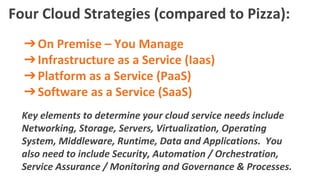
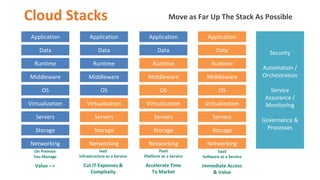
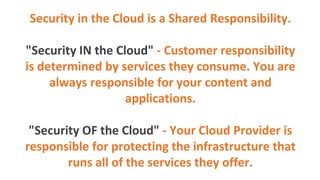
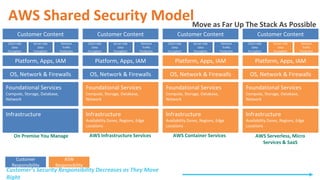
The document uses pizza as an analogy to explain different cloud service models: on-premise, IaaS, PaaS, and SaaS, highlighting the responsibilities of users across these models. It also discusses cloud security through the lens of layers, illustrating the shared responsibility between the customer and provider in protecting applications and data. The key takeaway is that as one moves up the cloud stack, the complexity and responsibility decrease, paralleling the experience of ordering pizza versus making it from scratch.