Password recovery procedure for the cisco 2900 integrated services router
•Download as DOC, PDF•
2 likes•2,760 views
How to reco
Report
Share
Report
Share
Recommended
How to configure flexible netflow export on cisco routers

This document provides instructions for configuring Flexible NetFlow export on Cisco routers to monitor network traffic. It explains the three key components needed: records (templates for the data), exporters (instructions for sending data), and monitors (assigning the tasks). Records define the data fields, exporters define where to send the data, and monitors combine records and exporters to assign the monitoring and exporting tasks. The document provides detailed configuration examples and commands for setting up each component to enable Flexible NetFlow export and network monitoring.
How to configure Nagios in Fedora ?

Nagios is a powerful monitoring system that enables organizations to identify and resolve IT infrastructure problems before they affect critical business processes.
5. mrtg in nagios1 0

This document discusses the configuration of MRTG in Nagios to monitor bandwidth usage. It describes adding services to the services.cfg file to check bandwidth on various routers and hosts using the check_local_mrtgtraf command. An error of "Unable to open MRTG log file" occurred which was fixed by adding the "-F $LOGFILE$" option to the check_local_mrtgtraf command definition in commands.cfg.
BGP Protocol Makes the Internet Work

This document provides an overview of the Border Gateway Protocol (BGP) which is the routing protocol that allows routers on the internet to exchange information about reachable destinations. BGP focuses on security and scalability to allow internet service providers to exchange routing information in an open environment. The document discusses how BGP enables routers to share information about hundreds of thousands of IP address prefixes and examines approaches for troubleshooting connectivity issues with BGP.
Network protocols

Network protocols govern communications between computers by establishing rules for access methods, topologies, cabling, and data transfer speeds. Some common protocols described are Ethernet, Fast Ethernet, LocalTalk, Token Ring, FDDI, ATM, and Gigabit Ethernet, which vary in cable type, speed, and topology supported. Network diagramming software can be used to visually represent different network protocols.
Cisco switch selector layer2 or layer3

Cisco Catalyst Fixed Configuration Gigabit Ethernet Switch Family...Which one is the right one for you? Read more here...
Ordering guide for cisco isr g2

The document provides ordering guidelines for Cisco 3900 and 2900 series integrated services routers (ISRs). It includes part numbers and descriptions for base systems, memory upgrades, power supplies, fans, and other options. Memory, power, and fan configurations can be ordered with the routers or as spare parts. Ordering the correct power supply type is important for powering Ethernet ports or using external redundant power supplies.
Recommended
How to configure flexible netflow export on cisco routers

This document provides instructions for configuring Flexible NetFlow export on Cisco routers to monitor network traffic. It explains the three key components needed: records (templates for the data), exporters (instructions for sending data), and monitors (assigning the tasks). Records define the data fields, exporters define where to send the data, and monitors combine records and exporters to assign the monitoring and exporting tasks. The document provides detailed configuration examples and commands for setting up each component to enable Flexible NetFlow export and network monitoring.
How to configure Nagios in Fedora ?

Nagios is a powerful monitoring system that enables organizations to identify and resolve IT infrastructure problems before they affect critical business processes.
5. mrtg in nagios1 0

This document discusses the configuration of MRTG in Nagios to monitor bandwidth usage. It describes adding services to the services.cfg file to check bandwidth on various routers and hosts using the check_local_mrtgtraf command. An error of "Unable to open MRTG log file" occurred which was fixed by adding the "-F $LOGFILE$" option to the check_local_mrtgtraf command definition in commands.cfg.
BGP Protocol Makes the Internet Work

This document provides an overview of the Border Gateway Protocol (BGP) which is the routing protocol that allows routers on the internet to exchange information about reachable destinations. BGP focuses on security and scalability to allow internet service providers to exchange routing information in an open environment. The document discusses how BGP enables routers to share information about hundreds of thousands of IP address prefixes and examines approaches for troubleshooting connectivity issues with BGP.
Network protocols

Network protocols govern communications between computers by establishing rules for access methods, topologies, cabling, and data transfer speeds. Some common protocols described are Ethernet, Fast Ethernet, LocalTalk, Token Ring, FDDI, ATM, and Gigabit Ethernet, which vary in cable type, speed, and topology supported. Network diagramming software can be used to visually represent different network protocols.
Cisco switch selector layer2 or layer3

Cisco Catalyst Fixed Configuration Gigabit Ethernet Switch Family...Which one is the right one for you? Read more here...
Ordering guide for cisco isr g2

The document provides ordering guidelines for Cisco 3900 and 2900 series integrated services routers (ISRs). It includes part numbers and descriptions for base systems, memory upgrades, power supplies, fans, and other options. Memory, power, and fan configurations can be ordered with the routers or as spare parts. Ordering the correct power supply type is important for powering Ethernet ports or using external redundant power supplies.
The feature licenses available for main cisco asa 5500 models

The document discusses Cisco ASA 5500 series licensing features. It provides a table listing the license features available for various Cisco ASA 5500 models including the ASA 5505, 5510, 5520, 5540, and 5550. The tables describe the base licenses and optional additional licenses available for each model relating to firewall, VPN, and general device capabilities. Upgrading licenses is common to broaden the functions of Cisco ASA 5500 series devices.
Computer repair -_a_complete_illustrated_guide_to_pc_hardware

This document provides an overview of digital data representation in computers. It explains that computers can only process data that is represented digitally using binary digits (bits) of 1s and 0s. Bytes made up of 8 bits can represent different characters using codes like ASCII. Common file types indicate whether the file contains program code, text, images or other user data. The document guides the reader through these concepts over multiple pages with examples and explanations of binary numbers, bytes, ASCII codes and file formats.
Nagios nrpe

The NRPE addon allows Nagios to monitor local resources on remote Linux/Unix machines. It consists of the check_nrpe plugin on the monitoring machine and the NRPE daemon on remote machines. When Nagios needs to check a remote resource, the check_nrpe plugin contacts the NRPE daemon, which runs the plugin and returns results to Nagios via the check_nrpe plugin. NRPE allows monitoring of both direct local resources like CPU and memory usage as well as indirect checks of services reachable by the remote machine but not the monitoring host.
GTU PHP Project Training Guidelines

TOPS Technologies provides PHP training in Ahmedabad, for MCA Students PHP live project training as per GTU project guidelines. Get more info @ http://www.tops-int.com/, 903 Samedh Complex, Next to Associated Petrol Pump, CG Road, Ahmedabad 380009.
Plugging Network Security Holes Using NetFlow

NetFlow is a network monitoring technology that collects IP traffic data from network devices and analyzes it to provide visibility into network usage, problems, and threats. It helps plug security loopholes that exist in current network security systems like IDS/IPS. NetFlow data can be used to detect hacking attempts, stop zero-day malware infections, monitor internal network threats, and provide effective monitoring of high-speed and complex meshed networks. ManageEngine NetFlow Analyzer is a software solution that leverages NetFlow data to provide granular traffic reporting, conversation details, protocol distribution details, and anomaly detection capabilities.
Licensing on Cisco 2960, 3560X and 3750X...

This document discusses licensing for Cisco 2900/3500/3700 series switches. It describes the available feature sets (LAN Base, IP Base, IP Services), how to install and remove software licenses using the CLI, and license considerations for specific switch models including 2960/2960-S, 3560/3750, 3560E/3750E, and 3560X/3750X. It provides commands for checking licenses and guidelines for license installation on switch stacks.
Central management of network and call services

Make servers of web service, ftp service, VoIP video call service
Monitor & manage them centrally from a host in private connection or from remote connection.
The remote connection can be established through Secure Shell (SSH) connection which will connect to the servers through Router (or Routers).
How to Configure NetFlow v5 & v9 on Cisco Routers

This document provides instructions for configuring NetFlow versions 5 and 9 on Cisco routers to monitor network traffic. It explains that NetFlow collects IP traffic data, what versions 5 and 9 are, and how to configure each version on a router by specifying the collector server, export port, and interfaces. It also describes how to verify the NetFlow export and how tools like SolarWinds NetFlow Traffic Analyzer analyze exported data to provide network usage insights.
Line cards that are available for cisco catalyst 4500 series switches

The document describes several line cards available for Cisco Catalyst 4500 Series switches, including both 10 Gigabit Ethernet fiber line cards and 10/100/1000/multigigabit Ethernet line cards. The line cards provide various port configurations and speeds, and support features like PoE, multigigabit connectivity, and fiber encryption. They are suitable for applications in the enterprise, commercial, and service provider spaces.
Packet Tracer: SNMP, Netflow, Sys-log

This document summarizes a packet tracer lab where SNMP, Netflow, and syslog protocols were configured to monitor network traffic and generate log messages. Key aspects covered include:
- SNMP allows network monitoring through protocols that transmit data to SNMP servers. It was configured to send traffic logs and router status updates to a server.
- Netflow captures detailed traffic information like source/destination IP/port and protocol from router interfaces and exports it to a server for analysis. Random traffic was generated to test netflow collection.
- Syslog messages of different severity levels were configured to be sent from routers to a server for logging and troubleshooting purposes.
Netflow slides

This document discusses network flows and the NetFlow protocol. It begins by defining network flows as packets or frames that share common properties, such as source/destination IP and port. It then describes how NetFlow works by having network devices generate flows and export them to NetFlow collectors. The document outlines the NetFlow export packet format and different NetFlow versions, focusing on Cisco's implementation including versions 1, 5, 8 and 9. It also discusses how flows are generated, exported, collected and analyzed to monitor network traffic.
Cisco ip phone key expansion module setup

The Cisco IP Phone 8800 Key Expansion Module adds extra programmable buttons to the phone. The programmable buttons can be set up as phone speed-dial buttons, or phone feature buttons.
Cisco catalyst 9200 series platform spec, licenses, transition guide

The Cisco Catalyst 9200 Series switches are Cisco’s latest addition to the fixed enterprise switching access platform, and are built for security, resiliency, and programmability.
Cisco isr 900 series highlights, platform specs, licenses, transition guide

The 900 ISRs offer easy management and pro-visioning capabilities through Cisco Configuration Professional Express, Cisco DNA Center, and Cisco IOS Software, with full visibility into and control of network configurations and applications.
Hpe pro liant gen9 to gen10 server transition guide

The document summarizes the key features and benefits of HPE ProLiant Gen10 servers. It introduces the new Gen10 servers as offering high performance, security, and flexibility to run demanding applications and workloads. Specific Gen10 server models highlighted include the DL360 and DL380 for compute environments, the ML110 and ML350 for versatility, and the MicroServer for small offices. Key security capabilities of the HPE iLO 5 management tool are also outlined.
The new cisco isr 4461 faq

Cisco ISR 4461 is the newest number of Cisco 4000 Family Integrated Services Router. Now the Cisco 4000 Family contains the following platforms: the 4461 ISR, 4451 ISR, 4431 ISR, 4351 ISR, 4331 ISR, 4321 ISR and 4221 ISR.
New nexus 400 gigabit ethernet (400 g) switches

Cisco unveiled new 400 Gigabit Ethernet (400G) switches to help large cloud and data center customers meet modern network challenges of high scale and bandwidth. The new portfolio includes the Nexus 3400 fixed switches and Nexus 9000 switches for Cisco's ACI architecture. The 400G switches bring more than just increased speed, with flexible deployment options and support for features like superfast policy enforcement, packet visibility, smart buffering, and low latency traffic prioritization.
Tested cisco isr 1100 delivers the richest set of wi-fi features

Cisco ISR 1000 offers a branch-in-a-box solution with various types of uplink connectivity, multiple Power over Ethernet (PoE) and PoE+ capable Gigabit-Ethernet ports, and built-in Cisco Mobility Express Solution for WLAN access and SD-WAN capability.
Aruba campus and branch switching solution

Aruba’s modern, programmable switches easily integrate with our industry leading network management solutions, either cloud-based Aruba Central or on premise Aruba AirWave.
Cisco transceiver module for compatible catalyst switches

In this doc it shows you the main Cisco Transceiver Module for Compatible Catalyst Switches (including Cat3650, 3850, 4500E, 4500-X, 6500 and 6800)
Cisco ios on cisco catalyst switches

Cisco IOS XE opens a completely new paradigm in network configuration, operation, and monitoring through network automation. Cisco’s automation solution is open, standards-based, and extensible across the entire lifecycle of a network device. The various automation mechanisms are outlined here.
Cisco's wireless solutions deployment modes

Cisco's wireless solutions can be broadly classified into Standalone systems that operate Cisco Aironet Access Points individually and Controller-based systems that centrally manage multiple Cisco Aironet Access Points using a Cisco Wireless Controller. Multiple expansion modes are also supported in Controller-based systems.
More Related Content
Viewers also liked
The feature licenses available for main cisco asa 5500 models

The document discusses Cisco ASA 5500 series licensing features. It provides a table listing the license features available for various Cisco ASA 5500 models including the ASA 5505, 5510, 5520, 5540, and 5550. The tables describe the base licenses and optional additional licenses available for each model relating to firewall, VPN, and general device capabilities. Upgrading licenses is common to broaden the functions of Cisco ASA 5500 series devices.
Computer repair -_a_complete_illustrated_guide_to_pc_hardware

This document provides an overview of digital data representation in computers. It explains that computers can only process data that is represented digitally using binary digits (bits) of 1s and 0s. Bytes made up of 8 bits can represent different characters using codes like ASCII. Common file types indicate whether the file contains program code, text, images or other user data. The document guides the reader through these concepts over multiple pages with examples and explanations of binary numbers, bytes, ASCII codes and file formats.
Nagios nrpe

The NRPE addon allows Nagios to monitor local resources on remote Linux/Unix machines. It consists of the check_nrpe plugin on the monitoring machine and the NRPE daemon on remote machines. When Nagios needs to check a remote resource, the check_nrpe plugin contacts the NRPE daemon, which runs the plugin and returns results to Nagios via the check_nrpe plugin. NRPE allows monitoring of both direct local resources like CPU and memory usage as well as indirect checks of services reachable by the remote machine but not the monitoring host.
GTU PHP Project Training Guidelines

TOPS Technologies provides PHP training in Ahmedabad, for MCA Students PHP live project training as per GTU project guidelines. Get more info @ http://www.tops-int.com/, 903 Samedh Complex, Next to Associated Petrol Pump, CG Road, Ahmedabad 380009.
Plugging Network Security Holes Using NetFlow

NetFlow is a network monitoring technology that collects IP traffic data from network devices and analyzes it to provide visibility into network usage, problems, and threats. It helps plug security loopholes that exist in current network security systems like IDS/IPS. NetFlow data can be used to detect hacking attempts, stop zero-day malware infections, monitor internal network threats, and provide effective monitoring of high-speed and complex meshed networks. ManageEngine NetFlow Analyzer is a software solution that leverages NetFlow data to provide granular traffic reporting, conversation details, protocol distribution details, and anomaly detection capabilities.
Licensing on Cisco 2960, 3560X and 3750X...

This document discusses licensing for Cisco 2900/3500/3700 series switches. It describes the available feature sets (LAN Base, IP Base, IP Services), how to install and remove software licenses using the CLI, and license considerations for specific switch models including 2960/2960-S, 3560/3750, 3560E/3750E, and 3560X/3750X. It provides commands for checking licenses and guidelines for license installation on switch stacks.
Central management of network and call services

Make servers of web service, ftp service, VoIP video call service
Monitor & manage them centrally from a host in private connection or from remote connection.
The remote connection can be established through Secure Shell (SSH) connection which will connect to the servers through Router (or Routers).
How to Configure NetFlow v5 & v9 on Cisco Routers

This document provides instructions for configuring NetFlow versions 5 and 9 on Cisco routers to monitor network traffic. It explains that NetFlow collects IP traffic data, what versions 5 and 9 are, and how to configure each version on a router by specifying the collector server, export port, and interfaces. It also describes how to verify the NetFlow export and how tools like SolarWinds NetFlow Traffic Analyzer analyze exported data to provide network usage insights.
Line cards that are available for cisco catalyst 4500 series switches

The document describes several line cards available for Cisco Catalyst 4500 Series switches, including both 10 Gigabit Ethernet fiber line cards and 10/100/1000/multigigabit Ethernet line cards. The line cards provide various port configurations and speeds, and support features like PoE, multigigabit connectivity, and fiber encryption. They are suitable for applications in the enterprise, commercial, and service provider spaces.
Packet Tracer: SNMP, Netflow, Sys-log

This document summarizes a packet tracer lab where SNMP, Netflow, and syslog protocols were configured to monitor network traffic and generate log messages. Key aspects covered include:
- SNMP allows network monitoring through protocols that transmit data to SNMP servers. It was configured to send traffic logs and router status updates to a server.
- Netflow captures detailed traffic information like source/destination IP/port and protocol from router interfaces and exports it to a server for analysis. Random traffic was generated to test netflow collection.
- Syslog messages of different severity levels were configured to be sent from routers to a server for logging and troubleshooting purposes.
Netflow slides

This document discusses network flows and the NetFlow protocol. It begins by defining network flows as packets or frames that share common properties, such as source/destination IP and port. It then describes how NetFlow works by having network devices generate flows and export them to NetFlow collectors. The document outlines the NetFlow export packet format and different NetFlow versions, focusing on Cisco's implementation including versions 1, 5, 8 and 9. It also discusses how flows are generated, exported, collected and analyzed to monitor network traffic.
Viewers also liked (11)
The feature licenses available for main cisco asa 5500 models

The feature licenses available for main cisco asa 5500 models
Computer repair -_a_complete_illustrated_guide_to_pc_hardware

Computer repair -_a_complete_illustrated_guide_to_pc_hardware
Line cards that are available for cisco catalyst 4500 series switches

Line cards that are available for cisco catalyst 4500 series switches
More from IT Tech
Cisco ip phone key expansion module setup

The Cisco IP Phone 8800 Key Expansion Module adds extra programmable buttons to the phone. The programmable buttons can be set up as phone speed-dial buttons, or phone feature buttons.
Cisco catalyst 9200 series platform spec, licenses, transition guide

The Cisco Catalyst 9200 Series switches are Cisco’s latest addition to the fixed enterprise switching access platform, and are built for security, resiliency, and programmability.
Cisco isr 900 series highlights, platform specs, licenses, transition guide

The 900 ISRs offer easy management and pro-visioning capabilities through Cisco Configuration Professional Express, Cisco DNA Center, and Cisco IOS Software, with full visibility into and control of network configurations and applications.
Hpe pro liant gen9 to gen10 server transition guide

The document summarizes the key features and benefits of HPE ProLiant Gen10 servers. It introduces the new Gen10 servers as offering high performance, security, and flexibility to run demanding applications and workloads. Specific Gen10 server models highlighted include the DL360 and DL380 for compute environments, the ML110 and ML350 for versatility, and the MicroServer for small offices. Key security capabilities of the HPE iLO 5 management tool are also outlined.
The new cisco isr 4461 faq

Cisco ISR 4461 is the newest number of Cisco 4000 Family Integrated Services Router. Now the Cisco 4000 Family contains the following platforms: the 4461 ISR, 4451 ISR, 4431 ISR, 4351 ISR, 4331 ISR, 4321 ISR and 4221 ISR.
New nexus 400 gigabit ethernet (400 g) switches

Cisco unveiled new 400 Gigabit Ethernet (400G) switches to help large cloud and data center customers meet modern network challenges of high scale and bandwidth. The new portfolio includes the Nexus 3400 fixed switches and Nexus 9000 switches for Cisco's ACI architecture. The 400G switches bring more than just increased speed, with flexible deployment options and support for features like superfast policy enforcement, packet visibility, smart buffering, and low latency traffic prioritization.
Tested cisco isr 1100 delivers the richest set of wi-fi features

Cisco ISR 1000 offers a branch-in-a-box solution with various types of uplink connectivity, multiple Power over Ethernet (PoE) and PoE+ capable Gigabit-Ethernet ports, and built-in Cisco Mobility Express Solution for WLAN access and SD-WAN capability.
Aruba campus and branch switching solution

Aruba’s modern, programmable switches easily integrate with our industry leading network management solutions, either cloud-based Aruba Central or on premise Aruba AirWave.
Cisco transceiver module for compatible catalyst switches

In this doc it shows you the main Cisco Transceiver Module for Compatible Catalyst Switches (including Cat3650, 3850, 4500E, 4500-X, 6500 and 6800)
Cisco ios on cisco catalyst switches

Cisco IOS XE opens a completely new paradigm in network configuration, operation, and monitoring through network automation. Cisco’s automation solution is open, standards-based, and extensible across the entire lifecycle of a network device. The various automation mechanisms are outlined here.
Cisco's wireless solutions deployment modes

Cisco's wireless solutions can be broadly classified into Standalone systems that operate Cisco Aironet Access Points individually and Controller-based systems that centrally manage multiple Cisco Aironet Access Points using a Cisco Wireless Controller. Multiple expansion modes are also supported in Controller-based systems.
Competitive switching comparison cisco vs. hpe aruba vs. huawei vs. dell

Is it hard to choose the right switching solutions for your network? The following Competitive Switching Comparison may help you a lot. Check it.
Four reasons to consider the all in-one isr 1000

The document discusses the benefits of Cisco's 1000 Series Integrated Services Routers for small and medium-sized businesses. It provides an all-in-one solution for routing, switching, wireless access and security in a single device. Key benefits include advanced wired and wireless connectivity, enterprise-class security features, and the ability to evolve the software-defined WAN over time through centralized management and policies. The 1000 Series offers an affordable way for SMBs to securely connect endpoints, devices and networks.
The difference between yellow and white labeled ports on a nexus 2300 series fex

What is the Difference between Yellow and White Labeled Ports on a Nexus 2300 Series FEX?
The Cisco Nexus 2300 platform provides two types of ports: ports for end-host attachment (host interfaces) and uplink ports (fabric interfaces). Both yellow and white colored fabric interfaces can be used to provide connectivity to the upstream parent Cisco Nexus switch. There is no difference between yellow labeled and white labeled uplink ports.
Cisco transceiver modules for compatible cisco switches series

Check the following Cisco Transceiver Modules for Compatible Cisco Switches Series: 95–500, 2960-L, 2960-CX, 3560-CX, 2960-X, 3650 and 3850.
Guide to the new cisco firepower 2100 series

The Cisco Firepower 2100 series security appliance includes the Firepower 2110, 2120, 2130, and 2140.
More details and features...
892 f sfp configuration example

The Cisco 892F ISRs have an SFP port that supports auto-media-detection, auto-failover, and remote fault indication (RFI), as described in the IEEE 802.3ah specification.
Cisco nexus 7000 and nexus 7700

The Nexus 7000 Series switches form the core data center networking fabric. There are multiple chassis options from the Nexus 7000 and Nexus 7700 product family. The Nexus 7000 and the Nexus 7700 switches offer a comprehensive set of features for the data center network.
Cisco firepower ngips series migration options

Upgrade your customers to Cisco Firepower NGIPS today to help them protect their network, users, applications, and information assets.
Eol transceiver to replacement model

The document discusses the replacement of legacy Cisco transceiver modules that have reached end-of-sale and end-of-life with newer models. It provides a table listing the legacy modules and their replacement modules. It also discusses the target end-of-sale dates for legacy modules and features of the new modules, including backward compatibility and enhanced monitoring. Finally, it lists and describes the newest Cisco SFP transceiver modules.
More from IT Tech (20)
Cisco catalyst 9200 series platform spec, licenses, transition guide

Cisco catalyst 9200 series platform spec, licenses, transition guide
Cisco isr 900 series highlights, platform specs, licenses, transition guide

Cisco isr 900 series highlights, platform specs, licenses, transition guide
Hpe pro liant gen9 to gen10 server transition guide

Hpe pro liant gen9 to gen10 server transition guide
Tested cisco isr 1100 delivers the richest set of wi-fi features

Tested cisco isr 1100 delivers the richest set of wi-fi features
Cisco transceiver module for compatible catalyst switches

Cisco transceiver module for compatible catalyst switches
Competitive switching comparison cisco vs. hpe aruba vs. huawei vs. dell

Competitive switching comparison cisco vs. hpe aruba vs. huawei vs. dell
The difference between yellow and white labeled ports on a nexus 2300 series fex

The difference between yellow and white labeled ports on a nexus 2300 series fex
Cisco transceiver modules for compatible cisco switches series

Cisco transceiver modules for compatible cisco switches series
Recently uploaded
Main news related to the CCS TSI 2023 (2023/1695)

An English 🇬🇧 translation of a presentation to the speech I gave about the main changes brought by CCS TSI 2023 at the biggest Czech conference on Communications and signalling systems on Railways, which was held in Clarion Hotel Olomouc from 7th to 9th November 2023 (konferenceszt.cz). Attended by around 500 participants and 200 on-line followers.
The original Czech 🇨🇿 version of the presentation can be found here: https://www.slideshare.net/slideshow/hlavni-novinky-souvisejici-s-ccs-tsi-2023-2023-1695/269688092 .
The videorecording (in Czech) from the presentation is available here: https://youtu.be/WzjJWm4IyPk?si=SImb06tuXGb30BEH .
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Discover how MongoDB Atlas and vector search technology can revolutionize your application's search capabilities. This comprehensive presentation covers:
* What is Vector Search?
* Importance and benefits of vector search
* Practical use cases across various industries
* Step-by-step implementation guide
* Live demos with code snippets
* Enhancing LLM capabilities with vector search
* Best practices and optimization strategies
Perfect for developers, AI enthusiasts, and tech leaders. Learn how to leverage MongoDB Atlas to deliver highly relevant, context-aware search results, transforming your data retrieval process. Stay ahead in tech innovation and maximize the potential of your applications.
#MongoDB #VectorSearch #AI #SemanticSearch #TechInnovation #DataScience #LLM #MachineLearning #SearchTechnology
Energy Efficient Video Encoding for Cloud and Edge Computing Instances

Energy Efficient Video Encoding for Cloud and Edge Computing Instances
Letter and Document Automation for Bonterra Impact Management (fka Social Sol...

Sidekick Solutions uses Bonterra Impact Management (fka Social Solutions Apricot) and automation solutions to integrate data for business workflows.
We believe integration and automation are essential to user experience and the promise of efficient work through technology. Automation is the critical ingredient to realizing that full vision. We develop integration products and services for Bonterra Case Management software to support the deployment of automations for a variety of use cases.
This video focuses on automated letter generation for Bonterra Impact Management using Google Workspace or Microsoft 365.
Interested in deploying letter generation automations for Bonterra Impact Management? Contact us at sales@sidekicksolutionsllc.com to discuss next steps.
5th LF Energy Power Grid Model Meet-up Slides

5th Power Grid Model Meet-up
It is with great pleasure that we extend to you an invitation to the 5th Power Grid Model Meet-up, scheduled for 6th June 2024. This event will adopt a hybrid format, allowing participants to join us either through an online Mircosoft Teams session or in person at TU/e located at Den Dolech 2, Eindhoven, Netherlands. The meet-up will be hosted by Eindhoven University of Technology (TU/e), a research university specializing in engineering science & technology.
Power Grid Model
The global energy transition is placing new and unprecedented demands on Distribution System Operators (DSOs). Alongside upgrades to grid capacity, processes such as digitization, capacity optimization, and congestion management are becoming vital for delivering reliable services.
Power Grid Model is an open source project from Linux Foundation Energy and provides a calculation engine that is increasingly essential for DSOs. It offers a standards-based foundation enabling real-time power systems analysis, simulations of electrical power grids, and sophisticated what-if analysis. In addition, it enables in-depth studies and analysis of the electrical power grid’s behavior and performance. This comprehensive model incorporates essential factors such as power generation capacity, electrical losses, voltage levels, power flows, and system stability.
Power Grid Model is currently being applied in a wide variety of use cases, including grid planning, expansion, reliability, and congestion studies. It can also help in analyzing the impact of renewable energy integration, assessing the effects of disturbances or faults, and developing strategies for grid control and optimization.
What to expect
For the upcoming meetup we are organizing, we have an exciting lineup of activities planned:
-Insightful presentations covering two practical applications of the Power Grid Model.
-An update on the latest advancements in Power Grid -Model technology during the first and second quarters of 2024.
-An interactive brainstorming session to discuss and propose new feature requests.
-An opportunity to connect with fellow Power Grid Model enthusiasts and users.
Trusted Execution Environment for Decentralized Process Mining

Presentation of the paper "Trusted Execution Environment for Decentralized Process Mining" given during the CAiSE 2024 Conference in Cyprus on June 7, 2024.
leewayhertz.com-AI in predictive maintenance Use cases technologies benefits ...

Predictive maintenance is a proactive approach that anticipates equipment failures before they happen. At the forefront of this innovative strategy is Artificial Intelligence (AI), which brings unprecedented precision and efficiency. AI in predictive maintenance is transforming industries by reducing downtime, minimizing costs, and enhancing productivity.
Taking AI to the Next Level in Manufacturing.pdf

Read Taking AI to the Next Level in Manufacturing to gain insights on AI adoption in the manufacturing industry, such as:
1. How quickly AI is being implemented in manufacturing.
2. Which barriers stand in the way of AI adoption.
3. How data quality and governance form the backbone of AI.
4. Organizational processes and structures that may inhibit effective AI adoption.
6. Ideas and approaches to help build your organization's AI strategy.
HCL Notes and Domino License Cost Reduction in the World of DLAU

Webinar Recording: https://www.panagenda.com/webinars/hcl-notes-and-domino-license-cost-reduction-in-the-world-of-dlau/
The introduction of DLAU and the CCB & CCX licensing model caused quite a stir in the HCL community. As a Notes and Domino customer, you may have faced challenges with unexpected user counts and license costs. You probably have questions on how this new licensing approach works and how to benefit from it. Most importantly, you likely have budget constraints and want to save money where possible. Don’t worry, we can help with all of this!
We’ll show you how to fix common misconfigurations that cause higher-than-expected user counts, and how to identify accounts which you can deactivate to save money. There are also frequent patterns that can cause unnecessary cost, like using a person document instead of a mail-in for shared mailboxes. We’ll provide examples and solutions for those as well. And naturally we’ll explain the new licensing model.
Join HCL Ambassador Marc Thomas in this webinar with a special guest appearance from Franz Walder. It will give you the tools and know-how to stay on top of what is going on with Domino licensing. You will be able lower your cost through an optimized configuration and keep it low going forward.
These topics will be covered
- Reducing license cost by finding and fixing misconfigurations and superfluous accounts
- How do CCB and CCX licenses really work?
- Understanding the DLAU tool and how to best utilize it
- Tips for common problem areas, like team mailboxes, functional/test users, etc
- Practical examples and best practices to implement right away
HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU

Webinar Recording: https://www.panagenda.com/webinars/hcl-notes-und-domino-lizenzkostenreduzierung-in-der-welt-von-dlau/
DLAU und die Lizenzen nach dem CCB- und CCX-Modell sind für viele in der HCL-Community seit letztem Jahr ein heißes Thema. Als Notes- oder Domino-Kunde haben Sie vielleicht mit unerwartet hohen Benutzerzahlen und Lizenzgebühren zu kämpfen. Sie fragen sich vielleicht, wie diese neue Art der Lizenzierung funktioniert und welchen Nutzen sie Ihnen bringt. Vor allem wollen Sie sicherlich Ihr Budget einhalten und Kosten sparen, wo immer möglich. Das verstehen wir und wir möchten Ihnen dabei helfen!
Wir erklären Ihnen, wie Sie häufige Konfigurationsprobleme lösen können, die dazu führen können, dass mehr Benutzer gezählt werden als nötig, und wie Sie überflüssige oder ungenutzte Konten identifizieren und entfernen können, um Geld zu sparen. Es gibt auch einige Ansätze, die zu unnötigen Ausgaben führen können, z. B. wenn ein Personendokument anstelle eines Mail-Ins für geteilte Mailboxen verwendet wird. Wir zeigen Ihnen solche Fälle und deren Lösungen. Und natürlich erklären wir Ihnen das neue Lizenzmodell.
Nehmen Sie an diesem Webinar teil, bei dem HCL-Ambassador Marc Thomas und Gastredner Franz Walder Ihnen diese neue Welt näherbringen. Es vermittelt Ihnen die Tools und das Know-how, um den Überblick zu bewahren. Sie werden in der Lage sein, Ihre Kosten durch eine optimierte Domino-Konfiguration zu reduzieren und auch in Zukunft gering zu halten.
Diese Themen werden behandelt
- Reduzierung der Lizenzkosten durch Auffinden und Beheben von Fehlkonfigurationen und überflüssigen Konten
- Wie funktionieren CCB- und CCX-Lizenzen wirklich?
- Verstehen des DLAU-Tools und wie man es am besten nutzt
- Tipps für häufige Problembereiche, wie z. B. Team-Postfächer, Funktions-/Testbenutzer usw.
- Praxisbeispiele und Best Practices zum sofortigen Umsetzen
June Patch Tuesday

Ivanti’s Patch Tuesday breakdown goes beyond patching your applications and brings you the intelligence and guidance needed to prioritize where to focus your attention first. Catch early analysis on our Ivanti blog, then join industry expert Chris Goettl for the Patch Tuesday Webinar Event. There we’ll do a deep dive into each of the bulletins and give guidance on the risks associated with the newly-identified vulnerabilities.
Building Production Ready Search Pipelines with Spark and Milvus

Spark is the widely used ETL tool for processing, indexing and ingesting data to serving stack for search. Milvus is the production-ready open-source vector database. In this talk we will show how to use Spark to process unstructured data to extract vector representations, and push the vectors to Milvus vector database for search serving.
Operating System Used by Users in day-to-day life.pptx

Dive into the realm of operating systems (OS) with Pravash Chandra Das, a seasoned Digital Forensic Analyst, as your guide. 🚀 This comprehensive presentation illuminates the core concepts, types, and evolution of OS, essential for understanding modern computing landscapes.
Beginning with the foundational definition, Das clarifies the pivotal role of OS as system software orchestrating hardware resources, software applications, and user interactions. Through succinct descriptions, he delineates the diverse types of OS, from single-user, single-task environments like early MS-DOS iterations, to multi-user, multi-tasking systems exemplified by modern Linux distributions.
Crucial components like the kernel and shell are dissected, highlighting their indispensable functions in resource management and user interface interaction. Das elucidates how the kernel acts as the central nervous system, orchestrating process scheduling, memory allocation, and device management. Meanwhile, the shell serves as the gateway for user commands, bridging the gap between human input and machine execution. 💻
The narrative then shifts to a captivating exploration of prominent desktop OSs, Windows, macOS, and Linux. Windows, with its globally ubiquitous presence and user-friendly interface, emerges as a cornerstone in personal computing history. macOS, lauded for its sleek design and seamless integration with Apple's ecosystem, stands as a beacon of stability and creativity. Linux, an open-source marvel, offers unparalleled flexibility and security, revolutionizing the computing landscape. 🖥️
Moving to the realm of mobile devices, Das unravels the dominance of Android and iOS. Android's open-source ethos fosters a vibrant ecosystem of customization and innovation, while iOS boasts a seamless user experience and robust security infrastructure. Meanwhile, discontinued platforms like Symbian and Palm OS evoke nostalgia for their pioneering roles in the smartphone revolution.
The journey concludes with a reflection on the ever-evolving landscape of OS, underscored by the emergence of real-time operating systems (RTOS) and the persistent quest for innovation and efficiency. As technology continues to shape our world, understanding the foundations and evolution of operating systems remains paramount. Join Pravash Chandra Das on this illuminating journey through the heart of computing. 🌟
Generating privacy-protected synthetic data using Secludy and Milvus

During this demo, the founders of Secludy will demonstrate how their system utilizes Milvus to store and manipulate embeddings for generating privacy-protected synthetic data. Their approach not only maintains the confidentiality of the original data but also enhances the utility and scalability of LLMs under privacy constraints. Attendees, including machine learning engineers, data scientists, and data managers, will witness first-hand how Secludy's integration with Milvus empowers organizations to harness the power of LLMs securely and efficiently.
Artificial Intelligence for XMLDevelopment

In the rapidly evolving landscape of technologies, XML continues to play a vital role in structuring, storing, and transporting data across diverse systems. The recent advancements in artificial intelligence (AI) present new methodologies for enhancing XML development workflows, introducing efficiency, automation, and intelligent capabilities. This presentation will outline the scope and perspective of utilizing AI in XML development. The potential benefits and the possible pitfalls will be highlighted, providing a balanced view of the subject.
We will explore the capabilities of AI in understanding XML markup languages and autonomously creating structured XML content. Additionally, we will examine the capacity of AI to enrich plain text with appropriate XML markup. Practical examples and methodological guidelines will be provided to elucidate how AI can be effectively prompted to interpret and generate accurate XML markup.
Further emphasis will be placed on the role of AI in developing XSLT, or schemas such as XSD and Schematron. We will address the techniques and strategies adopted to create prompts for generating code, explaining code, or refactoring the code, and the results achieved.
The discussion will extend to how AI can be used to transform XML content. In particular, the focus will be on the use of AI XPath extension functions in XSLT, Schematron, Schematron Quick Fixes, or for XML content refactoring.
The presentation aims to deliver a comprehensive overview of AI usage in XML development, providing attendees with the necessary knowledge to make informed decisions. Whether you’re at the early stages of adopting AI or considering integrating it in advanced XML development, this presentation will cover all levels of expertise.
By highlighting the potential advantages and challenges of integrating AI with XML development tools and languages, the presentation seeks to inspire thoughtful conversation around the future of XML development. We’ll not only delve into the technical aspects of AI-powered XML development but also discuss practical implications and possible future directions.
Skybuffer SAM4U tool for SAP license adoption

Manage and optimize your license adoption and consumption with SAM4U, an SAP free customer software asset management tool.
SAM4U, an SAP complimentary software asset management tool for customers, delivers a detailed and well-structured overview of license inventory and usage with a user-friendly interface. We offer a hosted, cost-effective, and performance-optimized SAM4U setup in the Skybuffer Cloud environment. You retain ownership of the system and data, while we manage the ABAP 7.58 infrastructure, ensuring fixed Total Cost of Ownership (TCO) and exceptional services through the SAP Fiori interface.
How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf

A Mix Chart displays historical data of numbers in a graphical or tabular form. The Kalyan Rajdhani Mix Chart specifically shows the results of a sequence of numbers over different periods.
Recently uploaded (20)
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf
Energy Efficient Video Encoding for Cloud and Edge Computing Instances

Energy Efficient Video Encoding for Cloud and Edge Computing Instances
Letter and Document Automation for Bonterra Impact Management (fka Social Sol...

Letter and Document Automation for Bonterra Impact Management (fka Social Sol...
Trusted Execution Environment for Decentralized Process Mining

Trusted Execution Environment for Decentralized Process Mining
leewayhertz.com-AI in predictive maintenance Use cases technologies benefits ...

leewayhertz.com-AI in predictive maintenance Use cases technologies benefits ...
Overcoming the PLG Trap: Lessons from Canva's Head of Sales & Head of EMEA Da...

Overcoming the PLG Trap: Lessons from Canva's Head of Sales & Head of EMEA Da...
HCL Notes and Domino License Cost Reduction in the World of DLAU

HCL Notes and Domino License Cost Reduction in the World of DLAU
HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU

HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU
Building Production Ready Search Pipelines with Spark and Milvus

Building Production Ready Search Pipelines with Spark and Milvus
Operating System Used by Users in day-to-day life.pptx

Operating System Used by Users in day-to-day life.pptx
Generating privacy-protected synthetic data using Secludy and Milvus

Generating privacy-protected synthetic data using Secludy and Milvus
Nordic Marketo Engage User Group_June 13_ 2024.pptx

Nordic Marketo Engage User Group_June 13_ 2024.pptx
Deep Dive: Getting Funded with Jason Jason Lemkin Founder & CEO @ SaaStr

Deep Dive: Getting Funded with Jason Jason Lemkin Founder & CEO @ SaaStr
How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf

How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf
Password recovery procedure for the cisco 2900 integrated services router
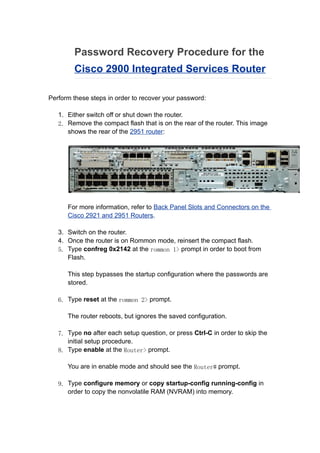
- 1. Password Recovery Procedure for the Cisco 2900 Integrated Services Router Perform these steps in order to recover your password: 1. Either switch off or shut down the router. 2. Remove the compact flash that is on the rear of the router. This image shows the rear of the 2951 router: For more information, refer to Back Panel Slots and Connectors on the Cisco 2921 and 2951 Routers. 3. Switch on the router. 4. Once the router is on Rommon mode, reinsert the compact flash. 5. Type confreg 0x2142 at the rommon 1> prompt in order to boot from Flash. This step bypasses the startup configuration where the passwords are stored. 6. Type reset at the rommon 2> prompt. The router reboots, but ignores the saved configuration. 7. Type no after each setup question, or press Ctrl-C in order to skip the initial setup procedure. 8. Type enable at the Router> prompt. You are in enable mode and should see the Router# prompt. 9. Type configure memory or copy startup-config running-config in order to copy the nonvolatile RAM (NVRAM) into memory.
- 2. Warning: Do not enter copy running-config startup-config or write. These commands erase your startup configuration. 10.Issue the show running-config command. The show running-config command shows the configuration of the router. In this configuration, the shutdown command appears under all interfaces, which indicates all interfaces are currently shut down. In addition, the passwords (enable password, enable secret, vty, and console passwords) are in either an encrypted or unencrypted format. You can reuse unencrypted passwords. You must change encrypted passwords to a new password. 11.Type configure terminal. The hostname(config)# prompt appears. 12.Type enable secret <password> in order to change the enable secret password. For example: 13.hostname(config)#enable secret cisco 14. 15.Issue the no shutdown command on every interface that you use. If you issue a show ip interface brief command, every interface that you want to use should display up up. 16.Type config-register <configuration_register_setting> . Where <configuration_register_setting> is either the value you recorded in step 2 or 0x2102 . For example: 17.hostname(config)#config-register 0x2102 18. 19.Press Ctrl-z or end in order to leave the configuration mode. The hostname# prompt appears. 20.Type write memory or copy running-config startup-config in order to commit the changes.
