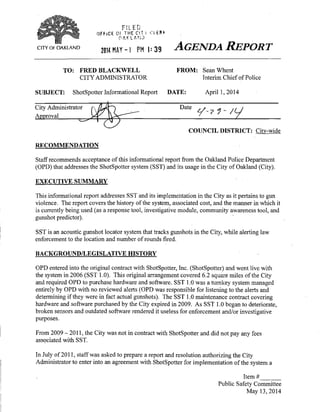
Oakland Report on ShotSpotter: May 13, 2014 Public Safety Committee Meeting
•
1 like•1,205 views
Report on ShotSpotter, Inc. and its uses in the City of Oakland. Presented at the May 13, 2014 Public Safety Committee meeting.
Report
Share
Report
Share
Download to read offline
Recommended
Informational interview report

This report summarizes an informational interview with Ian Aitken, the Coordinator of Residence Life for a dormitory. Ian leads by example and takes a laissez-faire approach, giving his staff freedom in how they accomplish goals. Key leadership skills Ian discussed include strong communication, listening abilities, and interpersonal skills. Ian's career path included undergraduate studies, volunteer work, teaching, and obtaining a master's degree in student personnel administration before becoming a Residence Life Coordinator. Ian finds personal satisfaction in helping students succeed and values integrity and teamwork in his leadership role.
Observation Interview

This document discusses the pros and cons of using observation versus other methods for collecting data in research studies. It notes that observation is better suited for sensitive topics where self-reports may be biased. However, observation requires that the phenomena being studied can actually be observed and may require a long time commitment. The document also outlines different types of observation, including direct, unobtrusive, and disguised field observations, noting ethical issues that need to be considered with each approach.
Safety Week Activity Report

Safety Week 2015 was held from May 4-8 at MLC-WH. Activities included:
1) An opening address and presentation on warehouse safety.
2) Training sessions on back safety, fire safety, ergonomics, and 5S housekeeping.
3) Practical drills like a fire drill and fire hydrant drill.
4) A safety talk and competition where Muhammad Sajid Khan was named Safety Champion.
5) Site visits and sessions to promote safety leadership and awareness.
Police Technologies

New technologies have advanced policing. The NYPD distributed 41,000 smartphones and tablets to officers to improve response times. Other technologies like body cameras, license plate readers, and ShotSpotter help identify criminals and reduce crime. However, critics argue these technologies infringe on privacy and civil liberties, and cost taxpayers money. Overall, law enforcement technologies aim to make communities safer and help solve crimes.
Introduction to chicago crime data with hive and pig

Using the Chicago Crime data available at (https://data.cityofchicago.org/) I will answer a few simple questions to illustrate the use of some common big data tools. The relevant code and screen shots of the output are provided in the appendix of the document.
Technology in crime fighting (project)

This document explores how modern technologies like cell phones, cameras, GPS, DNA testing, fingerprinting, and surveillance systems have improved crime fighting efforts. According to three research articles summarized, these technologies allow law enforcement to more quickly and accurately identify suspects, solve crimes, and exonerate the wrongly accused compared to methods used in past decades. While technology has enhanced crime fighting, the document notes there is still room for improvement in law enforcement's use of emerging technologies.
POLICE PPT.pptx

The document discusses the need for technological reform in the police system. It notes that while technology has helped speed up the criminal investigation process, proper legislation is needed to protect privacy and prevent misuse. Current technologies used by law enforcement like drones, biometrics, and GPS are discussed. The challenges of integrating technology include the lack of regulation and ensuring rural police systems can adopt new technologies. Recommendations include using AI for crime analysis and developing technologies domestically to lower costs. Overall reforms are needed to update police technology while establishing privacy protections.
Crime scene-investigation

The initial responding officers should assess any threats upon arriving at a crime scene, preserve evidence by limiting disturbance of the scene, and ensure safety by controlling any dangerous situations, persons, or materials.
Recommended
Informational interview report

This report summarizes an informational interview with Ian Aitken, the Coordinator of Residence Life for a dormitory. Ian leads by example and takes a laissez-faire approach, giving his staff freedom in how they accomplish goals. Key leadership skills Ian discussed include strong communication, listening abilities, and interpersonal skills. Ian's career path included undergraduate studies, volunteer work, teaching, and obtaining a master's degree in student personnel administration before becoming a Residence Life Coordinator. Ian finds personal satisfaction in helping students succeed and values integrity and teamwork in his leadership role.
Observation Interview

This document discusses the pros and cons of using observation versus other methods for collecting data in research studies. It notes that observation is better suited for sensitive topics where self-reports may be biased. However, observation requires that the phenomena being studied can actually be observed and may require a long time commitment. The document also outlines different types of observation, including direct, unobtrusive, and disguised field observations, noting ethical issues that need to be considered with each approach.
Safety Week Activity Report

Safety Week 2015 was held from May 4-8 at MLC-WH. Activities included:
1) An opening address and presentation on warehouse safety.
2) Training sessions on back safety, fire safety, ergonomics, and 5S housekeeping.
3) Practical drills like a fire drill and fire hydrant drill.
4) A safety talk and competition where Muhammad Sajid Khan was named Safety Champion.
5) Site visits and sessions to promote safety leadership and awareness.
Police Technologies

New technologies have advanced policing. The NYPD distributed 41,000 smartphones and tablets to officers to improve response times. Other technologies like body cameras, license plate readers, and ShotSpotter help identify criminals and reduce crime. However, critics argue these technologies infringe on privacy and civil liberties, and cost taxpayers money. Overall, law enforcement technologies aim to make communities safer and help solve crimes.
Introduction to chicago crime data with hive and pig

Using the Chicago Crime data available at (https://data.cityofchicago.org/) I will answer a few simple questions to illustrate the use of some common big data tools. The relevant code and screen shots of the output are provided in the appendix of the document.
Technology in crime fighting (project)

This document explores how modern technologies like cell phones, cameras, GPS, DNA testing, fingerprinting, and surveillance systems have improved crime fighting efforts. According to three research articles summarized, these technologies allow law enforcement to more quickly and accurately identify suspects, solve crimes, and exonerate the wrongly accused compared to methods used in past decades. While technology has enhanced crime fighting, the document notes there is still room for improvement in law enforcement's use of emerging technologies.
POLICE PPT.pptx

The document discusses the need for technological reform in the police system. It notes that while technology has helped speed up the criminal investigation process, proper legislation is needed to protect privacy and prevent misuse. Current technologies used by law enforcement like drones, biometrics, and GPS are discussed. The challenges of integrating technology include the lack of regulation and ensuring rural police systems can adopt new technologies. Recommendations include using AI for crime analysis and developing technologies domestically to lower costs. Overall reforms are needed to update police technology while establishing privacy protections.
Crime scene-investigation

The initial responding officers should assess any threats upon arriving at a crime scene, preserve evidence by limiting disturbance of the scene, and ensure safety by controlling any dangerous situations, persons, or materials.
PVRS Issue Paper (PADM5007)

This paper examines the costs and benefits of personal video recording systems (PVRs) or body cameras for law enforcement agencies. It summarizes experiences of agencies that have implemented body cameras like Modesto Police Department, which saw benefits such as reduced citizen complaints. The author also discusses a study by Taser International finding agencies saved $7.6 million over 3 years from efficiencies with body cameras. While body cameras involve upfront and ongoing costs, the paper argues they can help reduce costs from fewer lawsuits and internal investigations due to clear video evidence of encounters. The author believes body cameras improve transparency and trust between police and communities.
Developing technology

The document discusses the use of closed-circuit television (CCTV) surveillance by law enforcement. It describes how CCTV cameras have become widely used in public spaces and how they can help reduce crime rates. CCTV surveillance systems are either active, with a live monitor, or passive, recording for later review. The cameras are intended to increase the risk of getting caught committing a crime. However, their effectiveness depends on criminals being aware of the surveillance and believing there is a risk of arrest. While CCTV has benefits, it also raises issues regarding privacy and creating a perception of insecurity.
9639NCJRS.pdf nacional chemical justice service

This document provides a selected basic reference bibliography for police weapons and equipment. It includes references on topics such as combat pistol shooting, police handgun selection, shotguns, rifles, automatic weapons, chemical weapons, batons, explosives, and protective armor. The bibliography was produced as part of an information dissemination service by the Police Weapons Center.
Ci ch 3

The document describes the process for managing crime scenes and investigating crimes in South Africa. It outlines 10 phases for managing a crime scene: from initial reporting to the release of the scene. It also details the command structures for investigations conducted by detectives and forensic scientists. The roles of first responders, crime scene managers, detectives and forensic scientists are defined. Finally, it provides an example of how the type of crime determines which investigative units and forensic science labs are involved.
Running head CRIME ANALYSIS .docx

Running head: CRIME ANALYSIS 1
CRIME ANALYSIS TECHNOLOGY 2
Crime analysis is a function that usually involves the systemic analysis in identifying as well as analyzing the crime patterns and trends. Crime analysis is very important for law enforcement agencies as it helps law enforcers effectively deploy the available resources in a better and effective manner, which enables them to identify and apprehend suspects. Crime analysis is also very significant when it comes to arriving at solutions devised to come up with the right solution to solve the current crime problem and issues as well as coming up with the right prevention strategies. Since the year 2014, crime rates in the USA have increased steadily as per a study done by USAFacts, which is a non-partisan initiative (Osborne & Wernicke, 2013). With this increase in crime rates, which has majorly resulted in massive growth in technology, it is essential to come up with better means and ways of dealing with the increased crime rates. With the current advancement in technology, better law enforcement tools developed, which has enabled better crime deterrence in better and efficient ways. All this has been facilitated by the efforts of crime analysts who have come up with better tools and thus enabling the law enforcers to better deal with the crimes (Osborne & Wernicke, 2013). In this paper, I will consider the application of crime analysis technology and techniques in fighting crimes. Application of crime analysis technology and techniques used to make crime analysis more accurate and efficient.
Currently, the two technological tools that are used in predictive policing software have enabled security agencies to effectively use predictive policing ("Crime Analysis: Fighting Crime with Data," 2017). Application of this software has enabled better crime prevention as with data obtained in the previous crimes have been used to predict possible future severe crimes in a specific area.
Through the adoption and use of crime analysis, law enforcement agencies have been able to fight against crimes as when compared with the past effectively. The use of crime analysis comes at the right time, where there has been an increase in crime rates in the current digital error. In a survey done by Wynyard group in 2015, the study revealed that for every 10 law enforcement officials 9 of them believe that the use of current technology in crime analysis has had positive effects in helping the agencies in solving crimes as they can identify essential links and trends in crimes ("Crime Analysis: Fighting Crime with Data," 2017). In the same way, other sectors have benefited from data analysis with spreadsheets, databases, and mapping, law enforcers have been able to use data analysis to come up with a better decision. Crime analysis ha ...
Running head CRIME ANALYSIS .docx

Running head: CRIME ANALYSIS 1
CRIME ANALYSIS TECHNOLOGY 2
Crime analysis is a function that usually involves the systemic analysis in identifying as well as analyzing the crime patterns and trends. Crime analysis is very important for law enforcement agencies as it helps law enforcers effectively deploy the available resources in a better and effective manner, which enables them to identify and apprehend suspects. Crime analysis is also very significant when it comes to arriving at solutions devised to come up with the right solution to solve the current crime problem and issues as well as coming up with the right prevention strategies. Since the year 2014, crime rates in the USA have increased steadily as per a study done by USAFacts, which is a non-partisan initiative (Osborne & Wernicke, 2013). With this increase in crime rates, which has majorly resulted in massive growth in technology, it is essential to come up with better means and ways of dealing with the increased crime rates. With the current advancement in technology, better law enforcement tools developed, which has enabled better crime deterrence in better and efficient ways. All this has been facilitated by the efforts of crime analysts who have come up with better tools and thus enabling the law enforcers to better deal with the crimes (Osborne & Wernicke, 2013). In this paper, I will consider the application of crime analysis technology and techniques in fighting crimes. Application of crime analysis technology and techniques used to make crime analysis more accurate and efficient.
Currently, the two technological tools that are used in predictive policing software have enabled security agencies to effectively use predictive policing ("Crime Analysis: Fighting Crime with Data," 2017). Application of this software has enabled better crime prevention as with data obtained in the previous crimes have been used to predict possible future severe crimes in a specific area.
Through the adoption and use of crime analysis, law enforcement agencies have been able to fight against crimes as when compared with the past effectively. The use of crime analysis comes at the right time, where there has been an increase in crime rates in the current digital error. In a survey done by Wynyard group in 2015, the study revealed that for every 10 law enforcement officials 9 of them believe that the use of current technology in crime analysis has had positive effects in helping the agencies in solving crimes as they can identify essential links and trends in crimes ("Crime Analysis: Fighting Crime with Data," 2017). In the same way, other sectors have benefited from data analysis with spreadsheets, databases, and mapping, law enforcers have been able to use data analysis to come up with a better decision. Crime analysis ha.
Modern trends in police force

Modern policing is being transformed by new technologies that help solve, prevent, and enable new forms of crime. Surveillance cameras are becoming more widespread and advanced, using facial recognition and the ability to track suspects. New forensic techniques like DNA analysis and digital evidence collection are helping identify criminals. The role of intelligence analysts is growing to understand new threat environments and develop police strategies. Wearable cameras on officers and digital recordings of interrogations are increasing transparency and accountability.
Presentation eco.pptx

Technology has revolutionized crime prevention and investigation. In the past, law enforcement relied on tools like trained dogs and footprints, but now use advanced technologies like CCTV, satellites with GPS, and biometric identification through fingerprints, DNA, iris scans, and facial recognition. Other technologies that aid law enforcement include weapons, metal detectors, social media for awareness, and mobile devices that provide location data. While technology enables new types of crimes, it has provided many benefits to outpace criminals when used respectfully and judiciously by law enforcement.
Case Study - Waterloo Regional Police

The Waterloo Regional Police Service used to have an investigator spend full time manually analyzing location data from tracking devices and cell phones to generate reports on suspects' patterns of movement and activities. This was a time-consuming process. The police service purchased ICU Workbench software, which automatically analyzes location data and generates pattern of life reports. This new process provides deeper insights into suspects' behaviors more quickly. It allows the investigator previously dedicated to data analysis to return to field work, while gaining more powerful intelligence. The new software has significantly reduced the time needed to analyze location data and freed up resources for more optimal use.
IRJET- A Survey Paper of Blood Spatter Trajectory Analysis for Forensic Crime

This document discusses blood spatter analysis for forensic crime scene investigation. It begins with an abstract that outlines the application of image processing techniques to analyze blood trajectories at crime scenes. It then provides background on forensic science and crime scene analysis. Specifically, it discusses how blood stains can provide important evidence and how blood spatter analysis is used to help reconstruct crime events. The document emphasizes that accurately collecting and analyzing blood evidence is important for solving cases.
Crimea Russia or Ukraine An International Law Perspective.docx

Crimea: Russia or Ukraine? An International Law Perspective
Crimea was annexed by Russia in 2014 after a referendum was held which was not up to international standards. This move was largely condemned by the West and most of the international community does not recognize Crimea as a legitimate part of Russia, though it is now ruled by Russia and applicable to its laws, currency, and military. For example, residents of Crimea, even those who did not vote or voted against the annexation, are subject to the Russian conscription law which states that all healthy males aged 18 are required to complete mandatory military service unless unable to do so for a medical reason or if they are enrolled in a university (Conscription Service, p. 1). Up to today, Ukraine and Russia both claim that Crimea is theirs and there is no agreement reached at the time to settle this conflict.
Background on how crimea was taken (maidan revolution, etc.)
In order to begin to understand which country Crimea belongs to, it is important to understand the history of the peninsula. Crimea has been part of the Russian empire beginning in 1783 (Kramer, 1) after the defeat of the Ottomans up until 1954 when, during the Soviet Union, it was given to the Ukrainian SFSR by Premier Khrushchev.
Russia’s argument as to why Crimea is theirs
West’s argument as to why it belongs to Ukraine (their own motives and desire for influence)
International Law analysis
Works Cited
“Conscription Service.” Counterterrorism : Ministry of Defence of the Russian
Federation, eng.mil.ru/en/career/conscription/determent.htm.
Kramer, M. (2018, February 02). Why Did Russia Give Away Crimea Sixty Years Ago?
Retrieved December 07, 2018, from
https://www.wilsoncenter.org/publication/why-did-russia-give-away-crimea-sixty-y
ears-ago?gclid=CLHnyZC7ndACFSLicgod-UEIXw
Milestone One: MEMO Draft 1
Milestone One: MEMO Draft 6
THIS IS THE PROFESSOR’S COMMENT ON THE MEMO AND NEEDS TO BE FIXED FOR FINAL SUBMISSION.( Gifty,Thanks for getting this turned in. For a memo, this is a little long. You will want to be more succinct and cut this down a bit.)
MEMO
DATE: 12/08/2018
TO: Non-expert Stakeholder
FROM: (Cybersecurity Practitioner)
SUBJECT: DIGITAL FORENSIC INVESTIGATION MEMO
Over a period of years digital forensic investigation has out grown into a body that in need of details digital forensic model. Different academic researchers have suggested over a hundred different types of investigation procedural models. In addition to this proposed model over the years, there has been a challenged whereby the model lack experimental testing to ascertain the truth about the investigation. More so there is a need of evaluating the same model to complement the process of investigation progression in support to the entire scientific community (Learner, D. E. (2009). Electronic cri.
Anti-Forensic Techniques and Its Impact on Digital Forensic

This paper discusses anti-forensic techniques that are used to evade digital forensic investigations. It provides an overview of common anti-forensic techniques such as file wiping, data hiding using encryption, steganography, and obfuscation. The paper analyzes how these techniques work and their effectiveness at impeding investigations. It highlights the need for new forensic tools and techniques to counter increasingly sophisticated anti-forensic methods used by criminals to cover their digital traces and hide evidence.
Assignment 3 Major Essay

1) The document discusses 10 potential measures for effective criminal intelligence in law enforcement. It explores these measures in the context of the New Zealand Police and considers if they could be applied to other law enforcement organizations.
2) It provides definitions and models of intelligence to help establish what intelligence outcomes might be. Potential outcomes include having an impact on the criminal environment to make communities safer.
3) Measures are discussed within a framework of interpreting and influencing components of an intelligence model, as well as considering intelligence as a structure, process, and product.
IRAC WorksheetIRAC FormatFactsISSUE#1.docx

IRAC Worksheet
IRAC Format
Facts:
ISSUE:
#1:
#2:
#3
RULE of LAW:
ANALYSIS:
CONCLUSION:
worldwide.erau.edu
All rights are reserved. The material contained herein is the copyright property of Embry-Riddle Aeronautical University, Daytona Beach, Florida, 32114. No part of this material may be reproduced, stored in a retrieval system, or transmitted in any form, electronic, mechanical, photocopying, recording or otherwise without the prior written consent of the University.
image2.png
image3.png
Policing in America
Police officers are the gatekeepers of criminal justice. They are the ones that initiate criminal proceedings against those accused of crimes and send them on their journey through the criminal justice system. Policing has evolved immensely over the centuries. Since the inception of policing in 1066, we have seen a transformation from ill-equipped, untrained, corrupt, and unsupervised watchmen to the highly trained and supervised police agencies we see today.
Question 1: Using Chapter 4, "Police in Society: History and Organization," of your textbook, complete the table below.
History of the
Police
Time Period
Overview of the
Time Period – What Defined It
Strengths of
This Time Period
Weaknesses of
This Time Period
Key Developments
(list two per time period)
1066–1600
(example)
Policing initially began as villages protecting each other from thieves and marauders. This system was overseen by a constable, appointed by the local nobleman. This system expanded into the watch system that patrolled larger cities and towns. Watchmen patrolled at night to protect against robberies, burglaries, and fires. They reported to a constable making up a sort of primitive police agency.
Citizens were responsible for keeping their cities and villages safe. Giving citizens this responsibility made it tougher for criminals to commit a crime undetected.
While the people of the village were responsible for reporting crimes, there was no formal training involved and no oversight to ensure that those responsible for preventing crimes were not the same ones committing crimes.
1. Back then, counties were known as shires, and head law enforcement agents in a county were known as shire reves, which is where we get the modern-day term
sheriff.
2. In 1326, the Justice of the Peace was created and the role of law enforcement expanded beyond just reporting crimes. Justices then also served warrants, investigated crimes, and supervised the local watchmen.
1800–1900
1900–1960
1960–1980
1980–present
(Community Policing period)
Question 2: Which ONE of the above time periods do you believe has had the greatest impact on policing, and why? Be sure to include your rationale.
(
Type answer here) -
Question 3: Social media and technology have greatly affected policing in the past ten years. Please review the links provided for this week on technol.
An application development for police stations in pakistan

Program slice is the part of program that may take the program off the path of the
desired output at some point of its execution. Such point is known as the slicing criterion.
This point is generally identified at a location in a given program coupled with the subset
of variables of program. This process in which program slices are computed is called
program slicing. Weiser was the person who gave the original definition of program slice
in 1979. Since its first definition, many ideas related to the program slice have been
formulated along with the numerous numbers of techniques to compute program slice.
Meanwhile, distinction between the static slice and dynamic slice was also made.
Program slicing is now among the most useful techniques that can fetch the particular
elements of a program which are related to a particular computation. Quite a large
numbers of variants for the program slicing have been analyzed along with the
algorithms to compute the slice. Model based slicing split the large architectures of
software into smaller sub models during early stages of SDLC. Software testing is
regarded as an activity to evaluate the functionality and features of a system. It verifies
whether the system is meeting the requirement or not. A common practice now is to
extract the sub models out of the giant models based upon the slicing criteria. Process of
model based slicing is utilized to extract the desired lump out of slice diagram. This
specific survey focuses on slicing techniques in the fields of numerous programing
paradigms like web applications, object oriented, and components based. Owing to the
efforts of various researchers, this technique has been extended to numerous other
platforms that include debugging of program, program integration and analysis, testing
and maintenance of software, reengineering, and reverse engineering. This survey
portrays on the role of model based slicing and various techniques that are being taken
on to compute the slices.
1 Project Background Rosa County Public Safety Syste.docx

1
Project Background: Rosa County Public Safety System Upgrade
Note: this case study project focuses on the software development, physical installation, and personnel
training required for a public safety system upgrade, the addition of a computer-aided dispatch (CAD)
system that allows municipal governments to receive and process incoming emergency calls to public fire
and police departments and then to dispatch appropriate field units to required locations. Details included
in this case study are based on review of several different CAD systems throughout the United States and
are intentionally set in the late 1990s, when standardized project management processes and practices
were used less commonly than they are today. No individuals from any municipality are included in this
case study (either by name or pseudonym), and any similarities to actual systems, processes or events is
coincidental.
Rosa County (population 900,000, covering over 500 square miles) first investigated upgrading its public
safety response processes in the late 1990s, when the County Police Department had been working with
the County Fire Department to share handling all police and fire-related communications and dispatch
functions internally and, due to a rapidly increasing population, both departments realized call volume was
quickly exceeding current ability to respond.
The existing cumbersome and labor intensive call response process also required a steady pool of internal
support to maintain, made up of civilian call takers and dispatchers, and, more recently, uniformed
personnel who were tasked on an as-needed basis during especially active periods (holiday weekends, for
example). To address the growing problem, Rosa County public safety representatives attended a state-
wide public safety symposium in early 1998 to discuss similar issues encountered by other counties, as
well as potential solutions. One of several vendors at the symposium expo, OnCall Systems, caught the
attention of Rosa Police Department senior personnel and scheduled a demonstration of their recently-
developed computer-aided dispatch (CAD) system for the following week.
OnCall gave their prepared demonstration as scheduled, the week after the symposium. The
demonstration focused on assignment and tracking of units in response to calls for service, with enhanced
electronic mapping and address retrieval capability at the dispatch center and inside units themselves. The
demonstration also featured significant use of a Global Positioning System (GPS) to locate and track
emergency vehicles using externally-mounted transmitters. The demonstration was attended by Rosa
County police and fire department personnel, including the Chief of Police, his immediate assistant, and a
handful of deputy and assistant chiefs from both departments. The Fire Chief was unable to attend due to
a scheduling conflict, but his Assistant Chief of Administrative ...
External Mechanisms Of Accountaability

The document discusses various mechanisms of accountability for police departments, including internal mechanisms like COMPSTAT and external mechanisms like civilian review boards and courts. COMPSTAT is an internal accountability method that uses data analysis of crime statistics to hold police commanders accountable for addressing problems in their jurisdictions. It promotes focused problem-solving in police meetings. External accountability comes from civilian oversight like review boards and courts establishing police misconduct standards.
Malware analysis

This document discusses a case study involving a small-medium enterprise (SME) that has experienced anomalies in its accounting and product records. The SME has hired a digital forensic investigator to determine if any malicious activity has occurred and ensure its systems are free of malware. The investigator will conduct a malware investigation and digital forensic investigation following the four principles of the Association of Chief Police Officers (ACPO) guidelines. The investigator will use the Four Step Forensics Process (FSFP) model to identify, preserve, extract, and analyze evidence from the SME's systems to determine the cause of problems and make recommendations.
Predictive-Preventative-or-Intelligence-Led-Policing

This document discusses the current state and future of predictive policing and intelligence-led policing. It provides an overview of techniques currently used by UK police forces, such as crime mapping and repeat victimization analysis. It finds that while current approaches are data-driven, they are not truly predictive and instead focus on intelligence and prevention. The document envisions the future involving more advanced use of data and technology to help officers focus on prevention and improving community safety. However, it cautions that true predictive policing would require integrating more diverse data sources than what most current models use. Overall, the document argues that predictive policing can help police make valuable contributions to victim and community protection when its tools evolve to enable more preventative strategies.
Predictive preventative-or-intelligence-led-policing

This document discusses the current state and future of predictive policing and intelligence-led policing. It provides an overview of techniques currently used by UK police forces, such as crime mapping and repeat victimization analysis. It finds that while current approaches are effective at reducing crime, they are not truly predictive and rely on historical crime data. True predictive policing would require integrating additional data sources. The document also speculates on how policing demands may evolve with trends like cybercrime and how police can leverage new technologies and data to help prevent crime and support communities in the future.
Schedule of City of Oakland Meetings

This is an incomplete list as the City of Oakland doesn't have the meeting times and locations for a number of Boards and Commissions posted. If/when the city responds to requests for that information, an updated list will be posted.
Oakland Sharing the Vision (OSV) Members, 1992

This document lists the members of various task forces for the organization Oakland Sharing the Vision. It includes over 300 members divided among task forces focused on Expanded Economic Base, Neighborhood Revitalization, Safe Healthy Drug-Free City, Education and Lifelong Learning, Building Coalitions, Cultural Affairs, and Grants/Public Art/Marketing committees. The document provides names and is intended to identify individuals involved in different initiatives of the organization.
More Related Content
Similar to Oakland Report on ShotSpotter: May 13, 2014 Public Safety Committee Meeting
PVRS Issue Paper (PADM5007)

This paper examines the costs and benefits of personal video recording systems (PVRs) or body cameras for law enforcement agencies. It summarizes experiences of agencies that have implemented body cameras like Modesto Police Department, which saw benefits such as reduced citizen complaints. The author also discusses a study by Taser International finding agencies saved $7.6 million over 3 years from efficiencies with body cameras. While body cameras involve upfront and ongoing costs, the paper argues they can help reduce costs from fewer lawsuits and internal investigations due to clear video evidence of encounters. The author believes body cameras improve transparency and trust between police and communities.
Developing technology

The document discusses the use of closed-circuit television (CCTV) surveillance by law enforcement. It describes how CCTV cameras have become widely used in public spaces and how they can help reduce crime rates. CCTV surveillance systems are either active, with a live monitor, or passive, recording for later review. The cameras are intended to increase the risk of getting caught committing a crime. However, their effectiveness depends on criminals being aware of the surveillance and believing there is a risk of arrest. While CCTV has benefits, it also raises issues regarding privacy and creating a perception of insecurity.
9639NCJRS.pdf nacional chemical justice service

This document provides a selected basic reference bibliography for police weapons and equipment. It includes references on topics such as combat pistol shooting, police handgun selection, shotguns, rifles, automatic weapons, chemical weapons, batons, explosives, and protective armor. The bibliography was produced as part of an information dissemination service by the Police Weapons Center.
Ci ch 3

The document describes the process for managing crime scenes and investigating crimes in South Africa. It outlines 10 phases for managing a crime scene: from initial reporting to the release of the scene. It also details the command structures for investigations conducted by detectives and forensic scientists. The roles of first responders, crime scene managers, detectives and forensic scientists are defined. Finally, it provides an example of how the type of crime determines which investigative units and forensic science labs are involved.
Running head CRIME ANALYSIS .docx

Running head: CRIME ANALYSIS 1
CRIME ANALYSIS TECHNOLOGY 2
Crime analysis is a function that usually involves the systemic analysis in identifying as well as analyzing the crime patterns and trends. Crime analysis is very important for law enforcement agencies as it helps law enforcers effectively deploy the available resources in a better and effective manner, which enables them to identify and apprehend suspects. Crime analysis is also very significant when it comes to arriving at solutions devised to come up with the right solution to solve the current crime problem and issues as well as coming up with the right prevention strategies. Since the year 2014, crime rates in the USA have increased steadily as per a study done by USAFacts, which is a non-partisan initiative (Osborne & Wernicke, 2013). With this increase in crime rates, which has majorly resulted in massive growth in technology, it is essential to come up with better means and ways of dealing with the increased crime rates. With the current advancement in technology, better law enforcement tools developed, which has enabled better crime deterrence in better and efficient ways. All this has been facilitated by the efforts of crime analysts who have come up with better tools and thus enabling the law enforcers to better deal with the crimes (Osborne & Wernicke, 2013). In this paper, I will consider the application of crime analysis technology and techniques in fighting crimes. Application of crime analysis technology and techniques used to make crime analysis more accurate and efficient.
Currently, the two technological tools that are used in predictive policing software have enabled security agencies to effectively use predictive policing ("Crime Analysis: Fighting Crime with Data," 2017). Application of this software has enabled better crime prevention as with data obtained in the previous crimes have been used to predict possible future severe crimes in a specific area.
Through the adoption and use of crime analysis, law enforcement agencies have been able to fight against crimes as when compared with the past effectively. The use of crime analysis comes at the right time, where there has been an increase in crime rates in the current digital error. In a survey done by Wynyard group in 2015, the study revealed that for every 10 law enforcement officials 9 of them believe that the use of current technology in crime analysis has had positive effects in helping the agencies in solving crimes as they can identify essential links and trends in crimes ("Crime Analysis: Fighting Crime with Data," 2017). In the same way, other sectors have benefited from data analysis with spreadsheets, databases, and mapping, law enforcers have been able to use data analysis to come up with a better decision. Crime analysis ha ...
Running head CRIME ANALYSIS .docx

Running head: CRIME ANALYSIS 1
CRIME ANALYSIS TECHNOLOGY 2
Crime analysis is a function that usually involves the systemic analysis in identifying as well as analyzing the crime patterns and trends. Crime analysis is very important for law enforcement agencies as it helps law enforcers effectively deploy the available resources in a better and effective manner, which enables them to identify and apprehend suspects. Crime analysis is also very significant when it comes to arriving at solutions devised to come up with the right solution to solve the current crime problem and issues as well as coming up with the right prevention strategies. Since the year 2014, crime rates in the USA have increased steadily as per a study done by USAFacts, which is a non-partisan initiative (Osborne & Wernicke, 2013). With this increase in crime rates, which has majorly resulted in massive growth in technology, it is essential to come up with better means and ways of dealing with the increased crime rates. With the current advancement in technology, better law enforcement tools developed, which has enabled better crime deterrence in better and efficient ways. All this has been facilitated by the efforts of crime analysts who have come up with better tools and thus enabling the law enforcers to better deal with the crimes (Osborne & Wernicke, 2013). In this paper, I will consider the application of crime analysis technology and techniques in fighting crimes. Application of crime analysis technology and techniques used to make crime analysis more accurate and efficient.
Currently, the two technological tools that are used in predictive policing software have enabled security agencies to effectively use predictive policing ("Crime Analysis: Fighting Crime with Data," 2017). Application of this software has enabled better crime prevention as with data obtained in the previous crimes have been used to predict possible future severe crimes in a specific area.
Through the adoption and use of crime analysis, law enforcement agencies have been able to fight against crimes as when compared with the past effectively. The use of crime analysis comes at the right time, where there has been an increase in crime rates in the current digital error. In a survey done by Wynyard group in 2015, the study revealed that for every 10 law enforcement officials 9 of them believe that the use of current technology in crime analysis has had positive effects in helping the agencies in solving crimes as they can identify essential links and trends in crimes ("Crime Analysis: Fighting Crime with Data," 2017). In the same way, other sectors have benefited from data analysis with spreadsheets, databases, and mapping, law enforcers have been able to use data analysis to come up with a better decision. Crime analysis ha.
Modern trends in police force

Modern policing is being transformed by new technologies that help solve, prevent, and enable new forms of crime. Surveillance cameras are becoming more widespread and advanced, using facial recognition and the ability to track suspects. New forensic techniques like DNA analysis and digital evidence collection are helping identify criminals. The role of intelligence analysts is growing to understand new threat environments and develop police strategies. Wearable cameras on officers and digital recordings of interrogations are increasing transparency and accountability.
Presentation eco.pptx

Technology has revolutionized crime prevention and investigation. In the past, law enforcement relied on tools like trained dogs and footprints, but now use advanced technologies like CCTV, satellites with GPS, and biometric identification through fingerprints, DNA, iris scans, and facial recognition. Other technologies that aid law enforcement include weapons, metal detectors, social media for awareness, and mobile devices that provide location data. While technology enables new types of crimes, it has provided many benefits to outpace criminals when used respectfully and judiciously by law enforcement.
Case Study - Waterloo Regional Police

The Waterloo Regional Police Service used to have an investigator spend full time manually analyzing location data from tracking devices and cell phones to generate reports on suspects' patterns of movement and activities. This was a time-consuming process. The police service purchased ICU Workbench software, which automatically analyzes location data and generates pattern of life reports. This new process provides deeper insights into suspects' behaviors more quickly. It allows the investigator previously dedicated to data analysis to return to field work, while gaining more powerful intelligence. The new software has significantly reduced the time needed to analyze location data and freed up resources for more optimal use.
IRJET- A Survey Paper of Blood Spatter Trajectory Analysis for Forensic Crime

This document discusses blood spatter analysis for forensic crime scene investigation. It begins with an abstract that outlines the application of image processing techniques to analyze blood trajectories at crime scenes. It then provides background on forensic science and crime scene analysis. Specifically, it discusses how blood stains can provide important evidence and how blood spatter analysis is used to help reconstruct crime events. The document emphasizes that accurately collecting and analyzing blood evidence is important for solving cases.
Crimea Russia or Ukraine An International Law Perspective.docx

Crimea: Russia or Ukraine? An International Law Perspective
Crimea was annexed by Russia in 2014 after a referendum was held which was not up to international standards. This move was largely condemned by the West and most of the international community does not recognize Crimea as a legitimate part of Russia, though it is now ruled by Russia and applicable to its laws, currency, and military. For example, residents of Crimea, even those who did not vote or voted against the annexation, are subject to the Russian conscription law which states that all healthy males aged 18 are required to complete mandatory military service unless unable to do so for a medical reason or if they are enrolled in a university (Conscription Service, p. 1). Up to today, Ukraine and Russia both claim that Crimea is theirs and there is no agreement reached at the time to settle this conflict.
Background on how crimea was taken (maidan revolution, etc.)
In order to begin to understand which country Crimea belongs to, it is important to understand the history of the peninsula. Crimea has been part of the Russian empire beginning in 1783 (Kramer, 1) after the defeat of the Ottomans up until 1954 when, during the Soviet Union, it was given to the Ukrainian SFSR by Premier Khrushchev.
Russia’s argument as to why Crimea is theirs
West’s argument as to why it belongs to Ukraine (their own motives and desire for influence)
International Law analysis
Works Cited
“Conscription Service.” Counterterrorism : Ministry of Defence of the Russian
Federation, eng.mil.ru/en/career/conscription/determent.htm.
Kramer, M. (2018, February 02). Why Did Russia Give Away Crimea Sixty Years Ago?
Retrieved December 07, 2018, from
https://www.wilsoncenter.org/publication/why-did-russia-give-away-crimea-sixty-y
ears-ago?gclid=CLHnyZC7ndACFSLicgod-UEIXw
Milestone One: MEMO Draft 1
Milestone One: MEMO Draft 6
THIS IS THE PROFESSOR’S COMMENT ON THE MEMO AND NEEDS TO BE FIXED FOR FINAL SUBMISSION.( Gifty,Thanks for getting this turned in. For a memo, this is a little long. You will want to be more succinct and cut this down a bit.)
MEMO
DATE: 12/08/2018
TO: Non-expert Stakeholder
FROM: (Cybersecurity Practitioner)
SUBJECT: DIGITAL FORENSIC INVESTIGATION MEMO
Over a period of years digital forensic investigation has out grown into a body that in need of details digital forensic model. Different academic researchers have suggested over a hundred different types of investigation procedural models. In addition to this proposed model over the years, there has been a challenged whereby the model lack experimental testing to ascertain the truth about the investigation. More so there is a need of evaluating the same model to complement the process of investigation progression in support to the entire scientific community (Learner, D. E. (2009). Electronic cri.
Anti-Forensic Techniques and Its Impact on Digital Forensic

This paper discusses anti-forensic techniques that are used to evade digital forensic investigations. It provides an overview of common anti-forensic techniques such as file wiping, data hiding using encryption, steganography, and obfuscation. The paper analyzes how these techniques work and their effectiveness at impeding investigations. It highlights the need for new forensic tools and techniques to counter increasingly sophisticated anti-forensic methods used by criminals to cover their digital traces and hide evidence.
Assignment 3 Major Essay

1) The document discusses 10 potential measures for effective criminal intelligence in law enforcement. It explores these measures in the context of the New Zealand Police and considers if they could be applied to other law enforcement organizations.
2) It provides definitions and models of intelligence to help establish what intelligence outcomes might be. Potential outcomes include having an impact on the criminal environment to make communities safer.
3) Measures are discussed within a framework of interpreting and influencing components of an intelligence model, as well as considering intelligence as a structure, process, and product.
IRAC WorksheetIRAC FormatFactsISSUE#1.docx

IRAC Worksheet
IRAC Format
Facts:
ISSUE:
#1:
#2:
#3
RULE of LAW:
ANALYSIS:
CONCLUSION:
worldwide.erau.edu
All rights are reserved. The material contained herein is the copyright property of Embry-Riddle Aeronautical University, Daytona Beach, Florida, 32114. No part of this material may be reproduced, stored in a retrieval system, or transmitted in any form, electronic, mechanical, photocopying, recording or otherwise without the prior written consent of the University.
image2.png
image3.png
Policing in America
Police officers are the gatekeepers of criminal justice. They are the ones that initiate criminal proceedings against those accused of crimes and send them on their journey through the criminal justice system. Policing has evolved immensely over the centuries. Since the inception of policing in 1066, we have seen a transformation from ill-equipped, untrained, corrupt, and unsupervised watchmen to the highly trained and supervised police agencies we see today.
Question 1: Using Chapter 4, "Police in Society: History and Organization," of your textbook, complete the table below.
History of the
Police
Time Period
Overview of the
Time Period – What Defined It
Strengths of
This Time Period
Weaknesses of
This Time Period
Key Developments
(list two per time period)
1066–1600
(example)
Policing initially began as villages protecting each other from thieves and marauders. This system was overseen by a constable, appointed by the local nobleman. This system expanded into the watch system that patrolled larger cities and towns. Watchmen patrolled at night to protect against robberies, burglaries, and fires. They reported to a constable making up a sort of primitive police agency.
Citizens were responsible for keeping their cities and villages safe. Giving citizens this responsibility made it tougher for criminals to commit a crime undetected.
While the people of the village were responsible for reporting crimes, there was no formal training involved and no oversight to ensure that those responsible for preventing crimes were not the same ones committing crimes.
1. Back then, counties were known as shires, and head law enforcement agents in a county were known as shire reves, which is where we get the modern-day term
sheriff.
2. In 1326, the Justice of the Peace was created and the role of law enforcement expanded beyond just reporting crimes. Justices then also served warrants, investigated crimes, and supervised the local watchmen.
1800–1900
1900–1960
1960–1980
1980–present
(Community Policing period)
Question 2: Which ONE of the above time periods do you believe has had the greatest impact on policing, and why? Be sure to include your rationale.
(
Type answer here) -
Question 3: Social media and technology have greatly affected policing in the past ten years. Please review the links provided for this week on technol.
An application development for police stations in pakistan

Program slice is the part of program that may take the program off the path of the
desired output at some point of its execution. Such point is known as the slicing criterion.
This point is generally identified at a location in a given program coupled with the subset
of variables of program. This process in which program slices are computed is called
program slicing. Weiser was the person who gave the original definition of program slice
in 1979. Since its first definition, many ideas related to the program slice have been
formulated along with the numerous numbers of techniques to compute program slice.
Meanwhile, distinction between the static slice and dynamic slice was also made.
Program slicing is now among the most useful techniques that can fetch the particular
elements of a program which are related to a particular computation. Quite a large
numbers of variants for the program slicing have been analyzed along with the
algorithms to compute the slice. Model based slicing split the large architectures of
software into smaller sub models during early stages of SDLC. Software testing is
regarded as an activity to evaluate the functionality and features of a system. It verifies
whether the system is meeting the requirement or not. A common practice now is to
extract the sub models out of the giant models based upon the slicing criteria. Process of
model based slicing is utilized to extract the desired lump out of slice diagram. This
specific survey focuses on slicing techniques in the fields of numerous programing
paradigms like web applications, object oriented, and components based. Owing to the
efforts of various researchers, this technique has been extended to numerous other
platforms that include debugging of program, program integration and analysis, testing
and maintenance of software, reengineering, and reverse engineering. This survey
portrays on the role of model based slicing and various techniques that are being taken
on to compute the slices.
1 Project Background Rosa County Public Safety Syste.docx

1
Project Background: Rosa County Public Safety System Upgrade
Note: this case study project focuses on the software development, physical installation, and personnel
training required for a public safety system upgrade, the addition of a computer-aided dispatch (CAD)
system that allows municipal governments to receive and process incoming emergency calls to public fire
and police departments and then to dispatch appropriate field units to required locations. Details included
in this case study are based on review of several different CAD systems throughout the United States and
are intentionally set in the late 1990s, when standardized project management processes and practices
were used less commonly than they are today. No individuals from any municipality are included in this
case study (either by name or pseudonym), and any similarities to actual systems, processes or events is
coincidental.
Rosa County (population 900,000, covering over 500 square miles) first investigated upgrading its public
safety response processes in the late 1990s, when the County Police Department had been working with
the County Fire Department to share handling all police and fire-related communications and dispatch
functions internally and, due to a rapidly increasing population, both departments realized call volume was
quickly exceeding current ability to respond.
The existing cumbersome and labor intensive call response process also required a steady pool of internal
support to maintain, made up of civilian call takers and dispatchers, and, more recently, uniformed
personnel who were tasked on an as-needed basis during especially active periods (holiday weekends, for
example). To address the growing problem, Rosa County public safety representatives attended a state-
wide public safety symposium in early 1998 to discuss similar issues encountered by other counties, as
well as potential solutions. One of several vendors at the symposium expo, OnCall Systems, caught the
attention of Rosa Police Department senior personnel and scheduled a demonstration of their recently-
developed computer-aided dispatch (CAD) system for the following week.
OnCall gave their prepared demonstration as scheduled, the week after the symposium. The
demonstration focused on assignment and tracking of units in response to calls for service, with enhanced
electronic mapping and address retrieval capability at the dispatch center and inside units themselves. The
demonstration also featured significant use of a Global Positioning System (GPS) to locate and track
emergency vehicles using externally-mounted transmitters. The demonstration was attended by Rosa
County police and fire department personnel, including the Chief of Police, his immediate assistant, and a
handful of deputy and assistant chiefs from both departments. The Fire Chief was unable to attend due to
a scheduling conflict, but his Assistant Chief of Administrative ...
External Mechanisms Of Accountaability

The document discusses various mechanisms of accountability for police departments, including internal mechanisms like COMPSTAT and external mechanisms like civilian review boards and courts. COMPSTAT is an internal accountability method that uses data analysis of crime statistics to hold police commanders accountable for addressing problems in their jurisdictions. It promotes focused problem-solving in police meetings. External accountability comes from civilian oversight like review boards and courts establishing police misconduct standards.
Malware analysis

This document discusses a case study involving a small-medium enterprise (SME) that has experienced anomalies in its accounting and product records. The SME has hired a digital forensic investigator to determine if any malicious activity has occurred and ensure its systems are free of malware. The investigator will conduct a malware investigation and digital forensic investigation following the four principles of the Association of Chief Police Officers (ACPO) guidelines. The investigator will use the Four Step Forensics Process (FSFP) model to identify, preserve, extract, and analyze evidence from the SME's systems to determine the cause of problems and make recommendations.
Predictive-Preventative-or-Intelligence-Led-Policing

This document discusses the current state and future of predictive policing and intelligence-led policing. It provides an overview of techniques currently used by UK police forces, such as crime mapping and repeat victimization analysis. It finds that while current approaches are data-driven, they are not truly predictive and instead focus on intelligence and prevention. The document envisions the future involving more advanced use of data and technology to help officers focus on prevention and improving community safety. However, it cautions that true predictive policing would require integrating more diverse data sources than what most current models use. Overall, the document argues that predictive policing can help police make valuable contributions to victim and community protection when its tools evolve to enable more preventative strategies.
Predictive preventative-or-intelligence-led-policing

This document discusses the current state and future of predictive policing and intelligence-led policing. It provides an overview of techniques currently used by UK police forces, such as crime mapping and repeat victimization analysis. It finds that while current approaches are effective at reducing crime, they are not truly predictive and rely on historical crime data. True predictive policing would require integrating additional data sources. The document also speculates on how policing demands may evolve with trends like cybercrime and how police can leverage new technologies and data to help prevent crime and support communities in the future.
Similar to Oakland Report on ShotSpotter: May 13, 2014 Public Safety Committee Meeting (20)
IRJET- A Survey Paper of Blood Spatter Trajectory Analysis for Forensic Crime

IRJET- A Survey Paper of Blood Spatter Trajectory Analysis for Forensic Crime
Crimea Russia or Ukraine An International Law Perspective.docx

Crimea Russia or Ukraine An International Law Perspective.docx
Anti-Forensic Techniques and Its Impact on Digital Forensic

Anti-Forensic Techniques and Its Impact on Digital Forensic
An application development for police stations in pakistan

An application development for police stations in pakistan
1 Project Background Rosa County Public Safety Syste.docx

1 Project Background Rosa County Public Safety Syste.docx
Predictive-Preventative-or-Intelligence-Led-Policing

Predictive-Preventative-or-Intelligence-Led-Policing
Predictive preventative-or-intelligence-led-policing

Predictive preventative-or-intelligence-led-policing
More from Yehoshua7
Schedule of City of Oakland Meetings

This is an incomplete list as the City of Oakland doesn't have the meeting times and locations for a number of Boards and Commissions posted. If/when the city responds to requests for that information, an updated list will be posted.
Oakland Sharing the Vision (OSV) Members, 1992

This document lists the members of various task forces for the organization Oakland Sharing the Vision. It includes over 300 members divided among task forces focused on Expanded Economic Base, Neighborhood Revitalization, Safe Healthy Drug-Free City, Education and Lifelong Learning, Building Coalitions, Cultural Affairs, and Grants/Public Art/Marketing committees. The document provides names and is intended to identify individuals involved in different initiatives of the organization.
2010 Oakland Mayoral Election RCV Eliminations

In a ranked-choice election, Don Perata received the most first-choice votes at 40,342 (33.73%). Over subsequent rounds, more candidates were eliminated and their votes redistributed until Don Perata received 51,872 votes (49.04%) in the final round to win the election. Jean Quan placed second, receiving 53,897 votes (50.96%) after all redistributions.
Alameda County Registrar of Voters Ranked-Choice Voting Presentation

2012 presentation created by the Alameda County Registrar of Voters about Ranked-Choice Voting (RCV).
Alameda County Registrar of Voters' Report on Oakland's 2010 RCV Election

An informational report delivered to the Oakland City Council on 4/5/2011 by the Alameda County Registrar of Voters analyzing Oakland's first rankd-choice voting election in November 2010.
2014 Fair Political Practices Commission Filing Schedule for Candidates and C...

This document provides a filing schedule and guidelines for candidates and controlled committees for local office being voted on November 4, 2014 in California. It outlines reporting deadlines and required forms to file by specific dates for semi-annual reports, contribution reports, pre-election reports, and post-election reports. It also includes notes on requirements for candidates, county central committee candidates, officeholders, and rules regarding independent expenditures and public records.
Eric Wilson FPPC Form 700

This document is a Form 700 Statement of Economic Interests filed with the Fair Political Practices Commission of California. It contains information about an individual filing the form, including their name, position as Mayor of Oakley, and the period covered, which is January 1, 2013 through December 31, 2013. On the form, the individual indicates they have no reportable interests to disclose on any schedule.
Charles Williams FPPC Form 700

This document is a Form 700 Statement of Economic Interests filing for an individual. It includes schedules summarizing real estate holdings and investments. The investments include stocks in two companies. The real estate holdings include a residential property valued between $100,001 and $1,000,000. This appears to be the individual's annual economic disclosure filing for California as required for public officials.
Charles Williams FPPC Form 501

Walter Jones intends to run for City Council in Oakland, California in 2022 as a member of the Green Party. He provided his name, address in Oakland, and contact information. The office sought is for a non-partisan district seat on the City Council of Oakland in the 2022 election. Jones signed the form, certifying the information is true and correct.
Charles Williams FPPC Form 460 1-1-14 to 6-30-14

The document is a campaign finance disclosure form that includes:
1) A verification section requiring signatures of the treasurer and controlling candidates/officeholders;
2) A committee information section identifying the name, address, treasurer, and ID number of the committee filing the report;
3) Disclosure of the period covered by the report and the type of report being filed.
Charles Williams FPPC Form 410

This document is a Statement of Organization for a recipient committee called "Charles R. Williams for Mayor of Oakland 2014". It provides information such as the committee's treasurer, address, controlled candidate, and indicates that it is a controlled committee formed to support the candidacy of Charles R. Williams for Mayor of Oakland in 2014.
Joe Tuman FPPC Form 700

This document is Jose Corona's 2013 Statement of Economic Interests (Form 700) filed with the Fair Political Practices Commission of California. It discloses his investments, income sources, loans, and business positions held in 2013. Specifically, it lists investments in Wells Fargo bank and income over $100,000 from his position as Mayor of Oakland. It does not disclose any reportable loans or other business positions.
Joe Tuman FPPC Form 501

Joseph Smith is running for the nonpartisan office of Mayor of Orlando. He is accepting the voluntary expenditure ceiling for the upcoming primary election. He certifies that the information provided is true and correct.
Joe Tuman FPPC Form 460 7-1-13 to 12-31-13

The document is a campaign disclosure statement cover page for Joe Tuman for Mayor 2014. It includes information such as the time period covered, a summary of contributions received and expenditures made, cash on hand and outstanding debts. It also lists Joseph Tuman as the candidate and Scott Law as the treasurer. Signatures of the treasurer and candidate are included to verify the accuracy of the financial information.
Joe Tuman FPPC Form 460 1-1-14 to 6-30-14

The document is a campaign finance disclosure form that includes:
1) A verification section requiring signatures from the treasurer and controlling candidates/officeholders certifying the accuracy of the financial disclosures;
2) Sections requesting information about the recipient committee including the name, address, treasurer, and type of committee;
3) Disclosure of contributions received, expenditures made, outstanding loans and debts, and ending cash balances.
Joe Tuman FPPC Form 410

This document is a Statement of Organization form filed with the California Fair Political Practices Commission for a recipient committee called "CONTROLLING OFFICIAL (CANDIDATE MEASURE PROPONENT". It lists the committee's contact information, its treasurer, and indicates that it is a controlled committee with Jo as the candidate and the elective office being sought as Mayor of Oakland.
Dan Siegel FPPC Form 700

Dan Siegel, a candidate for Mayor of Oakland, filed a Form 700 Statement of Economic Interests. He reported owning a single-family home in Oakland worth $100,001-$1,000,000. He also reported income of over $100,000 from a law partnership. No other reportable economic interests or positions were disclosed.
Dan Siegel FPPC Form 501

This document is a candidate intention statement for Siegel, who is running for a partisan state office in district 1. It provides Siegel's contact information and indicates they will not exceed the voluntary expenditure ceiling for the primary election held on a unspecified date. Siegel also agrees to accept the voluntary expenditure ceiling for the general election. The document is signed and dated, with Siegel declaring under penalty of perjury that the information provided is true and correct.
Dan Siegel FPPC Form 460 1 1-14 to 6-30-14

The document is a campaign finance disclosure form that includes sections for verification of information, committee information, and a summary page. It requires original signatures from the treasurer, controlling officeholder, and candidate to verify the accuracy of the financial information provided in the report.
Dan Siegel FPPC Form 410

This document is a Statement of Organization form filed with the state of California disclosing information about the Dan Siegel for Mayor 2014 campaign committee. It provides details such as the committee name and address, the treasurer's name and contact information, the financial institution used, and indicates that the committee is a controlled committee seeking to elect Dan Siegel as Mayor of Oakland in 2014.
More from Yehoshua7 (20)
Alameda County Registrar of Voters Ranked-Choice Voting Presentation

Alameda County Registrar of Voters Ranked-Choice Voting Presentation
Alameda County Registrar of Voters' Report on Oakland's 2010 RCV Election

Alameda County Registrar of Voters' Report on Oakland's 2010 RCV Election
2014 Fair Political Practices Commission Filing Schedule for Candidates and C...

2014 Fair Political Practices Commission Filing Schedule for Candidates and C...
Recently uploaded
Border towns and spaces of (in)visibility.pdf

This report explores the significance of border towns and spaces for strengthening responses to young people on the move. In particular it explores the linkages of young people to local service centres with the aim of further developing service, protection, and support strategies for migrant children in border areas across the region. The report is based on a small-scale fieldwork study in the border towns of Chipata and Katete in Zambia conducted in July 2023. Border towns and spaces provide a rich source of information about issues related to the informal or irregular movement of young people across borders, including smuggling and trafficking. They can help build a picture of the nature and scope of the type of movement young migrants undertake and also the forms of protection available to them. Border towns and spaces also provide a lens through which we can better understand the vulnerabilities of young people on the move and, critically, the strategies they use to navigate challenges and access support.
The findings in this report highlight some of the key factors shaping the experiences and vulnerabilities of young people on the move – particularly their proximity to border spaces and how this affects the risks that they face. The report describes strategies that young people on the move employ to remain below the radar of visibility to state and non-state actors due to fear of arrest, detention, and deportation while also trying to keep themselves safe and access support in border towns. These strategies of (in)visibility provide a way to protect themselves yet at the same time also heighten some of the risks young people face as their vulnerabilities are not always recognised by those who could offer support.
In this report we show that the realities and challenges of life and migration in this region and in Zambia need to be better understood for support to be strengthened and tuned to meet the specific needs of young people on the move. This includes understanding the role of state and non-state stakeholders, the impact of laws and policies and, critically, the experiences of the young people themselves. We provide recommendations for immediate action, recommendations for programming to support young people on the move in the two towns that would reduce risk for young people in this area, and recommendations for longer term policy advocacy.
2024: The FAR - Federal Acquisition Regulations, Part 41

Jennifer Schaus and Associates hosts a complimentary webinar series on The FAR in 2024. Join the webinars on Wednesdays and Fridays at noon, eastern.
Recordings are on YouTube and the company website.
https://www.youtube.com/@jenniferschaus/videos
PUBLIC FINANCIAL MANAGEMENT SYSTEM (PFMS) and DBT.pptx

PUBLIC FINANCIAL MANAGEMENT SYSTEM (PFMS) and DBT - EXPLANATION
A guide to the International day of Potatoes 2024 - May 30th

Food and Agricultural Organization (FAO)
快速办理(Bristol毕业证书)布里斯托大学毕业证Offer一模一样

学校原件一模一样【微信:741003700 】《(Bristol毕业证书)布里斯托大学毕业证》【微信:741003700 】学位证,留信认证(真实可查,永久存档)原件一模一样纸张工艺/offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原。
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
【主营项目】
一.毕业证【q微741003700】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【q/微741003700】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
Monitoring Health for the SDGs - Global Health Statistics 2024 - WHO

The 2024 World Health Statistics edition reviews more than 50 health-related indicators from the Sustainable Development Goals and WHO’s Thirteenth General Programme of Work. It also highlights the findings from the Global health estimates 2021, notably the impact of the COVID-19 pandemic on life expectancy and healthy life expectancy.
在线办理美国乔治华盛顿大学毕业证(gwu毕业证书)学历学位证书原版一模一样

原版一模一样【微信:741003700 】【美国乔治华盛顿大学毕业证(gwu毕业证书)学历学位证书】【微信:741003700 】学位证,留信认证(真实可查,永久存档)offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原海外各大学 Bachelor Diploma degree, Master Degree Diploma
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
Milton Keynes Hospital Charity - A guide to leaving a gift in your Will

A forever thank you in your Will to Milton Keynes University Hospital can change lives for years to come.
Donate to charity during this holiday season

For people who have money and are philanthropic, there are infinite opportunities to gift a needy person or child a Merry Christmas. Even if you are living on a shoestring budget, you will be surprised at how much you can do.
Donate Us
https://serudsindia.org/how-to-donate-to-charity-during-this-holiday-season/
#charityforchildren, #donateforchildren, #donateclothesforchildren, #donatebooksforchildren, #donatetoysforchildren, #sponsorforchildren, #sponsorclothesforchildren, #sponsorbooksforchildren, #sponsortoysforchildren, #seruds, #kurnool
原版制作(英国Southampton毕业证书)南安普顿大学毕业证录取通知书一模一样

学校原件一模一样【微信:741003700 】《(英国Southampton毕业证书)南安普顿大学毕业证》【微信:741003700 】学位证,留信认证(真实可查,永久存档)原件一模一样纸张工艺/offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原。
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
【主营项目】
一.毕业证【q微741003700】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【q/微741003700】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
快速办理(UVM毕业证书)佛蒙特大学毕业证学位证一模一样

学校原件一模一样【微信:741003700 】《(UVM毕业证书)佛蒙特大学毕业证学位证》【微信:741003700 】学位证,留信认证(真实可查,永久存档)原件一模一样纸张工艺/offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原。
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
【主营项目】
一.毕业证【q微741003700】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【q/微741003700】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
Antyodaya saral portal haryana govt schemes

The Antyodaya Saral Haryana Portal is a pioneering initiative by the Government of Haryana aimed at providing citizens with seamless access to a wide range of government services
Awaken new depths - World Ocean Day 2024, June 8th.

UN WOD 2024 will take us on a journey of discovery through the ocean's vastness, tapping into the wisdom and expertise of global policy-makers, scientists, managers, thought leaders, and artists to awaken new depths of understanding, compassion, collaboration and commitment for the ocean and all it sustains. The program will expand our perspectives and appreciation for our blue planet, build new foundations for our relationship to the ocean, and ignite a wave of action toward necessary change.
United Nations World Oceans Day 2024; June 8th " Awaken new dephts".

The program will expand our perspectives and appreciation for our blue planet, build new foundations for our relationship to the ocean, and ignite a wave of action toward necessary change.
Practical guide for the celebration of World Environment Day on june 5th.

Land degradation, desertification and drought resilience. UN ENVIRONMENT PROGRAMME -WORLD ENVIRONMENT DAY 2024.
在线办理(ISU毕业证书)爱荷华州立大学毕业证学历证书一模一样

学校原件一模一样【微信:741003700 】《(ISU毕业证书)爱荷华州立大学毕业证学历证书》【微信:741003700 】学位证,留信认证(真实可查,永久存档)原件一模一样纸张工艺/offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原。
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
【主营项目】
一.毕业证【q微741003700】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【q/微741003700】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
Recently uploaded (20)
2024: The FAR - Federal Acquisition Regulations, Part 41

2024: The FAR - Federal Acquisition Regulations, Part 41
PUBLIC FINANCIAL MANAGEMENT SYSTEM (PFMS) and DBT.pptx

PUBLIC FINANCIAL MANAGEMENT SYSTEM (PFMS) and DBT.pptx
A guide to the International day of Potatoes 2024 - May 30th

A guide to the International day of Potatoes 2024 - May 30th
Monitoring Health for the SDGs - Global Health Statistics 2024 - WHO

Monitoring Health for the SDGs - Global Health Statistics 2024 - WHO
Milton Keynes Hospital Charity - A guide to leaving a gift in your Will

Milton Keynes Hospital Charity - A guide to leaving a gift in your Will
Awaken new depths - World Ocean Day 2024, June 8th.

Awaken new depths - World Ocean Day 2024, June 8th.
United Nations World Oceans Day 2024; June 8th " Awaken new dephts".

United Nations World Oceans Day 2024; June 8th " Awaken new dephts".
Practical guide for the celebration of World Environment Day on june 5th.

Practical guide for the celebration of World Environment Day on june 5th.
Oakland Report on ShotSpotter: May 13, 2014 Public Safety Committee Meeting
- 1. CITY OF OAKLAND FILED QFf iCE Of THE C(T i C l t ^ ^ 0 AP,L A n : ; 2014 HAY-! PM1:39 AGENDA REPORT TO: FRED BLACKWELL CITY ADMINISTRATOR FROM: SeanWhent Interim Chief of Police SUBJECT: ShotSpotter Informational Report DATE: April 1,2014 City Administrator Approval Date COUNCIL DISTRICT: Citv-wide RECOMMENDATION Staff recommends acceptance of this informational report from the Oakland Police Department (OPD) that addresses the ShotSpotter system (SST) and its usage in the City of Oakland (City). EXECUTIVE SUMMARY This informational report addresses SST and its implementation in the City as it pertains to gun violence. The report covers the history of the system, associated cost, and the manner in which it is currently being used (as a response tool, investigative module, community awareness tool, and gunshot predictor). SST is an acoustic gunshot locator system that tracks gunshots in the City, while alerting law enforcement to the location and number of rounds fired. BACKGROUND/LEGISLATIVE HISTORY OPD entered into the original contract with ShotSpotter, Inc. (ShotSpotter) and went live with the system in 2006 (SST 1.0). This original arrangement covered 6.2 square miles of the City and required OPD to purchase hardware and software. SST 1.0 was a turnkey system managed entirely by OPD with no reviewed alerts (OPD was responsible for listening to the alerts and determining if they were in fact actual gunshots). The SST 1.0 maintenance contract covering hardware and software purchased by the City expired in 2009. As SST 1.0 began to deteriorate, broken sensors and outdated software rendered it useless for enforcement and/or investigative purposes. From 2009 - 2011, the City was not in contract with ShotSpotter and did not pay any fees associated with SST. In July of 2011, staff was asked to prepare a report and resolution authorizing the City Administrator to enter into an agreement with ShotSpotter for implementation of the system a Item# Public Safety Committee May 13,2014
- 2. Fred Blackwell, City Administrator Subject: ShotSpotter Informational Report Date: April 1,2014 . Page 2 second time. The report and resolution was adopted by the City Council (Resolution No. 83580 C.M.S.). The Shotspotters system was implemented at a cost of $84,000 annually. At that point, the City considered expanding SST city-wide at an additional cost of $264,000 annually. This expansion was budgeted and approved by the City Council in the Fiscal Year 2012-2013 (FY2012-13) Adopted Mid-cycle Budget. The additional $264,000 did not include the annual cost of $84,000 for the current system and its maintenance. In November 2011, the City restarted the program with SST as a conversion-managed service. This new program (SST 2.0) required: • Upgraded sensor arrays to improve detection of gunfire; • Web-based alerts pushed to all police vehicles and selected desktops; and • Review of alerts 24/7 by ShotSpotter expert reviewers ("Flex"). SST 2.0 also added an investigative portal to assist in open investigations. Qualified gunfire incident alerts are sent directly to 911 dispatch and police vehicles at the same time. They provide precise location information, including street address, number of rounds fired, map images, and additional data. In August 2012, City Auditor Courtney Ruby released an audit titled Police Technology Audit. This audit focused on technologies purchased by OPD that were either underutilized or not being used at all. SST was one of the technologies identified as being underutilized. The audit addressed deficiencies in how technology deployment, accountability, and non-use of the system by investigators. Although the audit accurately identified deficiencies, these had been addressed during the transition to SST 2.0. This audit did inspire OPD to conduct ongoing monthly audits of the system for accuracy, completeness, and customer-service-related matters, which continue. In April 2013, the City expanded the system to cover 13.3 square miles and partnered with the Oakland Housing Authority (OHA) to join the system and enhance response to gun violence City-wide. OHA contributed $225,000 towards this expansion to off-set the cost to the City. Additionally, the system was integrated with Forensic Logic (a data mining system) to assist in predictive policing and Area Commander accountability. A recent audit of SST 2.0 data revealed that every 2 hours and 4 minutes, a gun is fired in Oakland. On average, approximately four rounds are fired in each gunfire incident. In 2013, a total of 16,557 rounds of gunfire were fired throughout the streets of Oakland. Item: Public Safety Committee May 13,2014
- 3. Fred Blackwell, City Administrator Subject: ShotSpotter Informational Report Date: April 1,2014 Page 3 ANALYSIS Privacy Issues Beyond being a crime-fighting tool, SST 2.0 is a powerful instrument for increasing community awareness and improving police-community relationships. To that end, transparency is the key for critique, support, and improvement. As technology evolves, so do questions regarding privacy as well as how this data is used. However, SST 2.0 only triggers on loud, explosive events. When an incident is detected and located, audio is pushed from the sensors and there is no live audio streaming capability. A recent audit of a 24-hour span in Oakland revealed the following: • 47 incidents occurred; • 42 gunfire rounds were fired; • Average length of recording was 2.7 seconds; • Maximum length of recording was 6.2 seconds; and • Out of a total 86,400 seconds in the day, SST 2.0 recorded 128 seconds (0.187% of the day). During this time no voices/conversations were recorded or were heard. ShotSpotter has reviewed its privacy policy and taken steps to assure that no audio other than the incident itself is retained. Incident audio records 2 seconds prior to and 4 seconds after the incident. ShotSpotter policies and the system design are intentionally designed to alleviate privacy concerns. 91I/Gunshot Notifications Without a doubt, human intelligence and eyewitness testimony is the best evidence in dealing with arrests, investigations, and prosecutions of individuals involved in gun violence. While not a panacea, SST is a very important tool in notification, response, and criminal investigation follow-up in regards to gun violence. OPD cannot always rely on the citizens of Oakland to be OPD's eyes and ears when it comes to gunshot deterrence and response. In fact, in many neighborhoods with high levels of gun violence, OPD has seen a decrease in calls to 911 regarding gun violence. During a recent audit comparing SST activations to 911 calls in response to actual confirmed gun violence in a very active 3/4 mile radius, it was determined that OPD received calls on 13% of the incidents: SST reported 98% of the incidents. The audit also looked at time delay in reporting. On average, calls to 911 were answered 4 minutes after the shooting; SST nofification averaged 30 seconds for the same incidents. Lastly, the audit looked at the distance between the caller and the shooting scene. On average, callers were 780 feet away, while SST was within 30 feet of the shooting incident. The more timely and accurate information provided by SST allows OPD to respond more rapidly, which increases the opportunity to capture perpetrators of Item: Public Safety Committee , May 13, 2014
- 4. Fred Blackwell, City Administrator Subject: ShotSpotter Informational Report Date: April 1,2014 Page 4 violence. Further, accurate information enables OPD to respond to the correct location, so that people in the community see that OPD cares and is responsive to violence in the community. Table 1 below provides raw data on the amount of incidents recorded by SST. Prior to November 30, 2011, the system was divided into two coverage areas - Oakland East and Oakland West. On November 30, 2011, the system was converted to Flex and both coverage areas were combined. It should also be noted that there were periods of time between 2006 - 2011 when the system was not fully functioning. Table 1. SST data. Oakland East Oakland West Current System Entire Coverage Area -;:;;r-9/26/O6r,i;|/28/0H^ ; A :l1/30/11^3/31/14: All Incidents 62,680 6,701 49,831 Guhs]tjots.<3nj5^^^ .-fv Investigative Component ShotSpotter forensic reports provide evidence to support criminal cases as well as evidence in liability cases for the City (e.g., officer-involved shootings). Since 2006, ShotSpotter has completed 70 detailed forensic reports (DFRs) for OPD. DFRs contain court-admissible evidence and are used frequently in court cases and prosecutions. In 2013 alone, ShotSpotter completed 17 DFRs for OPD that have provided law enforcement and criminal justice professionals with detailed audio and incident analysis. Because the City is an active customer, ShotSpotter has also provided expert testimony, reviewed report details, and. offered technical expertise on the technology at no additional charge. Oakland Housing Authority (OHA) OPD approached OHA in late 2012 and asked for assistance in funding the SST expansion project in exchange for data sharing and OHA access to SST equipment, training, and technical support. OHA agreed and entered into a memorandum of understanding (MOU) with OPD, contributing a one-time fee of $225,000 to OPD for what was believed to be a three-year commitment by OPD to ShotSpotter. Since the agreement, OHA Chief Carel Duplessis has stated that his agency uses the system for call response and crime analysis. OHA has stated that the system has been very beneficial, allowing its staff to provide improved crime analysis, call response planning for officers, confirmation of observations regarding gunshots, and reducing time on calls when canvassing the areas for evidence. Item: Public Safety Committee May 13,2014
- 5. Fred Blackwell, City Administrator Subject: ShotSpotter Informational Report Date: April 1,2014 Page 5 Training/Technology Innovations ShotSpotter has provided detailed training to all Patrol staff in use of the system and best practice responses to shooting scenes. Additionally, training has been provided to investigative units and OPD crime analysts. ShotSpotter trainers have conducted the training at various days and times during line-ups to accommodate rotating shifts. SST training also continues with webinars and "train the trainer" courses throughout the year. ShotSpotter has developed a new program called "Siren" which enables users anywhere to view SST incidents in detail via email or internet on virtually any device. Forensic Logic Integration Forensic Logic is a company founded on the simple idea that there is too much crime on our streets because critical information is inaccessible or unusable to our nation's law enforcement. Forensic Logic has assembled the largest database of law enforcement data in the country and matched it with some of the most robust and intuitive crime search and analysis tools. Forensic Logic currently mines the OPD CAD (911 system). Stop Data, License Plate Reader, and Reports Management System. Forensic Logic is also used by OPD as accountability metric during the bi-monthly COMPSTAT meetings for crime reduction by Areas. ShotSpotter and Forensic Logic began data sharing in 2013 and now SST data can be used during COMPSTAT and is readily available during deployment, operation planning, and community meetings. PUBLIC OUTREACH/INTEREST Implementation of the ShotSpotter Gun Location System will result in a technological force multiplier, increasing the likeliness that officers will apprehend subjects involved in violent crime. Concerted efforts such as this will undoubtedly do much to establish an environment in the community that is conducive for families to thrive free of crime and the fear of crime. The data collected by ShotSpotter is made accessible to the community so that they can have accurate knowledge about the state of the City. COORDINATION The Budget Office and the City Attorney's Office were consulted in the preparation of this report. COST SUMMARY/IMPLICATIONS OPD currently does not have fiinding for the continuance of this proposed program. Funding would need to be identified outside the current approved budget to continue this $348,000 yearly expenditure. Table 2 below depicts annual revenues paid to ShotSpotter since the inception of the system. Item: Public Safety Committee May 13, 2014 , /
- 6. Fred Blackwell, City Administrator Subject: ShotSpotter Informational Report Date: April 1,2014 Page 6 Table 2. Revenues paid to ShotSpotter since impementation of the system in Oakland. Year Total Spent 2006 : $377,920 2007 $56,276 2008 $54,151 2009 0 2010 0 2011 $84,151 2012 $10,000 2013 $432,000 SUSTAINABLE OPPORTUNITIES Economic: Responding to crime scenes in a timelier manner and having an increased capacity to analyze crime results in a more efficient use of resources, focuses efforts on crime trends and patterns, and enhances police services to respond to emerging crime trends. These results improve public safety, thereby providing a safer environment for residents and local commerce to flourish. Environmental: There are no environmental issues associated with this report. Social Equity: Implementation of the ShotSpotter Gun Location System will result in a technological force multiplier, increasing the likeliness that officers will apprehend subjects involved in violent crime. Concerted efforts such as this will undoubtedly do much to establish an environment in the community that is conducive for families to thrive free of crime and the fear of crime. The data collected by ShotSpotter is made accessible to the community so that they can have accurate knowledge about the state of the City. Item: Public Safety Committee May 13,2014
- 7. Fred Blackwell, City Administrator Subject: ShotSpotter Informational Report Date: April 1,2014 . Page 7 For questions regarding this report, please contact Captain Ersie M. Joyner III, at (510) 773- 0411. Respectfully submitted. Sean Wnent Interim Chief ofP^ice Oakland Police Department Prepared by: Ersie M. Joyner III Captain of Police Oakland Police Department Item: Public Safety Committee May 13, 2014