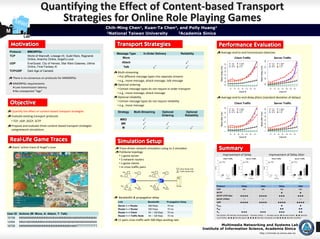
Quantifying the Effect of Content-based Transport Strategies for Online Role Playing Games
- 1. Quantifying the Effect of Content‐based Transport MNe t Strategies for Online Role Playing Games Chih-Ming Chen1, Kuan-Ta Chen2, and Polly Huang1 M 1National Taiwan University 2Academia Sinica Lab Motivation Transport Strategies Performance Evaluation Protocol MMORPGs Average end‐to‐end transmission latencies Message Type In-Order Delivery Reliability TCP World of Warcraft, Lineage I/II, Guild Wars, Ragnarok Move Client Traffic Server Traffic Online, Anarchy Online, Angel’s Love 600 UDP EverQuest, City of Heroes, Star Wars Galaxies, Ultima Attack √ TCP P_MRO TCP P_MRO 180 200 220 240 260 280 300 UDP P_MR UDP P_MR Online, Final Fantasy XI Talk √ √ 500 Mean delay (ms) Mean delay (ms) SCTP P_M SCTP P_M TCP/UDP Dark Age of Camelot Multi‐streaming 400 There is no consensus on protocols for MMORPGs • Put different message types into separate streams 300 • e.g., move message, attack message, talk message MMORPGs requirements 200 Optional ordering Low transmission latency • Certain message types do not require in‐order transport 20 40 60 80 100 120 140 20 40 60 80 100 120 140 No unexpected “lags” Client # Client # • e.g., move message, attack message Optional reliability Average end‐to‐end delay jitters (standard deviation of delays) Objective • Certain message types do not require reliability • e.g., move message Client Traffic Server Traffic 250 600 TCP P_MRO TCP P_MRO Quantify the effect of content‐based transport strategies Strategy Multi-Streaming Optional Optional UDP P_MR UDP P_MR 200 500 SCTP P_M SCTP P_M Mean jitter (ms) Mean jitter (ms) Evaluate existing transport protocols Ordering Reliability 400 150 MRO √ 300 • TCP, UDP, DCCP, SCTP 100 MR √ √ 200 Propose and evaluate three content‐based transport strategies 50 100 M √ √ √ usingnetwork simulations 0 0 20 40 60 80 100 120 140 20 40 60 80 100 120 140 Real-Life Game Traces Real-Life Client # Client # Simulation Setup Users’ action trace of Angel’s Love Trace‐driven network simulation using ns‐2 simulator Summary Fishbone topology • 1 game server Improvement of Delay Improvement of Delay Jitter • 2 network routers Client Traffic Server Traffic Client Traffic Server Traffic 100 100 100 100 70 Clients 70 Clients 70 Clients 70 Clients • n game clients 140 Clients 75 140 Clients 140 Clients 79 140 Clients 80 80 80 80 73 69 69 • m cross traffic pairs 55 60 60 60 60 Score Score Score Score 45 46 Client Node (CN) 40 40 40 40 33 28 CNi+2 . . . CN CN2 . . . CN Traffic Node (TN) 20 20 20 20 8 10 n i 0 2 0 0 2 0 1 1 0 1 5 5 CNi+1 CN1 0 0 0 0 P_MRO P_MR P_M P_MRO P_MR P_M P_MRO P_MR P_M P_MRO P_MR P_M Protocol Protocol Protocol Protocol Client to Server Server to Client TNj+1 TN1 Server Protocol Delay Jitter Delay Jitter TNj+2 . . . TNm TN2 TN . . . j TCP NA NA NA NA SCTP ≈ ≈ ★ ★ DCCP (TCP-like) ★★★★ ★★★★ ★★★ ★★★ Bandwidth & propagation delay DCCP (TFRC) ☆ ☆ ☆ ☆ Link Bandwidth Propagation Delay UDP ★★★★ ★★★★ ★★★★ ★★★★ Server <--> Router 600 Kbps 70 ms PMRO ≈ ≈ ★ ★ Router <--> Router 600 Kbps 70 ms PMR ≈ ≈ ★★ ★★ Router <--> Client 64 ~ 128 Kbps 70 ms PM ★★★ ★★★ ★★★ ★★ User ID Actions (M: Move, A: Attack, T: Talk) Description: NA denotes incomparable, ≈ denotes similar, ☆ denotes worse, ★ denotes better, ★ ★ denotes Router <--> Traffic Node 64 ~ 128 Kbps 70 ms 10159 MMMMMMMMMMMMMAMMAMMMMMMAMMMMMMMMMM much better, ★ ★ ★ denotes good, ★ ★ ★ ★ denotes very good, and ★ ★ ★ ★ denotes excellent. 11 pairs cross traffic with 500 Kbps sending rate 12454 MMAAMAMMMMMAAMAMAMAMAMAMAMAMAMAMAMAMA 16728 MMMMMMMMMMMMMMMMMMMMMMAMMTTTTTTTTTTTT Multimedia Networking and Systems Lab Institute of Information Science, Academia Sinica http://mmnet.iis.sinica.edu.tw
