SDK Datasheet
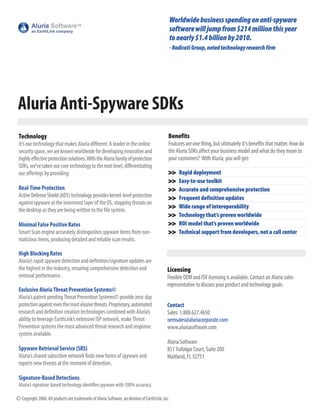
- 2. Aluria AntiSpyware SDKs Proven, reliable and robust gateway and desktop antispyware technologyfromAluria Software. Local Points Forms of Spyware of Entry ! ! Internet • Adware (Discs,Thumbdrives, Etc.) (Threat Pool) • Backdoor ! ! • Cookies ! ! • Homepage Hijacker • Searchpage Hijacker • Rogue ActiveX • BHO • Emailer • Keylogger • Dialer • Remote AdminTools • Security Software Subverter • Trojan • Malware • Thiefware • Dataminer Dual Layered Protection • Surveillance Software Unique to our industry, the Aluria family of protection SDKs offers complete multilayered protection against spyware. • Consumerware Two independently engineered SDKs one Desktop/Server, one Gateway can be combined to stop spyware from entering • Covert Installer a network regardless of point of entry whether Web, disk, email, etc. • HackerTools Gateway Protection Desktop/Server Protection Installed on the server/gateway Installed on individual desktops and network servers Protects against external threats (i.e. file traffic, Web sites and IP addresses) Active Defense Shield (ADS) Built on vast Aluria/EarthLink definitions database Blocks in real time & at the kernel level Adds value to IDS/IPS/NAC solutions Protects registry & file system through all entry points Protects from both internal and external threats, and is an ideal solution for stopping spyware with elusive morphing properties Scans on demand The Aluria family of SDKs are feature rich and versatile, requiring minimal development effort while providing maximum opportunity for a rapid return on investment. Gateway Protection Desktop/Server Protection Database • Designed specifically for network gateways • Comprehensive scan engine and spyware Created in 1999, Aluria’s definitions database • Works with the Desktop/Server Protection SDK definition database deliver accurate and continues to be among the largest and most • Blocks spyware at the gateway before it reliable scan results and removal routines definitive in the world, fully supported by one of the reaches the network • Robust antispyware application most dynamic and aggressive research teams in the • Similar feature set as the Desktop/Server • Programming interface (API) industry. With a direct tie to EarthLink, (our parent Protection SDK • Written in C++ with full interoperability with company), and its 7 million residential and • Supported Operating Systems: Windows VB, MFC, Win32, C, C++ and C# commercial subscribers, Aluria Software is uniquely 9X to 2003, Linux (Debian, Mandrake, SUSE, • Scanning and quarantining ability for able to identify threats in real time. The same cannot Red Hat, Knoppix) and Unix (FreeBSD, NetBSD) inmemory processes, registry keys, be said for other antispyware companies dependent • Supported architectures: X86, 32bit Little files/directories, services, drivers and cookies upon thirdparty updates which many times result in Endian, ARM Big Endian/Little Endian, MIsPS • Customizable definition files lessthanreliable protection. Big Endian/Little Endian • Choice of full or partial definition load • Includes multifaceted protection and monitoring • Supports COMbased applications Aluria’s massive spyware database is constantly • Monitors file traffic, Web sites and IP addresses • Multithreading capability updated to provide our OEM and ISV partners with • Scans compressed files (future release) • Incremental update capability the latest spyware signatures and profiles, ensuring • Notifies based on events • Highspeed scans your customers’ information remains secure. • Ability to use shim libraries (future release) • Targets customized Linux operating systems Contact More Info 1.888.627.4650 To learn more about Aluria’s technology visit oemsales@aluriacorporate.com www.aluriasoftware.com/technology/