Report
Share
Download to read offline
Recommended
More Related Content
What's hot
What's hot (20)
Cyber Security Awareness (Reduce Personal & Business Risk)

Cyber Security Awareness (Reduce Personal & Business Risk)
3 data leak possibilities that are easy to overlook

3 data leak possibilities that are easy to overlook
Similar to Public WiFi Hot Spots
Similar to Public WiFi Hot Spots (20)
mobile or cellphones attacked by viruses,phishing,swishing-1.pptx

mobile or cellphones attacked by viruses,phishing,swishing-1.pptx
InfraGard Albany Member Alliance Monthly Security Tips

InfraGard Albany Member Alliance Monthly Security Tips
Securing Mobile & Online Identity in the Cyber World

Securing Mobile & Online Identity in the Cyber World
Frontier Secure: Handout for small business leaders on "How to be Secure" 

Frontier Secure: Handout for small business leaders on "How to be Secure"
Online Safety, Security, Ethics and Etiquette Standards.pptx

Online Safety, Security, Ethics and Etiquette Standards.pptx
More from Centextech
More from Centextech (20)
Security at the Core: Unraveling Secure by Design Principles

Security at the Core: Unraveling Secure by Design Principles
Cybersecurity Incident Management for Small and Medium-sized Businesses

Cybersecurity Incident Management for Small and Medium-sized Businesses
Mobile Application Security: Safeguarding Apps in the Digital Age

Mobile Application Security: Safeguarding Apps in the Digital Age
Incident Management for Ransomware Attacks Best Practices for Response and Re...

Incident Management for Ransomware Attacks Best Practices for Response and Re...
10 Essentials Of Effective Cyber Security Strategy

10 Essentials Of Effective Cyber Security Strategy
Recently uploaded
Rohini Sector 6 Call Girls Delhi 9999965857 @Sabina Saikh No Advance

Rohini Sector 6 Call Girls Delhi 9999965857 @Sabina Saikh No AdvanceCall Girls In Delhi Whatsup 9873940964 Enjoy Unlimited Pleasure
Rohini Sector 22 Call Girls Delhi 9999965857 @Sabina Saikh No Advance

Rohini Sector 22 Call Girls Delhi 9999965857 @Sabina Saikh No AdvanceCall Girls In Delhi Whatsup 9873940964 Enjoy Unlimited Pleasure
Recently uploaded (20)
Rohini Sector 6 Call Girls Delhi 9999965857 @Sabina Saikh No Advance

Rohini Sector 6 Call Girls Delhi 9999965857 @Sabina Saikh No Advance
SEO Growth Program-Digital optimization Specialist

SEO Growth Program-Digital optimization Specialist
Rohini Sector 22 Call Girls Delhi 9999965857 @Sabina Saikh No Advance

Rohini Sector 22 Call Girls Delhi 9999965857 @Sabina Saikh No Advance
Call Girls in Mayur Vihar ✔️ 9711199171 ✔️ Delhi ✔️ Enjoy Call Girls With Our...

Call Girls in Mayur Vihar ✔️ 9711199171 ✔️ Delhi ✔️ Enjoy Call Girls With Our...
✂️ 👅 Independent Andheri Escorts With Room Vashi Call Girls 💃 9004004663

✂️ 👅 Independent Andheri Escorts With Room Vashi Call Girls 💃 9004004663
AWS Community DAY Albertini-Ellan Cloud Security (1).pptx

AWS Community DAY Albertini-Ellan Cloud Security (1).pptx
Call Girls In Sukhdev Vihar Delhi 💯Call Us 🔝8264348440🔝

Call Girls In Sukhdev Vihar Delhi 💯Call Us 🔝8264348440🔝
On Starlink, presented by Geoff Huston at NZNOG 2024

On Starlink, presented by Geoff Huston at NZNOG 2024
Delhi Call Girls Rohini 9711199171 ☎✔👌✔ Whatsapp Hard And Sexy Vip Call

Delhi Call Girls Rohini 9711199171 ☎✔👌✔ Whatsapp Hard And Sexy Vip Call
Enjoy Night⚡Call Girls Dlf City Phase 3 Gurgaon >༒8448380779 Escort Service

Enjoy Night⚡Call Girls Dlf City Phase 3 Gurgaon >༒8448380779 Escort Service
Russian Call girls in Dubai +971563133746 Dubai Call girls

Russian Call girls in Dubai +971563133746 Dubai Call girls
All Time Service Available Call Girls Mg Road 👌 ⏭️ 6378878445

All Time Service Available Call Girls Mg Road 👌 ⏭️ 6378878445
'Future Evolution of the Internet' delivered by Geoff Huston at Everything Op...

'Future Evolution of the Internet' delivered by Geoff Huston at Everything Op...
10.pdfMature Call girls in Dubai +971563133746 Dubai Call girls

10.pdfMature Call girls in Dubai +971563133746 Dubai Call girls
Call Girls Service Chandigarh Lucky ❤️ 7710465962 Independent Call Girls In C...

Call Girls Service Chandigarh Lucky ❤️ 7710465962 Independent Call Girls In C...
DDoS In Oceania and the Pacific, presented by Dave Phelan at NZNOG 2024

DDoS In Oceania and the Pacific, presented by Dave Phelan at NZNOG 2024
Pune Airport ( Call Girls ) Pune 6297143586 Hot Model With Sexy Bhabi Ready...

Pune Airport ( Call Girls ) Pune 6297143586 Hot Model With Sexy Bhabi Ready...
Moving Beyond Twitter/X and Facebook - Social Media for local news providers

Moving Beyond Twitter/X and Facebook - Social Media for local news providers
Challengers I Told Ya ShirtChallengers I Told Ya Shirt

Challengers I Told Ya ShirtChallengers I Told Ya Shirt
Call Now ☎ 8264348440 !! Call Girls in Shahpur Jat Escort Service Delhi N.C.R.

Call Now ☎ 8264348440 !! Call Girls in Shahpur Jat Escort Service Delhi N.C.R.
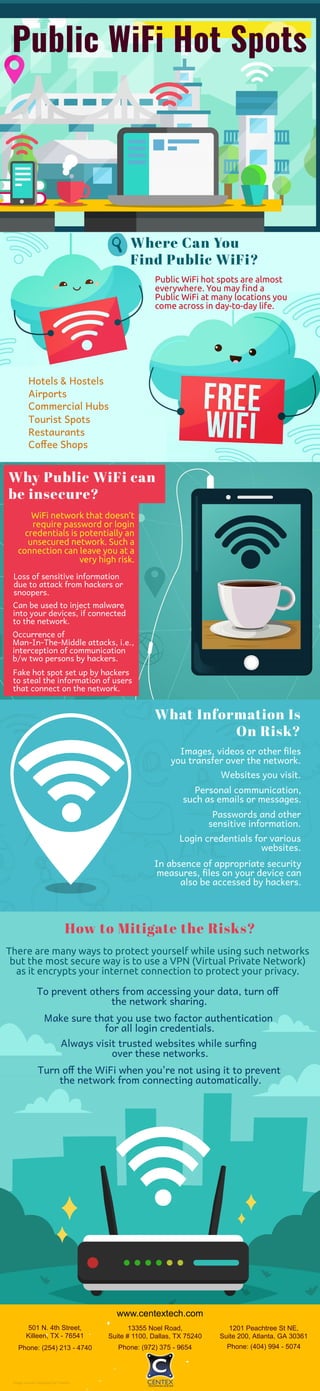
Public WiFi Hot Spots
- 1. Public WiFi Hot Spots Where Can You Find Public WiFi? Public WiFi hot spots are almost everywhere. You may find a Public WiFi at many locations you come across in day-to-day life. Hotels & Hostels Airports Commercial Hubs Tourist Spots Restaurants Co ee Shops WiFi network that doesn’t require password or login credentials is potentially an unsecured network. Such a connection can leave you at a very high risk. Loss of sensitive information due to attack from hackers or snoopers. Why Public WiFi can be insecure? Can be used to inject malware into your devices, if connected to the network. Occurrence of Man-In-The-Middle attacks, i.e., interception of communication b/w two persons by hackers. Fake hot spot set up by hackers to steal the information of users that connect on the network. What Information Is On Risk? Websites you visit. Personal communication, such as emails or messages. Passwords and other sensitive information. In absence of appropriate security measures, les on your device can also be accessed by hackers. Login credentials for various websites. Images, videos or other les you transfer over the network. There are many ways to protect yourself while using such networks but the most secure way is to use a VPN (Virtual Private Network) as it encrypts your internet connection to protect your privacy. How to Mitigate the Risks? To prevent others from accessing your data, turn o the network sharing. Make sure that you use two factor authentication for all login credentials. Always visit trusted websites while sur ng over these networks. Turn o the WiFi when you're not using it to prevent the network from connecting automatically. www.centextech.com 501 N. 4th Street, Killeen, TX - 76541 Phone: (254) 213 - 4740 13355 Noel Road, Suite # 1100, Dallas, TX 75240 Phone: (972) 375 - 9654 1201 Peachtree St NE, Suite 200, Atlanta, GA 30361 Phone: (404) 994 - 5074 Image source: Designed by Freepik