Policy InformationPolicy Name __________________________ ID _.docx
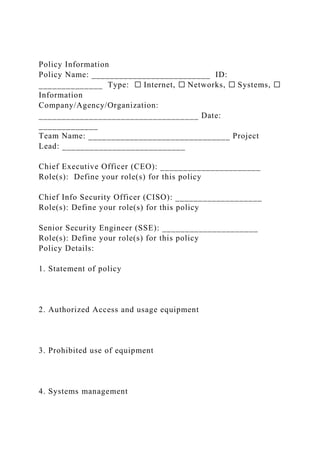
Policy Information Policy Name: __________________________ ID: ______________ Type: ☐ Internet, ☐ Networks, ☐ Systems, ☐ Information Company/Agency/Organization: ___________________________________ Date: _____________ Team Name: _______________________________ Project Lead: ___________________________ Chief Executive Officer (CEO): ______________________ Role(s): Define your role(s) for this policy Chief Info Security Officer (CISO): ___________________ Role(s): Define your role(s) for this policy Senior Security Engineer (SSE): _____________________ Role(s): Define your role(s) for this policy Policy Details: 1. Statement of policy 2. Authorized Access and usage equipment 3. Prohibited use of equipment 4. Systems management 5. Violations of policy 6. Policy review and modification 7. Limitations of liability Table 4-2Components of an ISSP11 (Source: Whitman, Townsend, and Aalberts, Communications of the ACM) Components of an ISSP 1.Statement of policy a.Scope and applicability b.Definition of technology addressed c.Responsibilities 2.Authorized access and usage of equipment a.User access b.Fair and responsible use c.Protection of privacy 3.Prohibited use of equipment a.Disruptive use or misuse b.Criminal use c.Offensive or harassing materials d.Copyrighted, licensed, or other intellectual property e.Other restrictions 4.Systems management a.Management of stored materials b.Employee monitoring c.Virus protection d.Physical security e.Encryption 5.Violations of policy a.Procedures for reporting violations b.Penalties for violations 6.Policy review and modification a.Scheduled review of policy procedures for modification b.Legal disclaimers 7.Limitations of liability a.Statements of liability b.Other disclaimers as needed Figure 1 Shperes of Security Table 4-4ISO 27000 Series Current and Planned Standards17 ISO 27000 Series Standard Title or Topic Comment 27000 Series Overview and Terminology Defines terminology and vocabulary for the standard series 27001:2013 Information Security Management System Specification Drawn from BS7799:2 27002:2013 Code of Practice for Information Security Management Renamed from ISO/IEC 17799; drawn from BS7799:1 27003:2010 Information Security Management Systems Implementation Guidelines Guidelines for project planning requirements for implementing an ISMS 27004:2009 Information Security Measurements and Metrics Performance measures and metrics for information security management decisions 27005:2011 ISMS Risk Management Supports 27001, but doesn't recommend any specific risk method 27006:2011 Requirements for Bodies Providing Audit and Certification of an ISMS Largely intended to support the accreditation of certification bodies providing ISMS certification 27007:2011 Guideline for ISMS Auditing Focuses on management systems 27008:2011 Guideline for Information Security Auditing Focuses on security controls 27009:Draft Sector-specific application of ISO/IEC 27001 Guidance for th ...
Recommended
Recommended
More Related Content
Similar to Policy InformationPolicy Name __________________________ ID _.docx
Similar to Policy InformationPolicy Name __________________________ ID _.docx (20)
More from stilliegeorgiana
More from stilliegeorgiana (20)
Recently uploaded
Recently uploaded (20)
Policy InformationPolicy Name __________________________ ID _.docx
- 1. Policy Information Policy Name: __________________________ ID: ______________ Type: ☐ Internet, ☐ Networks, ☐ Systems, ☐ Information Company/Agency/Organization: ___________________________________ Date: _____________ Team Name: _______________________________ Project Lead: ___________________________ Chief Executive Officer (CEO): ______________________ Role(s): Define your role(s) for this policy Chief Info Security Officer (CISO): ___________________ Role(s): Define your role(s) for this policy Senior Security Engineer (SSE): _____________________ Role(s): Define your role(s) for this policy Policy Details: 1. Statement of policy 2. Authorized Access and usage equipment 3. Prohibited use of equipment 4. Systems management
- 2. 5. Violations of policy 6. Policy review and modification 7. Limitations of liability Table 4-2Components of an ISSP11 (Source: Whitman, Townsend, and Aalberts, Communications of the ACM) Components of an ISSP 1.Statement of policy a.Scope and applicability b.Definition of technology addressed c.Responsibilities 2.Authorized access and usage of equipment a.User access b.Fair and responsible use c.Protection of privacy 3.Prohibited use of equipment a.Disruptive use or misuse b.Criminal use c.Offensive or harassing materials d.Copyrighted, licensed, or other intellectual property e.Other restrictions 4.Systems management a.Management of stored materials b.Employee monitoring c.Virus protection d.Physical security e.Encryption 5.Violations of policy
- 3. a.Procedures for reporting violations b.Penalties for violations 6.Policy review and modification a.Scheduled review of policy procedures for modification b.Legal disclaimers 7.Limitations of liability a.Statements of liability b.Other disclaimers as needed Figure 1 Shperes of Security Table 4-4ISO 27000 Series Current and Planned Standards17 ISO 27000 Series Standard Title or Topic Comment 27000 Series Overview and Terminology Defines terminology and vocabulary for the standard series 27001:2013 Information Security Management System Specification Drawn from BS7799:2 27002:2013 Code of Practice for Information Security Management Renamed from ISO/IEC 17799; drawn from BS7799:1 27003:2010 Information Security Management Systems Implementation Guidelines Guidelines for project planning requirements for implementing an ISMS 27004:2009 Information Security Measurements and Metrics Performance measures and metrics for information security management decisions 27005:2011 ISMS Risk Management
- 4. Supports 27001, but doesn't recommend any specific risk method 27006:2011 Requirements for Bodies Providing Audit and Certification of an ISMS Largely intended to support the accreditation of certification bodies providing ISMS certification 27007:2011 Guideline for ISMS Auditing Focuses on management systems 27008:2011 Guideline for Information Security Auditing Focuses on security controls 27009:Draft Sector-specific application of ISO/IEC 27001 Guidance for those who develop “sector-specific” standards based on or relating to ISO/IEC 27001 27010:2015 Information security management for inter-sector and inter- organizational communications Guidance for inter-sector and inter-organizational communications 27011:2008 Information security management guidelines for telecommunications organizations Guidance in the application of ISO/IEC 27002 in telecommunications organizations 27013:2015 Guidance on the integrated implementation of ISO/IEC 27001 and ISO/IEC 20000-1 Support for implementing an integrated dual management system 27014:2013 Governance of information security ISO's approach to security governance—guidance on evaluating, directing, monitoring, and communicating information security
- 5. 27015:2012 Information Security Management Guidelines for Financial Services Guidance for financial services organizations 27016:2014 Information security management — Organizational economics Guidance for understanding the economical consequences of information protection decisions 27017:2015 Code of practice for information security controls based on ISO/IEC 27002 for cloud services Guidance for practice in applying 27002 standards to cloud services 27018:2014 Code of practice for protection of personally identifiable information (PII) in public clouds acting as PII processors Guidance for practice in applying 27002 standards to PII processed in cloud services 27019:2013 Information security management guidelines for process control systems specific to the energy industry Focused on helping organizations in the energy industry implement ISO standards 27023:2015 Mapping the revised editions of ISO/IEC 27001 and ISO/IEC 27002 Guidance on the revised editions of ISO/IEC 27001 and ISO/IEC 27002 27031:2011 Guidelines for information and communication technology readiness for business continuity Application of ISO/IEC 27002 to information and communication technology readiness for business continuity 27032:2012 Guidelines for cybersecurity Guidance to achieve cybersecurity
- 6. 27033-1:2015 Network security — Part 1: Overview and concepts Overview and concepts of network security 27033-2:2012 Network security — Part 2: Design and implementation of network security Guidance for the design and implementation of network security 27033-3:2010 Network security — Part 3: Reference networking scenarios — Threats, design techniques, and control issues Networking scenarios 27033-4:2014 Network security — Part 4: Securing communications between networks using security gateways Securing communications between networks using security gateways 27033-5:2013 Network security — Part 5: Securing communications across networks using virtual private networks (VPNs) Securing communications across networks using VPNs 27034-1:2011 Application security — Part 1: Overview and concepts Overview and concepts of application security 27034-2:2015 Application security — Part 2: Organization normative framework for application security A framework for application security 27035:2011 Information security incident management Guidance for information security incident management 27036-1:2014 Information security for supplier relationships — Part 1: Overview and concepts Overview of information security for supplier relationships 27036-2:2014 Information security for supplier relationships — Part 2:
- 7. Requirements Requirements for information security for supplier relationships 27036-3:2013 Information security for supplier relationships — Part 3: Guidelines for information and communication technology supply chain security Guidelines for information security for supplier relationships 27038:2014 Specification for digital redaction Digital redaction specification 27039:2015 Selection, deployment, and operations of intrusion detection systems (IDPSs) Guidance for IDPS selection, deployment, and operations 27040:2015 Storage security Guidance on storage security 27041:2015 Guidance on assuring suitability and adequacy of incident investigative methods Guidance on incident investigative methods 27042:2015 Guidelines for the analysis and interpretation of digital evidence Guidelines for the analysis and interpretation of digital evidence 27043:2015 Incident investigation principles and processes Incident investigation principles and processes 27799:2008 Health informatics-Information security management in health using ISO/IEC 27002 Provides guidance to health organizations and other holders of personal health information on how to protect such information via implementation of ISO/IEC 27002 Identified Future 27000 Series Standards (In Draft)
- 8. 27033-6 Network security — Part 6: Securing wireless IP network access 27034-3 Application security — Part 3: Application security management process 27034-5 Application security — Part 5: Protocols and application security controls data structure — XML schemas 27034-7 Application security — Part 7: Application security assurance prediction 27035-2 Information security incident management — Part 2: Guidelines to plan and prepare for incident response 27035-3 Information security incident management — Part 3: Guidelines for CSIRT operations Page 2 of 2