Embed presentation
Downloaded 32 times
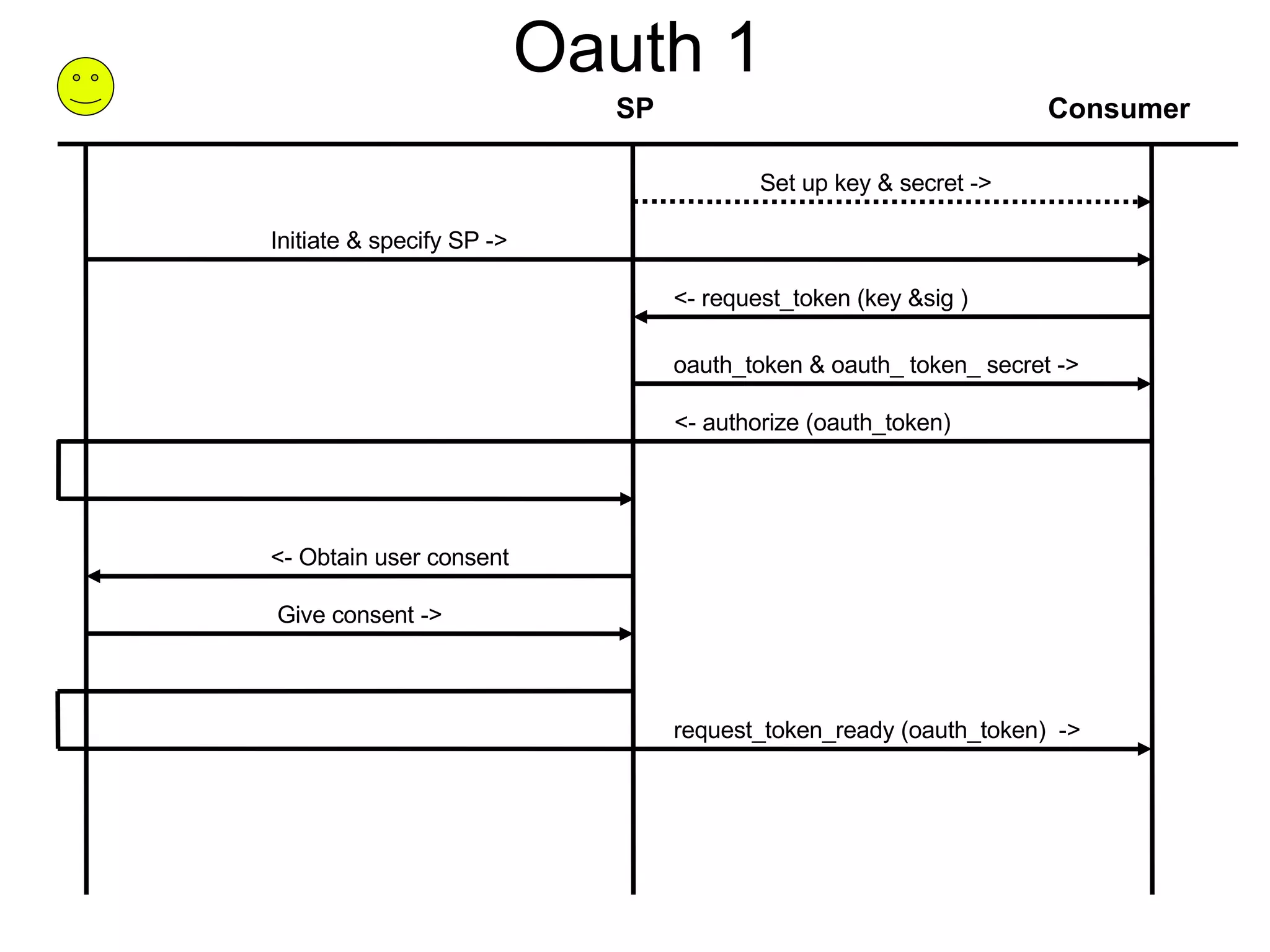
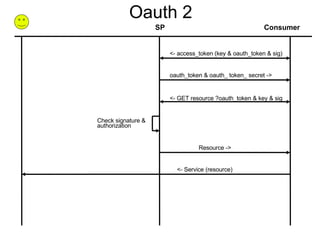

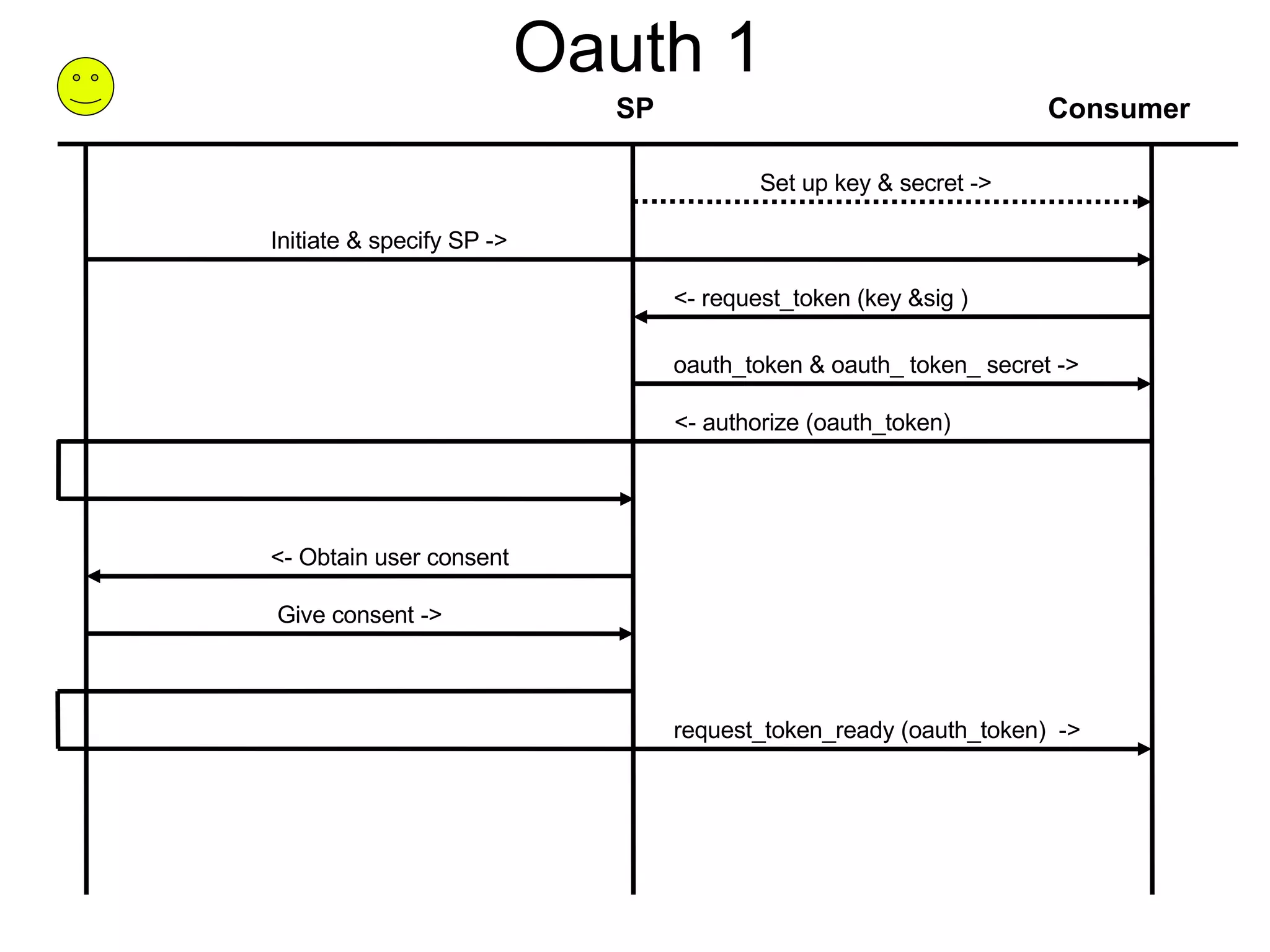
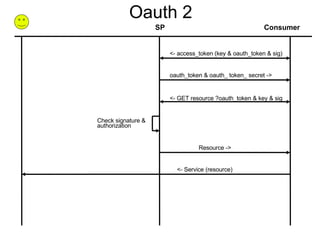
This document outlines the OAuth 1 and OAuth 2 authorization flows. For OAuth 1, it describes how a consumer requests a request token from the service provider, the user authorizes access, and then the consumer exchanges the request token for an access token. For OAuth 2, it shows how the consumer requests an access token directly from the service provider, which can then be used to access protected resources via signatures.