Rundll32test
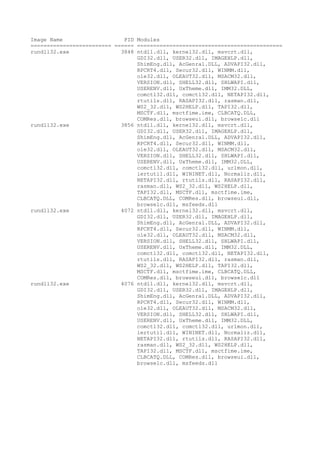
- 1. Image Name PID Modules ========================= ====== ============================================= rundll32.exe 3848 ntdll.dll, kernel32.dll, msvcrt.dll, GDI32.dll, USER32.dll, IMAGEHLP.dll, ShimEng.dll, AcGenral.DLL, ADVAPI32.dll, RPCRT4.dll, Secur32.dll, WINMM.dll, ole32.dll, OLEAUT32.dll, MSACM32.dll, VERSION.dll, SHELL32.dll, SHLWAPI.dll, USERENV.dll, UxTheme.dll, IMM32.DLL, comctl32.dll, comctl32.dll, NETAPI32.dll, rtutils.dll, RASAPI32.dll, rasman.dll, WS2_32.dll, WS2HELP.dll, TAPI32.dll, MSCTF.dll, msctfime.ime, CLBCATQ.DLL, COMRes.dll, browseui.dll, browselc.dll rundll32.exe 3856 ntdll.dll, kernel32.dll, msvcrt.dll, GDI32.dll, USER32.dll, IMAGEHLP.dll, ShimEng.dll, AcGenral.DLL, ADVAPI32.dll, RPCRT4.dll, Secur32.dll, WINMM.dll, ole32.dll, OLEAUT32.dll, MSACM32.dll, VERSION.dll, SHELL32.dll, SHLWAPI.dll, USERENV.dll, UxTheme.dll, IMM32.DLL, comctl32.dll, comctl32.dll, urlmon.dll, iertutil.dll, WININET.dll, Normaliz.dll, NETAPI32.dll, rtutils.dll, RASAPI32.dll, rasman.dll, WS2_32.dll, WS2HELP.dll, TAPI32.dll, MSCTF.dll, msctfime.ime, CLBCATQ.DLL, COMRes.dll, browseui.dll, browselc.dll, msfeeds.dll rundll32.exe 4072 ntdll.dll, kernel32.dll, msvcrt.dll, GDI32.dll, USER32.dll, IMAGEHLP.dll, ShimEng.dll, AcGenral.DLL, ADVAPI32.dll, RPCRT4.dll, Secur32.dll, WINMM.dll, ole32.dll, OLEAUT32.dll, MSACM32.dll, VERSION.dll, SHELL32.dll, SHLWAPI.dll, USERENV.dll, UxTheme.dll, IMM32.DLL, comctl32.dll, comctl32.dll, NETAPI32.dll, rtutils.dll, RASAPI32.dll, rasman.dll, WS2_32.dll, WS2HELP.dll, TAPI32.dll, MSCTF.dll, msctfime.ime, CLBCATQ.DLL, COMRes.dll, browseui.dll, browselc.dll rundll32.exe 4076 ntdll.dll, kernel32.dll, msvcrt.dll, GDI32.dll, USER32.dll, IMAGEHLP.dll, ShimEng.dll, AcGenral.DLL, ADVAPI32.dll, RPCRT4.dll, Secur32.dll, WINMM.dll, ole32.dll, OLEAUT32.dll, MSACM32.dll, VERSION.dll, SHELL32.dll, SHLWAPI.dll, USERENV.dll, UxTheme.dll, IMM32.DLL, comctl32.dll, comctl32.dll, urlmon.dll, iertutil.dll, WININET.dll, Normaliz.dll, NETAPI32.dll, rtutils.dll, RASAPI32.dll, rasman.dll, WS2_32.dll, WS2HELP.dll, TAPI32.dll, MSCTF.dll, msctfime.ime, CLBCATQ.DLL, COMRes.dll, browseui.dll, browselc.dll, msfeeds.dll