Pembagian slide struktur data
•Download as DOCX, PDF•
0 likes•107 views
Report
Share
Report
Share
Recommended
948 p02 

Dokumen tersebut membahas tentang pengumpulan data sebagai prosedur sistematik untuk memperoleh data yang diperlukan, termasuk metode pengumpulan data seperti observasi, wawancara, angket, dan studi kepustakaan."
948 p01 

Pertemuan 1 memberikan penjelasan tentang pengertian penelitian, jenis-jenis penelitian, sifat penelitian kualitatif dan kuantitatif, serta tahapan metode ilmiah. Materi pokok mata kuliah ini meliputi dasar-dasar penelitian, pengumpulan data, sampel random, uji validitas dan reliabilitas, penulisan tugas akhir dan artikel ilmiah, serta PKM.
948 p03 

`
Teknik sampling acak sederhana dan pembuatan skala dijelaskan. Teknik sampling acak memilih sampel secara acak dari populasi untuk memperkirakan rata-rata dan variansi populasi. Berbagai jenis skala dijelaskan seperti skala sosial, penilaian, Likert, dan Guttman untuk mengubah atribut kualitatif menjadi kuantitatif.
948 p06

Ringkasan dokumen tersebut adalah:
Dokumen tersebut membahas tentang 7 jenis Program Kreativitas Mahasiswa (PKM) beserta karakteristik dan persyaratan administrasinya. Jenis-jenis PKM tersebut adalah PKM Penelitian, PKM Kewirausahaan, PKM Pengabdian kepada Masyarakat, PKM Penerapan Teknologi, PKM Karsa Cipta, PKM Artikel Ilmiah, dan PKM Gagasan Tertulis. Dok
Recommended
948 p02 

Dokumen tersebut membahas tentang pengumpulan data sebagai prosedur sistematik untuk memperoleh data yang diperlukan, termasuk metode pengumpulan data seperti observasi, wawancara, angket, dan studi kepustakaan."
948 p01 

Pertemuan 1 memberikan penjelasan tentang pengertian penelitian, jenis-jenis penelitian, sifat penelitian kualitatif dan kuantitatif, serta tahapan metode ilmiah. Materi pokok mata kuliah ini meliputi dasar-dasar penelitian, pengumpulan data, sampel random, uji validitas dan reliabilitas, penulisan tugas akhir dan artikel ilmiah, serta PKM.
948 p03 

`
Teknik sampling acak sederhana dan pembuatan skala dijelaskan. Teknik sampling acak memilih sampel secara acak dari populasi untuk memperkirakan rata-rata dan variansi populasi. Berbagai jenis skala dijelaskan seperti skala sosial, penilaian, Likert, dan Guttman untuk mengubah atribut kualitatif menjadi kuantitatif.
948 p06

Ringkasan dokumen tersebut adalah:
Dokumen tersebut membahas tentang 7 jenis Program Kreativitas Mahasiswa (PKM) beserta karakteristik dan persyaratan administrasinya. Jenis-jenis PKM tersebut adalah PKM Penelitian, PKM Kewirausahaan, PKM Pengabdian kepada Masyarakat, PKM Penerapan Teknologi, PKM Karsa Cipta, PKM Artikel Ilmiah, dan PKM Gagasan Tertulis. Dok
948 p04

Dokumen tersebut membahas tentang uji validitas dan reliabilitas suatu kuesioner. Secara singkat, dibahas mengenai langkah-langkah pengujian validitas butir pertanyaan menggunakan SPSS dengan melihat nilai korelasi butir-total yang dikoreksi, serta pengujian reliabilitas konstruk dengan menggunakan nilai Cronbach's Alpha. Contoh output SPSS juga ditampilkan untuk mendemonstrasikan hasil analisis validitas dan reliabilitas terhadap but
948 p03

`
Teknik sampling acak sederhana dan pembuatan skala dijelaskan. Teknik sampling acak memilih sampel secara acak dimana setiap anggota populasi memiliki kesempatan yang sama untuk terpilih. Berbagai jenis skala dijelaskan seperti skala sosial, penilaian, peringkat, Likert dan Guttman untuk mengubah atribut kualitatif menjadi kuantitatif.
948 ltm metode penelitian - 3 sks

Dokumen tersebut berisi lembar tugas mahasiswa (LTM) mata kuliah Metode Penelitian untuk program studi Teknik Komputer di AMIK BSI. LTM terdiri dari 16 pertanyaan yang membahas berbagai topik terkait metode penelitian seperti penelitian kualitatif vs kuantitatif, teknik sampling, validitas dan reliabilitas, serta penyusunan proposal skripsi dan artikel ilmiah.
Kuiz dasar manajemen bisnis pert 9 14

Quiz Dasar Manajemen Bisnis Pertanyaan 9-14 membahas tentang faktor-faktor yang mempengaruhi sikap individu, karakteristik kepribadian, pengertian organisasi, penentuan jumlah bawahan, variabel lingkungan yang mempengaruhi perilaku, rentang manajemen, dan jenis komunikasi organisasi.
Silabus bahasa inggris ii

This document outlines the syllabus for a Diploma III Program course in English for Computers. The course covers topics related to computers, software, hardware, networks, security, and the internet over 16 meetings. It includes introductory topics like the components of a computer as well as more advanced topics such as cryptography, steganography, and website design. Students will complete quizzes, exercises and two exams to assess their understanding of the key concepts from each meeting's material.
Silabus bahasa inggris ii ok

This document outlines the syllabus for a Diploma III Program course in English for Computers. The course covers topics related to computers, software, hardware, networks, security, and the internet over 16 meetings. It includes introductory topics like the components of a computer as well as more advanced topics such as cryptography, steganography, and website design. Students will complete quizzes, exercises and two exams to assess their understanding of the key concepts from each meeting's material.
Meeting 14 ok

A website is a collection of web pages located on the World Wide Web that is owned by an individual, company, or organization. Each website has a home page, which is the main page users see first when entering the site. Web pages are written in HTML code and contain text and links. A search engine is a program that searches documents for specified keywords and returns a list of matching documents. Search engines like Google use crawlers to fetch documents which are then indexed by keywords to return relevant results when users search.
Meeting 12 ok

The document discusses the basics of the internet including:
- The internet is a worldwide network of millions of connected computers that share and exchange data. It allows for various services like the world wide web, file transfers, email, remote access, and discussions.
- The world wide web uses hyperlinks to connect documents and resources through uniform resource identifiers and the HTTP protocol. Search engines help users find information on the web through keyword searches.
- Each computer on the internet has a unique IP address for identification, but domain name service addresses like websites are easier for humans to use.
- Internet usage has grown tremendously, reaching over 1 billion users by 2010 who perform activities daily like Google searches, reading blogs
Meeting 10 ok

Steganography is the art and science of hiding secret messages in such a way that no one apart from the sender and recipient is aware of the message's existence. It works by concealing a message within another innocent-looking object like a picture, article, or document. Historically, messages were hidden in wax tablets or by tattooing a slave's head and letting their hair regrow. Modern steganography uses digital files and techniques like embedding one document into another to conceal secret communications.
Meeting 6 ok

Hardware is the physical equipment of a computer system and can be divided into input and output devices. Input devices such as keyboards, mice, and microphones are used to enter data into the system, while output devices like printers, speakers, and monitors are used to display or present the output from the computer. Common input devices include keyboards for text, mice and trackballs for pointing, joysticks for gaming, scanners for images, and webcams for video input. Common output devices are printers for hardcopy images and text, and speakers and headsets for audio output.
Meeting 5 ok

Malicious software, or malware, includes viruses, worms, and Trojan horses. Viruses infect other files by overwriting, appending to, or prepending code. Worms replicate themselves through networks and emails without infecting files. Trojan horses disguise harmful programs as legitimate ones to damage systems or steal information. Antivirus software can clean systems of malware infections.
Meeting 4 ok

A programming language is a language used to communicate instructions to a computer. There are many programming languages including Pascal, C++, Visual Basic, Visual Foxpro, and Java. A LAN connects individual PCs within an organization while a WAN allows connection over a wider area. Networks allow resources like printers and scanners to be shared. Computers are used in daily life for activities like banking, IDs, shopping, working from home, and accessing the internet. Viruses hide on disks and infect computers when the disk is accessed, then spread from computer to computer via infected disks or networks. Software copyright issues include awareness of freeware, shareware, and software found online as well as site licenses.
Meeting 3 ok

Software refers to programs and data stored in a computer that do not have a physical form. An operating system is a special type of software that loads automatically and acts as an interface between the user and hardware. Common operating systems include Windows, Linux, and Mac OS. Application software are programs used by users once the operating system loads, such as word processors, spreadsheets, and databases. Examples of application software include Microsoft Office, presentation tools, and multimedia applications.
Silabus chacarter building d3 kbk

Mata kuliah Character Building membahas pengenalan, penerimaan, dan pengembangan diri sendiri, sikap sosial, lingkungan sosial, dan interaksi sosial. Mahasiswa dibagi kelompok untuk membuat presentasi dan laporan mengenai topik-topik tersebut, serta mengikuti ujian tengah dan akhir semester.
Pertemuan 5 cb

Dokumen tersebut membahas tentang lingkungan sosial yang mencakup keluarga dan kelompok dekat, dengan menjelaskan berbagai bentuk perkawinan seperti monogami, poligami, eksogami, endogami, dan lainnya; serta unsur-unsur kebudayaan menurut Kluckhohn dan pentingnya nilai budaya dalam masyarakat.
More Related Content
More from Bina Sarana Informatika
948 p04

Dokumen tersebut membahas tentang uji validitas dan reliabilitas suatu kuesioner. Secara singkat, dibahas mengenai langkah-langkah pengujian validitas butir pertanyaan menggunakan SPSS dengan melihat nilai korelasi butir-total yang dikoreksi, serta pengujian reliabilitas konstruk dengan menggunakan nilai Cronbach's Alpha. Contoh output SPSS juga ditampilkan untuk mendemonstrasikan hasil analisis validitas dan reliabilitas terhadap but
948 p03

`
Teknik sampling acak sederhana dan pembuatan skala dijelaskan. Teknik sampling acak memilih sampel secara acak dimana setiap anggota populasi memiliki kesempatan yang sama untuk terpilih. Berbagai jenis skala dijelaskan seperti skala sosial, penilaian, peringkat, Likert dan Guttman untuk mengubah atribut kualitatif menjadi kuantitatif.
948 ltm metode penelitian - 3 sks

Dokumen tersebut berisi lembar tugas mahasiswa (LTM) mata kuliah Metode Penelitian untuk program studi Teknik Komputer di AMIK BSI. LTM terdiri dari 16 pertanyaan yang membahas berbagai topik terkait metode penelitian seperti penelitian kualitatif vs kuantitatif, teknik sampling, validitas dan reliabilitas, serta penyusunan proposal skripsi dan artikel ilmiah.
Kuiz dasar manajemen bisnis pert 9 14

Quiz Dasar Manajemen Bisnis Pertanyaan 9-14 membahas tentang faktor-faktor yang mempengaruhi sikap individu, karakteristik kepribadian, pengertian organisasi, penentuan jumlah bawahan, variabel lingkungan yang mempengaruhi perilaku, rentang manajemen, dan jenis komunikasi organisasi.
Silabus bahasa inggris ii

This document outlines the syllabus for a Diploma III Program course in English for Computers. The course covers topics related to computers, software, hardware, networks, security, and the internet over 16 meetings. It includes introductory topics like the components of a computer as well as more advanced topics such as cryptography, steganography, and website design. Students will complete quizzes, exercises and two exams to assess their understanding of the key concepts from each meeting's material.
Silabus bahasa inggris ii ok

This document outlines the syllabus for a Diploma III Program course in English for Computers. The course covers topics related to computers, software, hardware, networks, security, and the internet over 16 meetings. It includes introductory topics like the components of a computer as well as more advanced topics such as cryptography, steganography, and website design. Students will complete quizzes, exercises and two exams to assess their understanding of the key concepts from each meeting's material.
Meeting 14 ok

A website is a collection of web pages located on the World Wide Web that is owned by an individual, company, or organization. Each website has a home page, which is the main page users see first when entering the site. Web pages are written in HTML code and contain text and links. A search engine is a program that searches documents for specified keywords and returns a list of matching documents. Search engines like Google use crawlers to fetch documents which are then indexed by keywords to return relevant results when users search.
Meeting 12 ok

The document discusses the basics of the internet including:
- The internet is a worldwide network of millions of connected computers that share and exchange data. It allows for various services like the world wide web, file transfers, email, remote access, and discussions.
- The world wide web uses hyperlinks to connect documents and resources through uniform resource identifiers and the HTTP protocol. Search engines help users find information on the web through keyword searches.
- Each computer on the internet has a unique IP address for identification, but domain name service addresses like websites are easier for humans to use.
- Internet usage has grown tremendously, reaching over 1 billion users by 2010 who perform activities daily like Google searches, reading blogs
Meeting 10 ok

Steganography is the art and science of hiding secret messages in such a way that no one apart from the sender and recipient is aware of the message's existence. It works by concealing a message within another innocent-looking object like a picture, article, or document. Historically, messages were hidden in wax tablets or by tattooing a slave's head and letting their hair regrow. Modern steganography uses digital files and techniques like embedding one document into another to conceal secret communications.
Meeting 6 ok

Hardware is the physical equipment of a computer system and can be divided into input and output devices. Input devices such as keyboards, mice, and microphones are used to enter data into the system, while output devices like printers, speakers, and monitors are used to display or present the output from the computer. Common input devices include keyboards for text, mice and trackballs for pointing, joysticks for gaming, scanners for images, and webcams for video input. Common output devices are printers for hardcopy images and text, and speakers and headsets for audio output.
Meeting 5 ok

Malicious software, or malware, includes viruses, worms, and Trojan horses. Viruses infect other files by overwriting, appending to, or prepending code. Worms replicate themselves through networks and emails without infecting files. Trojan horses disguise harmful programs as legitimate ones to damage systems or steal information. Antivirus software can clean systems of malware infections.
Meeting 4 ok

A programming language is a language used to communicate instructions to a computer. There are many programming languages including Pascal, C++, Visual Basic, Visual Foxpro, and Java. A LAN connects individual PCs within an organization while a WAN allows connection over a wider area. Networks allow resources like printers and scanners to be shared. Computers are used in daily life for activities like banking, IDs, shopping, working from home, and accessing the internet. Viruses hide on disks and infect computers when the disk is accessed, then spread from computer to computer via infected disks or networks. Software copyright issues include awareness of freeware, shareware, and software found online as well as site licenses.
Meeting 3 ok

Software refers to programs and data stored in a computer that do not have a physical form. An operating system is a special type of software that loads automatically and acts as an interface between the user and hardware. Common operating systems include Windows, Linux, and Mac OS. Application software are programs used by users once the operating system loads, such as word processors, spreadsheets, and databases. Examples of application software include Microsoft Office, presentation tools, and multimedia applications.
Silabus chacarter building d3 kbk

Mata kuliah Character Building membahas pengenalan, penerimaan, dan pengembangan diri sendiri, sikap sosial, lingkungan sosial, dan interaksi sosial. Mahasiswa dibagi kelompok untuk membuat presentasi dan laporan mengenai topik-topik tersebut, serta mengikuti ujian tengah dan akhir semester.
Pertemuan 5 cb

Dokumen tersebut membahas tentang lingkungan sosial yang mencakup keluarga dan kelompok dekat, dengan menjelaskan berbagai bentuk perkawinan seperti monogami, poligami, eksogami, endogami, dan lainnya; serta unsur-unsur kebudayaan menurut Kluckhohn dan pentingnya nilai budaya dalam masyarakat.
More from Bina Sarana Informatika (20)
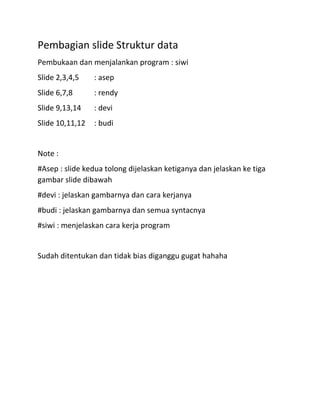
Pembagian slide struktur data
- 1. Pembagian slide Struktur data Pembukaan dan menjalankan program : siwi Slide 2,3,4,5 : asep Slide 6,7,8 : rendy Slide 9,13,14 : devi Slide 10,11,12 : budi Note : #Asep : slide kedua tolong dijelaskan ketiganya dan jelaskan ke tiga gambar slide dibawah #devi : jelaskan gambarnya dan cara kerjanya #budi : jelaskan gambarnya dan semua syntacnya #siwi : menjelaskan cara kerja program Sudah ditentukan dan tidak bias diganggu gugat hahaha
