Shift Left continous Testing.pptx
•Download as PPTX, PDF•
0 likes•8 views
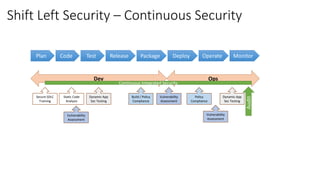
This document outlines a continuous security model that shifts security left by integrating it into the entire software development lifecycle from planning to deployment. It involves establishing security practices like training, threat modeling, static and dynamic testing, secrets management and monitoring across development, operations, and monitoring phases through automation and integration into existing DevOps processes. Centralized dashboards provide continuous feedback across teams.
Report
Share
Report
Share
Recommended
Devops security-An Insight into Secure-SDLC

The integration of Security into DevOps is already happening out of necessity. DevOps is a powerful paradigm shift and companies often don’t understand how security fits. Aim of this session is to give an overview of DevOps security and How security can be integrated and automated into each phases of software development life-cycle.
Secure SDLC in mobile software development.

Agenda:
- SDLC vs S-SDLC
- Mobile development security process
- What tools using for security testing?
- How to integrate into existing processes?
- What additionally you can do?
Software Security Initiatives

The document discusses starting a software security initiative within an organization using a maturity-based and metrics-driven approach. It recommends assessing the current maturity level, defining security standards and processes, and implementing security activities throughout the software development lifecycle (SDLC). Key metrics to track include the percentage of issues identified and fixed by lifecycle phase, average time to fix vulnerabilities, and vulnerability density.
DevSecOps Indonesia : Pain & Pleasure of doing AppSec in DevOps

1) The document discusses the challenges of implementing application security in a DevOps environment, noting that while many organizations are adopting DevOps, few are integrating security testing during development.
2) It presents the DevSecOps approach which incorporates security capabilities and practices into DevOps technologies, processes, and culture through principles of collaboration, continuous improvement, automation, and security as code.
3) Key aspects of DevSecOps discussed include threat modeling, static and dynamic application security testing integrated into the development pipeline, container security, analytics dashboards for visualizing security metrics and risks, and maturity models for prioritizing applications based on risk assessments.
Agile software security assurance

A short presentation covering the important aspects of an software security assurance effort in agile development environments. Towards the end we provide tips of how it can work in the real-world...
ОЛЬГА АКСЬОНЕНКО «Безпечна розробка програмного забезпечення в Agile проектах...

Online Quality Assurance Day 2020 #2
ОЛЬГА АКСЬОНЕНКО
«Безпечна розробка програмного забезпечення в Agile проектах»
telegram: wwww.t.me/goqameetup
fb: www.fb.com/goqaevent
fb: www.fb.com/qaday.org
Сайт: www.qaday.org
DevOps

The document discusses DevSecOps, which combines DevOps and network security. It outlines the stages of a DevSecOps pipeline including continuous integration, delivery, and deployment. It presents a DevSecOps manifesto advocating for open collaboration, security as a service, exploit testing, and compliance as operations. The document also provides examples of integrating security practices at different stages of the software development lifecycle and approaches for legacy versus new applications.
Recommended
Devops security-An Insight into Secure-SDLC

The integration of Security into DevOps is already happening out of necessity. DevOps is a powerful paradigm shift and companies often don’t understand how security fits. Aim of this session is to give an overview of DevOps security and How security can be integrated and automated into each phases of software development life-cycle.
Secure SDLC in mobile software development.

Agenda:
- SDLC vs S-SDLC
- Mobile development security process
- What tools using for security testing?
- How to integrate into existing processes?
- What additionally you can do?
Software Security Initiatives

The document discusses starting a software security initiative within an organization using a maturity-based and metrics-driven approach. It recommends assessing the current maturity level, defining security standards and processes, and implementing security activities throughout the software development lifecycle (SDLC). Key metrics to track include the percentage of issues identified and fixed by lifecycle phase, average time to fix vulnerabilities, and vulnerability density.
DevSecOps Indonesia : Pain & Pleasure of doing AppSec in DevOps

1) The document discusses the challenges of implementing application security in a DevOps environment, noting that while many organizations are adopting DevOps, few are integrating security testing during development.
2) It presents the DevSecOps approach which incorporates security capabilities and practices into DevOps technologies, processes, and culture through principles of collaboration, continuous improvement, automation, and security as code.
3) Key aspects of DevSecOps discussed include threat modeling, static and dynamic application security testing integrated into the development pipeline, container security, analytics dashboards for visualizing security metrics and risks, and maturity models for prioritizing applications based on risk assessments.
Agile software security assurance

A short presentation covering the important aspects of an software security assurance effort in agile development environments. Towards the end we provide tips of how it can work in the real-world...
ОЛЬГА АКСЬОНЕНКО «Безпечна розробка програмного забезпечення в Agile проектах...

Online Quality Assurance Day 2020 #2
ОЛЬГА АКСЬОНЕНКО
«Безпечна розробка програмного забезпечення в Agile проектах»
telegram: wwww.t.me/goqameetup
fb: www.fb.com/goqaevent
fb: www.fb.com/qaday.org
Сайт: www.qaday.org
DevOps

The document discusses DevSecOps, which combines DevOps and network security. It outlines the stages of a DevSecOps pipeline including continuous integration, delivery, and deployment. It presents a DevSecOps manifesto advocating for open collaboration, security as a service, exploit testing, and compliance as operations. The document also provides examples of integrating security practices at different stages of the software development lifecycle and approaches for legacy versus new applications.
Implementing an Application Security Pipeline in Jenkins

Performing continuous security testing in a DevOps environment with short release cycles and a continuous delivery pipeline is a big challenge and the traditional secure SDLC model fails to deliver the desired results. DevOps understand the process of built, test and deploy. They have largely automated this process in a delivery pipeline, they deploy to production multiple times per day but the big challenge is how can they do this securely?
This session will focus on a strategy to build an application security pipeline in Jenkins, challenges and possible solutions, also how existing application security solutions (SAST, DAST, IAST, OpenSource Libraries Analysis) are playing a key role in growing the relationship between security and DevOps.
Applicaiton Security - Building The Audit Program

Why and How to build an Application Security Audit Program from the ISACA Chicago 2012 Boat Cruise Event
Security Validation as Code.pdf

Cloud applications demand security validation to guarantee that the software is safe and compliant with security standards. It also aids in the prevention of data breaches and other threats prevalent to the public cloud.
we45 - SecDevOps Concept Presentation

we45’s SecDevOps and Security Automation Framework (2SAF) aims at decreasing mean time to product deployment with reduced operational resources – with the inclusion of relevant custom product security controls. The 2SAF enables engineering teams to implement a customized automated and threat modeled penetration testing model for every release of the produce lifecycle.
Our powerful Review – Train – Study model has enabled engineering and DevOps teams to implement 2SAF within weeks to a fully operational and measurable working framework.
Alt. GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using ...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Software Security Engineering

The document discusses approaches to building secure web applications, including establishing software security processes and maturity levels. It covers security activities like threat modeling, defining security requirements, secure coding standards, security testing, and metrics. Business cases for software security focus on reducing costs of vulnerabilities, threats to web apps, and root causes being application vulnerabilities and design flaws.
DevSecOps

Security Automation by integrating SAST(Static Application Security Testing),DAST(Dynamic Application Secuirty Testing) and SIEM (Security Information and Event Management) tools with Jenkins.
By automating Security(SAST,DAST,SIEM) developers can them selves perform VA and monitor on application without going to IT and Security team
Below Tools are used to Automate everything:
SAST - Fortify,CheckMarx
DAST - IBM App Scan,OWASP ZAP,HP Web Inspect
SIEM - Alien Vault
Security Validation

Security Validation as Code enables validation of cloud applications and infrastructure in a more automated and API-driven way. If you’re interested in implementing Security Validation as Code for your cloud applications, sign up for Prancer Platform!
Agile and Secure SDLC

This document discusses implementing a secure software development lifecycle (SDLC) to improve application security. It outlines why the traditional approach of only involving security experts does not work. Instead, it proposes integrating security practices throughout each phase of the development process, including requirements, design, implementation, verification, and release. This includes training developers, conducting threat modeling and security testing, using security tools in continuous integration, and analyzing results to address issues early. The goal is to reduce security defects over time by changing developer mindsets and integrating security as applications are built.
Agile and Secure Development

This document discusses SoftServe's approach to application security testing. It outlines typical security processes, reports, and issues found. It then proposes an integrated security process using both static code analysis and dynamic testing. This would involve deploying applications through a CI pipeline to security tools to identify vulnerabilities early in development cycles. The benefits are presented as reduced remediation costs, improved knowledge, and full technology coverage through internal testing versus third parties.
Securing Your Public Cloud Infrastructure

Public cloud providers operate on a shared responsibility model, which places the onus on the customer to define and secure the data and applications that are hosted within cloud infrastructure.
To that end, it is critical that organizations accurately and selectively pinpoint which cloud workloads and virtual IT assets must be monitored, updated and patched based on developing threats to customer data and applications.
In this webcast, Mark Butler, Chief Information Security Officer at Qualys, and Hari Srinivasan, Director of Product Management for Qualys Cloud and Virtualization Security detail how you can gain complete visibility of your organization’s entire cloud asset inventory and security posture to help you keep up with shared security responsibility models across public cloud infrastructure.
The presentation covers:
• Challenges surrounding increased migration to public clouds
• Using automation for secure DevOps
• How to ensure effective and efficient operations
To watch the on-demand webcast, visit https://lps.qualys.com/securing-your-public-cloud-infrastructure.html
Intro to Security in SDLC

This document discusses implementing a secure software development lifecycle (SDLC). It emphasizes building security into software from the start rather than adding it later. The summary is:
The document outlines a secure SDLC process involving defining security requirements, designing for security, implementing secure coding practices, testing software security, and ongoing security monitoring. It notes that software security is a shared responsibility and discusses challenges like team pushback and measuring security benefits. The document also presents a case study of a company that implemented a secure SDLC process to address client security issues and prevent future problems.
Digital Product Security

This document provides an overview of digital product security. It discusses common cyberattacks against businesses, security issues in product development processes, and tips for developing software with security by design. It emphasizes starting with secure requirements, using static analysis, dynamic testing, and manual reviews. Following secure SDLC practices and continuous integration of security tools can help improve security, reduce costs, and better satisfy security audits.
Application_security_Strategic

This document discusses building secure applications and outlines several key points:
1) It discusses the importance of application security governance, frameworks, processes and procedures, and secure coding practices across all layers of computing environments.
2) It outlines strategies for building security into the development process from design through testing and deployment.
3) It emphasizes the need for educating developers on security best practices and gaining their buy-in on secure development standards.
Cybersecurity overview - Open source compliance seminar

Follow this presentation to see how an OSS audit and static code analysis can be used to reduce and mitigate the security risks associated with open source software and Internet-based applications. Presented January 2016 at the Open source compliance seminar hosted Brooks Kushman and Rogue Wave Software.
Securing Devops_toolchain

This document outlines the key steps in a secure DevOps toolchain including pre-commit security checks like threat modeling and code reviews, continuous integration checks for dependencies, static analysis and unit tests, continuous delivery testing and scanning, and continuous monitoring and compliance checks once code is deployed to production. The goal is to build security into every stage of the development and deployment process from code check-ins through production.
Security management

Knowledge is power. This session will explore the rich real-time telemetry and tools available in Windows and in our cloud services for analyzing security activity in your IT environment.
Filling your AppSec Toolbox - Which Tools, When to Use Them, and Why

According to SAP 85% of cybersecurity attacks target the application layer. To be successful in defending against these attacks you need to use a variety of tools. In session we'll go into the various types application security tools and approaches, including SAST, DAST, RASP, PEN, as well as Open Source Vulnerability Management. We'll help you understand the differences between these tools and help you develop a plan for filling your application security toolbox.
Security Checkpoints in Agile SDLC

Product Engineering teams have started to realize the importance of software security. This has resulted in the trend where teams are taking efforts to include it as part of their software development life cycle; as opposed to treating it as another item in their checklist prior to release. However, the real challenge is in trying to find the balance between agility and quality which is where many team find this an uphill task.
While there is no golden standard when it comes to implementing software security, product teams should focus on bringing about systematic and cultural practices within their teams. This should help them to bring about the required efficiency to enable software security as a market differentiator.
This slide-deck on Software Security Initiative focuses on translating a plan of action into sustainable activities as part of the secure software development life cycle that can be adopted by engineering teams. The slides will delve deep into aspects like identifying and designing security checkpoints in the SDLC alongside concepts such as Threat Modelling in Agile, AppSec Toolchain and Security Regressions.
This was presented as a we45 Webinar on April 12, 2018
Layer 7: Automated SOA Policy Enforcement

Adam Vincent presents the challenges of run-time SOA governance & the path from automated policy enforcement to governance.
Crafting Excellence: A Comprehensive Guide to iOS Mobile App Development Serv...

Crafting Excellence: A Comprehensive Guide to iOS Mobile App Development Serv...Pitangent Analytics & Technology Solutions Pvt. Ltd
Discover top-tier mobile app development services, offering innovative solutions for iOS and Android. Enhance your business with custom, user-friendly mobile applications.Dandelion Hashtable: beyond billion requests per second on a commodity server

This slide deck presents DLHT, a concurrent in-memory hashtable. Despite efforts to optimize hashtables, that go as far as sacrificing core functionality, state-of-the-art designs still incur multiple memory accesses per request and block request processing in three cases. First, most hashtables block while waiting for data to be retrieved from memory. Second, open-addressing designs, which represent the current state-of-the-art, either cannot free index slots on deletes or must block all requests to do so. Third, index resizes block every request until all objects are copied to the new index. Defying folklore wisdom, DLHT forgoes open-addressing and adopts a fully-featured and memory-aware closed-addressing design based on bounded cache-line-chaining. This design offers lock-free index operations and deletes that free slots instantly, (2) completes most requests with a single memory access, (3) utilizes software prefetching to hide memory latencies, and (4) employs a novel non-blocking and parallel resizing. In a commodity server and a memory-resident workload, DLHT surpasses 1.6B requests per second and provides 3.5x (12x) the throughput of the state-of-the-art closed-addressing (open-addressing) resizable hashtable on Gets (Deletes).
More Related Content
Similar to Shift Left continous Testing.pptx
Implementing an Application Security Pipeline in Jenkins

Performing continuous security testing in a DevOps environment with short release cycles and a continuous delivery pipeline is a big challenge and the traditional secure SDLC model fails to deliver the desired results. DevOps understand the process of built, test and deploy. They have largely automated this process in a delivery pipeline, they deploy to production multiple times per day but the big challenge is how can they do this securely?
This session will focus on a strategy to build an application security pipeline in Jenkins, challenges and possible solutions, also how existing application security solutions (SAST, DAST, IAST, OpenSource Libraries Analysis) are playing a key role in growing the relationship between security and DevOps.
Applicaiton Security - Building The Audit Program

Why and How to build an Application Security Audit Program from the ISACA Chicago 2012 Boat Cruise Event
Security Validation as Code.pdf

Cloud applications demand security validation to guarantee that the software is safe and compliant with security standards. It also aids in the prevention of data breaches and other threats prevalent to the public cloud.
we45 - SecDevOps Concept Presentation

we45’s SecDevOps and Security Automation Framework (2SAF) aims at decreasing mean time to product deployment with reduced operational resources – with the inclusion of relevant custom product security controls. The 2SAF enables engineering teams to implement a customized automated and threat modeled penetration testing model for every release of the produce lifecycle.
Our powerful Review – Train – Study model has enabled engineering and DevOps teams to implement 2SAF within weeks to a fully operational and measurable working framework.
Alt. GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using ...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Software Security Engineering

The document discusses approaches to building secure web applications, including establishing software security processes and maturity levels. It covers security activities like threat modeling, defining security requirements, secure coding standards, security testing, and metrics. Business cases for software security focus on reducing costs of vulnerabilities, threats to web apps, and root causes being application vulnerabilities and design flaws.
DevSecOps

Security Automation by integrating SAST(Static Application Security Testing),DAST(Dynamic Application Secuirty Testing) and SIEM (Security Information and Event Management) tools with Jenkins.
By automating Security(SAST,DAST,SIEM) developers can them selves perform VA and monitor on application without going to IT and Security team
Below Tools are used to Automate everything:
SAST - Fortify,CheckMarx
DAST - IBM App Scan,OWASP ZAP,HP Web Inspect
SIEM - Alien Vault
Security Validation

Security Validation as Code enables validation of cloud applications and infrastructure in a more automated and API-driven way. If you’re interested in implementing Security Validation as Code for your cloud applications, sign up for Prancer Platform!
Agile and Secure SDLC

This document discusses implementing a secure software development lifecycle (SDLC) to improve application security. It outlines why the traditional approach of only involving security experts does not work. Instead, it proposes integrating security practices throughout each phase of the development process, including requirements, design, implementation, verification, and release. This includes training developers, conducting threat modeling and security testing, using security tools in continuous integration, and analyzing results to address issues early. The goal is to reduce security defects over time by changing developer mindsets and integrating security as applications are built.
Agile and Secure Development

This document discusses SoftServe's approach to application security testing. It outlines typical security processes, reports, and issues found. It then proposes an integrated security process using both static code analysis and dynamic testing. This would involve deploying applications through a CI pipeline to security tools to identify vulnerabilities early in development cycles. The benefits are presented as reduced remediation costs, improved knowledge, and full technology coverage through internal testing versus third parties.
Securing Your Public Cloud Infrastructure

Public cloud providers operate on a shared responsibility model, which places the onus on the customer to define and secure the data and applications that are hosted within cloud infrastructure.
To that end, it is critical that organizations accurately and selectively pinpoint which cloud workloads and virtual IT assets must be monitored, updated and patched based on developing threats to customer data and applications.
In this webcast, Mark Butler, Chief Information Security Officer at Qualys, and Hari Srinivasan, Director of Product Management for Qualys Cloud and Virtualization Security detail how you can gain complete visibility of your organization’s entire cloud asset inventory and security posture to help you keep up with shared security responsibility models across public cloud infrastructure.
The presentation covers:
• Challenges surrounding increased migration to public clouds
• Using automation for secure DevOps
• How to ensure effective and efficient operations
To watch the on-demand webcast, visit https://lps.qualys.com/securing-your-public-cloud-infrastructure.html
Intro to Security in SDLC

This document discusses implementing a secure software development lifecycle (SDLC). It emphasizes building security into software from the start rather than adding it later. The summary is:
The document outlines a secure SDLC process involving defining security requirements, designing for security, implementing secure coding practices, testing software security, and ongoing security monitoring. It notes that software security is a shared responsibility and discusses challenges like team pushback and measuring security benefits. The document also presents a case study of a company that implemented a secure SDLC process to address client security issues and prevent future problems.
Digital Product Security

This document provides an overview of digital product security. It discusses common cyberattacks against businesses, security issues in product development processes, and tips for developing software with security by design. It emphasizes starting with secure requirements, using static analysis, dynamic testing, and manual reviews. Following secure SDLC practices and continuous integration of security tools can help improve security, reduce costs, and better satisfy security audits.
Application_security_Strategic

This document discusses building secure applications and outlines several key points:
1) It discusses the importance of application security governance, frameworks, processes and procedures, and secure coding practices across all layers of computing environments.
2) It outlines strategies for building security into the development process from design through testing and deployment.
3) It emphasizes the need for educating developers on security best practices and gaining their buy-in on secure development standards.
Cybersecurity overview - Open source compliance seminar

Follow this presentation to see how an OSS audit and static code analysis can be used to reduce and mitigate the security risks associated with open source software and Internet-based applications. Presented January 2016 at the Open source compliance seminar hosted Brooks Kushman and Rogue Wave Software.
Securing Devops_toolchain

This document outlines the key steps in a secure DevOps toolchain including pre-commit security checks like threat modeling and code reviews, continuous integration checks for dependencies, static analysis and unit tests, continuous delivery testing and scanning, and continuous monitoring and compliance checks once code is deployed to production. The goal is to build security into every stage of the development and deployment process from code check-ins through production.
Security management

Knowledge is power. This session will explore the rich real-time telemetry and tools available in Windows and in our cloud services for analyzing security activity in your IT environment.
Filling your AppSec Toolbox - Which Tools, When to Use Them, and Why

According to SAP 85% of cybersecurity attacks target the application layer. To be successful in defending against these attacks you need to use a variety of tools. In session we'll go into the various types application security tools and approaches, including SAST, DAST, RASP, PEN, as well as Open Source Vulnerability Management. We'll help you understand the differences between these tools and help you develop a plan for filling your application security toolbox.
Security Checkpoints in Agile SDLC

Product Engineering teams have started to realize the importance of software security. This has resulted in the trend where teams are taking efforts to include it as part of their software development life cycle; as opposed to treating it as another item in their checklist prior to release. However, the real challenge is in trying to find the balance between agility and quality which is where many team find this an uphill task.
While there is no golden standard when it comes to implementing software security, product teams should focus on bringing about systematic and cultural practices within their teams. This should help them to bring about the required efficiency to enable software security as a market differentiator.
This slide-deck on Software Security Initiative focuses on translating a plan of action into sustainable activities as part of the secure software development life cycle that can be adopted by engineering teams. The slides will delve deep into aspects like identifying and designing security checkpoints in the SDLC alongside concepts such as Threat Modelling in Agile, AppSec Toolchain and Security Regressions.
This was presented as a we45 Webinar on April 12, 2018
Layer 7: Automated SOA Policy Enforcement

Adam Vincent presents the challenges of run-time SOA governance & the path from automated policy enforcement to governance.
Similar to Shift Left continous Testing.pptx (20)
Implementing an Application Security Pipeline in Jenkins

Implementing an Application Security Pipeline in Jenkins
Alt. GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using ...

Alt. GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using ...
Cybersecurity overview - Open source compliance seminar

Cybersecurity overview - Open source compliance seminar
Filling your AppSec Toolbox - Which Tools, When to Use Them, and Why

Filling your AppSec Toolbox - Which Tools, When to Use Them, and Why
Recently uploaded
Crafting Excellence: A Comprehensive Guide to iOS Mobile App Development Serv...

Crafting Excellence: A Comprehensive Guide to iOS Mobile App Development Serv...Pitangent Analytics & Technology Solutions Pvt. Ltd
Discover top-tier mobile app development services, offering innovative solutions for iOS and Android. Enhance your business with custom, user-friendly mobile applications.Dandelion Hashtable: beyond billion requests per second on a commodity server

This slide deck presents DLHT, a concurrent in-memory hashtable. Despite efforts to optimize hashtables, that go as far as sacrificing core functionality, state-of-the-art designs still incur multiple memory accesses per request and block request processing in three cases. First, most hashtables block while waiting for data to be retrieved from memory. Second, open-addressing designs, which represent the current state-of-the-art, either cannot free index slots on deletes or must block all requests to do so. Third, index resizes block every request until all objects are copied to the new index. Defying folklore wisdom, DLHT forgoes open-addressing and adopts a fully-featured and memory-aware closed-addressing design based on bounded cache-line-chaining. This design offers lock-free index operations and deletes that free slots instantly, (2) completes most requests with a single memory access, (3) utilizes software prefetching to hide memory latencies, and (4) employs a novel non-blocking and parallel resizing. In a commodity server and a memory-resident workload, DLHT surpasses 1.6B requests per second and provides 3.5x (12x) the throughput of the state-of-the-art closed-addressing (open-addressing) resizable hashtable on Gets (Deletes).
"What does it really mean for your system to be available, or how to define w...

We will talk about system monitoring from a few different angles. We will start by covering the basics, then discuss SLOs, how to define them, and why understanding the business well is crucial for success in this exercise.
Apps Break Data

How information systems are built or acquired puts information, which is what they should be about, in a secondary place. Our language adapted accordingly, and we no longer talk about information systems but applications. Applications evolved in a way to break data into diverse fragments, tightly coupled with applications and expensive to integrate. The result is technical debt, which is re-paid by taking even bigger "loans", resulting in an ever-increasing technical debt. Software engineering and procurement practices work in sync with market forces to maintain this trend. This talk demonstrates how natural this situation is. The question is: can something be done to reverse the trend?
"$10 thousand per minute of downtime: architecture, queues, streaming and fin...

Direct losses from downtime in 1 minute = $5-$10 thousand dollars. Reputation is priceless.
As part of the talk, we will consider the architectural strategies necessary for the development of highly loaded fintech solutions. We will focus on using queues and streaming to efficiently work and manage large amounts of data in real-time and to minimize latency.
We will focus special attention on the architectural patterns used in the design of the fintech system, microservices and event-driven architecture, which ensure scalability, fault tolerance, and consistency of the entire system.
"Frontline Battles with DDoS: Best practices and Lessons Learned", Igor Ivaniuk

At this talk we will discuss DDoS protection tools and best practices, discuss network architectures and what AWS has to offer. Also, we will look into one of the largest DDoS attacks on Ukrainian infrastructure that happened in February 2022. We'll see, what techniques helped to keep the web resources available for Ukrainians and how AWS improved DDoS protection for all customers based on Ukraine experience
Session 1 - Intro to Robotic Process Automation.pdf

👉 Check out our full 'Africa Series - Automation Student Developers (EN)' page to register for the full program:
https://bit.ly/Automation_Student_Kickstart
In this session, we shall introduce you to the world of automation, the UiPath Platform, and guide you on how to install and setup UiPath Studio on your Windows PC.
📕 Detailed agenda:
What is RPA? Benefits of RPA?
RPA Applications
The UiPath End-to-End Automation Platform
UiPath Studio CE Installation and Setup
💻 Extra training through UiPath Academy:
Introduction to Automation
UiPath Business Automation Platform
Explore automation development with UiPath Studio
👉 Register here for our upcoming Session 2 on June 20: Introduction to UiPath Studio Fundamentals: https://community.uipath.com/events/details/uipath-lagos-presents-session-2-introduction-to-uipath-studio-fundamentals/
High performance Serverless Java on AWS- GoTo Amsterdam 2024

Java is for many years one of the most popular programming languages, but it used to have hard times in the Serverless community. Java is known for its high cold start times and high memory footprint, comparing to other programming languages like Node.js and Python. In this talk I'll look at the general best practices and techniques we can use to decrease memory consumption, cold start times for Java Serverless development on AWS including GraalVM (Native Image) and AWS own offering SnapStart based on Firecracker microVM snapshot and restore and CRaC (Coordinated Restore at Checkpoint) runtime hooks. I'll also provide a lot of benchmarking on Lambda functions trying out various deployment package sizes, Lambda memory settings, Java compilation options and HTTP (a)synchronous clients and measure their impact on cold and warm start times.
The Microsoft 365 Migration Tutorial For Beginner.pptx

This presentation will help you understand the power of Microsoft 365. However, we have mentioned every productivity app included in Office 365. Additionally, we have suggested the migration situation related to Office 365 and how we can help you.
You can also read: https://www.systoolsgroup.com/updates/office-365-tenant-to-tenant-migration-step-by-step-complete-guide/
Freshworks Rethinks NoSQL for Rapid Scaling & Cost-Efficiency

Freshworks creates AI-boosted business software that helps employees work more efficiently and effectively. Managing data across multiple RDBMS and NoSQL databases was already a challenge at their current scale. To prepare for 10X growth, they knew it was time to rethink their database strategy. Learn how they architected a solution that would simplify scaling while keeping costs under control.
How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf

A Mix Chart displays historical data of numbers in a graphical or tabular form. The Kalyan Rajdhani Mix Chart specifically shows the results of a sequence of numbers over different periods.
"NATO Hackathon Winner: AI-Powered Drug Search", Taras Kloba

This is a session that details how PostgreSQL's features and Azure AI Services can be effectively used to significantly enhance the search functionality in any application.
In this session, we'll share insights on how we used PostgreSQL to facilitate precise searches across multiple fields in our mobile application. The techniques include using LIKE and ILIKE operators and integrating a trigram-based search to handle potential misspellings, thereby increasing the search accuracy.
We'll also discuss how the azure_ai extension on PostgreSQL databases in Azure and Azure AI Services were utilized to create vectors from user input, a feature beneficial when users wish to find specific items based on text prompts. While our application's case study involves a drug search, the techniques and principles shared in this session can be adapted to improve search functionality in a wide range of applications. Join us to learn how PostgreSQL and Azure AI can be harnessed to enhance your application's search capability.
Northern Engraving | Nameplate Manufacturing Process - 2024

Manufacturing custom quality metal nameplates and badges involves several standard operations. Processes include sheet prep, lithography, screening, coating, punch press and inspection. All decoration is completed in the flat sheet with adhesive and tooling operations following. The possibilities for creating unique durable nameplates are endless. How will you create your brand identity? We can help!
Harnessing the Power of NLP and Knowledge Graphs for Opioid Research

Gursev Pirge, PhD
Senior Data Scientist - JohnSnowLabs
From Natural Language to Structured Solr Queries using LLMs

This talk draws on experimentation to enable AI applications with Solr. One important use case is to use AI for better accessibility and discoverability of the data: while User eXperience techniques, lexical search improvements, and data harmonization can take organizations to a good level of accessibility, a structural (or “cognitive” gap) remains between the data user needs and the data producer constraints.
That is where AI – and most importantly, Natural Language Processing and Large Language Model techniques – could make a difference. This natural language, conversational engine could facilitate access and usage of the data leveraging the semantics of any data source.
The objective of the presentation is to propose a technical approach and a way forward to achieve this goal.
The key concept is to enable users to express their search queries in natural language, which the LLM then enriches, interprets, and translates into structured queries based on the Solr index’s metadata.
This approach leverages the LLM’s ability to understand the nuances of natural language and the structure of documents within Apache Solr.
The LLM acts as an intermediary agent, offering a transparent experience to users automatically and potentially uncovering relevant documents that conventional search methods might overlook. The presentation will include the results of this experimental work, lessons learned, best practices, and the scope of future work that should improve the approach and make it production-ready.
Leveraging the Graph for Clinical Trials and Standards

Katja Glaß
OpenStudyBuilder Community Manager - Katja Glaß Consulting
Marius Conjeaud
Principal Consultant - Neo4j
"Scaling RAG Applications to serve millions of users", Kevin Goedecke

How we managed to grow and scale a RAG application from zero to thousands of users in 7 months. Lessons from technical challenges around managing high load for LLMs, RAGs and Vector databases.
Astute Business Solutions | Oracle Cloud Partner |

Your goto partner for Oracle Cloud, PeopleSoft, E-Business Suite, and Ellucian Banner. We are a firm specialized in managed services and consulting.
GNSS spoofing via SDR (Criptored Talks 2024)

In the realm of cybersecurity, offensive security practices act as a critical shield. By simulating real-world attacks in a controlled environment, these techniques expose vulnerabilities before malicious actors can exploit them. This proactive approach allows manufacturers to identify and fix weaknesses, significantly enhancing system security.
This presentation delves into the development of a system designed to mimic Galileo's Open Service signal using software-defined radio (SDR) technology. We'll begin with a foundational overview of both Global Navigation Satellite Systems (GNSS) and the intricacies of digital signal processing.
The presentation culminates in a live demonstration. We'll showcase the manipulation of Galileo's Open Service pilot signal, simulating an attack on various software and hardware systems. This practical demonstration serves to highlight the potential consequences of unaddressed vulnerabilities, emphasizing the importance of offensive security practices in safeguarding critical infrastructure.
Recently uploaded (20)
Crafting Excellence: A Comprehensive Guide to iOS Mobile App Development Serv...

Crafting Excellence: A Comprehensive Guide to iOS Mobile App Development Serv...
Dandelion Hashtable: beyond billion requests per second on a commodity server

Dandelion Hashtable: beyond billion requests per second on a commodity server
"What does it really mean for your system to be available, or how to define w...

"What does it really mean for your system to be available, or how to define w...
"$10 thousand per minute of downtime: architecture, queues, streaming and fin...

"$10 thousand per minute of downtime: architecture, queues, streaming and fin...
"Frontline Battles with DDoS: Best practices and Lessons Learned", Igor Ivaniuk

"Frontline Battles with DDoS: Best practices and Lessons Learned", Igor Ivaniuk
Session 1 - Intro to Robotic Process Automation.pdf

Session 1 - Intro to Robotic Process Automation.pdf
High performance Serverless Java on AWS- GoTo Amsterdam 2024

High performance Serverless Java on AWS- GoTo Amsterdam 2024
The Microsoft 365 Migration Tutorial For Beginner.pptx

The Microsoft 365 Migration Tutorial For Beginner.pptx
Freshworks Rethinks NoSQL for Rapid Scaling & Cost-Efficiency

Freshworks Rethinks NoSQL for Rapid Scaling & Cost-Efficiency
How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf

How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf
"NATO Hackathon Winner: AI-Powered Drug Search", Taras Kloba

"NATO Hackathon Winner: AI-Powered Drug Search", Taras Kloba
Northern Engraving | Nameplate Manufacturing Process - 2024

Northern Engraving | Nameplate Manufacturing Process - 2024
Harnessing the Power of NLP and Knowledge Graphs for Opioid Research

Harnessing the Power of NLP and Knowledge Graphs for Opioid Research
From Natural Language to Structured Solr Queries using LLMs

From Natural Language to Structured Solr Queries using LLMs
Leveraging the Graph for Clinical Trials and Standards

Leveraging the Graph for Clinical Trials and Standards
"Scaling RAG Applications to serve millions of users", Kevin Goedecke

"Scaling RAG Applications to serve millions of users", Kevin Goedecke
Astute Business Solutions | Oracle Cloud Partner |

Astute Business Solutions | Oracle Cloud Partner |
Shift Left continous Testing.pptx
- 1. Shift Left Security – Continuous Security Plan Code Test Package Release Deploy Monitor Operate Dev Ops Continuous Integrated Security Audit Secure SDLC Training Static Code Analysis Vulnerability Assessment Dynamic App Sec Testing Build / Policy Compliance Vulnerability Assessment Vulnerability Assessment Policy Compliance Dynamic App Sec Testing
- 2. CODE BUILD TEST DEPLOY OPERATE MONITOR Manage digital supply chain Automated Software Composition Analysis Automated Container Image Scanning Scan artifact and source code repositories Threat modeling Security Requirements Security SLA cloud providers Risk Analysis Automated Security Testing Automated Static Testing Integrate security tests with unit testing Run-Time application security testing Establish Security Mindset Perform Security Training Establish Security Satellites Perform Continuous Assurance Manual Security Testing Manual Penetration Testing Manual Security Verifications Secrets management Security Configuration Automation Automated Remediation Practice Incident Response Continuous Monitoring Security Controls Application behaviour Ci/CD security metrics System metrics Security SLAs Centralised dashboards Self-service capabilities for dev and ops Continuous feedback from prod to dev Secure the Ci/CD pipeline