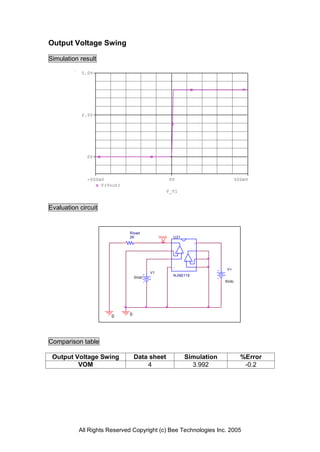
The document provides a detailed modeling report for the NJM2119 operational amplifier, including simulation results for output voltage swing, input offset voltage, slew rate, input current, open loop voltage gain, and common-mode rejection. Each section includes comparison tables with simulation data and percentage error figures. The report emphasizes the accuracy of simulations and measurements conducted on the device, reflecting performance metrics crucial for design applications.