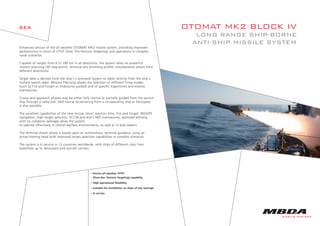
The OTOMAT MK2 BLOCK IV is an enhanced long range anti-ship missile system capable of targeting ships from 6 to 180 km away. It relies on powerful mission planning and flexible targeting options to operate effectively in littoral warfare environments. The missile has a high subsonic cruise speed, 210 kg warhead, and less than 1 minute reaction time. It is in service on ships from 12 countries worldwide.