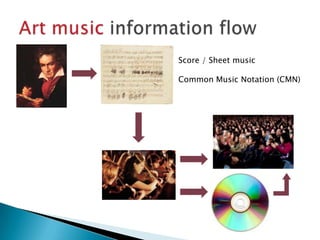
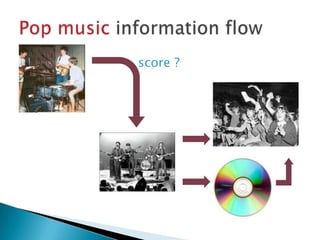
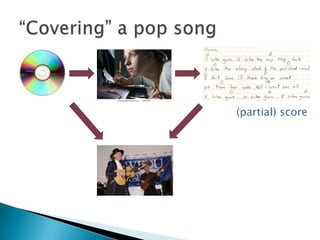
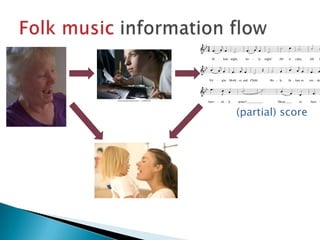
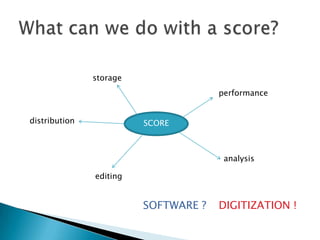
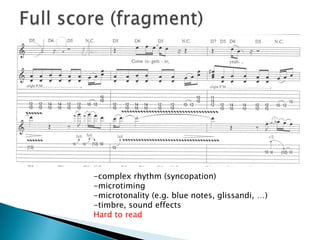
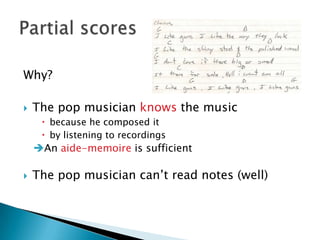
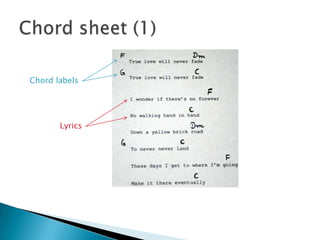
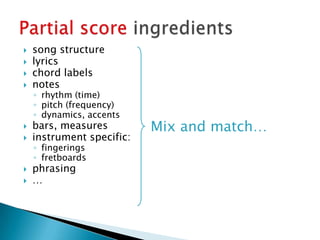
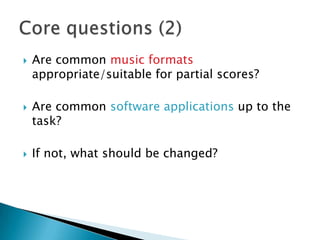
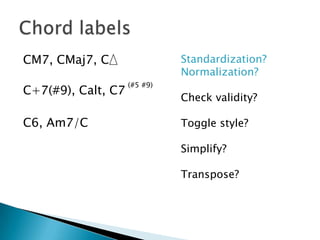
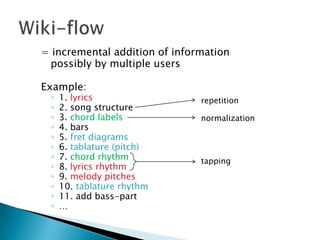
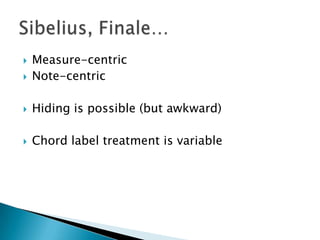
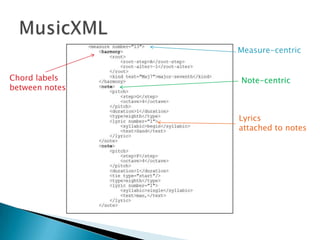
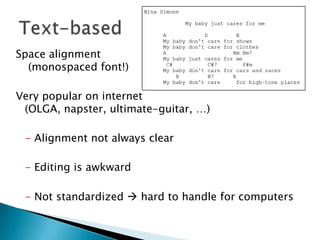
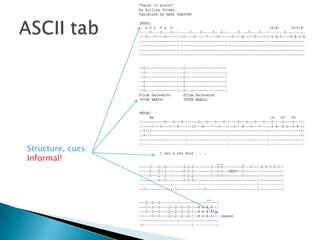
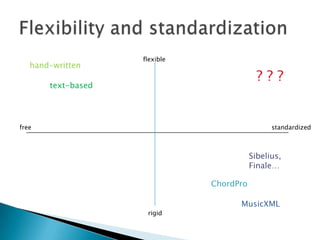
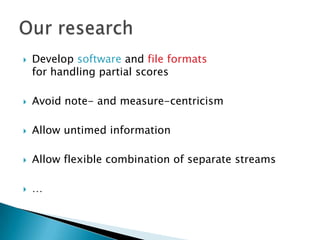
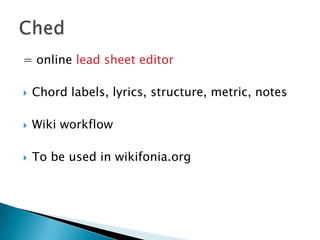
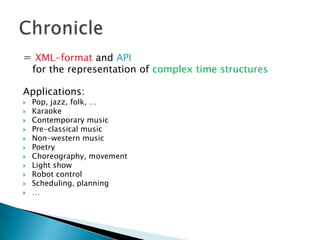
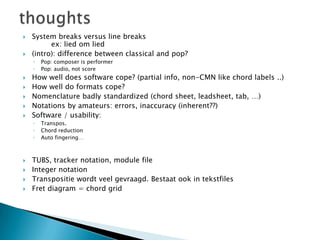
The document discusses the complexities of pop music notation, exploring how traditional common music notation (CMN) may not adequately represent the unique characteristics of pop music, such as syncopation and microtiming. It evaluates various score formats and software applications, highlighting their limitations in handling the diverse needs of pop musicians who often rely on audio rather than written scores. The conclusion emphasizes the necessity for flexible and standardized software and file formats to accommodate the distinct features of pop, jazz, and folk music compositions.