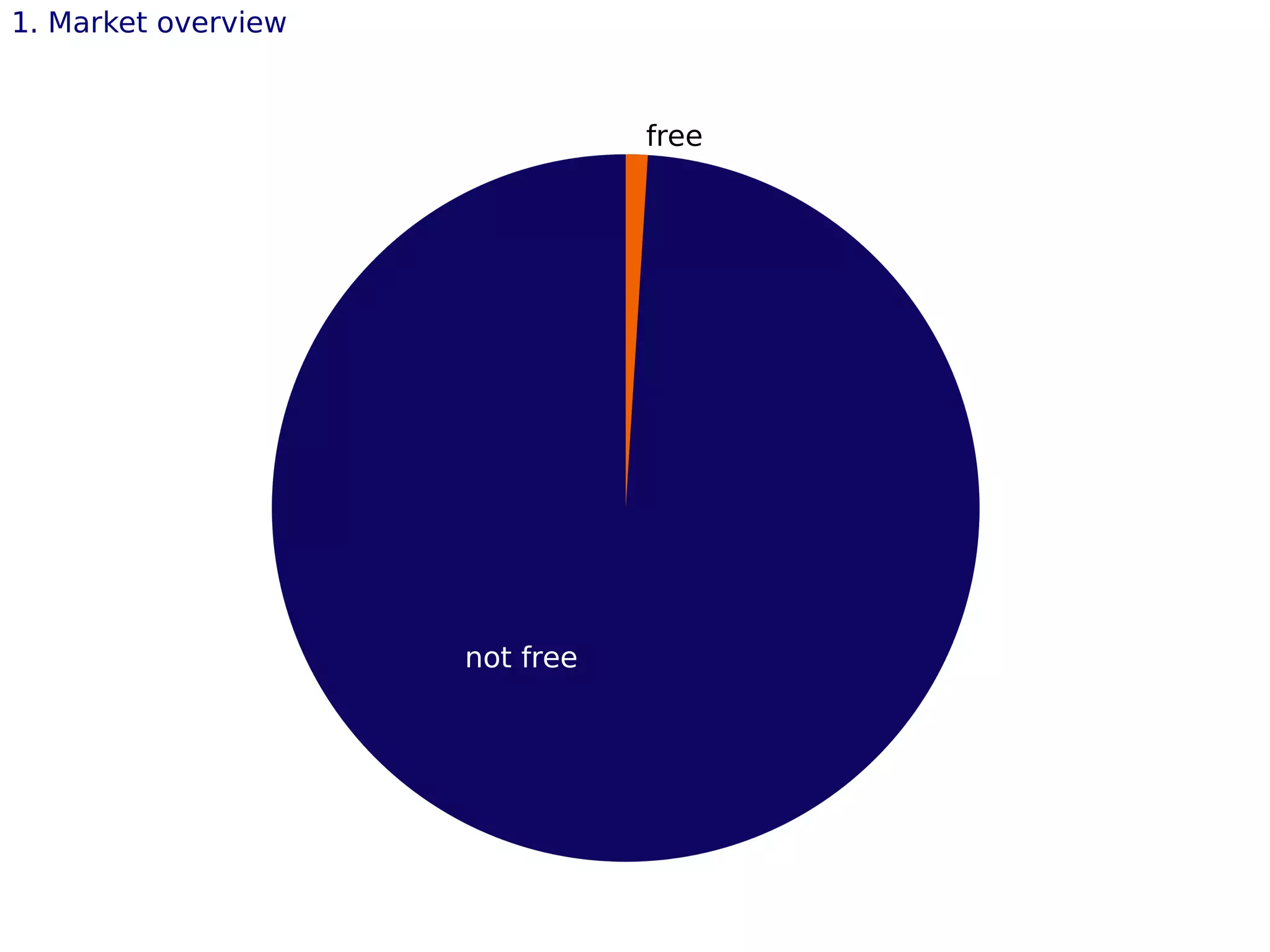
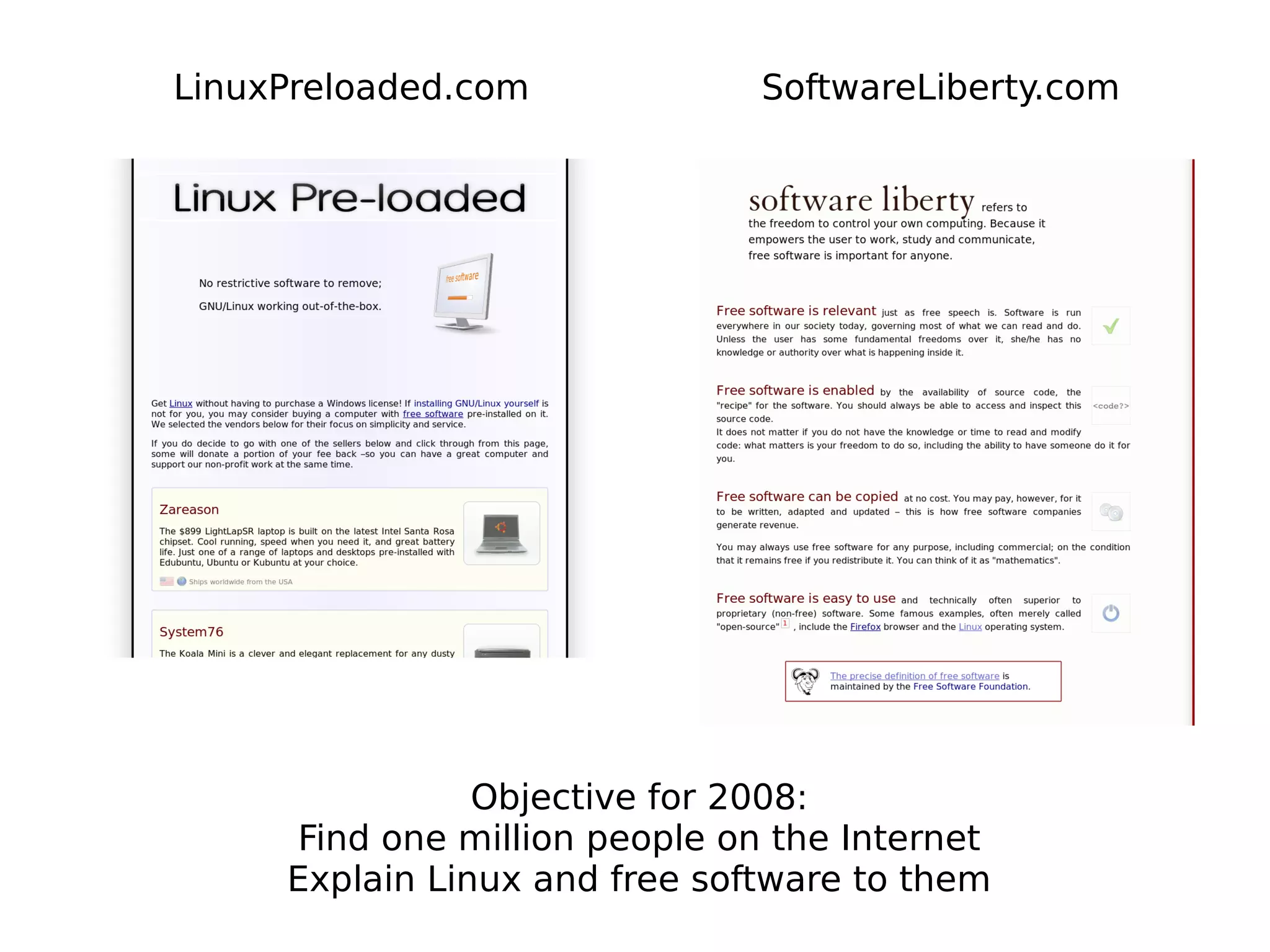
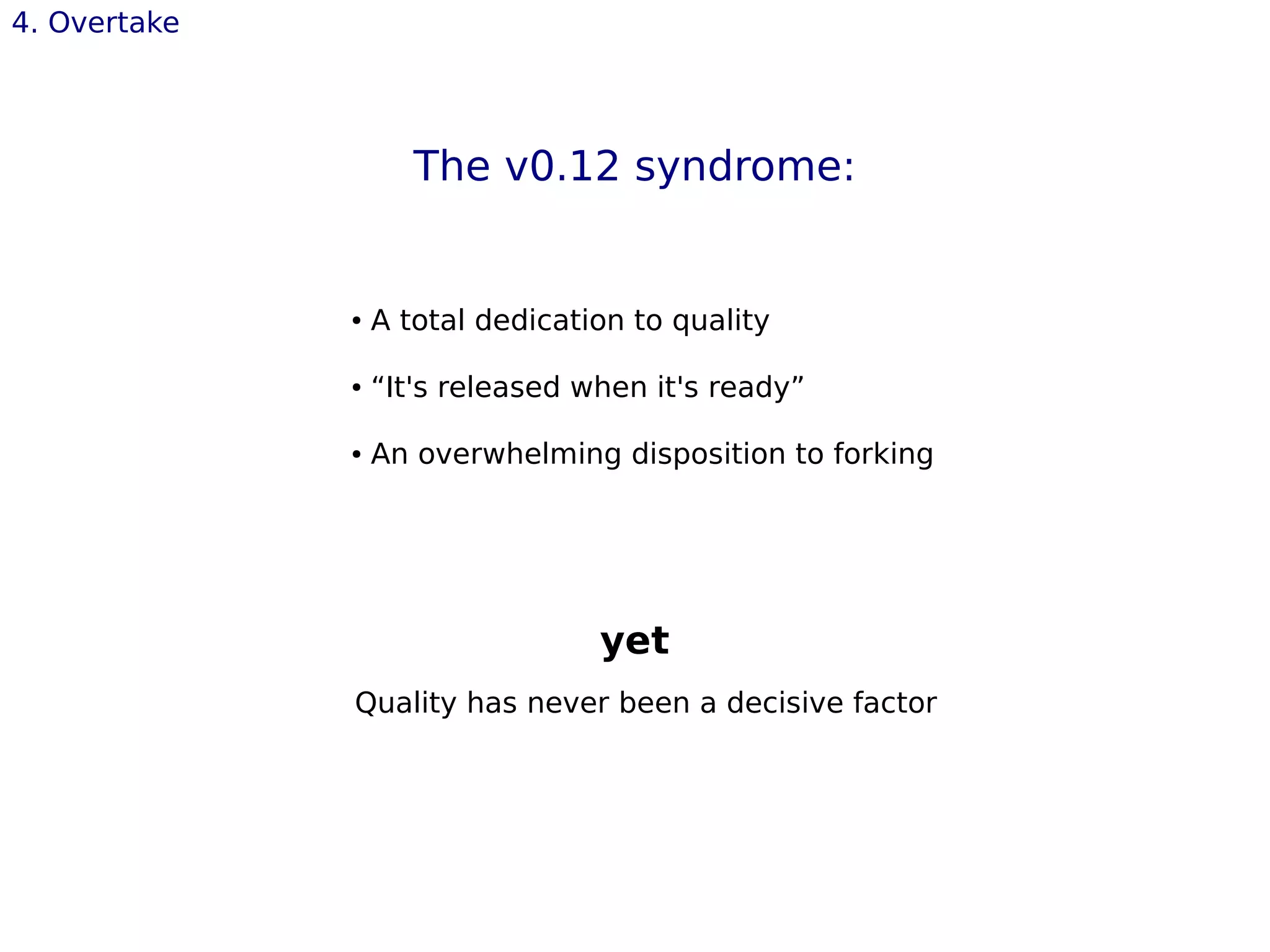
This document discusses the challenges and strategies for advancing free software in a market dominated by proprietary software. It emphasizes the importance of relevance, market alignment, and catering to user needs over focusing solely on software quality. The speaker, Olivier Cleynen, also stresses the necessity of a cultural shift in how free software is perceived and promoted to the public.



![4. Overtake
Firefox [Mozilla]
● Surfing is cool
● Quality is not the recipe...
● “talks to Joe”, but must continually prove
itself “better”](https://image.slidesharecdn.com/overtakingproprietarysoftwarewithoutwritingcode-130505135823-phpapp02/75/Olivier-Cleynen-Overtaking-Proprietary-Software-Without-Writing-Code-24c3-39-2048.jpg)
![4. Overtake
Ubuntu [Canonical]
● Not any better than the 250 other distros
● But it's different. friendly-friendly-friendly.
● A lot of work outside of code-writing: branding, drivers,
pre-install...
● Not afraid to be relevant](https://image.slidesharecdn.com/overtakingproprietarysoftwarewithoutwritingcode-130505135823-phpapp02/75/Olivier-Cleynen-Overtaking-Proprietary-Software-Without-Writing-Code-24c3-40-2048.jpg)