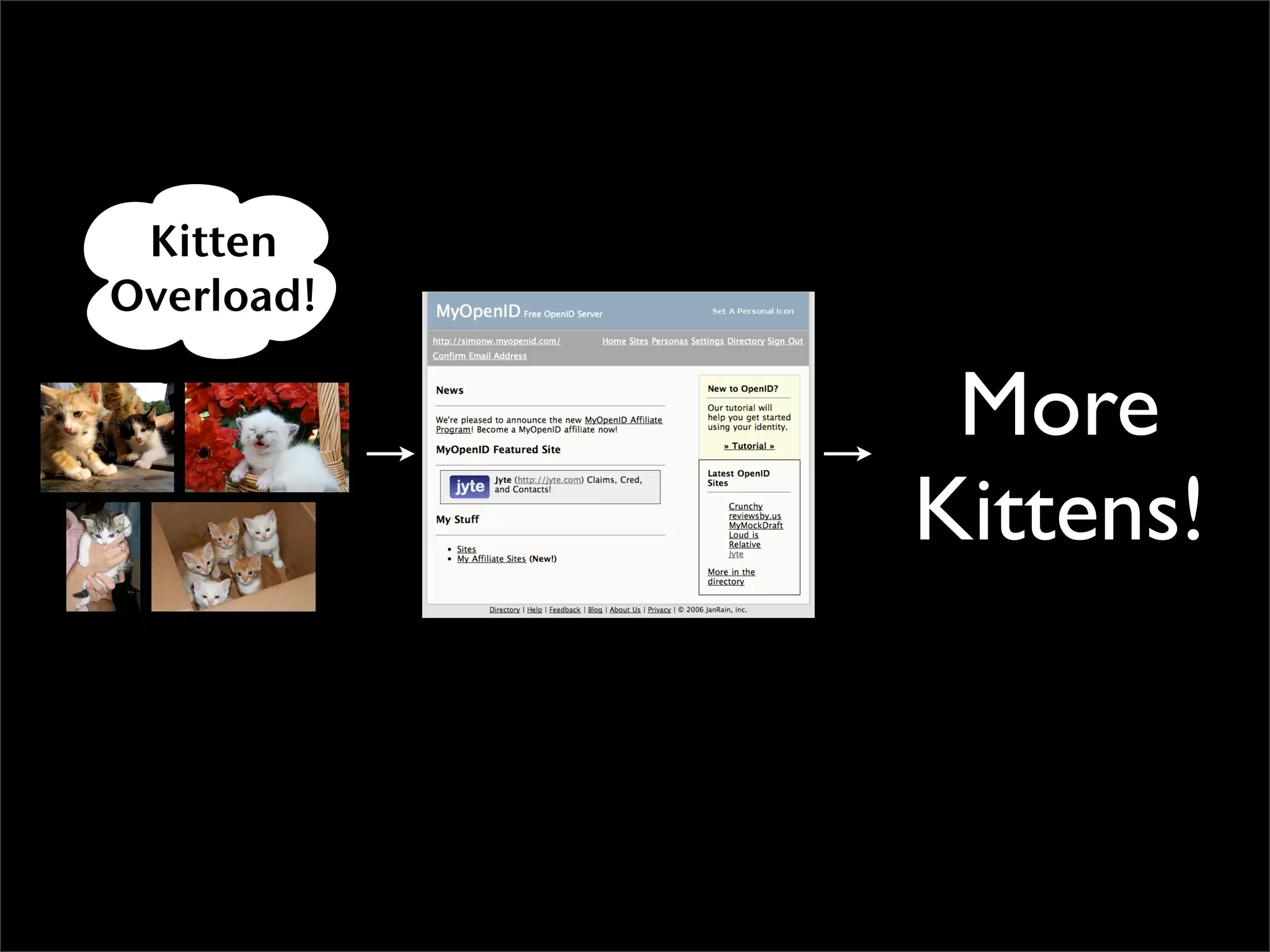


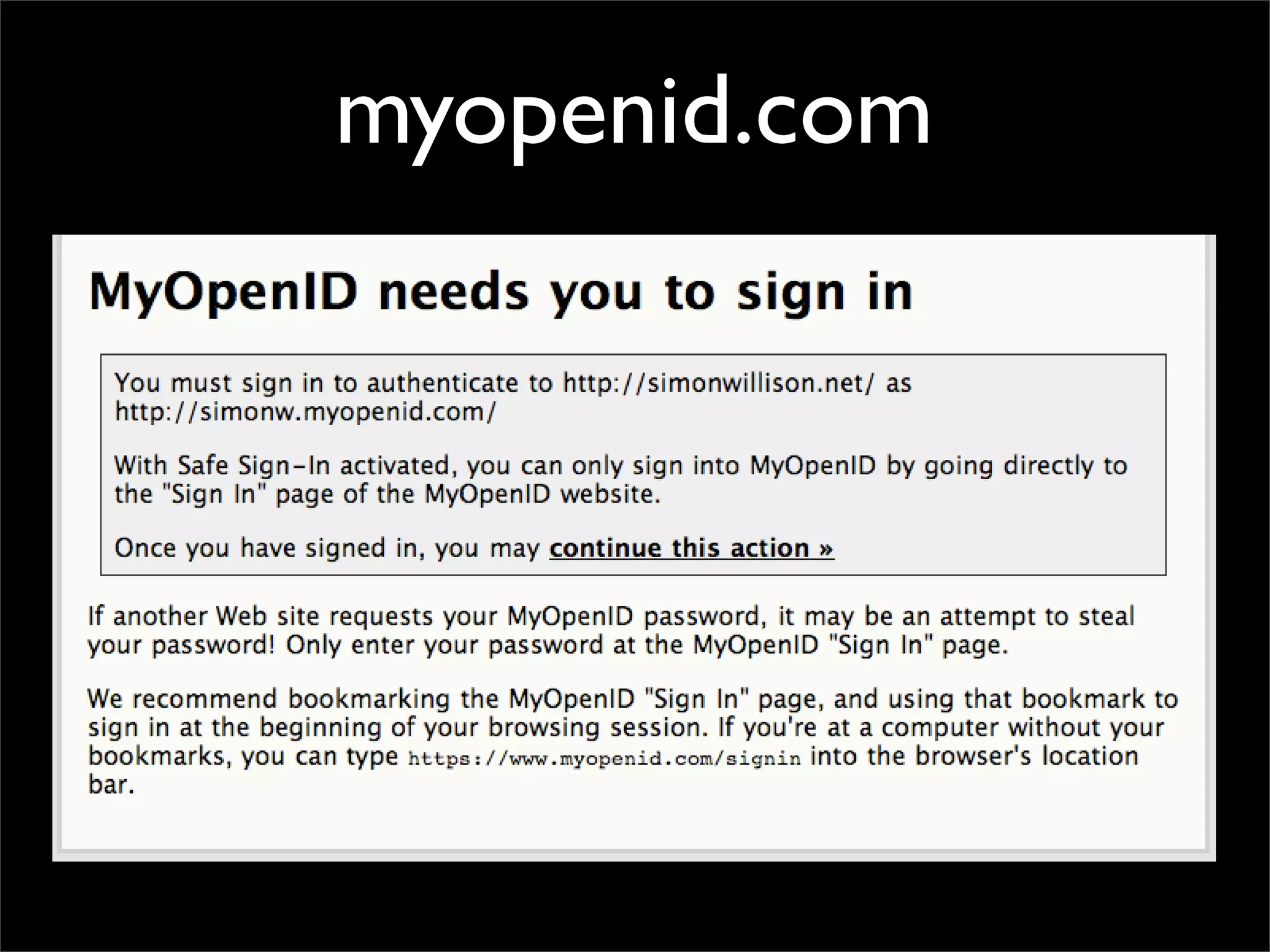










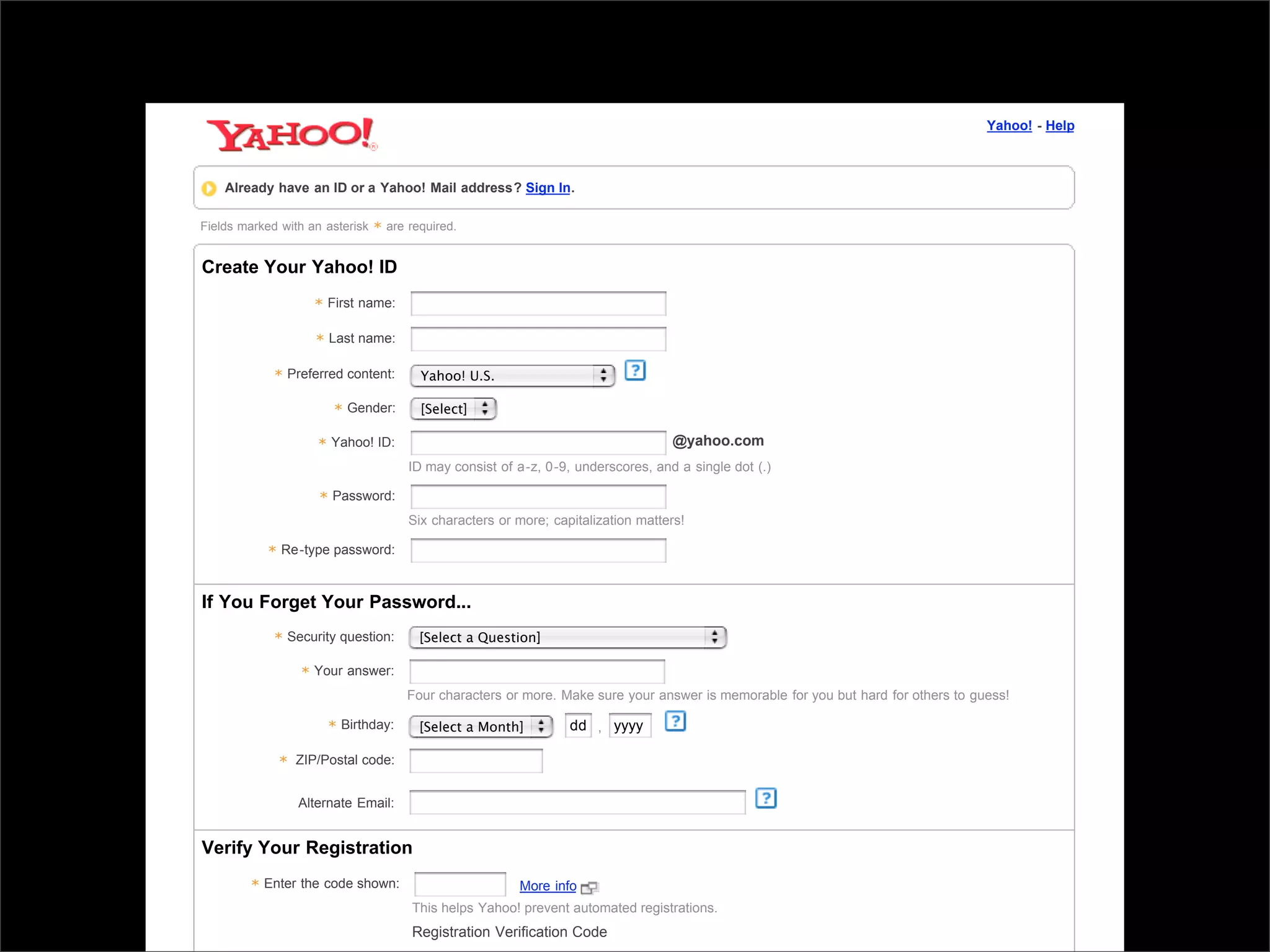
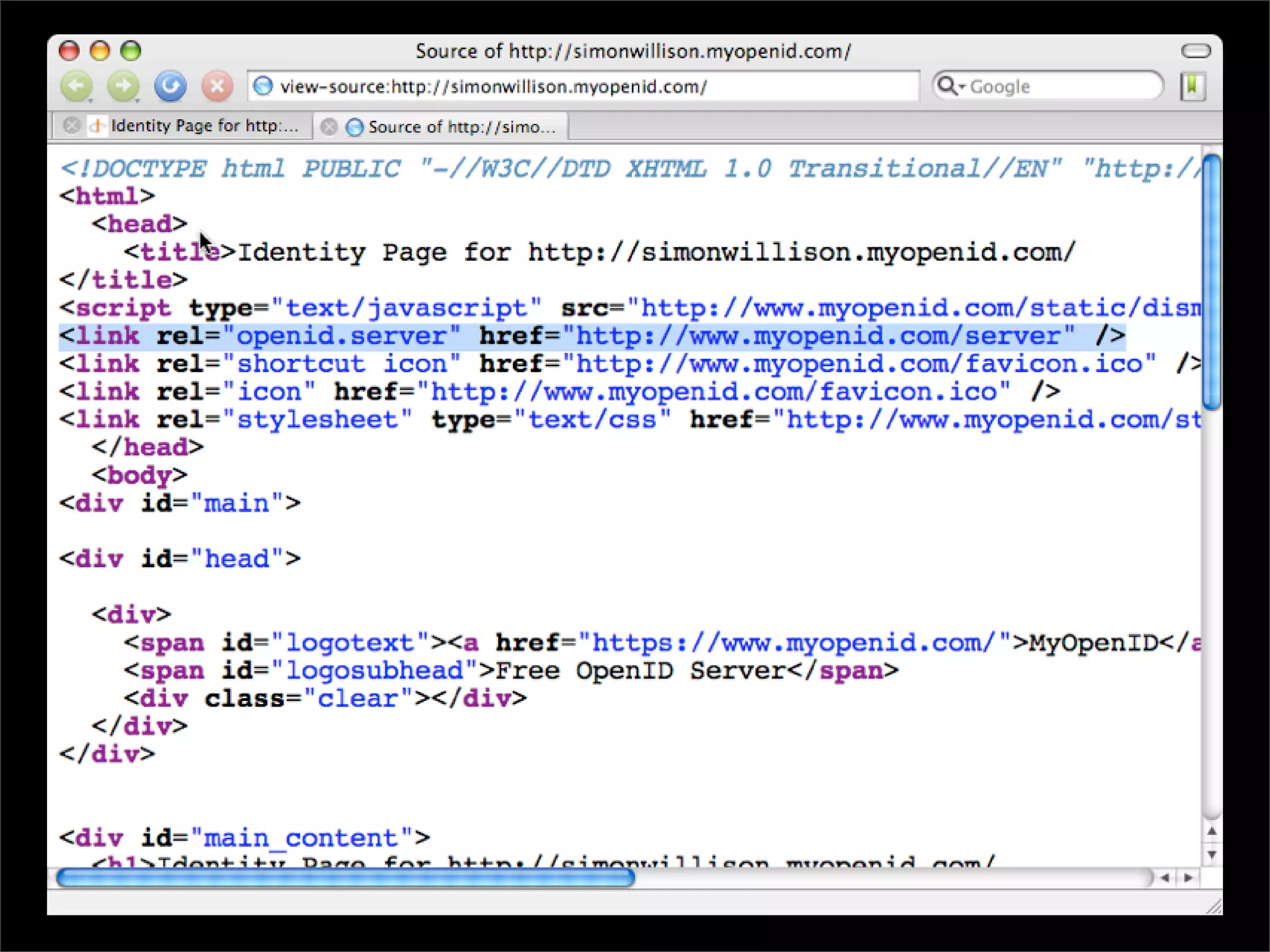
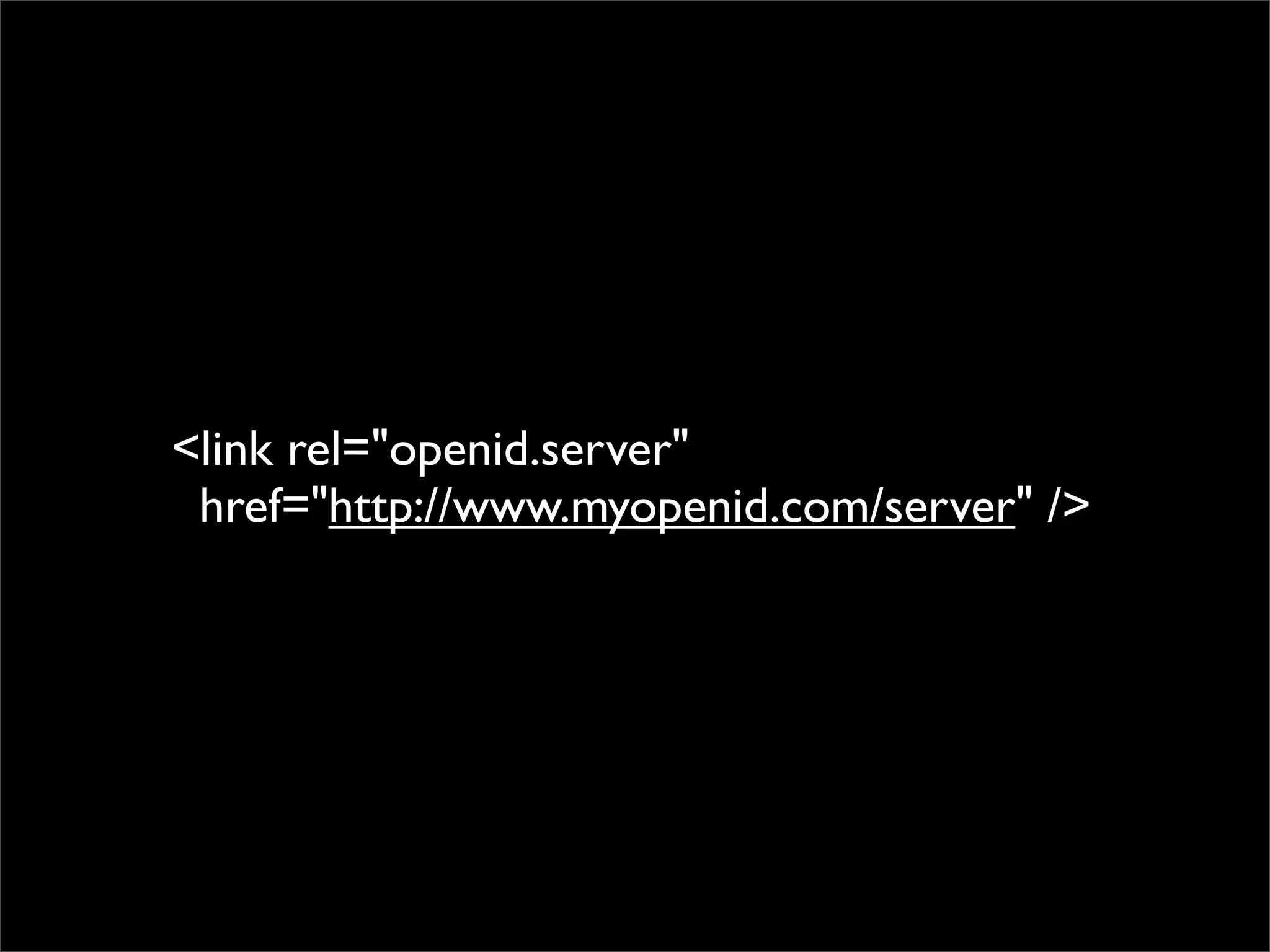
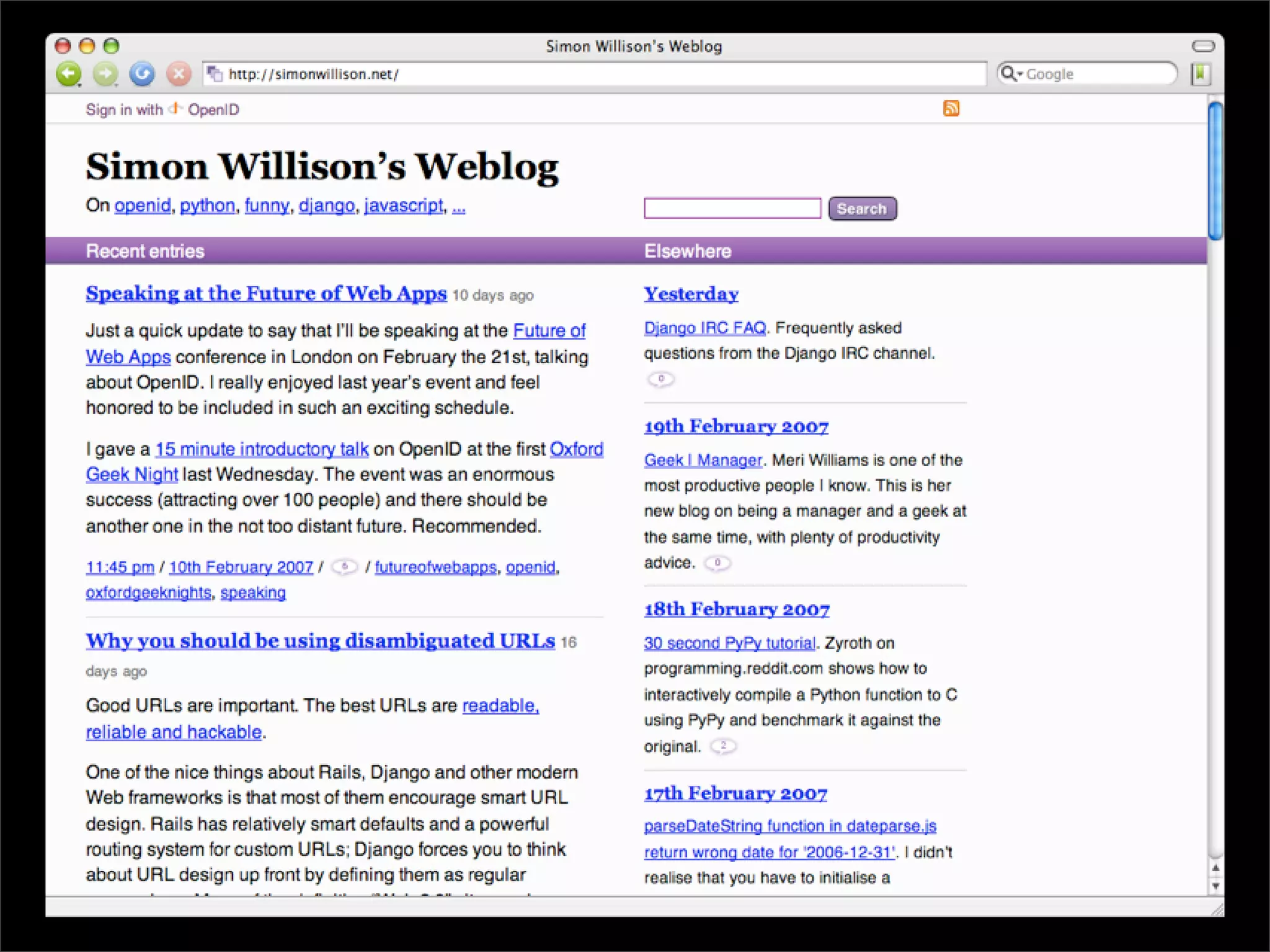
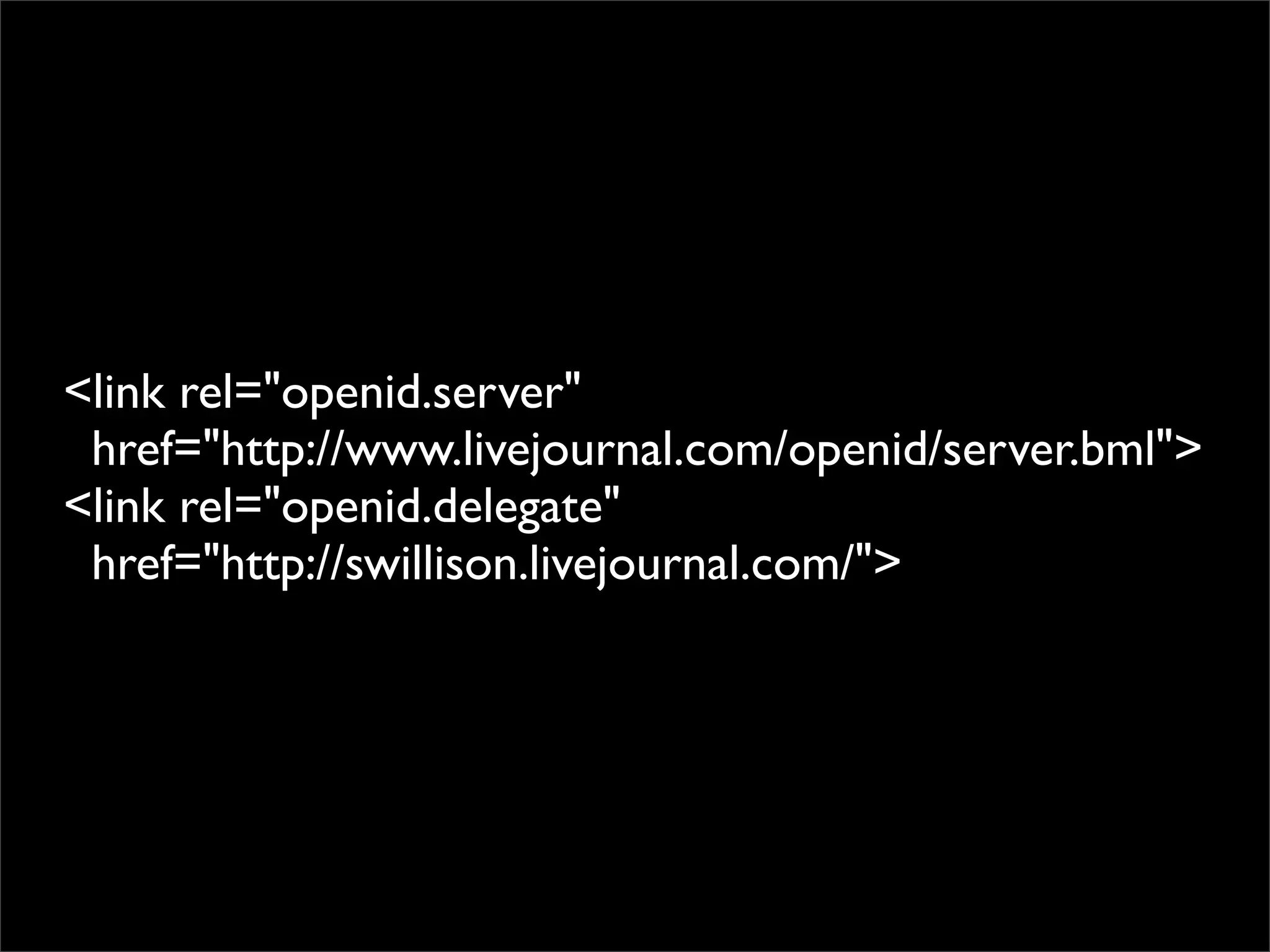
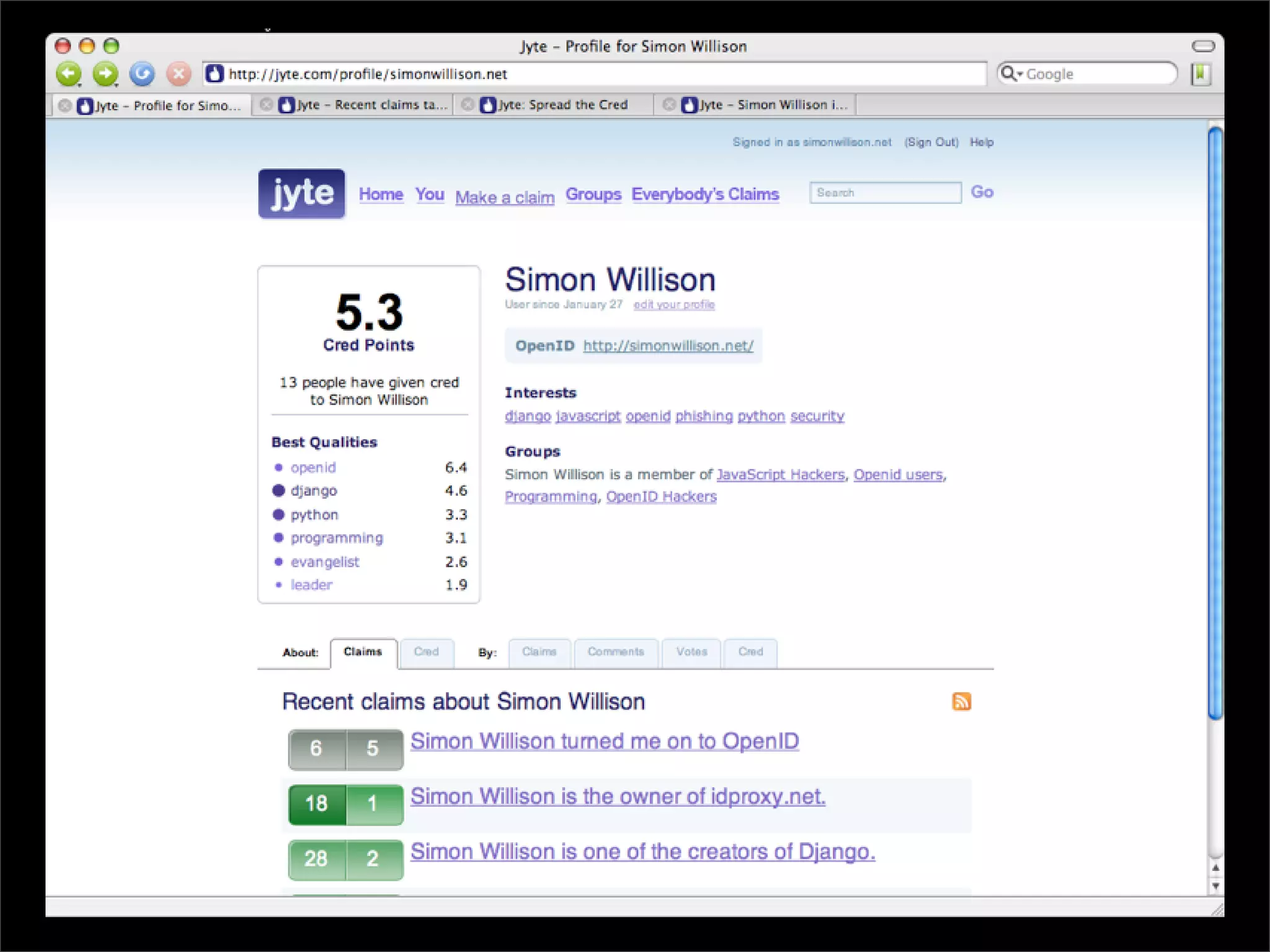
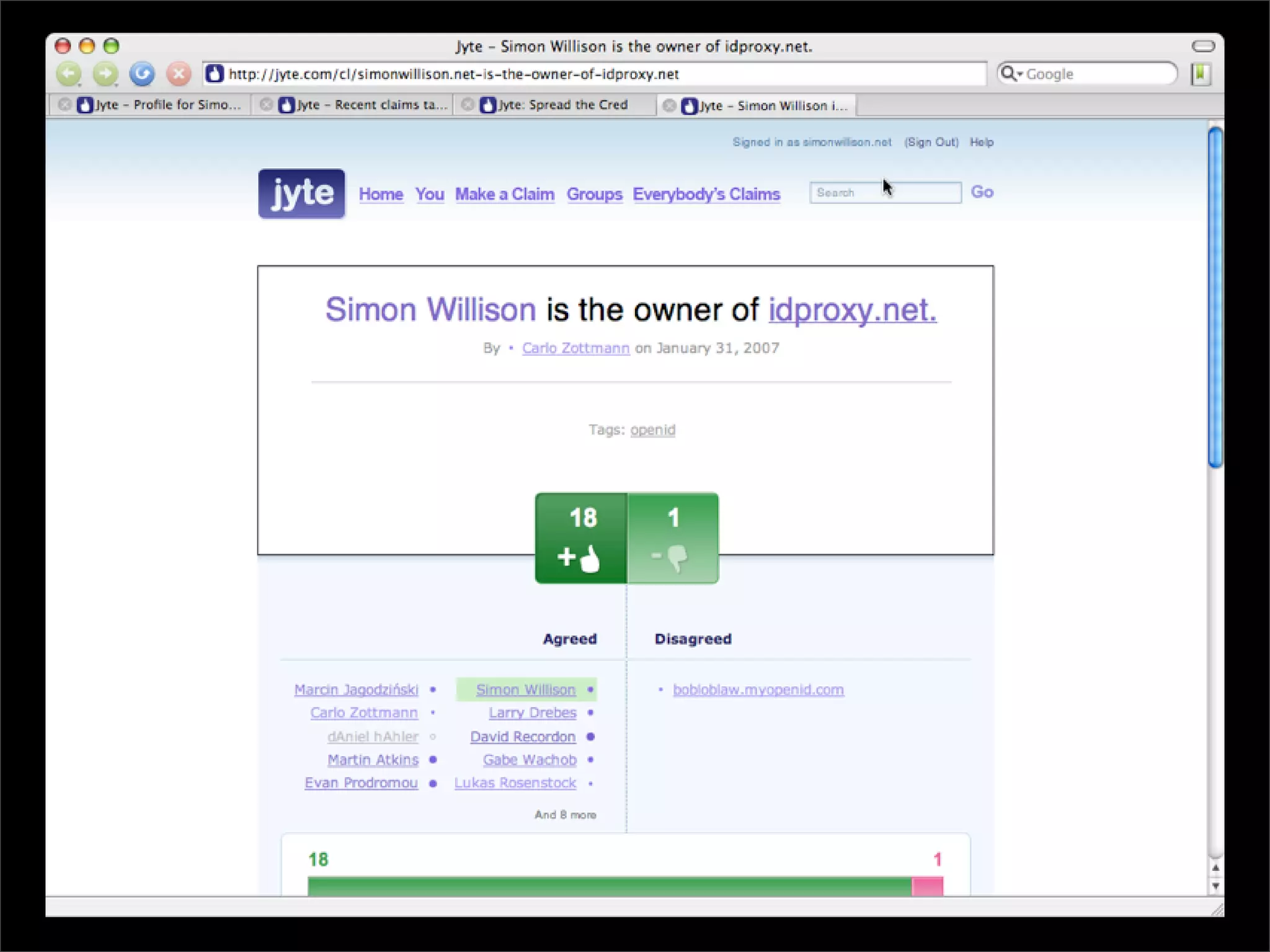
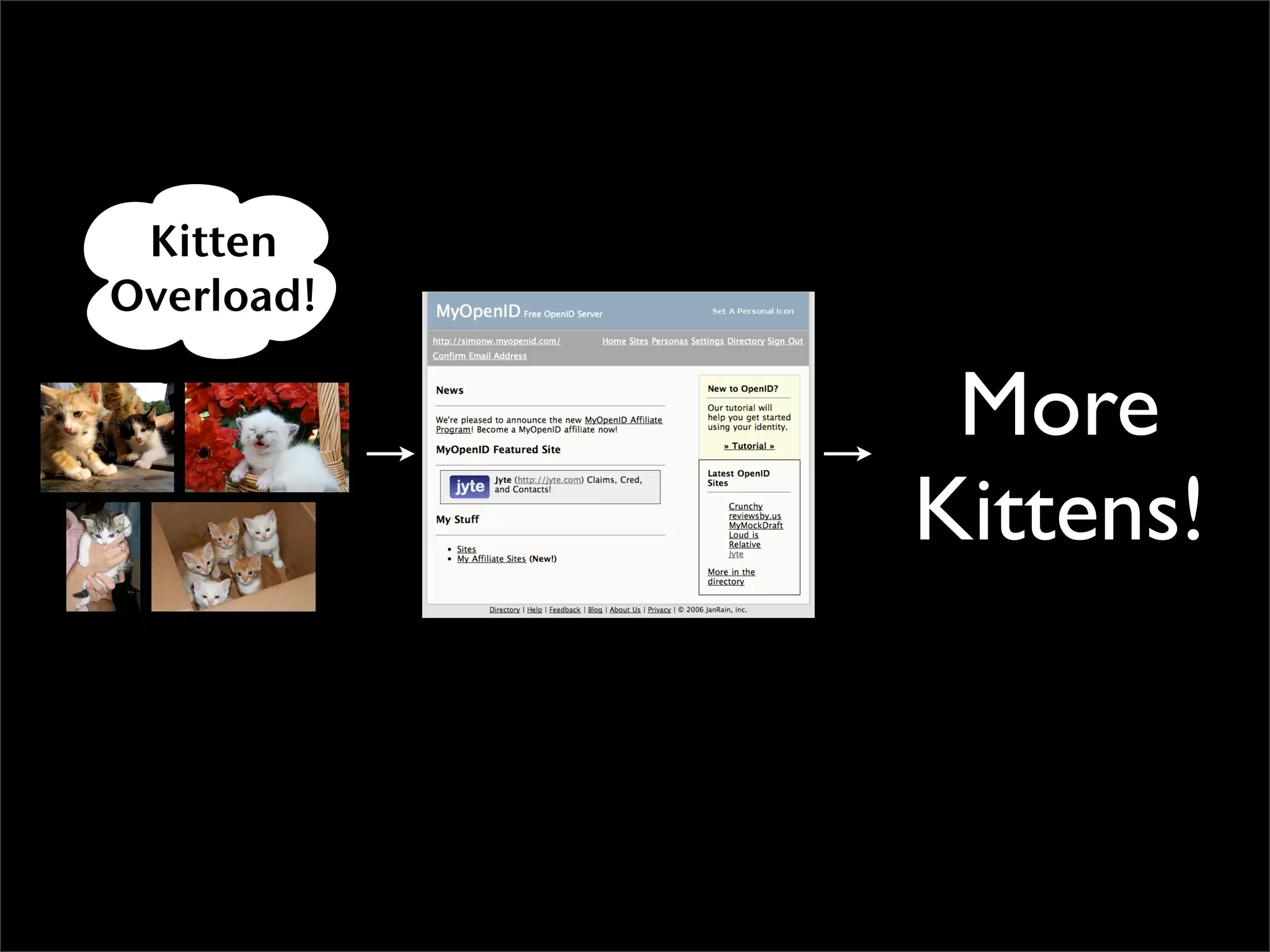
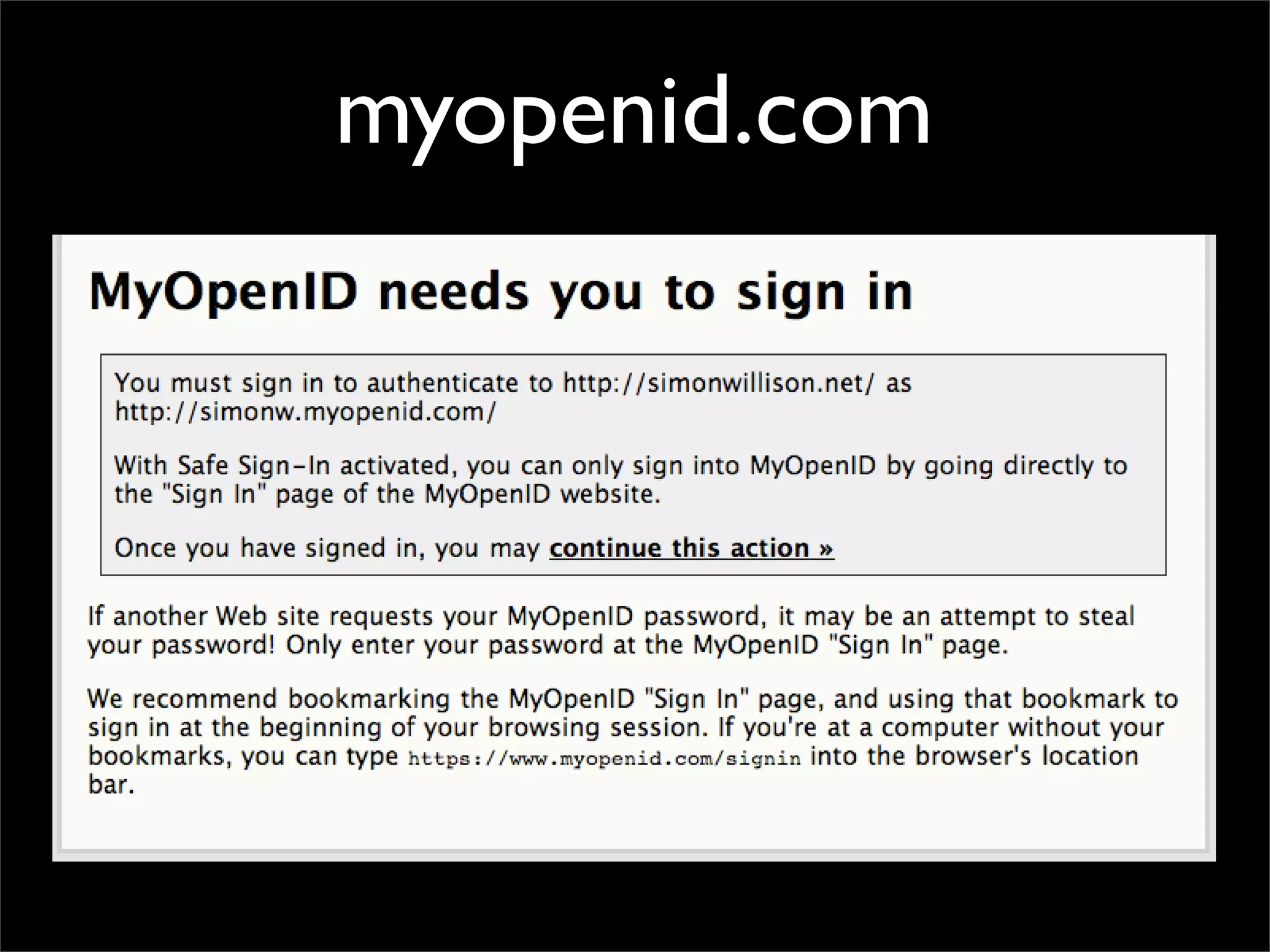
OpenID is a decentralized single sign-on system that allows users to log into multiple websites using their existing identities, such as a URL like "username.openid.com". It provides benefits like reducing the need to create and remember multiple usernames and passwords. However, OpenID also faces challenges like potential identity theft if the authentication provider is hacked, and that its technical workings can be difficult to explain to average users. Overall, OpenID shows promise as a solution to many of the frustrations of the current web authentication system, but also needs continued development to address security and usability issues.