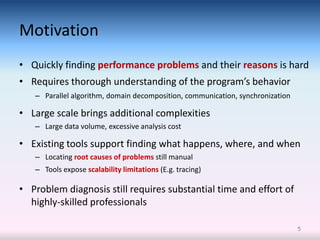
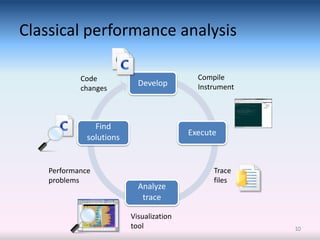
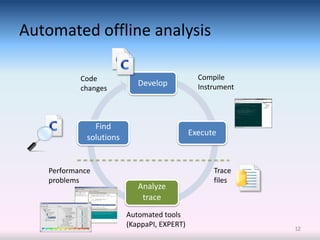
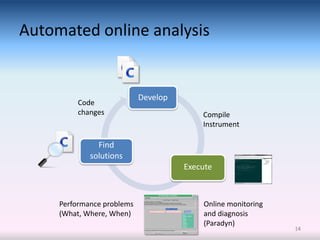
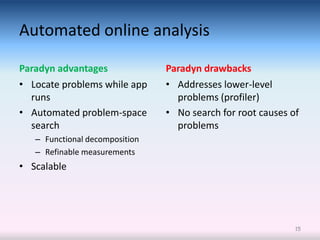
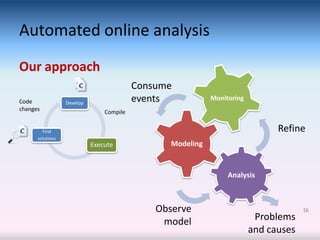
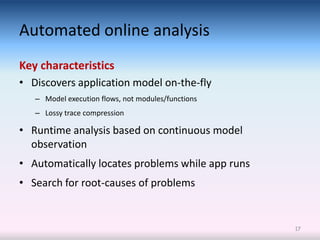
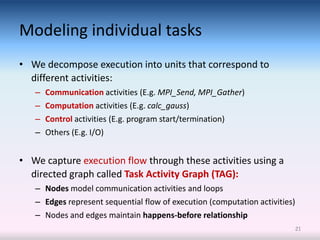
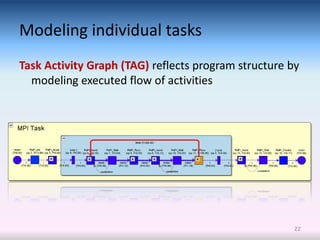
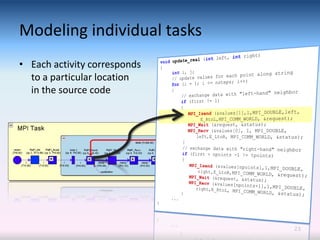
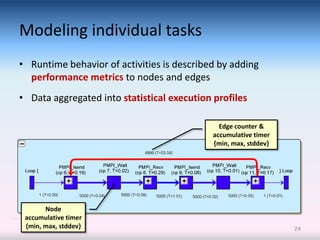
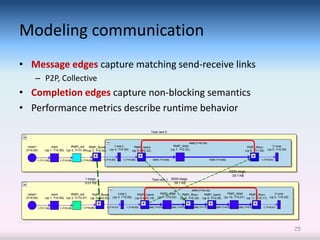
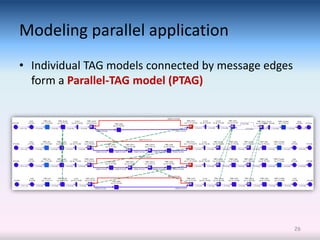
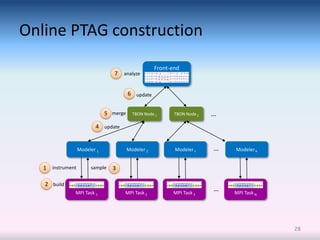
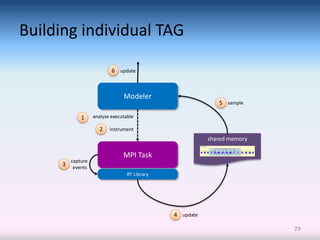
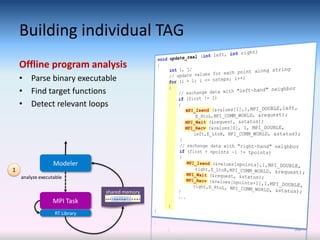
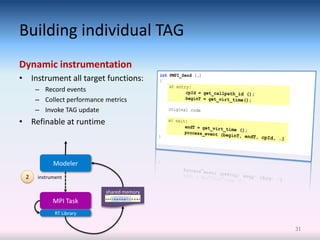
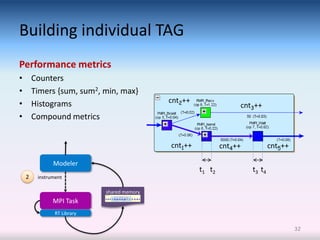
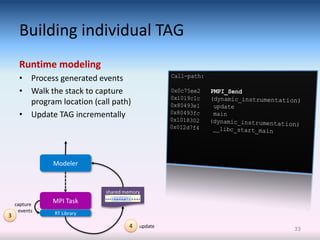
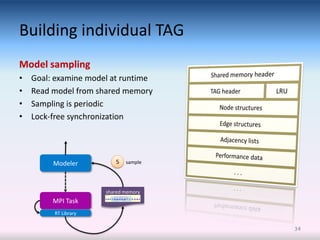
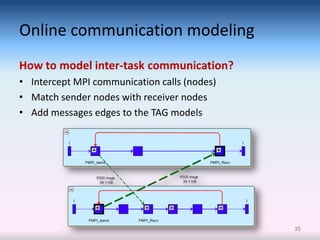
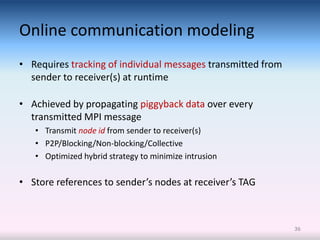
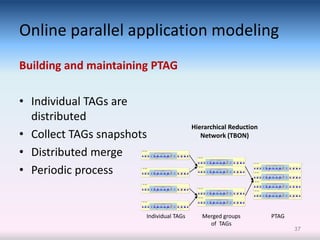
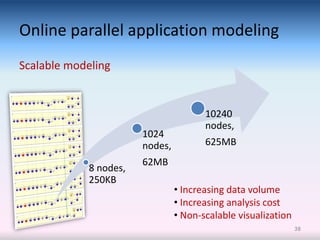
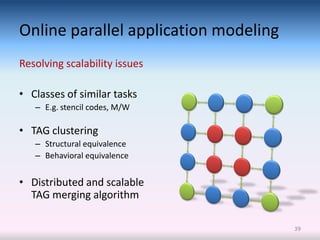
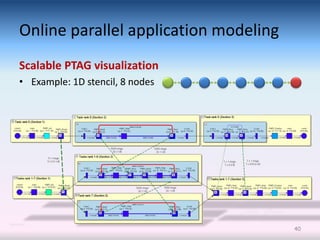
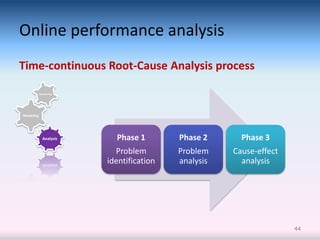
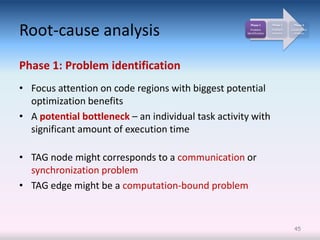
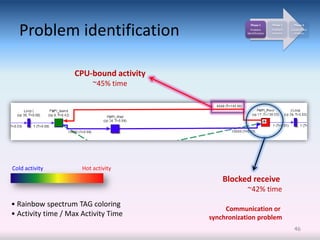
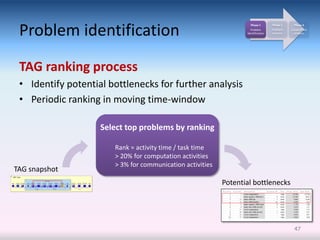
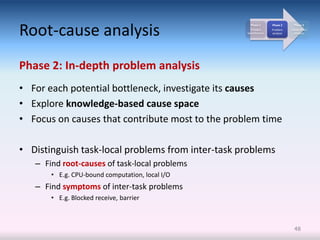
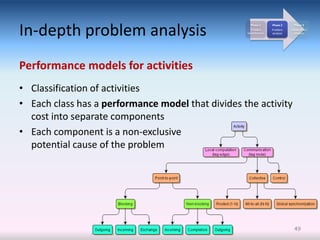
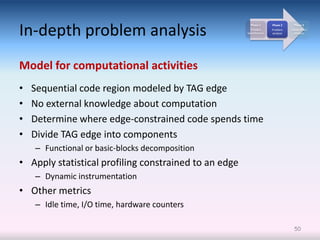
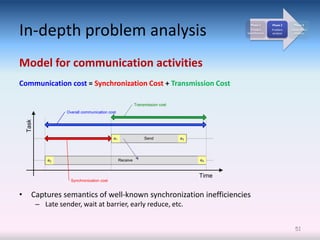
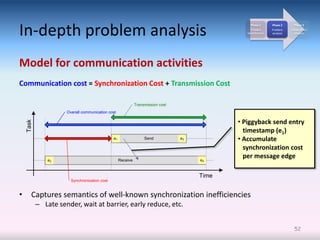
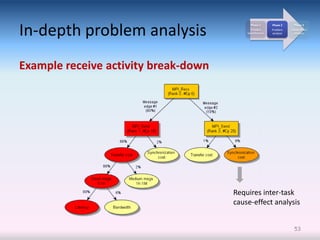
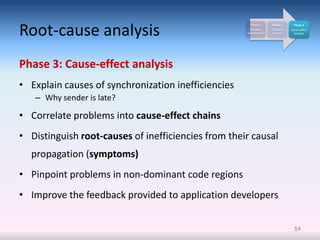
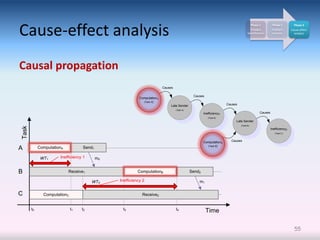
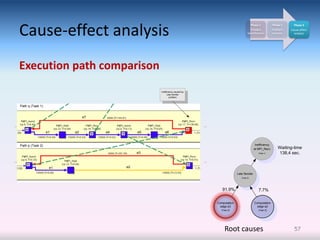
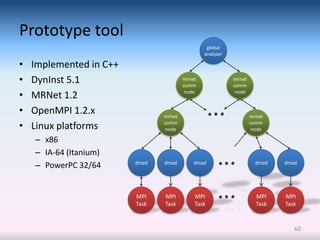
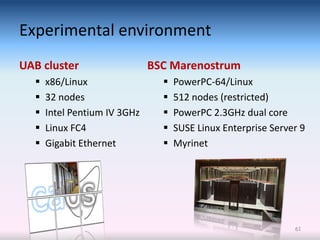
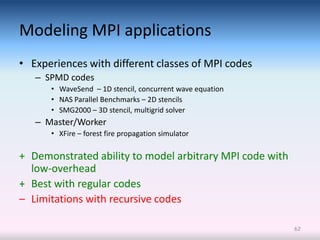
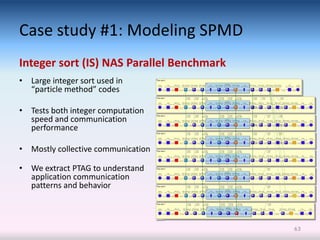
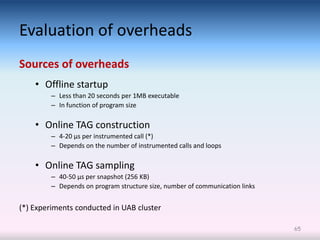
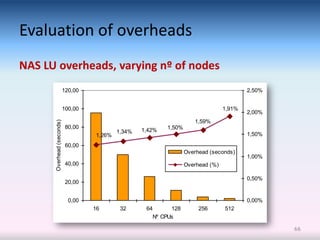
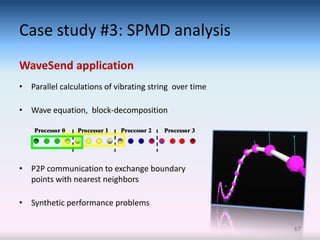
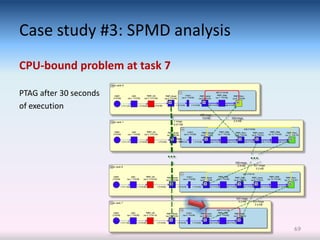
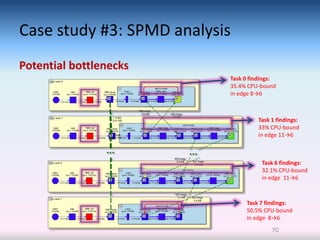
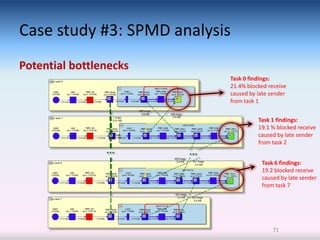
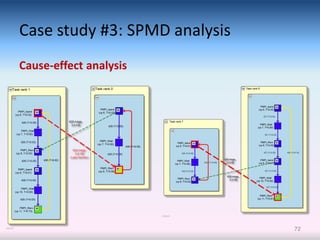
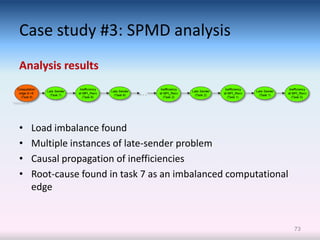
The document details a PhD thesis on online performance modeling and analysis of message-passing parallel applications, emphasizing the challenges of developing large-scale scientific software and the need for efficient performance analysis. It proposes a systematic, automated approach to diagnose application performance, detect bottlenecks, and explain their causes during execution without relying on trace files. The work includes techniques for runtime monitoring, modeling of communication and computation patterns, and an evaluation of its feasibility through case studies and prototype tool development.